In today’s digital landscape, ensuring the safeguarding of client data is paramount for businesses. Adhering to recognized compliance standards is vital to meeting this demand. ISO 27001 vs. SOC 2 represent two prominent benchmarks in the realm of data security with substantial global influence. These standards serve as indicators, aiding companies in constructing robust security frameworks and assuring clients that their vendors are committed to the safeguarding of confidential data.
The American Institute of CPAs (AICPA) established SOC 2, which is especially important for service providers who handle client data. Its approach assesses the safeguards and controls put in place to guarantee the privacy, availability, and integrity of data. In contrast, ISO 27001 is an international standard that is renowned for its all-encompassing approach to information security management. It offers a methodical approach to creating, putting into practice, preserving, and continuously enhancing an organization’s information security management system.
Businesses frequently come under scrutiny in the competitive landscape from potential partners or clients who look for concrete proof of adhering to these criteria. A company’s dedication to data security can be powerfully demonstrated by meeting ISO 27001, SOC 2, or both requirements. ISO 27001 vs. SOC 2 may be chosen depending on regional preferences or industry-specific subtleties as firms traverse the complex world of compliance. However, adopting these standards strengthens a business’s defenses against possible threats and gives customers who are concerned about the risks associated with data breaches confidence. Thus, the comparison of ISO 27001 vs. SOC 2 becomes crucial for businesses hoping to meet and even surpass today’s connected world’s data security requirements.
WHAT IS ISO 27001?
Among the many standards developed by the International Organization for Standardization, ISO 27001 is one that is well-known throughout the world. This specific standard lays out clear requirements for building an effective Information Security Management System (ISMS). A number of techniques, such as risk assessment, access control, and incident reporting processes, are used in the construction of the ISMS.
Organizations that manage consumer data frequently utilize ISO 27001 as a tool to showcase their comprehensive data protection protocols to stakeholders and potential clients. An impartial third-party auditor must conduct a comprehensive evaluation to ensure strict compliance with the criteria for achieving ISO 27001 certification.
WHAT IS SOC 2?
The American Institute of Certified Public Accountants (AICPA) developed the SOC 2 standard, which establishes a framework for documenting the precautions taken to safeguard client information during handling, processing, or storage. This standard lays out requirements that companies must meet, including having the capacity to manage and identify fraud and restrict employee access to data.
To obtain a SOC 2 certification, you must hire an auditor to perform a comprehensive review of your controls and evaluate your adherence to the required standards. The auditor then creates a comprehensive report detailing your security procedures and evaluating whether your company meets the requirements for SOC 2 compliance.
WHAT IS THE DIFFERENCE BETWEEN SOC 2 AND ISO 27001?
There are a number of noteworthy differences between SOC 2 and ISO 27001, the main one being their respective scopes. In order to comply with ISO 27001, businesses must show that they have implemented a fully functional Information Security Management System (ISMS). The goal of ISO 27001 is to create a complete framework that guides organizations in managing their data. On the other hand, SOC 2’s goal is narrower and focuses on verifying that an organization has implemented the necessary data security procedures.
To clarify, SOC 2 focuses on assessing the current security measures, whereas ISO 27001 stresses the creation and ongoing maintenance of an ISMS. For this reason, in order to receive certification, ISO 27001 requires more stringent compliance requirements.
While SOC 2 consists of a set of audit reports produced by an independent Certified Public Accountant (CPA) or accounting organization, ISO 27001 functions as an official international security certification standard. Unlike SOC 2, which can be tailored and adjusted to meet specific industry norms and requirements, ISO 27001 is a prescriptive certification that uses industry-wide standards that can be applied to any industry, regardless of location.
1. Requirements for compliance: The security measures outlined in ISO 27001 and SOC 2 overlap, although there are differences in how much integration of these controls is required between the two standards. Organizations should only implement controls that are relevant to their unique business context, according to SOC 2 and ISO 27001 standards. To comply with the ISO 27001 standard, however, a more comprehensive set of security measures must be implemented due to the standard’s broader range of requirements. The Trust Services Criteria are five different categories into which SOC 2 divides security controls. Interestingly, all SOC 2 reports only need to include one of these categories. Only if the following four controls apply to your goods and services are they required within the context of your SOC 2 report.
2. Distinguishing between Attestation and Certification: When SOC 2 is finished successfully, an independent certified public accountant attests to the data and cloud security strength of the company and presents the results in the form of a thorough SOC 2 report. On the other hand, an ISO Certification Body issues concise certification following a successful ISO 27001 audit, which acts as a benchmark for the creation of an Information Security Management System (ISMS).
3. Relevance of location: In the security and technology sectors, SOC 2 and ISO 27001 are widely recognized; yet, several regions have a preference for one standard over the other. Since SOC 2 is the most widely used compliance standard in North America, doing business with North American firms is likely to demand a SOC 2 report. On the other hand, ISO 27001 is more widely recognized worldwide, which means that it is likely required for any interactions with enterprises outside of North America.
