Staying compliant today is no longer optional but a vital business requirement. Businesses across sectors, from finance, healthcare, and SaaS, must prove they follow strict data privacy laws. Plus, the regulators demand proof to ensure your regulatory compliance. To add on, your auditors would also review that evidence by asking hard questions. Even one small oversight could lead your business to fines or lawsuits, which could damage your reputation. This is where SIEM tools (Security Information and Event Management) gain prominence. These tools help you track, prove, analyze, and maintain compliance in real time. To elaborate, the SIEM tools collect logs, monitor systems, and trigger alerts when something goes wrong. In particular, they automatically create detailed audit trails and reports. This makes life easier when an auditor shows up at your door.
Whether you’re aiming for ISO 27001, SOC 2, HIPAA, GDPR, or PCI DSS compliance, SIEM security tools help check access control, data integrity, incident response, and log monitoring. If you’ve ever struggled with organizing logs, tracking down security events, or struggling to prepare for an audit, you’re not alone. The right SIEM setup can turn a stressful process into a smooth, ongoing practice.
In this guide, you’ll learn in detail about SIEM tools and how to choose one according to your compliance needs. Additionally, we will explain how to use it without confusing your team. Let’s make compliance one less thing to worry about.
Tl; DR:
Concern: Maintaining compliance with standards such as ISO 27001, SOC 2, HIPAA, or GDPR is challenging. Because one missed log or unmonitored event can lead to serious fines, lawsuits, or audit failures.
Overview: SIEM tools (Security Information and Event Management) help businesses collect logs, monitor threats, and generate audit-ready reports automatically. Furthermore, they track security events in real time and build tamper-proof audit trails for easy compliance proof.
Solution: With the right SIEM tool and proper setup, you can streamline compliance tasks, reduce risk, and impress auditors. Therefore, this guide shows how to pick the right SIEM, set it up correctly, and use it to stay fully audit-ready at all times.
WHAT ARE SIEM TOOLS, AND HOW DO THEY MATTER FOR COMPLIANCE?
A SIEM (Security Information and Event Management) tool functions as the central hub for your cybersecurity and compliance operations. To clarify, it watches everything, gathers data from across your systems, and makes sense of what’s going on in real time.
At its core, SIEM has a dual purpose:
- Detect security threats before they cause damage
- Prove to regulators and auditors that your controls are working
Have you ever tried to pull together logs manually for an audit or trace a suspicious login? If the answer is yes, then you know how frustrating and time-consuming it is. However, SIEM tools fix that and ease the process of staying audit-ready. They automatically collect logs from servers, devices, apps, and cloud platforms. Additionally, they correlate events that look harmless on their own but become suspicious when viewed together. For instance, consider that someone logs into your system at 2 a.m. from a foreign IP, accesses sensitive files, and disables a security alert. A good SIEM tool would spot that, send you an instant alert, and log every detail. That alert, and the surrounding evidence, becomes part of your audit trail.
Key Features of SIEM tools:
- Data collection
- Live monitoring
- Instant threat alerts
- Clear audit trails and insights
SIEM tools also give you clear dashboards and reports. This feature helps you demonstrate the effectiveness of your control to your auditors and ensure regulatory requirements. The regulators and auditors want proof, and SIEM security tools give it to them. They don’t take your word for it anymore. They want data, patterns, and timelines. Tools of SIEM security deliver all of that and help you sleep better knowing your systems are being watched, even when you’re not.
HOW TO IMPLEMENT SIEM TOOLS FOR AUDIT READINESS: A STEP-BY-STEP PROCESS
Getting the SIEM tools up and running is not as simple as just plugging them in. To truly support your audit readiness, you need a well-planned approach. Here’s a step-by-step process to help you avoid common mistakes and pass audits with confidence.
Define your Compliance Scope
Start by asking a few relevant questions, like, what regulations apply to us? Consequently, map out which systems store sensitive data, what controls are needed, and which teams are involved. Whether it’s GDPR, ISO 27001, HIPAA, or SOC 2, clarity here helps you focus your efforts.
