Cloud computing is a common term used multiple times in today’s businesses. It is a revolutionizing technology that helps businesses in their digital transformation and offers multiple benefits for their growth and development. In addition, the technology is beneficial for small, medium, and large businesses. However, technological advancement brings more cloud security challenges to cloud computing. In brief, cloud computing offers data privacy and security and maintains collaboration within the organization. The process is cost-saving and simple for managing the functionality of your organization.
Despite the benefits, cloud computing has multiple privacy and data security drawbacks. Many of these risks arise from poor visibility, compliance gaps, and weak access control, all of which are common cloud security challenges. Moreover, to stay ahead of these issues, companies often turn to cloud automation tools to monitor, manage, and scale their operations more efficiently. Based on the numerous research and articles, we will try to discover the challenges in cloud computing and understand how to avoid such risks.
TL; DR:
Concern: Cloud computing helps businesses grow faster with flexible, low-cost IT services. But as cloud use increases, so do the risks. Particularly, the risks revolve around data privacy, cyberattacks, misconfigurations, and concealed expenses.
Overview: Cloud computing lets companies rent IT infrastructure like storage, software, and servers. It offers flexibility, speed, and savings. However, organizations face challenges like unauthorized access, unsecure third-party apps, lack of data visibility, and legal compliance gaps.
Solution: Businesses can overcome these risks by using encryption, strong access controls, regular audits, and clear compliance practices. CertPro helps companies build secure cloud systems through expert cloud auditing and compliance support for standards like ISO 27001, SOC 2, and GDPR. With proper implementation and monitoring, cloud security becomes manageable and scalable.
WHAT IS CLOUD COMPUTING?
It refers to using hosted services, including data storage, databases, networking, and servers. Simply put, the cloud service provider maintains physical servers on which an organization stores its data. Cloud computing is renting space on the cloud for your data.
For instance, consider cloud computing like renting a fully furnished apartment instead of buying a house. You don’t need to buy furniture, set up a kitchen, or worry about plumbing. All that’s necessary is already there. You can simply move in and begin living. That’s what cloud computing does for IT-based services. In simple terms, cloud computing is the delivery of computing services over the internet, instead of your own hard drives or local servers. These services include storage, servers, databases, software, and analytics. It’s on-demand, flexible, and scalable. Therefore, you can use it and pay according to your needs and requirements.
For businesses, this solution removes the need for setting up bulky infrastructure, hiring a large IT team, or worrying about regular upgrades. It transforms technology from a capital expense (CapEx) to an operating expense (OpEx), a transformative shift for compliance-intensive sectors such as finance, healthcare, and cybersecurity.
Fundamental Features of Cloud Computing:
Resource Pooling: It helps you to use a shared infrastructure to serve multiple customers at the same time.
Enhanced Scalability: Cloud platforms could scale according to your business needs and requirements.
Save Resources: Every action and process in your cloud is tracked and monitored. So, you can pay only for what you are using. This reduces the wastage of resources.
Broad Network Access: With a proper internet connection, you can access your cloud from anywhere. This helps in remote work, collaboration, and instant response to client needs and requests.
TYPES OF CLOUD COMPUTING
Cloud computing is divided based on the deployment and type of services.
Based on Deployment: It can be categorized into three main categories:
Private Cloud:
It is also known as corporate cloud or enterprise cloud. In addition, it offers a private IT network for the dedicated use of a single organization. The cloud is not accessible to anyone outside the organization. However, a private cloud provides all the benefits of a public cloud and offers all the security controls. In addition, the private cloud provides high security through firewalls and internal hosting. Thus, it prevents third-party providers from accessing internal data. Regardless of the benefits, the organization becomes responsible for data maintenance and management in a private cloud. Therefore, the process demands extensive resources and efforts from the organizations.
Public Cloud:
It refers to cloud services offered by third-party providers over the Internet. Thus, the Public cloud is available to anyone who wants to use it. The service changes depending on demand, usage, and storage. In addition, the public clouds reduce organizations’ burden of on-premises infrastructure.
Hybrid Cloud:
As the name suggests, it combines public and private cloud features. Suppose your business graph and data are elevating. Therefore, the hybrid cloud helps your business develop an on-premises infrastructure and change the public cloud model. Thus, the process ensures that your data is secured and free from access to the data centers.
Based on the Service Model:
Cloud computing categorized as Infrastructure-as-a-Service (IaaS), Platform-as-a-Service (PaaS), and Software-as-a-Service(SaaS).
Infrastructure-as-a-Service (IaaS):
In this type of cloud computing, service providers offer servers, storage, and networking over a virtual interface. Therefore, users are free from managing any cloud infrastructure but control the storage and operating systems. For example, Amazon Web Services lets you launch virtual machines for hosting websites or running applications.
