Data sits at the center of every digital business today. Because of this, companies must protect sensitive information with strong controls. A certification that stands out as the gold standard for confirming that service providers adhere to the stringent guidelines for data security, availability, and confidentiality is SOC 2 (Service Organization Control 2). To elaborate, SOC 2 helps service providers show that they follow high standards for security, availability, confidentiality, privacy, and processing integrity.
This in – depth guide takes a closer look at the complexities of SOC 2 Compliance. It explains the functions of SOC 2 and the people who manage the SOC 2 certification process. Join us as we explore the SOC 2 certification process. Furthermore, we will be clarifying the nuances of the process, which helps businesses identify the essential factors that help them build trust in this contemporary, data – driven ecosystem.
TL;DR:
Concern: Businesses know the importance of the SOC 2 certification process, yet they lack clarity about who handles certification, what the standard covers, and how the process works from beginning to end. Teams often worry about buyer demands, long audit cycles, and the pressure to prove strong security controls without slowing sales. Additionally, they also struggle to understand the Trust Services Criteria and which audit type suits their stage of growth.
Overview: SOC 2 is an auditing standard created by the AICPA. It helps service providers show that their internal controls protect customer data across security, availability, confidentiality, privacy, and processing integrity. Only licensed CPA firms can perform SOC 2 audits. The SOC 2 certification process includes defining scope, fixing gaps, implementing controls, and completing a third – party audit. The Trust Services Criteria guide the auditors in assessing these controls. Companies that store or process customer data, especially SaaS firms and regulated industries, require SOC 2 reports to build trust, meet client expectations, and ensure long – term business growth. In this context, the SOC 2 Type 1 checks whether controls are designed well at a single point. On the other hand, the SOC 2 Type 2 verifies the effectiveness of controls over the course of an audit period.
Solution: A clear and structured SOC 2 program solves confusion and helps teams prove their security posture. Start by defining scope and identifying gaps. Your business must then implement practical controls that align with the Trust Services Criteria. Work with an accredited CPA firm to complete your Type 1 or Type 2 audit based on your business needs and scope. A Type 1 report helps early – stage teams move faster, while a Type 2 report provides stronger proof for enterprise buyers. Continue with ongoing monitoring so your controls stay reliable and audit – ready.
WHAT IS SOC 2?
SOC 2 is an auditing standard created by AICPA (American Institute of Certified Public Accountants). Its primary objective is to help organizations prove their data security practices. In this context, the SOC 2 audit checks whether internal controls meet the AICPA Trust Services Criteria. Namely, these criteria cover security, availability, processing integrity, confidentiality, and privacy. SaaS providers, cloud platforms, and outsourcing partners widely use this standard.
It provides an organized approach to reporting and audits, clarifying the steps taken by companies to ensure the security and integrity of the data they handle. As discussed previously, this standard outlines a set of guidelines, called the Trust Services Principles, that form the basis for evaluating internal controls in an enterprise. Every principle is associated with a unique set of requirements that specify how an organization must comply with the standard.
WHAT ARE (AICPA) TRUST SERVICES CRITERIA?
The Trust Services Criteria, previously referred to as the Trust Services Principles, constitute the foundational components of the SOC 2 framework.
The following section outlines the details of each criterion. Also, it offers a practical example and the process of implementing them:
- Security: Security is one of the mandatory criteria of SOC 2 audits and the attestation process. Here, the service organizations must ensure that they are following secure measures to protect their digital assets. One of the sample controls to ensure security is MFA (Multi – Factor Authentication).
How to implement it:
- Enforce MFA for all admin and engineering logins.
- Review MFA logs every month to track failed attempts.
- Disable old authentication protocols that bypass MFA.
- Availability: According to this criterion, the service organization must uphold the agreed – upon availability standards. This is to assure that the digital assets are available to clients as per their service commitments and business goals. One of the sample controls is the high availability for production systems.
How to implement:
- Use auto – scaling and load balancers.
- Configure backup and failover across two regions.
- Conduct disaster recovery tests twice a year.
- Maintain a log of all downtime and track root – cause fixes.
- Confidentiality: Confidentiality is guaranteed by restricted access to the company’s sensitive data. Here, the auditor assesses security control measures like access restrictions, network and software firewalls, and data encryption. Role – Based Access Control is a good example to use when thinking about privacy standards.