Choose the Right SIEM Tool
Pick a SIEM that offers built-in compliance templates. For instance, certain tools pre-install ISO 27001 or GDPR-specific dashboards. These features save you hours of manual work and help you meet reporting standards faster.
Connect all the Right Systems
Your SIEM is only as strong as its visibility. So integrate it with your cloud platforms (like AWS or Azure), internal servers, databases, firewalls, and even endpoints. Thus gaining full coverage to build trust with auditors.
Set up Correlation Rules
Please instruct your SIEM security to monitor for unauthorized access, unusual login times, or large data transfers. These rules help detect violations that matter for compliance.
Configure Log Settings
Decide how long to store logs, where to archive them, and how to protect their integrity. Various standards necessitate distinct retention durations. So, maintain accuracy in this context.
Turn on Reporting and Dashboards
Set up automated compliance reports. This procedure lets you walk into any audit with solid, timestamped evidence in hand.
Do this right, and your SIEM becomes your audit-readiness guardian.
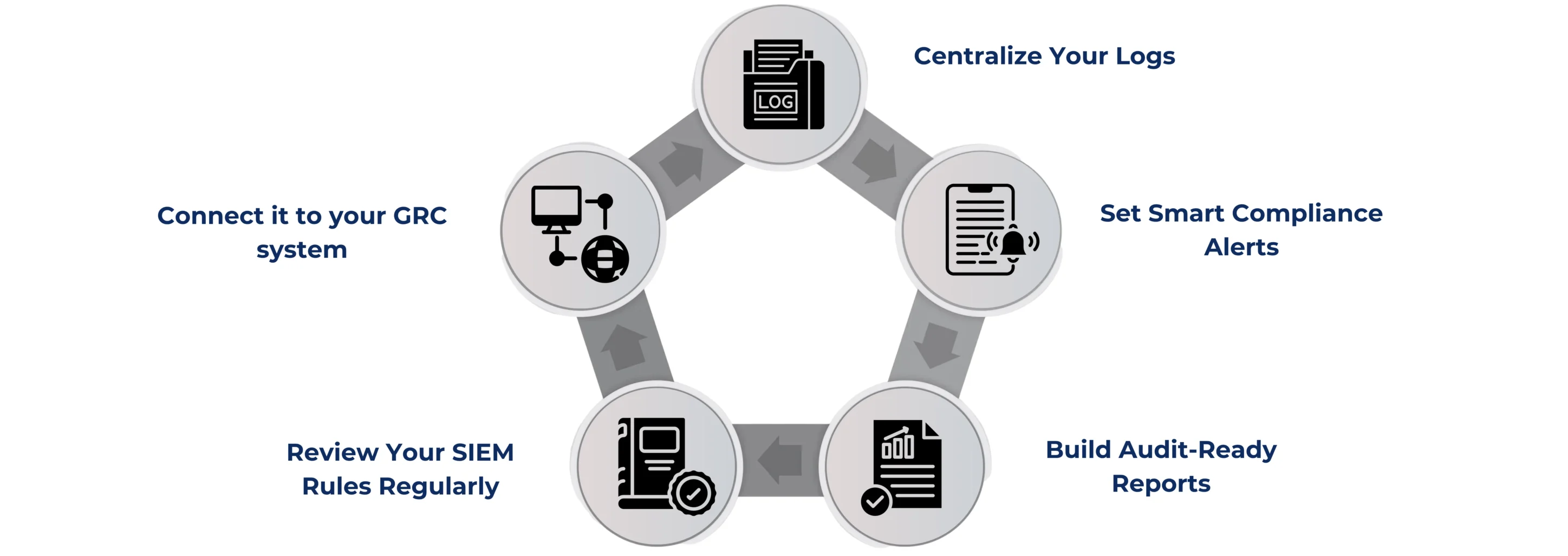
BEST PRACTICES FOR USING SIEM TOOLS FOR CONTINUOUS COMPLIANCE
Installing a SIEM tool is only half the job done. To truly assist with compliance, you must consistently manage it properly. The following best practices will help you get the most from your SIEM and ensure regulatory compliance.
