SOC 1 VS SOC 2: WHICH REPORT YOUR CUSTOMERS ACTUALLY ASK FOR
If you sell SaaS or provide outsourced services, you have likely been asked for a SOC report. However, the follow-up question is rarely easy to answer: do they mean SOC 1 or SOC 2?
Both reports fall under the AICPA’s System and Organization Controls (SOC) reporting framework. However, they serve different purposes, address different risks, and go to different audiences. Understanding SOC 1 vs SOC 2 starts with recognizing this distinction. SOC 1 focuses on financial reporting controls. In contrast, SOC 2 focuses on security and day-to-day operational controls. Also, both come in two versions. Type 1 checks the control design at a point in time, while Type 2 checks whether controls operated effectively over a set period, meaning it assesses the performance of the controls over time.
For SaaS companies navigating compliance, a SOC report example can clarify differences in approach and expectations. Choosing the wrong report does not just waste time. It can delay enterprise deals, raise audit costs, and create doubt with buyers. So, getting clarity early matters.
This guide breaks down SOC 1 vs SOC 2 clearly. It covers what SOC 1 report Type 2 and SOC 2 Type 2 involve, walks through a SOC 2 report example, and explains which report your customers are most likely asking for.
Tl; DR:
Concern: Many SaaS companies get asked for a SOC report but are not sure which one. Choosing the wrong report can stall enterprise deals, raise audit costs, and create friction during buying. The confusion between choosing SOC 1 vs SOC 2 is common and costly.
Overview: SOC 1 covers internal controls over financial reporting, while SOC 2 covers security and day-to-day controls. Both come in Type 1 and Type 2 versions. The difference between SOC 1 and SOC 2 reports comes down to your core service’s risk exposure, target audience, and customer expectations.
Solution: Identify whether your customers are asking about financial reporting or data security. For most SaaS (Software as a Service) companies, SOC 2 Type 2 is the report that enterprise buyers expect, as it focuses on data security and operational effectiveness. For financial services and payment platforms, a SOC 1 Type 2 report may also apply, as it assesses the controls relevant to financial reporting.
WHAT IS A SOC 1 REPORT?
A SOC 1 report covers internal controls over financial reporting. The AICPA defines this as controls at a service organization that are relevant to a user entity’s internal control over financial reporting (ICFR). So, if your product processes payroll data or handles billing records that feed into a customer’s books, SOC 1 is right.
SOC 1 reports are reviewed mainly by external auditors, finance teams, and compliance staff focused on financial accuracy. In short, they are not designed to address security risks or data privacy.
SOC 1 Report Type 1 and Type 2
SOC 1 Report Type 1 verifies the proper design of a company’s financial reporting controls. It looks at a single point. So, it answers the question, “Are the right controls in place today?” It doesn’t, however, verify that those controls have been operating reliably. For that reason, Type 1, which assesses the design of controls at a specific point in time, is often used as a first step. It works well for companies that need to show readiness before a full audit period begins.
SOC 1 Report Type 2, on the other hand, goes further. It checks whether those same controls operated well over a defined review period, typically six to twelve months. In practice, most enterprise customers and their auditors ask for a SOC 1 report, type 2. It provides ongoing proof rather than a one-day snapshot. So, finance teams and external auditors rely on it to confirm your controls remained sound throughout the review period.
WHAT IS A SOC 2 REPORT?
A SOC 2 report checks controls related to security and system reliability. It is based on the AICPA Trust Services Criteria. Of these, security is included in every SOC 2 engagement. The others include availability, processing integrity, confidentiality, and privacy. These depend on what your product does and what your customers need.
Unlike SOC 1, SOC 2 is not tied to financial reporting. It applies broadly to SaaS platforms, cloud providers, and tech service companies that handle customer data. A SOC 2 report example can demonstrate how these controls are documented and tested in practice. So, vendor risk teams, IT departments, and enterprise buying teams are the primary audience.
SOC 2 Report Type I and Type II
SOC 2 Type 1 checks whether your security and operational controls are well-designed at one point in time. It answers whether the right controls exist. However, it does not show whether those controls have been running consistently. So, Type 1 works well as a starting point, particularly for companies that need to show a buyer they have controls in place before a full audit period is complete.
SOC 2 Type 2 checks whether those controls operated effectively over an observation period, often six to twelve months. Most enterprise buyers expect SOC 2 Type 2 because it provides ongoing proof that one-time assessments cannot match. Also, SOC 2 reports are restricted-use documents.SOC 2 reports are restricted-use documents. Licensed CPA firms issue them under AICPA attestation standards. They are intended for specified parties such as customers, prospects, and business partners evaluating vendor risk.
SOC 3 reports cover the same criteria but are written for a public audience and can be shared freely.