How to implement:
- Create access groups separately for each team.
- Review and approve access requests within a ticketing system.
- Remove unused accounts within 24 hours of exit.
- Encrypt sensitive files with AES-256 (Advanced Encryption Standard).
- Privacy: Privacy principles cover the handling of personal information according to AICPA’s generally accepted principles. This encompasses data like names, addresses, and sensitive details. Therefore, the auditors ensure that control measures prevent the unauthorized access or breach of personally identifiable Information (PII). In this context, privacy notices and user rights workflows could be a better example.
How to implement:
- Keep a clear privacy notice that explains data use.
- Track consent within a CRM or consent – management tool.
- Log subject – rights requests and respond within approved timelines.
- Train employees to handle personal data.
- Processing Integrity: As required by the processing integrity, your system must process data in such a way as to ensure accuracy, completeness, timeliness, validity, and alignment with the main business goals. Here, you can consider input validation for critical workflows.
How to implement:
- Enforce input validation at the API layer.
- Add automated alerts for unexpected processing errors.
- Restrict manual overrides to authorized roles.
- Use audit logs to confirm data accuracy.
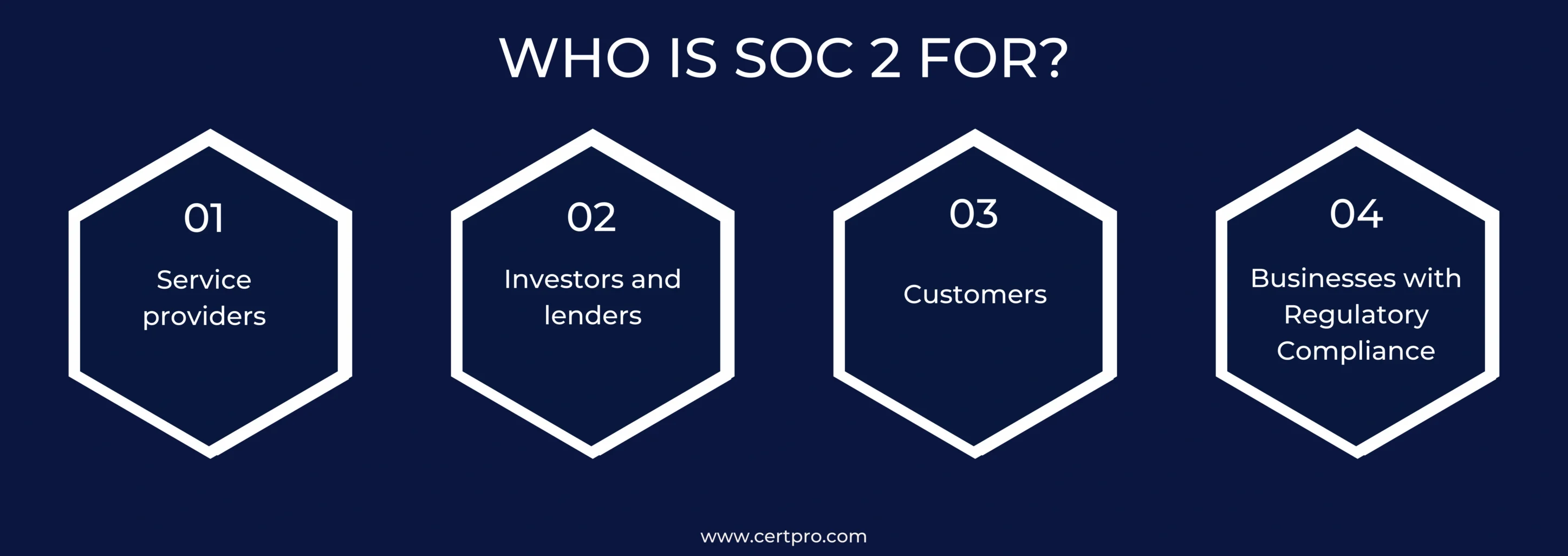
WHO NEEDS SOC 2 CETIFICATION?
SOC 2 is crafted to suit the needs of service organizations and SaaS companies involved in the management or storage of customer data. In simple words, any company that stores or processes customer data can benefit from SOC 2, regardless of size. This is crucial for guaranteeing the security and reliability of their data systems and protective measures.