Centralize Your Logs
Don’t just monitor your firewall or server. Moreover, pull logs from everything, like your cloud platforms, endpoints, web apps, VPNs, databases, and more. If your SIEM security tools miss a log, then your auditor might miss it too. Therefore, centralization gives you a complete picture and prevents weaknesses.
Set Smart Compliance Alerts
Create alerts for real risks, like logins after hours, repeated access failures, or admin-level privilege changes. As a result, these alerts help you spot compliance issues before they become audit failures.
Build Audit-Ready Reports
Different standards have different needs. Accordingly, your SIEM tools should generate reports that match ISO 27001, SOC 2, HIPAA, or whatever regulation you’re focusing on. Automated and framework-specific reports simplify audit preparation, eliminating the last-minute rush.
Review Your SIEM Rules Regularly
Your environment changes, so should your SIEM rules. Therefore, set time each month to check which alerts are useful and which ones aren’t. Clean up the unwanted and unnecessary noises, fine-tune thresholds, and close gaps.
Connect it to your GRC system
If you use a GRC (Governance, Risk, and Compliance) tool, integrate it with your SIEM. The integration gives you consistent tracking from detection to documentation. Consequently, SIEM security boosts and organizes your audit trails more effectively.
KEY BENEFITS OF USING SIEM TOOLS
SIEM tools are not just for identifying threats. Rather, they are the core part of your security compliance strategy. They help reduce audit stress, lower the risk of penalties, and bring structure to how your team handles data and incidents.
Real-Time Threat Detection
SIEM tools help you catch issues as they happen, not days or weeks later. With SIEM security in charge, you can spot unusual logins, failed access attempts, or unauthorized file changes immediately. Such detection prevents security incidents from turning into compliance violations. For example, if someone tries to access sensitive HR data from an unknown IP address, the system can alert your team in seconds.
Centralized Log Management
One of the biggest audit challenges is dealing with disconnected systems. SIEM tools pull logs from every part of your environment, including the cloud, servers, laptops, apps, and more. Such data gives you full visibility and prevents gaps that auditors will question. SIEM platforms also protect the integrity of log files through encryption and role-based access control. These features help ensure only authorized users can view or modify the audit logs.
Automated Compliance Reporting
Instead of scrambling to build reports manually, you can use pre-built templates for standards like ISO 27001, SOC 2, GDPR, HIPAA, or PCI-DSS. These SIEM platforms generate audit-ready reports fast, helping you save time and stay compliant. Hence, SIEM security tools ensure regulatory compliance, save time, and reduce human errors.
Improved Audit Trail Accuracy
SIEM logs are time-stamped and tamper-resistant. As a result, they show exactly who did what and when. Thereby, building trust with auditors and keeping your records airtight.
HOW TO CHOOSE THE RIGHT SIEM TOOL FOR YOUR BUSINESS
Choosing the right SIEM tools plays a major role for businesses. Especially when you’re balancing security compliance and limited resources. With the right approach, you can pick a solution that fits your needs without overpaying or overcomplicating things. Monitor the following factors when selecting SIEM tools.
Understand Your Compliance and Security Requirements
Start by clarifying your security compliance obligations. Are you under ISO 27001, HIPAA, SOC 2, or GDPR? Each one has distinct requirements for reporting, log retention, and monitoring. Therefore, make a checklist of what you must track. Also, consider the frequency of your audits, as it impacts your reporting features.
Assess Your IT Environment
Are you a small business or a global enterprise? If your business is smaller, you might not require the advanced features of an enterprise-grade SIEM. Check your business setup. Is it on-premises, in the cloud, or hybrid? Moreover, count your log sources, like servers, endpoints, cloud apps, and databases.