SOC 1 VS SOC 2: CORE DIFFERENCES AND TYPE 2 DISTINCTIONS
Although SOC 1 and SOC 2 reports follow the same attestation framework, they address different oversight needs. This is the core of the SOC 1 vs SOC 2 comparison that many buyers evaluate. The comparison below outlines the primary structural differences.
| Factor | SOC 1 | SOC 2 |
|---|---|---|
| Core Objectives | Controls over financial reporting | Controls over security and operational reliability |
| Risk Category | Financial misstatement risk | Data security and system risk |
| Primary Audience | External auditors and finance teams | Vendor risk, IT, and procurement teams |
| Common Industries | Payroll, billing, and payment processors | SaaS, cloud, and tech-based firms |
| Most Requested Version | SOC 1 Type 2 | SOC 2 Type 2 |
| Review Period (Type 2) | Typically 6–12 months | Typically 6–12 months |
| Standards | AT-C 320 (SOC 1 examination) | AT-C 105/205 (Trust Services Criteria) |
Beyond these structural differences, the depth and orientation of testing vary in meaningful ways. In a SOC 1 engagement, auditors focus on control activities that affect transaction processing and the accuracy of financial data. When comparing SOC 1 vs SOC 2, the focus on financial accuracy is a key differentiator. This includes evaluating how transactions are authorized, recorded, reconciled, and reviewed.
Accordingly, auditors assess whether these controls operated consistently enough to prevent material errors from affecting a customer’s financial statements. Because user entity auditors may rely on this report during their own audit procedures, the testing approach is closely aligned with financial reporting standards and documentation expectations. Understanding SOC 1 vs SOC 2 helps companies clarify which report aligns with auditor and customer expectations.
By comparison, a SOC 2 engagement focuses on the operational environment that supports data protection and system reliability. Understanding SOC 1 vs SOC 2 clarifies that SOC 2 evaluates controls over security, availability, and confidentiality, rather than financial reporting. Auditors check whether system access is restricted, whether changes are approved, whether monitoring mechanisms detect unusual activity, and whether management follows defined security policies. This distinction is key when customers request SOC 1 vs SOC 2 reports. Evidence typically includes technical logs, security tickets, configuration records, and governance documentation rather than financial transactions.
WHAT’S INSIDE A SOC 2 REPORT: WHAT CUSTOMERS ACTUALLY REVIEW
Knowing what is inside a SOC 2 report example explains why enterprise buyers ask for it during vendor due diligence. A SOC 2 Type 2 report follows a structured format, and each section serves a specific purpose.
It starts with the Auditor’s Opinion. This section states whether the controls operated effectively during the review period. Most enterprise customers read this first because it gives them a quick risk signal. Right after that comes the Management Statement. Here, company leadership confirms that the system description is accurate and that controls were designed and operated as stated.
Next, the report moves into the System Description. This section outlines the systems, software, infrastructure, processes, and boundaries under review. In simple terms, it defines what is in scope. For buyers, scope clarity matters. A strong opinion means little if critical systems fall outside the review.
After scope, the report gets more technical. The Control Activities and Testing Results section lists each control, explains how the auditor tested it, and shows the outcome. If a control failed or did not operate consistently, the auditor records it as an exception. Material issues appear in a dedicated findings section, where details and context are documented.
In practice, enterprise customers focus on three core areas. First, the auditor’s opinion. Second, the scope of systems covered. Third, any exceptions and their severity. They rarely review every single control line by line. Instead, they assess whether identified gaps create meaningful risk and whether management addressed them properly.
When a SOC 2 Type 2 report shows consistent control performance and minimal exceptions, vendor assessments move faster. Procurement teams gain confidence. Security reviews become smoother. That is why preparation before the audit period matters. The quality of evidence, documentation discipline, and control maturity ultimately shape how the final report reads.
WHICH REPORT DO YOUR CUSTOMERS ACTUALLY ASK FOR?
In practice, the report customers ask for depends on what your product does and who is leading the vendor review. For most SaaS companies, the answer is SOC 2 Type 2. Security questionnaires and vendor risk reviews are a standard part of enterprise buying. Buyers want to know that data is protected, access is restricted, incidents are managed, and changes are controlled. SOC 2 addresses all of these directly. When evaluating SOC 1 vs SOC 2, it’s clear that SOC 2 focuses on operational and security controls, while SOC 1 focuses on financial reporting.
Companies in financial services, payroll, or payment processing commonly use the SOC 1 Type 2 report. These companies touch customer financial records directly. So, their customers’ auditors need proof that the controls around those records are sound. Some regulated industries also require SOC 1 as part of their standard vendor review.
When choosing which report to pursue, recognizing the differences between SOC 1 vs SOC 2 can help align customer expectations with your product’s focus. Some companies need both. If your product processes financial transactions and also stores sensitive data, customers may ask for both SOC 1 and SOC 2. In that case, the two reports work together. However, for most tech companies, SOC 2 is the starting point and the most common request.