4. Timelines: The process of being ready for SOC 2 compliance takes about six to twelve months, and the path to ISO 27001 compliance takes another six to twenty-four months. These schedules show how committed companies must be to creating and upholding strong security policies that are customized to the unique details of each framework.
5. Duration of Renewal: SOC 2 compliance requires an annual renewal along with an annual audit. On the other hand, ISO 27001 accreditation is only good for three years, and it comes with annual monitoring checks to make sure that the security criteria are still being followed.
6. Scope, Standards, and Controls: SOC 2 dives into detailed controls, with roughly 61 standards across five Trust Service Criteria (TSCs). Security is a must during audits, which are conducted according to the TSC that each organization has chosen. On the other hand, ISO 27001 comprises 14 sections with seven mandatory requirements that house 114 security controls (Annex A). The audit evaluates the Information Security Management System (ISMS) or any of its constituent parts to confirm that the requirements of the standard are being followed. In contrast to SOC 2, ISO 27001 requires surveillance audits to be conducted on a regular basis in the second and third years to guarantee continued compliance with the standards. Furthermore, SOC 2 retrospective assessments concentrate on evidence and do not guarantee the organization’s future operations; in contrast, ISO 27001 accreditation requires partial reviews via surveillance audits in the following years.
7. Presentation: ISO 27001 and SOC 2 employ distinct presentation strategies, offering varying levels of information about your compliance status. ISO 27001 certifies the audit’s success, but it doesn’t provide detailed information on the parts of the system that pass or fail. SOC 2, on the other hand, provides a thorough report outlining the elements that comply with standards and those that don’t. Customers can gain further insight into the operational nuances of your systems with this comprehensive SOC 2 report.
8. Audit Scope: SOC 2 compliance evaluates the design (SOC 2 Type 1) and operational effectiveness (SOC 2 Type 2) of internal controls across particular Trust Service Criteria (TSCs), covering data, personnel, software, infrastructure, and procedure. On the other hand, in stage 1 and stage 2 audits, ISO 27001 evaluates the operational efficacy and design of an information security management system (ISMS) in maintaining availability, integrity, and confidentiality.
9. Report Scope: The SOC 2 report offers a comprehensive overview of the audit, including the independent auditor’s view, the management assertion, a description of the system, a list of controls, and specifics of the tests that were carried out. On the other hand, the ISO 27001 report functions as an audit results document, emphasizing observations, nonconformities, remarks, and favorable findings, and it ends with the certificate being issued.
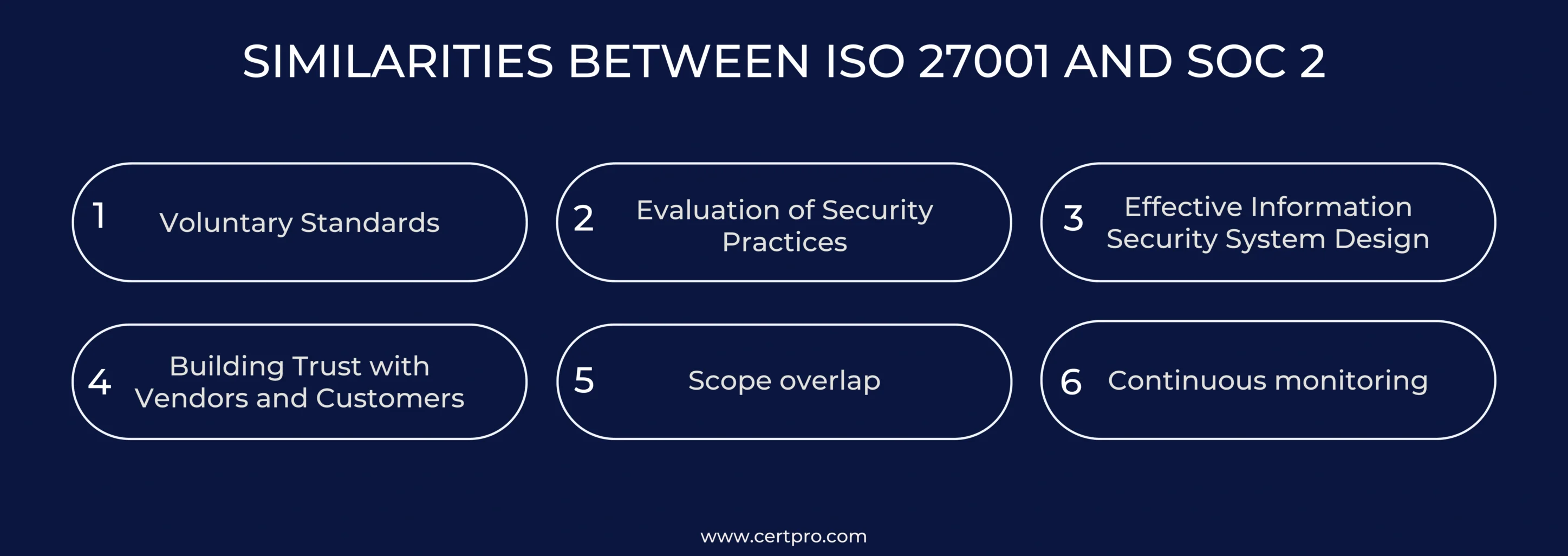
SIMILARITIES BETWEEN ISO 27001 AND SOC 2
Though they have different features, ISO 27001 and SOC 2 have several things in common. Though they differ, the two standards do share some similarities. Explore the subtle parallels between ISO 27001 and SOC 2 that characterize how they line up inside their respective frameworks.