Look for Built-in Compliance Support
Great SIEM tools come with prebuilt templates for GDPR, ISO 27001, and more. These features save hours of manual setup. Also, check if it creates audit-ready reports and supports data correlation. So, you can easily track down events if something goes wrong.
Consider Ease of Use and Deployment
Some SIEMs are painfully complex. Therefore, choose one with a clean interface and AI-powered insights. Always look for tools that are easy to use. This applies not only to you, but also to your team.
Compare Cost vs Value
Don’t just chase the lowest price or the biggest brand. Compare costs for licensing, storage, and support against your requirements. Therefore, a simple and reliable SIEM security solution is often more effective than a flashy one that includes features you may never utilize.
CONCLUSION
Relying on spreadsheets, scattered logs, or last-minute audit prep puts you at risk. Because compliance today moves fast. Moreover, the regulators want real-time proof, not promises. Not to forget, your auditors expect accurate logs and structured reports, not excuses. That’s why investing in smart, compliance-ready SIEM security solutions is necessary. But startups and growing businesses don’t have the time, staff, or expertise to configure SIEM tools properly. So, they end up with expensive, bloated tools they can’t fully use. That’s where CertPro steps in. At CertPro, we don’t just help you pick a SIEM tool; we help you use it to its full compliance potential.
Partnering with CertPro gets you:
- Step-by-step SIEM implementation aligned with ISO 27001, SOC 2, HIPAA, or GDPR
- Clear, tamper-proof audit trails your auditors will trust
- Real-time alerts that stop violations before they become fines
- Expert guidance to help your team stay focused and confident
We have partnered with industry-leading SIEM tools to ensure robust regulatory and security compliance for your business. Talk to CertPro today, and let’s build a compliance system that grows with your business in a simple, secure, and audit-ready manner from day one.
FAQ
What is a SIEM tool?
A SIEM (Security Information and Event Management) tool collects and analyzes log data from across IT systems. It helps detect threats, monitor activity, and support compliance by providing alerts, reports, and audit trails.
What are some SIEM tool examples?
Popular SIEM tools include Splunk, IBM QRadar, LogRhythm, Sumo Logic, and Microsoft Sentinel. These tools help businesses track security threats, manage logs, and stay compliant with standards like ISO 27001 and SOC 2.
What are the objectives of data retention?
Data retention aims to ensure compliance, reduce legal risk, optimize storage, support audits, and protect sensitive information by keeping data only as long as necessary for business or regulatory purposes.
What are three types of SIEM tools?
The three main types of SIEM tools are on-premise SIEM, cloud-based SIEM, and hybrid SIEM. Each type offers different features for managing security events, compliance reporting, and real-time monitoring across your systems.
What is the difference between antivirus and SIEM?
Antivirus software protects individual devices by blocking malware. A SIEM tool, on the other hand, monitors your whole IT system. It detects threats, tracks logs, and supports compliance across servers, apps, and networks.

About the Author
RAGHURAM S
Raghuram S, Regional Manager in the United Kingdom, is a technical consulting expert with a focus on compliance and auditing. His profound understanding of technical landscapes contributes to innovative solutions that meet international standards.
GRC IN CYBERSECURITY: WHAT IT MEANS AND WHY IT MATTERS IN 2026
In 2026, the pressure on companies to manage cyber risk responsibly has never been greater. Regulators demand structured controls, boards want clear risk reporting, and threat actors are becoming more sophisticated. Against this backdrop, GRC in cybersecurity has...
HOW COMPLIANCE AUDIT SOFTWARE IMPROVES AUDIT READINESS
Today, most companies deal with a growing number of compliance regulations. From data privacy standards to security frameworks like SOC 2 and ISO 27001, the list of compliance obligations keeps expanding. At the same time, regulators and external auditors now expect...
Compliance Best Practices in 2026: How to stay ahead of regulatory changes
Why is the implementation of compliance best practices critical for 2026? Compliance in 2026 demands operational proof, not the documentation intent. Regulations change faster, audit scrutiny is higher, and reporting timelines are tighter across privacy,...