Platform-as-a-Service (PaaS):
Cloud computing allows users to develop an application without maintaining the infrastructure. In addition, users can feel free from managing the underlying infrastructure in the PaaS model. For example, using the Google web engine, developers could build and deploy apps without worrying about servers or scalability.
Software-as-a-Service (SaaS):
SaaS allows users to access a vendor’s software on the cloud on a subscription basis. In this service criteria, installing or downloading the application on the user’s devices is unnecessary. Microsoft 365 is one good example that businesses use in their daily communication and file sharing.
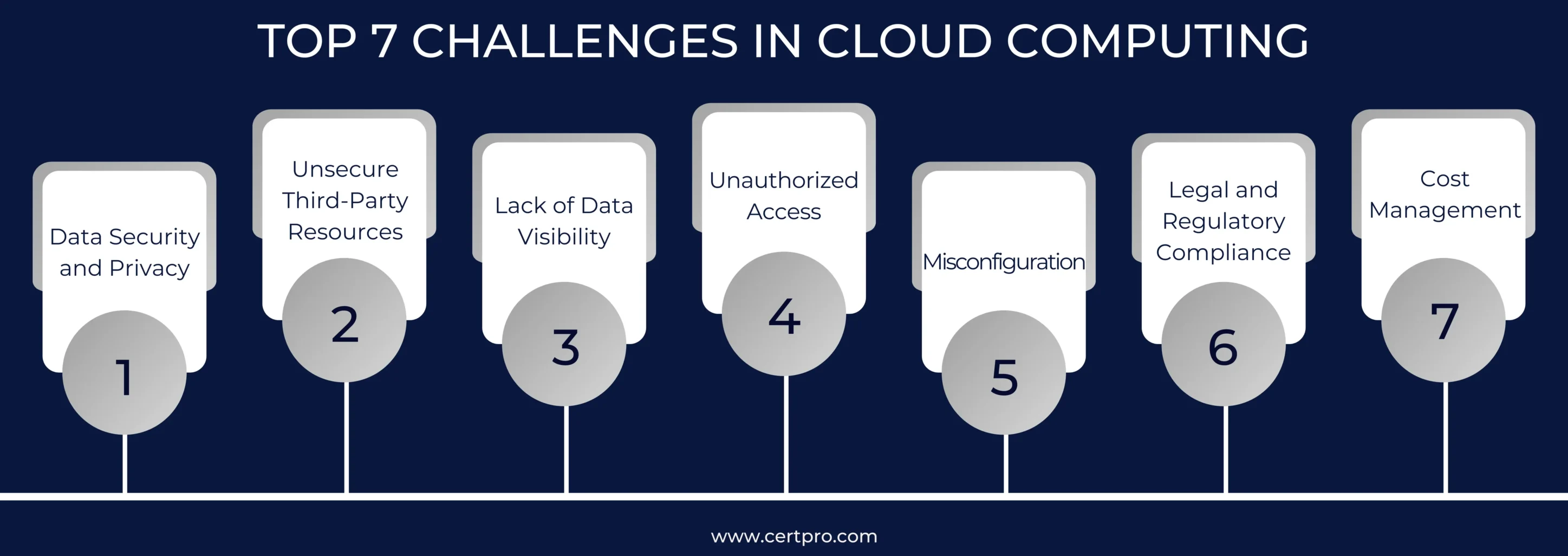
TOP 7 CHALLENGES IN CLOUD COMPUTING
Technological advancement enhances security threats for the data storage process. Therefore, computing services face challenges in maintaining security and data breaches. The cloud infrastructure needs to follow proper guidance to avoid such challenges. Let’s discuss the top 7 cloud computing challenges:
1. Data Security and Privacy:
Cloud computing assists businesses in accessing their data from anywhere in the world. It is an exciting idea, but it is raising concerns about the security of the cloud system. Therefore, organizations do not have any control over their data access, and cyber attackers can access the data. In recent years, many incidents of data breaches have been recorded due to a lack of data security and privacy in cloud systems. The incidents will likely increase as most companies use the cloud for data storage.
Solution:
Data privacy and confidentiality issues will continue to concern businesses. Organizations can avoid such complications by implementing network security, using antivirus and firewalls, and increasing the bandwidth for cloud data. In addition, the implementation of cybersecurity guidelines can also provide data security.
2. Unsecure Third-Party Resources:
Third-party resources include the applications, websites, and services provided by cloud service providers. Therefore, such resources can have security vulnerabilities that put data at risk. Thus, it is essential to ensure the authorized access of data, as unauthorized resources can threaten cloud security. Cyber attackers can access the resources to manipulate the cloud data and systems.
