The advancement of technologies and globalization of businesses make cyber threats complex and refined. According to a recent analysis by cybersecurity firm CyberArk, ransomware attackers had a very “successful” year in 2024, targeting nearly 90% of enterprises, up from 89% in 2023. Such occurrences might have disastrous financial repercussions; some experts say damage costs could surpass $265 billion by 2031. Experts predict that 99% of data breaches will happen due to human error by the end of 2025. Therefore, your organization can avoid the risk of cyber threats with proper employee training and education. In addition, your organization must have a robust security framework to mitigate the risk and respond to the incident.
Organizations with industry-specific security compliance and regular monitoring processes help to avoid cybersecurity threats. The trends in cybersecurity threats suggested that the cost of cybercrime was $3 trillion in 2015, which will reach $10.5 trillion by 2025. According to experts, the world will face substantial cyber attacks in 2025, so take proactive approaches to avoid cyber attacks.
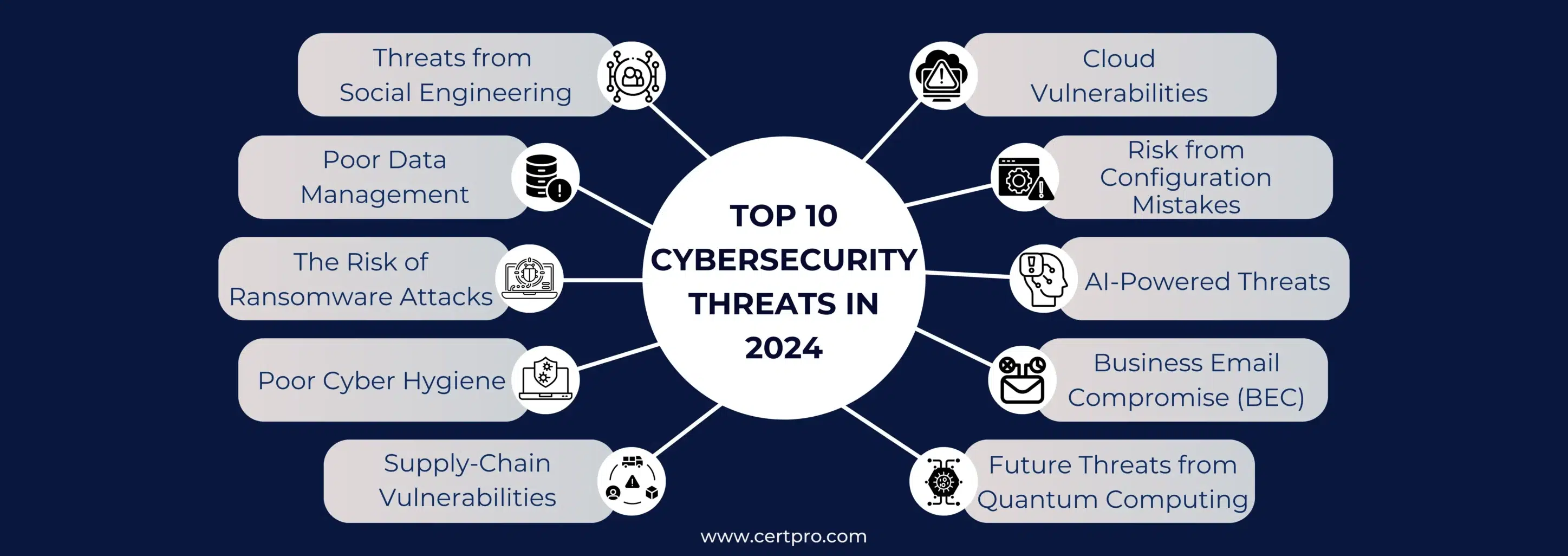
This blog will discuss the top 10 cybersecurity threats in 2025, the latest cybersecurity trends, and how CertPro can help you.
TOP 10 CYBERSECURITY THREATS IN 2025
2025 will be the most complicated year for cloud-based companies, as cybersecurity incidents will increase this year. Let’s discuss some common cyber threat examples and discuss the conditions.
- Threats from Social Engineering: The most common hacking technique relies on human error. Hackers realize that breaking the security posture is difficult; it is easier to wait for human mistakes. In most cases of data breaches, humans are involved. Cyber attacks usually start with malicious mail. In 2023, phishing was one of the top causes of data breaches worldwide. Therefore, hackers are using technologies and tactics to mislead humans. The most common reason for workplace risk is careless human instinct. Employees often use weak passwords, cannot secure their physical devices, mishandle sensitive information, or unintentionally download malicious software.
