COMPLIANCE AUDIT CHECKLIST 2026: A COMPLETE READINESS GUIDE FOR ORGANIZATIONS
As global auditors with years of experience, we have understood one trend. That is, compliance audits won’t arrive quietly. Instead, they show up fast, ask harder security questions, and perform more in – depth analysis than before. In 2026, that pressure is rising to higher levels.
Furthermore, the business market is highly competitive and complex now. The data protection laws keep expanding. Accordingly, the industry – specific compliance regulations grow stricter after every security incident. For business, this feels like handling multiple critical tasks without clear guidance or a roadmap.
What’s also changed is how audits work. Earlier, you could treat them like an annual exercise. That approach of preparing once, passing the audit, and moving on doesn’t hold anymore. Regulators and customers now expect continuous compliance and a stringent security posture from your organization.
Then there comes the evolution of technology. To elaborate, the AI tools now touch customer data, cloud setups change weekly, and most businesses outsource critical products and services with vendors and SaaS partners.
Each of these developments increases risk exposure, and your auditors are aware of this. Therefore, they ask sharper questions and ask them often. That’s where an audit checklist earns its place.
A compliance audit checklist is a structured list of controls, documents, and processes organizations review to prepare for regulatory and cybersecurity audits. Holding a compliance audit checklist is like switching from loose sticky notes to a comprehensive guide.
This guide is designed for CISOs, compliance leaders, founders, and audit leads. It shows what to check, why it matters, and how to stay ready all year.
Tl; DR:
Concern: Compliance audits are no longer yearly events. In 2026, auditors review deeper, ask sharper questions, and expect continuous evidence. To add on, the evolving cloud infrastructures, AI use, vendor risks, and expanding data security standards increase audit pressure. In such a situation, businesses without a solid audit checklist are the ones that face higher compliance costs, audit delays, and loss of business trust.
Overview: This guide defines a compliance audit checklist, explains its importance, and outlines the key steps on how to use it effectively. It clarifies key audit areas and major frameworks like ISO 27001, SOC 2, GDPR, and HIPAA, and shows how checklists support ongoing audit readiness.
Solution: A structured compliance audit checklist brings clarity, ownership, and control. It reduces audit hours, lowers costs, and improves credibility with auditors, customers, and investors. CertPro helps organizations standardize audit preparation, close gaps early, and stay audit – ready to achieve certification on global compliance frameworks and standards.
WHAT IS A COMPLIANCE AUDIT CHECKLIST AND HOW IT IS USED
A compliance audit checklist is a practical guide that helps teams prepare for regulatory audits. It outlines the existing controls, the required proof, and the owner of each task. In simple terms, it addresses a crucial question: are we truly prepared if an auditor conducts a review today?
In real – world work, audits fail less due to missing controls and more often because of a lack of clarity. Files reside in different tools and locations, owners change, and your evidence goes unchecked. But with a proper checklist, you can pull everything into one clear view and bring order to the process.
There are two types to understand. One is the internal audit checklists that help teams review their controls. They are used early and often. The other is the external audit readiness list, which is built with the auditor in mind. They focus on evidence, timing, and how controls will be tested. To sum up, one is for fixing gaps, and the other is for proving maturity. A solid audit readiness program uses both.
During ISO and SOC 2 audits, compliance auditors use these checklists to test whether controls exist and work as stated. For GDPR and HIPAA, checklists guide reviews of data handling, access controls, and incident response plans. Regulators use them to stay uniform and follow one standard parameter across audits and reduce subjectivity. Therefore, detailed checklists that align with their logic simplify audits.
At its core, a compliance audit checklist does four things:
- Defines audit scope and priorities.
- Tracks control coverage across teams.
- Flags missing or weak evidence early.
- Reduces delays during active audits.