The shift in buying priorities is worth noting. Data security concerns have moved earlier in the buying process. Vendor risk teams now often lead buying reviews. Also, they ask for SOC 2 before finance teams ask for SOC 1. So, if you are building toward enterprise sales, SOC 2 Type 2 is almost always the first report to pursue.
HOW TO DECIDE BETWEEN SOC 1 AND SOC 2 FOR YOUR BUSINESS
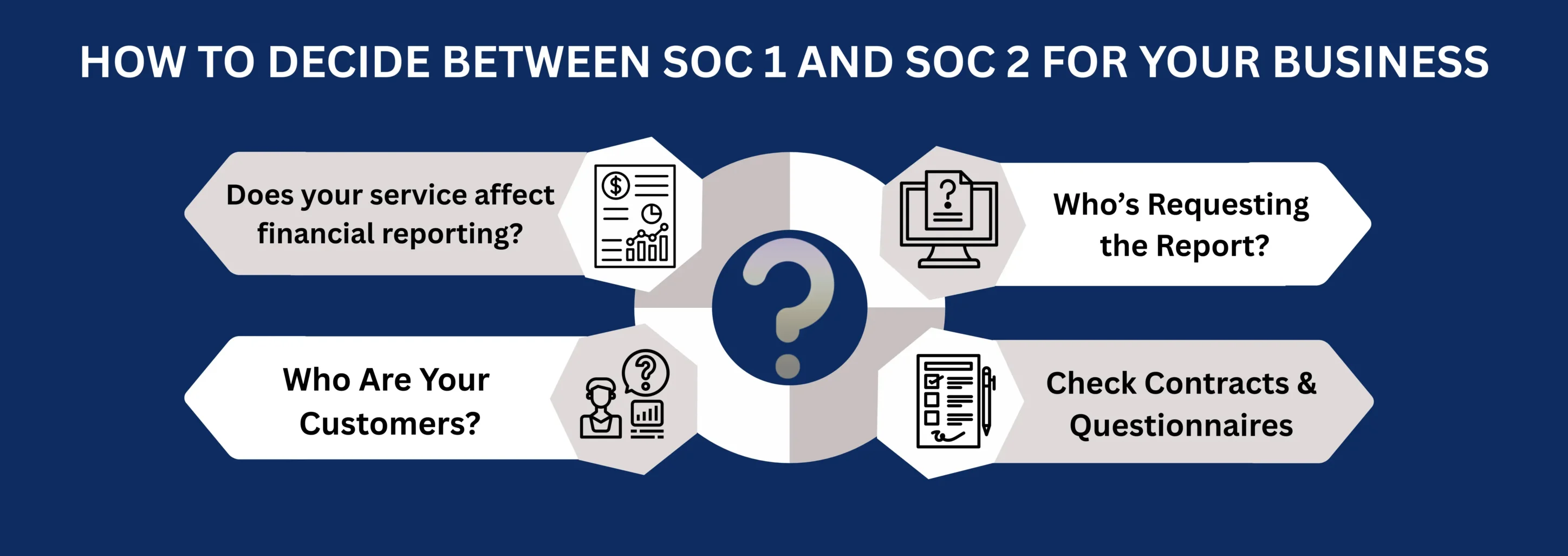
Choosing between SOC 1 and SOC 2 becomes easier when you ask the right questions.
Start with impact. Does your system directly affect your customer’s financial reporting? For example, do you process payroll, manage billing, or support accounting records? If yes, SOC 1 is usually required. However, if you store or process customer data without affecting financial statements, SOC 2 is the logical starting point.
Next, look at who is requesting the report. If the request comes from auditors or finance teams, they are typically asking for SOC 1. On the other hand, if security, IT, or vendor risk teams initiate the review, they usually expect SOC 2. In many cases, the requester makes the answer obvious.
Then consider your customer base. SaaS companies selling to mid-market or enterprise buyers almost always need SOC 2 Type II. Meanwhile, service providers supporting regulated financial institutions may need SOC 1 Type II. If you plan to enter new markets, review local expectations early. Different industries prioritize different reports.
Also, avoid assuming that one report replaces the other. SOC 1 and SOC 2 address different risk areas. One focuses on financial reporting controls. The other focuses on security, availability, processing integrity, confidentiality, and privacy. Review customer contracts and security questionnaires carefully. They usually state the exact requirement.
Finally, think about how enterprise buying works. Security and vendor risk assessments often happen before finance reviews. As a result, many growing SaaS companies prioritize SOC 2 first. Once revenue concentration in finance-heavy clients increases, SOC 1 may follow.
When you align the report with customer expectations, the decision becomes practical rather than confusing.