1. Voluntary Standards: Unlike mandatory government-mandated standards like GDPR compliance and HIPAA compliance, ISO 27001 and SOC 2 are voluntary frameworks rather than regulatory mandates. In accordance with their own goals and objectives, organizations voluntarily decide to achieve these criteria.
2. Evaluation of Security Practices: Using internal risk assessment and management procedures, both models help businesses evaluate their current security practices by giving a broad picture of their strengths and weaknesses.
3. Effective Information Security System Design: ISO 27001 and SOC 2 are well-known compliance standards that help businesses create reliable and functional information security systems. To guarantee thorough security measures, this entails combining policies, procedures, and best practices.
4. Building Trust with Vendors and Customers: SOC 2 and ISO 27001 are two often-used techniques that show clients that a company has strong and reliable security procedures.
5. Scope overlap: Between the two frameworks, there is about an 80% overlap in terms of security criteria.
6. Continuous monitoring: Both frameworks require the implementation of continuous monitoring practices to ensure ongoing compliance. Following a successful audit, the company must continue to make regular efforts to maintain compliance with these standards because they are ongoing initiatives rather than one-time tasks.
ISO 27001 vs. SOC 2: WHICH STANDARD FITS YOU THE BEST?
When contemplating the choice between ISO 27001 vs. SOC 2 certification, strategic decision-making becomes crucial, considering the specific requirements of customers. It is not feasible to wait for a client’s request because getting these certificates or attestations takes a significant amount of time. Take into account important elements like the geographic spread of your clientele and industry-specific requirements in order to make an informed choice.
Consider your target market’s primary location. SOC 2 is more common in North America, whereas ISO 27001 is recognized worldwide. Also, evaluate the frequency of each certification in the industries that your customers serve. You’ll find that some industries are more inclined to use SOC 2, while others prefer ISO 27001 standards. Another crucial factor to take into account is the current condition of your information security management system (ISMS). If your data security is still in its infancy, ISO 27001 offers instructions for setting up a strong ISMS. In contrast, SOC 2 helps to incorporate best practices if your system is already developed.
Opting for certifications in both ISO 27001 vs. SOC 2 proves highly advantageous for many companies aiming to serve diverse markets and industries, both domestically and internationally, in North America. This dual certification approach ensures comprehensive coverage, satisfying a variety of customer requirements effectively.
FAQ
Can you pursue both ISO 27001 and SOC 2 certifications simultaneously?
Yes, you can obtain both ISO 27001 and SOC 2 certifications concurrently. Implementing controls for one standard can contribute to compliance with the other due to significant overlapping controls.
Is there equivalence between ISO 27001 and SOC 2?
No, ISO 27001 and SOC 2 are distinct standards. They are not interchangeable, and client requests for one will not be satisfied with certification or a report from the other.
Is SOC 2 mandatory for organizations?
SOC 2 compliance is not a legal requirement, but some organizations insist on it. It is not obligatory, but it may be necessary for businesses engaging with vendors that demand SOC 2 compliance.
What is the difference between SOC 2 and ISO 27001 in terms of their security measures?
While both standards share security measures, ISO 27001 has a broader range of requirements. The implementation of controls in ISO 27001 is more comprehensive due to its all-encompassing nature.
How long does it take to become ready for SOC 2 compliance?
Preparing for SOC 2 compliance typically takes 6–12 months. In comparison, the journey to ISO 27001 compliance can extend from 6 to 24 months.

About the Author
ANUPAM SAHA
Anupam Saha, an accomplished Audit Team Leader, possesses expertise in implementing and managing standards across diverse domains. Serving as an ISO 27001 Lead Auditor, Anupam spearheads the establishment and optimization of robust information security frameworks.
Multi-Framework Compliance Guide: Best Practices and Strategies
SOC 2 FRAMEWORK REQUIREMENTS IN 2026. WHAT HAS CHANGED?
HOW SOC 2 COMPLIANCE SOFTWARE CHANGES AUDIT READINESS
There's a version of SOC 2 preparation that most security teams know too well. The audit date is approaching. Someone sends a spreadsheet asking for access logs, vendor assessments, and approval records. People scramble. Documentation gaps appear. What should take...





