GRC IN CYBERSECURITY: WHAT IT MEANS AND WHY IT MATTERS IN 2026
In 2026, the pressure on companies to manage cyber risk responsibly has never been greater. Regulators demand structured controls, boards want clear risk reporting, and threat actors are becoming more sophisticated. Against this backdrop, GRC in cybersecurity has evolved from a back-office task into a central element of enterprise security management.
Many teams still treat governance, risk, and compliance as separate functions, which can create duplicate efforts, overlooked gaps, and limited visibility across the security program. A structured GRC in cybersecurity approach solves this by bringing all three functions into one connected framework.
This blog covers what GRC in cybersecurity means, how its core components work together, why it matters for modern companies, and what its future looks like in 2026. Whether you are building a program from scratch or improving an existing one, this guide gives you a clear picture of where to start.
Tl; DR:
Concern: Cyber threats are growing, and companies face more compliance rules than ever. Without a clear structure, managing security, risk, and oversight becomes fragmented and reactive.
Overview: GRC in cybersecurity brings governance, risk management, and compliance together in one framework. It gives companies a structured way to manage threats, meet legal standards, and stay audit-ready at all times.
Solution: By adopting a GRC cybersecurity program, companies can connect technical controls to business goals, reduce compliance gaps, and give leaders a clear, real-time view of their security posture. This approach builds long-term resilience across the whole organization.
GRC IN CYBERSECURITY
What Is GRC in Cybersecurity?
GRC in cybersecurity refers to the structured integration of governance, risk management, and compliance within a security program. Rather than treating each area in isolation, this approach links them together so that policies, risk controls, and legal standards all work in sync.
In practice, this means that every security decision is guided by a policy, every identified risk has a mitigation plan, and every control is mapped to a compliance requirement. This gives teams a consistent and repeatable way to manage their security responsibilities. As a result, companies can protect their systems more reliably and respond to audits with far less effort.
What Is Governance Risk Compliance?
What is governance risk compliance? It is a structured business approach that brings oversight, risk assessment, and legal adherence together under one program. Companies use this framework to manage operational risks, align their IT controls with business goals, and maintain clear records for regulators.
This concept applies across industries, but it is especially important in cybersecurity. Here, it helps companies set clear rules for how data is handled, how threats are assessed, and how evidence is collected for audits. When done well, a governance risk compliance program removes the guesswork from security management and replaces it with a documented, repeatable process.
How GRC Applies Specifically to Cybersecurity
In cybersecurity, this framework connects technical controls directly to business and legal requirements. It aligns threat identification, access management, and security tracking with governance objectives. For instance, a risk assessment does not just flag a vulnerability. It also maps that vulnerability to a policy and a compliance standard, giving the security team a clear path to remediation.
This connection between technical and business layers is what makes GRC in cybersecurity so valuable. It means that security teams and business leaders are working from the same picture of risk, rather than operating in separate silos.
Why Organizations Combine Governance, Risk, and Compliance
When governance, risk, and compliance are managed separately, teams often duplicate work and miss important connections. An integrated framework removes this overlap and provides leaders with a consistent view of security posture. This makes reporting cleaner, decisions faster, and audit preparation less stressful. Over time, it also fosters a stronger culture of security ownership.
CORE COMPONENTS OF GRC IN CYBERSECURITY
A well-built GRC in cybersecurity program rests on three core components. Each one plays a distinct role, but together they create a framework that balances oversight, threat management, and legal compliance. The table below summarizes how each component works in practice.
| Component | Definition | Key Activities | Role in Cybersecurity |
|---|---|---|---|
| Governance | Oversight and ownership of security programs | Policy development, decisions, audit oversight | Aligns security goals with business objectives |
| Risk Management | Identifying and assessing cyber threats | Risk review, threat modeling, mitigation planning | Helps teams focus resources on the highest risks |
| Compliance | Aligning controls with legal and industry frameworks | Control mapping, tracking, evidence collection | Keeps regulatory standards met and audits on track |
These three components are not independent. Governance sets the rules, risk management identifies where the rules are most needed, and compliance ensures that the rules are followed. When aligned, the program functions as a continuous improvement cycle.
Regulatory Expectations and Business Impact
Companies today operate under more security and compliance pressure than ever before. Standards such as SOC 2, ISO 27001, GDPR, and HIPAA require continuous evidence of control operation.
Cyber incidents now have measurable impacts on revenue, reputation, and customer trust. GRC cybersecurity translates technical risk findings into business-level insights, helping leaders make informed decisions. Structured oversight and reporting provide dashboards and consistent metrics, enabling faster decisions and efficient audits.