Solution:
Implementing multi-factor authentication and enforcing strict passwords safeguards cloud data. Again, restricting access control can ensure authorized access to data and reduce the risk of data breaches. On the other hand, cloud-based password managers should alert users about security risks.
3. Lack of Data Visibility:
Cloud computing allows businesses to store and access their data online. However, cloud systems pose security threats due to their remote servers. Therefore, companies must implement a strong security posture to prevent data loss, detect breaches, and respond. Organizations can also secure their data through regular audits and identify potential threats and vulnerabilities in the cloud system.
Solution:
On the other hand, organizations can ensure their data remains secure in cloud systems by implementing precautions and security controls. Therefore, multi-layer authorization and authentication tools can prevent data losses.
4. Unauthorized Access:
The most common security issue with the cloud is accessing the information without permission. Therefore, companies find storing and accessing data in the cloud easy, which can expose data to hacking dangers. Cloud computing risks include accessing user data without permission, stealing data, and malware attacks. Thus, businesses need to ensure that only permitted users can access their data to keep it safe from these threats.
Solution:
Encrypting private data in the cloud is another security measure companies can use to prevent unauthorized access to data. Businesses can protect their data from people who should not be able to see it and ensure that it is correct by using security measures like encryption and backups.
5. Misconfiguration:
Cloud computing is now the standard way to access resources remotely while reducing costs. Setting up your cloud systems can ease your worries about cloud computing security. The prime security problem with cloud computing is that users need to learn how to protect their data in the cloud. Users need to safeguard their data and correctly configure applications to thwart this cloud security threat.
Solution:
Businesses can use a cloud storage service with security features like encryption or access control. In addition, authentication and password rules are security steps for cloud systems. By following these steps, users can make their cloud computing systems safer and stay safe from cyber dangers.
6. Legal and Regulatory Compliance:
Cloud systems help businesses cut data storage costs and continue functionality. However, cloud computing brings new security issues that must be dealt with to keep data safe and ensure that legal and regulatory rules are followed. Businesses must enforce all data security laws and regulations to keep their cloud-based systems safe and secure. Malware, data breaches, and scams are just a few problems businesses face when using cloud computing.
Solution:
To fix these cloud-based security problems, it is essential to perform regular security checks, keep security settings up to date, set up robust login methods, use strong passwords, and ensure that software is always up to date. Thus, cyberattacks are more likely to happen when you use the cloud, but appropriate security measures can help them stay ahead of their rivals in this quickly changing market.
7. Cost Management:
In many cases, cloud service providers initially started with the pay-as-you-go subscription model. But gradually, the hidden costs and charges of the systems have come up with a massive financial burden. Organizations face economic pressure to continue the cloud journey. In addition, the organization must implement multiple safety and security processes to work in a cloud environment. Thus, the process requires plenty of financial support to become digital.
Solution:
Organizations can fix this by enforcing resource utilization, monitoring the tools, and auditing the process. Thus, the effort can help organizations deal with the common challenges in cloud computing and its associated budget requirements.
BENEFITS OF CLOUD COMPUTING FOR MODERN BUSINESSES
Improved Performance and Scalability
- Cloud servers are optimized for speed. Thus, they provide faster loading and response time. Unlike on-premise setups, cloud platforms like AWS or Azure deliver quick performance, helping apps and websites load instantly.
- Your business doesn’t have to guess future demand. Cloud systems scale based on real-time needs. They possess the ability to adjust on their own without manual effort.
- With data centers across the globe, cloud computing offers faster content delivery to users anywhere. Hence, businesses could serve their global customers with minimal lag.
Significant Cost Savings
- Only pay for what you use with a pay-as-you-go pricing model. This flexibility especially benefits startups and growing businesses with limited and lean budgets.
- You could avoid the upfront investments and high costs of servers, routers, and data centers. As cloud providers handle it all, you could redirect funds to innovation and strategic growth initiatives.
- The need for a large in-house IT team has been eliminated. To clarify, regular maintenance tasks like software updates, patches, and server maintenance are handled by the provider.
Accelerated Deployment and Speed
- Projects that once took months can now be deployed in a matter of hours. Cloud computing removes the wait time for hardware procurement or setup.
- Need a new server or storage space? It’s just a few clicks away. This instant access supports rapid experiments and scaling.
- Cloud computing is more suitable for agile teams. You can test, fail, improve, and launch new features faster, without infrastructure delays that slow you down.
Key Cloud Compliance Standards that Every Business Must Know
GDPR—General Data Protection Regulation
- This regulation applies to any company that handles personal data of EU residents, regardless of its location outside the EU. Key cloud responsibilities include encrypting stored and transferred personal data. Additionally, it facilitates user requests such as access, deletion, and data portability. It also guarantees legal cross-border data transfers, such as through Standard Contractual Clauses.