In addition, poor security hygiene in your organization may increase your trouble. The same incident happened with cryptocurrency attacks in 2021. Due to human negligence, data breaches in blockchain-based currency have increased. Therefore, it is essential to raise employees’ awareness and educate them about current cybersecurity trends. Implementing human risk management can also help identify potential threats.
- Poor Data Management: An adequate data management system is concerned with more than just the data storage and handling process. An effective data management system will find unnecessary data in the record, increasing the vulnerability of cyber attacks. Therefore, mishandling data management systems also increases the risk of data breaches. Thus, in 2025, organizations are shifting to storing the correct data to avoid such risks. The way to mitigate cybersecurity threats is to eliminate unnecessary data from the storage.
In this process, the organization depends on automation, which has multiple risk factors. Hackers can easily manipulate the automation process, and human error can influence the use of AI in this process. Thus, organizations must follow a strict data management framework to avoid these risks.
- The Risk of Ransomware Attacks: The attacks involve malicious software that encrypts the victim’s data. Now, hackers can access your data and make it inaccessible to you. Thus, you have to pay a ransom to access your data. In general, the attacks start with phishing mail or manipulating the network. The hackers always try installing ransomware in your system to lock your data. The result will be a massive payment for the decryption keys of your data. The trends of ransomware attacks show that it ascended from late 2022 and peaked in the first part of 2023. The trend is still high and will continue to grow in 2025. It is assumed that ransomware attacks will occur every 2 seconds by the end of 2031.
Now, what can you do to fight against such risk? Firstly, educate the employees to avoid clicking on suspicious emails or links. Thus, you can also apply advanced email filtering tools to detect ransomware attempts on your systems.
- Poor Cyber Hygiene: Maintaining cyber hygiene is essential for avoiding cybersecurity threats. Therefore, using unprotected Wi-Fi networks, poor data access, and lack of multifactor authentication risk one’s existence. In many organizations, employees donot require passwords to access the company accounts. In addition, only a few employees use two-factor authentication to work in the company’s network. Such incidents increase the risk of data breaches and make the data vulnerable. A study reveals that less than half of Americans agree that they changed their passwords after data breaches. Only a few percent said that they changed their passwords regularly for security.
In this context, the remote work culture has enhanced the cybersecurity threats after the COVID waves. Employees work in unprotected home networks, which increases the risk of stolen data. If your organization has the same issues, fix them before it’s too late. Similarly, IT industries lack cyber hygiene compared to other sectors. Therefore, your organization can improve cyber hygiene by securing its network and authentication process.
- Supply-Chain Vulnerabilities: It appear when hackers infiltrate your systems through your outside partners, such as your software, hardware, or service providers. Hackers quickly access your secure data through these providers. Supply chain attacks can be dangerous as they are challenging to detect and exploit business relationships. Therefore, businesses rely on third-party services; such attacks destroy their businesses. The trends of cybersecurity attacks show that supply chain attacks have increased in the last three years.
Therefore, your organization can ask for industry-specific compliance from the vendors. The contract must mention that compliance is necessary for collaboration. In addition, implementing policy management tools can help your organization manage security policies. Thus, it helps in interaction and cooperation with the vendors.
- Cloud Vulnerabilities: Cloud security is the fastest-growing cybersecurity market. The cloud has become more secure and advanced. However, the exact fact is shocking: IBM reports that cloud vulnerabilities have risen 150% in the last five years. The report suggested that cloud vulnerabilities increased at midpoint in 2023. Now, cloud security has changed to zero trust security. Thus, zero-trust systems require verification at every step despite the recognized devices in the network.
Therefore, the growing market for cloud computing enhances the risk for IT industries. The increasing number of cloud data breaches creates anxiety among cloud users and organizations using the cloud for sensitive data. What can we do to protect our data in the cloud? You can implement GDPR or ISO 27001 compliance to secure your data and choose the vendor with security compliance.
- Risk from Configuration Mistakes: Organizations install cybersecurity software to strengthen their security posture. However, misconfiguration during the installation process makes the whole process vulnerable. In addition, using weak passwords, software updates without security patches, and a lack of firewalls make the scenario critical. One of the most common and easy mistakes people make is not setting up the default usernames and passwords for databases, installs, and devices. Hackers can run several scripted attacks that try different combinations of usernames and passwords on devices. Your systems, databases, and servers must be hardened according to best practices to have the correct security settings.