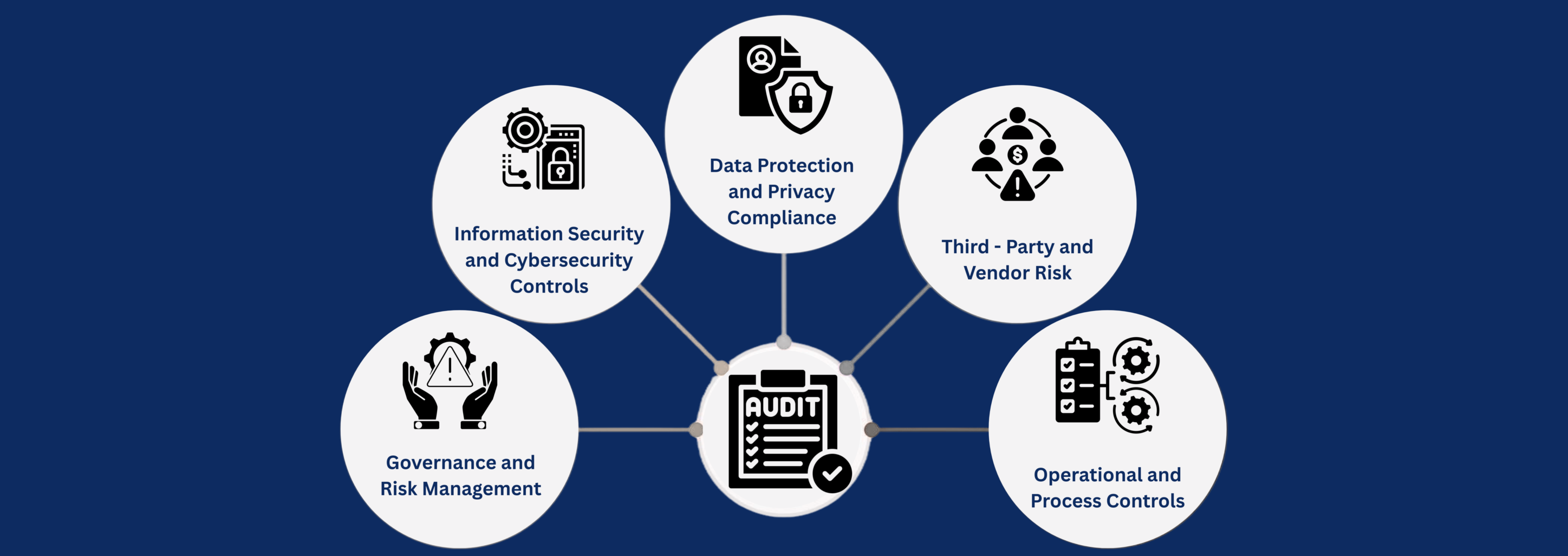
KEY AREAS THAT EVERY COMPLIANCE AUDIT CHECKLIST MUST COVER
A strong audit checklist must reflect how your business actually runs. In 2026, auditors look beyond paper policies. They expect evidence to prove that your controls exist, work, and are owned by people. Here are the core areas that show up in almost every audit, irrespective of the framework.
Governance and Risk Management
This is where accountability starts. Auditors check whether policies exist, but they care more about well – defined ownership. To clarify, they want to know who approves the policies, who reviews risk, and who escalates issues. Risk assessments must be updated and tied to real systems, not copied from last year.
Information Security and Cybersecurity Controls
As you know, the presence of security controls is essential. Auditors test who can access systems, how access is reviewed, and how fast it is removed if found irrelevant. Furthermore, they check your incident response plans and whether teams have practiced them. To add on, clear logs must exist, and they must be reviewed continuously. Encryption should protect data at rest and in transit. Furthermore, the vulnerability scans should run on a schedule, with proper tracking and closure of issues.
Data Protection and Privacy Compliance
Privacy audits focus on how data flows through your business. Here auditors review GDPR obligations, consent records, and data maps. They verify the legal foundation for the data retention duration and ensure its safe disposal. Breach handling is another crucial aspect in an audit checklist. Therefore, the teams must show they can detect, report, and respond within legal timelines.
Third – Party and Vendor Risk
Your risk boundary now also includes vendors. Hence, the auditors expect due diligence and a provable security posture before onboarding. Contracts should include clear security and privacy terms. Moreover, continuous and ongoing monitoring matters rather than one – time reviews.
Operational and Process Controls
These controls keep your digital assets stable. In this context, a change management policy tracks what changed and who approved it, and an asset management policy shows what you own and protect. With solid change management and asset management controls, you can prove your business continuity. This sign of real operational maturity helps you prove to your auditors that you can recover when things break.
COMPLIANCE AUDIT CHECKLIST BY FRAMEWORK AND REGULATION
The simple reason why audits feel complex is that each framework asks similar questions but expects different evidence as proof. A solid checklist helps you to transform your daily operation and controls that match compliance requirements across frameworks and standards.
ISO 27001 and ISO 27701: ISO audits focus mainly on your risk management practices. Auditors start with your ISMS scope and check whether it is clear and updated. They review the Statement of Applicability to see which controls you chose and why. Evidence for managing risks matters here. Therefore, you must show how risks were identified, accepted, reduced, or transferred. For privacy management, ISO 27701 adds how personal data is handled across your firm.
SOC 2 Type I and Type II: SOC 2 is about trust and uniformity. Auditors map controls to the Trust Services Criteria, which includes security, availability, confidentiality, processing integrity, and privacy. Type I audits check your control design at a point. Meanwhile, SOC 2 Type II goes further and tests their operational effectiveness over months.
GDPR and Global Privacy Standards: Privacy audits focus on people’s personal data. Therefore, auditors check the lawful basis for processing and whether consent is true and recorded. Data Protection Impact Assessments (DPIA) matter when risk is high. However, data subject rights, such as access and deletion requests, must be effectively implemented in practice.