Following is the breakdown of who can benefit from SOC 2 compliance:
1. Service Providers: Organizations handling customer data through storage, processing, or transmission must prioritize data security and privacy. This includes cloud computing providers, data centers, SaaS companies, managed service providers (MSPs), and financial institutions. Achieving SOC 2 compliance reflects their dedication to data security, building trust and credibility with clients.
2. Early – Stage Startups: Effective data security controls may be a great help to businesses trying to attract investments, and SOC 2 compliance may have an impact on lenders’ or investors’ choices.
3. Customers: Customers reliant on service providers for data management are extremely worried about the security procedures being followed. But SOC 2 certification could help you earn their trust. SOC 2 reports are transparent and reassuring, confirming that the service provider is taking the necessary security measures to protect the customer data.
4. Regulated Industries: Strict data security requirements are mandatory for businesses operating in healthcare (HIPAA), finance (PCI DSS), and other regulated sectors. SOC 2 compliance serves as a crucial step, demonstrating adherence to these regulations. As a result, these industries can also prevent themselves from regulatory fines and reputational harm.
BENEFITS OF SOC 2 COMPLIANCE?
The primary focus of SOC 2 security principles is to prevent unauthorized use of the organization’s digital assets. Let’s learn about the key benefits of SOC 2 compliance in this section.
1. Customer Trust: SOC 2 certification is a clear sign of commitment to secured business practices. This commitment to data security and privacy builds confidence with clients and partners who look for assured practices in the handling of sensitive information.
2. Market Advantage: Obtaining SOC 2 certification sets your business apart from your competitors and establishes you as a business with a solid security posture. Furthermore, this accreditation will boost your sales cycles, as it demonstrates your commitment to strict SOC 2 principles.
3. Data Protection: SOC 2 certification guides businesses to establish and maintain strong security controls. This, in turn, reduces the likelihood of data breaches.
4. Regulatory Requirements: Some industries demand compliance with regulatory requirements, making SOC 2 accreditation a valuable business necessity. Therefore, a company with SOC certification could prove that it is committed to the highest levels of data protection, paving the way to adherence with industry – specific regulatory requirements.
5. Operational Resilience: To achieve SOC 2 compliance, companies often modify their internal policies and workflows to align with SOC 2 requirements. Thereby refining the policies to improve operational resilience and risk management. This process further helps them in reducing the downtime and boosts their risk mitigation procedures.
6. Third – Party Assurance: SOC 2 compliance includes independent third – party audits, offering external validation of an organization’s security controls. This process provides reassurance to stakeholders, including customers, investors, and business partners, as it ensures an unbiased assessment of the company’s commitment to robust security measures.
KEY STEPS INVOLVED IN SOC 2 CERTIFICATION PROCESS
The SOC 2 process is a collaborative process, a structured way to ensure rigorous data security standards are followed. The following are the key steps involved in this process:
1. Establish Your Scope: To initiate the SOC 2 certification process, it is essential to define your scope first. In simple words, identify the specific systems and processes that directly involve or handle client data within your organization. This process helps you determine the scope of the SOC 2 audit. Consequently, specify the Trust Service Criteria (TSC) that align with your service commitments.
2. Conduct a Gap Analysis: Check your current controls against the chosen Trust Service Criteria (TSC) to find areas that need improvement, making sure they meet the required TSCs for SOC 2 compliance.
3. Implement Controls: Implement controls to effectively address the identified gaps. This process includes building access controls, implementing robust data encryption measures, establishing comprehensive disaster recovery plans, and instituting regular monitoring procedures within your organizational policies and service commitments.
4. Obtain a Third – Party Audit: Collaborate with a registered Certified Public Accountant (CPA) firm specialized in SOC 2 audits to evaluate your internal controls according to scope and TSCs. After careful assessment, you will receive a detailed report wherein the auditor expresses their opinion on the level of compliance your organization maintains in accordance with SOC 2 standards.
5. Keep Up Ongoing Compliance: Set up and carry out regular internal audits and risk assessments in your firm to continually assess and confirm that your controls are working as intended. This routine check is essential to keep them effective and adjust the controls according to changing security requirements and risks.
WHAT IS THE DIFFERENCE BETWEEN SOC 2 TYPE 1 AND TYPE 2 AUDITS
As a business, if you’re choosing between a SOC 2 Type 1 and Type 2 audit, the real question is simple. Do you want to show the presence of your controls or prove that they actually work as intended?