WHY SOC 2 IS OFTEN THE SMARTER FIRST STEP FOR GROWING SAAS COMPANIES
From a business perspective, many growing SaaS companies choose SOC 2 before SOC 1. The reason is practical: most enterprise buying processes begin with a security review, not a financial audit. This difference illustrates the key distinction between SOC 1 vs SOC 2, helping companies prioritize based on customer expectations. As a result, SOC 2 often removes friction earlier in the sales cycle.
SOC 2 also applies to a wider range of SaaS models. If your product stores, processes, or transmits customer data, enterprise buyers usually expect SOC 2 Type II. Therefore, starting with SOC 2 can accelerate sales and streamline vendor risk assessments.
Key benefits of pursuing SOC 2 first include:
- Shorter security reviews during enterprise sales.
- Stronger positioning in vendor risk assessments.
- Higher trust with IT and procurement teams.
- Support for data protection commitments.
- A clearer foundation for future compliance programs.
However, SOC 2 is not a substitute for SOC 1 when financial reporting risk exists. If your service affects customer financial statements, SOC 1 may still be required. Recognizing the differences in SOC 1 vs SOC 2 ensures companies address both security and financial audit requirements appropriately. In most technology-driven SaaS environments, SOC 2 remains the more strategic starting point.
CONCLUSION
SOC 1 and SOC 2 solve different business problems. Precisely, SOC 1 focuses on financial control reliability, whereas SOC 2 speaks to system security and data protection. Both can be issued as Type II reports, which test how controls perform over time. Yet the value of each report depends entirely on who relies on it.
If your revenue depends on enterprise SaaS contracts, SOC 2 Type II often drives deal momentum. Security and vendor risk teams review it early, sometimes before commercial discussions move forward. However, if your services influence customer financial statements, SOC 1 Type II carries more weight because external auditors depend on it.
Hence, the smarter move is to map your report choice to revenue exposure, customer expectations, security questionnaires, contractual commitments, and the demand for the report in each procurement cycle. That data tells you where audit investment delivers return.
Also, understand the operational commitment behind both reports. Annual testing means controls must run consistently, not occasionally. Evidence collection must become routine, as gaps surface quickly when processes lack discipline.
Treat SOC reporting as part of your commercial strategy. The right report will help you in sales cycles, build buyer confidence, and position your company as low risk. When aligned with customer expectations, deciding between SOC 1 vs SOC 2 becomes a revenue enabler rather than a compliance burden.
FAQ
Are SOC 1 and SOC 2 reports issued by the same type of firm?
Yes. Both SOC 1 and SOC 2 reports are issued by licensed CPA firms in accordance with AICPA professional standards. The firm must be independent of the company being audited. However, the scope, testing procedures, and intended audience differ based on the report type.
Can a company have both a SOC 1 and SOC 2 report at the same time?
Yes. Some companies need both. For example, a payroll platform that also stores sensitive HR data may need SOC 1 to satisfy customer auditors and SOC 2 to satisfy security and buying teams. However, most tech companies start with SOC 2 and add SOC 1 only if customer demand requires it.
How long is a SOC 2 Type II report valid?
SOC 2 Type II reports remain valid after issuance. However, their value depends on how recent the audit period is. Enterprise customers typically look for a report that covers a period ending within the past twelve months. As a result, most companies follow an annual audit cycle to keep their reporting current and aligned with buyer expectations.
What happens if a SOC 2 report has exceptions?
Exceptions are findings where a control did not operate as described during the review period. They do not automatically rule out a vendor. However, customers will review them closely. In practice, buyers want to know the cause of each exception and whether it has been fixed. A clean fix plan matters as much as the issue itself.
Is SOC 2 compliance required by law?
SOC 2 is not a statutory requirement for most private companies. It is an independent assurance report under AICPA standards. However, many enterprise and regulated customers require SOC 2 Type II in contracts or vendor onboarding. In practice, it often becomes a commercial requirement for enterprise sales.
HOW SOC 2 COMPLIANCE SOFTWARE CHANGES AUDIT READINESS
There's a version of SOC 2 preparation that most security teams know too well. The audit date is approaching. Someone sends a spreadsheet asking for access logs, vendor assessments, and approval records. People scramble. Documentation gaps appear. What should take...
HOW SOC 2 TYPE II CERTIFICATION IMPACTS CUSTOMER CONFIDENCE AND DATA SECURITY
Enterprise buyers changed how they evaluate vendors. They no longer trust self-reported security claims. Instead, vendor risk management became a top priority. Consequently, procurement teams demand independent proof. They need verification that vendors protect their...
SOC COMPLIANCE EXPLAINED FOR GROWING SAAS COMPANIES
If you run a growing SaaS company, you have likely heard the term "SOC compliance." It comes up in sales calls, vendor reviews, and enterprise contracts. However, many SaaS teams are not sure what it means in practice, what it costs, or when they actually need it. The...