KEY PROCESSES IN A CYBERSECURITY GRC FRAMEWORK
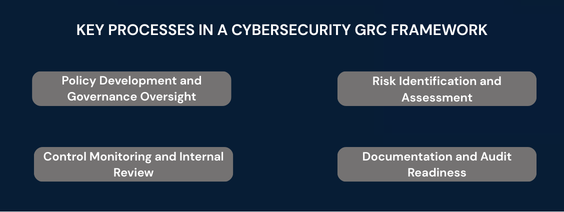
So what is GRC in cyber security when it comes to day-to-day operations? In practice, it is a set of connected processes that keep the security program running in a structured and documented way. Each process feeds into the next, creating a continuous cycle of review and improvement.
Policy Development and Governance Oversight
Policies are the foundation of any strong security program. They define the rules that govern how systems are used, how data is handled, and how security events are reported. Governance oversight ensures these policies are current, enforced, and reviewed on a regular schedule.
Without this layer, security controls lack direction. Even with robust technical tools, teams may lack consistent policies to guide their use. Policy governance ties the technical and organizational sides of security together.
Risk Identification and Assessment
Risk identification is the process of finding and cataloguing every threat that could affect the company’s systems, data, or operations. Assessment then evaluates each threat by asking two questions: how likely is it, and how much damage could it cause?
The answers guide priority. High-likelihood, high-impact risks get addressed first. This stops teams from spreading resources too thinly and helps them focus on what matters most. It is also a core part of how this framework works in practice.
Control Monitoring and Internal Review
Controls are effective only when actively monitored. A misconfigured firewall, a lapsed access review, or a missing patch can all create serious gaps. Control tracking catches these issues before they become audit findings.
Internal reviews add a second layer of assurance. They test whether controls are working as intended and whether the security program as a whole is still aligned with current risks and compliance requirements. Together, tracking and internal review form the backbone of a GRC cybersecurity program.
Documentation and Audit Readiness
At its core, what is GRC in cyber security if not a discipline of good record-keeping? Every policy update, risk review, and control test should be documented in an organized way. This creates a clear audit trail that shows regulators exactly how the security program operates.
When records are kept on an ongoing basis, audit preparation becomes straightforward. Teams do not need to scramble to compile evidence at the last minute. Instead, they simply pull the records that are already organized and ready to share. This is one of the most practical benefits of a well-run GRC in cybersecurity program.
HOW GRC IN CYBERSECURITY SUPPORTS COMPLIANCE AND AUDITS
One of the strongest arguments for GRC in cybersecurity is the direct support it provides during compliance reviews and formal audits. Rather than treating audits as isolated events, a GRC program treats compliance as an ongoing state. This shifts the preparation burden from a few stressful weeks to a steady, low-effort background process.
Mapping Security Controls to Frameworks
Most companies must meet more than one compliance standard at the same time. SOC 2, ISO 27001, GDPR, and HIPAA all have overlapping control requirements. Without a structured approach, teams end up doing the same work multiple times for different frameworks.
This approach solves it through control mapping. A single control can link to multiple frameworks at once. For example, one access review can satisfy both SOC 2 and ISO 27001. This cuts duplicate effort and ensures consistent coverage.
Maintaining Evidence and Documentation
Auditors require documented evidence rather than relying on verbal assurances. They want evidence. Logs, policy approvals, access reviews, and test results all need to be current, accurate, and easy to find. What is GRC in cyber security fundamentally about? It is about maintaining this kind of structured, continuous evidence base.
A good program automates much of this collection. Evidence is gathered and stored on a set schedule, tied to the specific controls being tested. When an auditor requests proof that a control was operating during a certain period, the records are already there. Firms such as CertPro, an independent CPA firm registered under AICPA, work with companies to validate that this evidence meets audit standards and supports formal compliance reviews.
Improving Transparency for Audits
Transparency is one of the clearest benefits of structured GRC work is what it brings to the audit process. When all policies, risks, and evidence are held in one structured system, auditors can navigate the review with far less back-and-forth.
Auditors can see the full history of a control, including when it was last tested and what evidence supports it. This reduces audit timelines and lowers the chance of findings caused by missing records. In turn, it builds trust with regulators and shortens the overall audit cycle.
COMMON CHALLENGES IN IMPLEMENTING GRC CYBERSECURITY
Rolling out a GRC in cybersecurity program is not without challenges. Companies of all sizes run into similar obstacles, and understanding them upfront helps teams plan more effectively and avoid common setbacks.
Data Silos Across Systems: One of the most common problems in a GRC program is fragmented data. Risk records, compliance evidence, and policy documents often live in separate tools that do not connect. This prevents teams from getting a unified view of the security program. Without that visibility, it is hard to spot gaps or report accurately to leadership.
Limited Cross-Team Visibility: These programs require input from IT, legal, security, and business teams. However, these teams often use different tools and speak different languages. Without shared dashboards and clear reporting lines, leadership cannot quickly assess the company’s overall risk posture or compliance status.