If you leave these applications or systems in a default or weak state, attackers will have an easier time doing their job. Therefore, you can eliminate the risk of configuration mistakes by educating the staff, automating the process, and establishing a configuration management database.
- AI-Powered Threats: Artificial intelligence (AI) is not only for technological development; hackers can also use the same technology. Hackers can use AI to simplify their jobs, like finding holes in systems, writing phishing emails, or even hacking into the systems. Therefore, hackers use artificial intelligence (AI) and machine learning to create authentic-looking audio, video, or images. The application of technology makes their job simple and less time-consuming. As per PwC, new technologies exacerbated the cybersecurity threats.
In addition, the report talks about how cyber risks are changing as AI technologies are used in many ways to attack what we have to do to mitigate the risk of cyber threats. The main point is to educate the employees. Educate your employees about the specific problems that AI-based threats can cause. Thus, AI-powered threats should be modeled in training situations so that workers learn how to spot and deal with them effectively.
- Business Email Compromise (BEC): It is considered another top cybersecurity threat. Basically, it is a sophisticated scam targeting organizations that deal with international suppliers that regularly perform wire transfer payments. Therefore, a successful BEC can cause massive financial losses for your organization. In addition to losing money, you can also lose your hard-earned reputation with the attacks. The trick is simple: the hackers pretend to be trusted figures who access corporate email accounts and transfer data or funds to fraudulent accounts. It mainly causes financial losses for organizations.
A study introduced that the incidence of BEC increased by 7% in 2023. How do we fight against these hackers? Your organization must practice safe email habits, such as not sending private information, especially banking details, through email. Try to use private file exchanges instead of email attachments. Some cybersecurity companies utilize risk-scoring tools to identify your company’s human threat.
- Future Threats from Quantum Computing: As quantum computing becomes popular and evolves, it threatens existing cybersecurity systems. Cryptography now depends on solving complex math problems that are too hard for old computers to handle. This could be done much faster and automatically with quantum computing. Therefore, quantum computing could break many security methods that protect our data. You should buy quantum-resistant encryption and keep up with the latest developments in quantum technology. Such powerful computers can break public key infrastructures(PKIs) that protect digital communications.
Thus, it could be possible that quantum computing can break any kind of encryption. So, do we have anything in our hands? You can collaborate with cybersecurity vendors to get information about the new technology. Thus, the process of regular updates keeps you awake from cybersecurity threats. In addition, it could help you learn new things and acquire helpful information that you can use to strengthen your security posture.
CERTPRO’S APPROACHES IN MITIGATING THE CYBERSECURITY THREATS
You must first understand the top 10 cyber security threats to protect your organization. Any organization that wishes to safeguard its operations in the digital era has to be aware of possible cybersecurity risks. Businesses today require flexible and adaptive alternatives based on the goals of the firm. You can handle the process of data privacy, security, compliance, and AI monitoring with the aid of CertPro. We have been in the business for a while and know how important data security is to your company.
Our proactive approaches help you to implement a robust data security framework in your organization. We offer auditing and consulting services in GDPR, ISO 27001, and SOC 2. Our professionals guide you in maintaining compliance after the certification process. CertPro’s clients get surveillance audits to ensure the security protocol. In addition, we provide ISO 42001 for an AI management system that reduces AI-related risks. Contact us or visit CertPro.com for more details. Our customer-centric approaches will also strengthen your cybersecurity.
FAQ
What will be the trend in cybersecurity in 2025?
Organizations should improve their cybersecurity measures, such as strong encryption procedures and regular security checks, to protect themselves from supply chain attacks and keep up with new threats.
What is the security month for 2025?
October 2025 is Cybersecurity Awareness Month. The theme for 2025 is “Secure Our World.”
How much will cyber-attacks cost in 2025?
Cyberattacks were thought to cost the world 8 trillion USD in 2023 and 10.5 trillion USD in 2025.
Why is cybersecurity critical?
Cybersecurity is essential as it creates plans to keep our servers, networks, and important data safe. This all-encompassing shield protects against dangers and illegal entry into the vast digital world.
How is quantum computing used in cyber security?
Soon, quantum cryptography will be encrypted data that uses the principles of quantum theory to send and protect data in a way that can’t be broken.

About the Author
SUBBAIAH KU
Subbaiah Ku is the Regional Director for CertPro in Oman, bringing a wealth of expertise in process and system auditing. As a seasoned lead assessor, Subbaiah is dedicated to ensuring the highest standards in compliance and security. His unique blend of technical acumen, rooted in Mechanical Engineering, is complemented by a diverse range of certifications and extensive training.