Industry – Specific Audits: HIPAA looks closely at safeguarding the Protected Health Information (PHI) and access controls. In parallel, the PCI DSS focuses on protecting the payment data. Both demand strong technical and procedural evidence.
HOW TO USE AN AUDIT CHECKLIST TO ACHIEVE PRE – AUDIT AND ONGOING READINESS
Using a compliance audit checklist well helps teams stay ready without living in audit mode every day. The process is simple, but commitment and order matter.
Audit Scope: Start by scoping the audit. Be clear about which regulations apply and which systems fall in scope. This step saves and helps you pass audits without any obstacles.
Control Mapping: Next, map your controls to the items in the checklist. Every policy, process, or technical control should point to a daily practice and compliance requirement. For example, if access reviews exist, link them to user logs and review records.
Built Accountability: Assign owners and timelines. Audits often fail due to unclear accountability, where everyone owns everything. Therefore, each item needs one responsible person and a clear review cycle.
Evidence Management: Thereafter, collect and validate evidence by checking the dates, approvals, and uniformity. Here, old screenshots and unsigned policies are common audit blockers.
Internal Audit: Conduct an internal gap assessment before auditors arrive. This phase is where your teams catch missing controls or vulnerable areas early. It’s more effective to address gaps internally than explain them under external audit pressure.
Once the audit ends, update your audit checklist by removing outdated items, adding new risks, and capturing lessons learned. As a result, following these steps could turn your audits into continuous progress.
CONCLUSION
In 2026, audit readiness directly affects your compliance cost, trust, and business growth. Hence, a well – maintained compliance audit checklist gives teams control. It reduces scope reworks, reduces audit hours, and lowers reputational risk. When customers, partners, or investors ask tough security questions, prepared teams with a solid audit checklist answer them with evidence.
Organizations that standardize their audit preparation process scale faster. To clarify, they could onboard new tools without fear, expand into new markets, and pass audits without pulling teams away from daily operations.
If you delay it, then you will miss enterprise deals, your external audits could be complex, and you might face recurring issues. In such situations, your team acts fast to fix them soon, only to realize that things have gone beyond repair.
This is where CertPro enters the scenario. CertPro works as a strategic compliance audit partner to help you understand how your business actually operates and achieve compliance using our quality audit approach. Our approach aligns your controls, evidence, and risks across ISO, SOC 2, GDPR, HIPAA, and other global frameworks and standards. We don’t just hand over templates; rather, we help you build readiness, which provides a hassle – free audit and certification process.
If audits feel stressful, fragmented, or expensive, now is the time to collaborate with experts. Connect with CertPro today. Let’s build an audit readiness that saves time and cost with zero business disruption.
FAQ
How to prepare an audit checklist?
To prepare an audit checklist, define the audit scope, list applicable regulations, map controls to requirements, assign owners, and gather evidence. Furthermore, review risks, test controls internally, and update the checklist regularly to stay audit – ready across teams and systems.
What are the common gaps in an audit checklist?
Common audit checklist gaps include unclear scope, outdated policies, missing evidence, weak access reviews, poor vendor oversight, and untested incident response.
What is an ISO audit checklist?
An ISO audit checklist is a structured list of controls and evidence used to assess compliance with ISO standards like ISO 27001. It helps auditors verify risk management, control design, and ongoing effectiveness during certification audits.
What are some audit checklist examples?
Audit checklist examples include ISO 27001 ISMS checklists, SOC 2 control testing lists, GDPR compliance checklists, IT security audit checklists, and internal audit templates. Each example aligns controls, evidence, and responsibilities for specific regulatory or audit needs.
What is included in a compliance audit?
A compliance audit includes reviewing policies, controls, risks, and evidence against legal or regulatory requirements. It covers governance, cybersecurity, data protection, vendor risk, and operations to confirm controls work and meet audit and regulatory expectations.
GRC IN CYBERSECURITY: WHAT IT MEANS AND WHY IT MATTERS IN 2026
In 2026, the pressure on companies to manage cyber risk responsibly has never been greater. Regulators demand structured controls, boards want clear risk reporting, and threat actors are becoming more sophisticated. Against this backdrop, GRC in cybersecurity has...
HOW COMPLIANCE AUDIT SOFTWARE IMPROVES AUDIT READINESS
Today, most companies deal with a growing number of compliance regulations. From data privacy standards to security frameworks like SOC 2 and ISO 27001, the list of compliance obligations keeps expanding. At the same time, regulators and external auditors now expect...
Compliance Best Practices in 2026: How to stay ahead of regulatory changes
Why is the implementation of compliance best practices critical for 2026? Compliance in 2026 demands operational proof, not the documentation intent. Regulations change faster, audit scrutiny is higher, and reporting timelines are tighter across privacy,...