Manual Compliance Tracking: Many teams still rely on spreadsheets to track compliance tasks, evidence, and control status. This approach is slow, error-prone, and hard to scale. As programs expand, manual tracking can become a bottleneck, potentially increasing audit risk instead of mitigating it.
Change Management and Team Adoption: Introducing new workflows often meets resistance. Staff may be used to existing processes and slow to adopt new systems. Without clear ownership, proper training, and support from leadership, even well-designed programs can fail to take hold.
Linking Risk to Business Objectives: A key goal of this framework is connecting technical risk findings to business outcomes. However, this connection is often easier said than done. It requires both technical knowledge and business acumen, along with a clear framework for translating one into the other. Building this capability takes time and sustained effort from both security and executive teams.
THE FUTURE OF GRC IN CYBERSECURITY IN 2026
The security landscape is shifting fast. As threats grow more sophisticated and rules expand, companies need more adaptive and automated programs to keep pace.
Artificial intelligence is beginning to play a bigger role in GRC cybersecurity programs. AI tools can scan large volumes of security data, flag anomalies, and flag potential compliance gaps far faster than manual reviews. This shifts the team’s focus from data collection to analytical decision-making, leveraging skilled resources more effectively.
At the same time, cloud-based GRC platforms are replacing on-premise tools. These offer real-time dashboards, automated evidence collection, and cross-framework control mapping. They also make it easier for distributed teams to collaborate on compliance tasks.
Zero-trust security models are also becoming a natural fit for GRC cybersecurity programs. By requiring verification at every access point, zero-trust aligns well with the principle of ongoing control monitoring and documented evidence. This model aligns with the core of GRC in cyber security: maintaining continuous, verifiable evidence of security control operations.
Finally, compliance expectations will keep rising. Regulators will demand more real-time evidence and faster reporting. Companies that invest in GRC in cybersecurity now will be far better positioned to meet these demands as they evolve through 2026 and beyond.
CONCLUSION
As cyber threats grow more complex and regulatory expectations increase, organizations need a structured way to manage security responsibilities. GRC in cybersecurity provides that structure by integrating governance oversight, risk evaluation, and compliance tracking into a single framework. Instead of handling policies, risks, and regulatory obligations separately, companies can align them through a unified system that improves visibility and consistency across the security program.
A well-implemented GRC cybersecurity approach helps organizations monitor controls, document security practices, and maintain reliable records for compliance reviews and audits. It also enables leadership teams to better understand cyber risks and make informed decisions based on clear reporting.
Looking ahead, automation, cloud platforms, and evolving security models will continue to shape GRC in cybersecurity programs. However, the core objective will remain the same: maintaining a transparent, well-governed security framework that supports accountability, resilience, and long-term regulatory readiness.
FAQ
What is GRC in cybersecurity?
GRC in cybersecurity is the structured integration of governance, risk management, and compliance within a security program. It connects policies, threat controls, and legal standards into one consistent framework.
What is governance risk compliance?
Governance risk compliance is a structured approach to managing oversight, risk assessment, and legal standards together. It helps companies align controls with business goals and maintain consistent regulatory records.
Why does GRC matter for cybersecurity programs?
GRC cybersecurity programs bring structure to security management. They reduce duplicate work, improve risk visibility, and ensure that controls meet compliance standards consistently across all teams and frameworks.
How does GRC in cybersecurity support audits?
It keeps evidence organized, controls mapped to standards, and audit trails complete at all times. This means companies can respond to audit requests quickly and with far less last-minute effort.
What are the main challenges in GRC cybersecurity?
Common challenges include data silos, manual tracking, limited cross-team visibility, and difficulty linking technical risk to business goals. These require clear processes, the right tools, and strong leadership support.
HOW SOC 2 COMPLIANCE SOFTWARE CHANGES AUDIT READINESS
There's a version of SOC 2 preparation that most security teams know too well. The audit date is approaching. Someone sends a spreadsheet asking for access logs, vendor assessments, and approval records. People scramble. Documentation gaps appear. What should take...
HOW SOC 2 TYPE II CERTIFICATION IMPACTS CUSTOMER CONFIDENCE AND DATA SECURITY
Enterprise buyers changed how they evaluate vendors. They no longer trust self-reported security claims. Instead, vendor risk management became a top priority. Consequently, procurement teams demand independent proof. They need verification that vendors protect their...
SOC 1 VS SOC 2: WHICH REPORT YOUR CUSTOMERS ACTUALLY ASK FOR
If you sell SaaS or provide outsourced services, you have likely been asked for a SOC report. However, the follow-up question is rarely easy to answer: do they mean SOC 1 or SOC 2? Both reports fall under the AICPA’s System and Organization Controls (SOC) reporting...