- Under Article 28, cloud providers (processors) must meet strict contractual and technical safeguards. For example, a US-based SaaS firm that stores EU client data on AWS must ensure that AWS complies with GDPR requirements as a data processor.
HIPAA – Health Insurance Portability and Accountability Act
- U.S. healthcare providers, insurers, and any business dealing with PHI (Protected Health Information) must comply with this requirement. It requires healthcare businesses to sign Business Associate Agreements (BAAs) with any cloud vendor that handles PHI. Also, apply administrative, technical, and physical safeguards (e.g., access control, encryption, and backup policies). Finally, the regulation requires that regular risk assessments be conducted and that workforce training is provided.
ISO/IEC 27001 – Information Security Management
- The ISO/IEC 27001 standard is globally recognized for its ability to build and maintain an Information Security Management System (ISMS). It proves your security program is structured, risk-based, and audited. Additionally, it helps cloud providers and SaaS firms build customer trust. It encompasses risk assessments, incident response, access controls, and audits.
SOC 2 – System and Organization Controls
- It is specifically tailored for SaaS companies and cloud service providers that manage sensitive data. It focuses on five Trust Service principles: Security, Availability, Processing Integrity, Confidentiality, and Privacy.
- Tailored for tech and SaaS, SOC 2 compliance proves your cloud systems are secure and available. Type II reports play a major role during your sales deals.
OVERCOME CLOUD COMPUTING CHALLENGES WITH CERTPRO
Cloud computing will soon bring revolutionary changes in the services industry and improve product satisfaction. Business leaders have confirmed that cloud computing provides a competitive edge in the changing market. However, as many businesses shift toward a hybrid cloud environment, they face added complexities in managing security. The process requires implementing a robust compliance framework to prevent risk. Strong data security regulations in your organization can reduce the risk of data breaches in cloud systems and help address cloud security challenges more effectively.
CertPro is a consulting and auditing firm that specializes in cybersecurity implementation. We offer services in security compliance and cloud security. CertPro helps Software-as-a-Service (SaaS) companies obtain data security compliance certifications such as GDPR, ISO27001, SOC 2, and HIPAA. In addition, we can help you implement and monitor your organization’s data security protocol. Our auditing professionals can also assist you in creating a register of all cloud infrastructure and services. Hence, our implementing controls in authorizations and regular backup processes can eliminate the risk of data breaches; for more concise information and guidance, contact experts at CertPro.
FAQ
What is cloud computing?
Cloud computing refers to the delivery of computing services, such as storage, servers, and software over the internet. For example, Google Drive lets users store and access files online without needing physical storage devices.
What is hybrid cloud?
A hybrid cloud is a computing environment that combines public and private clouds, allowing data and applications to move between them. It offers flexibility, scalability, and better control over sensitive data and resources.
How does cloud compliance work?
Cloud compliance ensures that cloud services meet industry regulations and security standards. It involves data protection, regular audits, access controls, and working with providers who follow frameworks like ISO, SOC 2, or GDPR.
What are the four models of cloud computing?
The four cloud computing deployment models are private clouds, public clouds, hybrid clouds, and multiclouds.
What are the characteristics of cloud computing?
Cloud computing is scalable, cost-efficient, and on-demand. It offers self-service provisioning, broad network access, resource pooling, rapid elasticity, and measured service. This enables flexible, reliable, and accessible computing over the internet without heavy infrastructure investment.

SUBBAIAH KU
Subbaiah Ku is the Regional Director for CertPro in Oman, bringing a wealth of expertise in process and system auditing. As a seasoned lead assessor, Subbaiah is dedicated to ensuring the highest standards in compliance and security. His unique blend of technical acumen, rooted in Mechanical Engineering, is complemented by a diverse range of certifications and extensive training.
GRC IN CYBERSECURITY: WHAT IT MEANS AND WHY IT MATTERS IN 2026
In 2026, the pressure on companies to manage cyber risk responsibly has never been greater. Regulators demand structured controls, boards want clear risk reporting, and threat actors are becoming more sophisticated. Against this backdrop, GRC in cybersecurity has...
HOW COMPLIANCE AUDIT SOFTWARE IMPROVES AUDIT READINESS
Today, most companies deal with a growing number of compliance regulations. From data privacy standards to security frameworks like SOC 2 and ISO 27001, the list of compliance obligations keeps expanding. At the same time, regulators and external auditors now expect...
Compliance Best Practices in 2026: How to stay ahead of regulatory changes
Why is the implementation of compliance best practices critical for 2026? Compliance in 2026 demands operational proof, not the documentation intent. Regulations change faster, audit scrutiny is higher, and reporting timelines are tighter across privacy,...