A SOC 2 Type 1 report reviews whether controls are suitably designed at a single point in time. Whereas a SOC 2 Type 2 report tests those controls and their operating effectiveness over a period of time.
A Type 1 report focuses on design. It tells the auditor and your customers that your controls look sound on the date of review. For instance, consider a SOC 2 type 1 audit as showing someone the blueprint of a house. Everything seems right on paper. This helps in your early stage of the compliance journey or if you need something sooner to support a sales deal.
Accordingly, the auditor checks your system description, reviews your documentation, and issues an opinion on whether the design is fine or not.
Soc 2 Type 2 goes further by testing whether your controls worked every day during a defined period. If you handle sensitive data, then this gives you confidence that your security posture is consistent.
Here, instead of checking a blueprint, the auditor watches how the house holds up while people live in it. They look at logs, incidents, approvals, backup results, and other evidence collected over time.
Moreover, timing is a key factor to consider. Because you can complete a Type 1 as soon as your controls are in place. But the type 2 report needs an audit window, usually three to twelve months. Many teams start with Type 1, then use the next year to gather steady evidence for their SOC 2 Type 2 audit process.
CONCLUSION
Investing in the SOC 2 attestation process is imperative for service organizations operating in the modern business world. This is because buyers, particularly those who entrust you with their data, demand proof rather than verbal assurance.
Therefore, delaying SOC 2 often slows sales, increases security risks, and creates more pressure during investor reviews. Businesses often realize this only when a deal stalls or a client asks for a SOC 2 report that they cannot provide.
This is where CertPro becomes a reliable partner. CertPro is a registered CPA firm under the AICPA and offers complete SOC 2 audit and attestation services. By collaborating with CertPro, you work with certified auditors who understand the standard at a technical and practical level.
Furthermore, we guide you through the scope, the controls, and the evidence collection process, and we make sure you understand what is relevant for both Type 1 and Type 2.
CertPro also supports you with continuous ongoing compliance. This helps your firm to ensure that your controls function as intended and are ready for any client review. Such assistance is especially helpful for growing SaaS teams that cannot afford long audit cycles or obstacles during procurement.
If you want to start the SOC 2 attestation process or you need help preparing for your next audit period, reach out to CertPro. We help you move forward and turn compliance into a real business advantage.
FAQ
What is SOC 2 certification?
A SOC 2 certification is an independent audit report that shows a service provider follows strong controls around data security, confidentiality, privacy, processing integrity, and availability. It helps customers and regulators trust the provider when handling sensitive data responsibly.
Who can certify SOC 2?
Only a licensed, independent CPA firm can perform a SOC 2 audit and issue the report. The auditors must follow guidance from AICPA (American Institute of Certified Public Accountants), so you get a credible, third – party attestation.
Is SOC 2 the same as ISO 27001?
No, they are not similar. SOC 2 and ISO 27001 both address data security, but SOC 2 focuses on operational controls and audit reports. ISO/IEC 27001 (ISMS) is a formal Information Security Management framework with certification, continuous compliance, and global recognition.
What are the 5 TSCs for SOC 2?
The AICPA’s five Trust Services Criteria (TSCs) are security, availability, processing Integrity, confidentiality, and privacy. Auditors use these categories to assess the proper design and functions of the controls in a service provider’s systems to safeguard client data.
What are the challenges of SOC 2 certification?
Achieving SOC 2 often means building or updating processes, collecting documentation, maintaining logs, and ensuring consistent controls. Here, the key challenges faced by organizations are time, resource, and technical gaps.

About the Author
BHOOMIKA JOIS
Bhoomika Jois is a creative content writer specializing in compliance, ISO 27001, GDPR, and SOC 2. As a Social Media Marketing Specialist, she amplifies her engaging content. Bhoomika’s knack for simplifying complex topics makes compliance and cybersecurity accessible to all.
HOW SOC 2 COMPLIANCE SOFTWARE CHANGES AUDIT READINESS
There's a version of SOC 2 preparation that most security teams know too well. The audit date is approaching. Someone sends a spreadsheet asking for access logs, vendor assessments, and approval records. People scramble. Documentation gaps appear. What should take...
HOW SOC 2 TYPE II CERTIFICATION IMPACTS CUSTOMER CONFIDENCE AND DATA SECURITY
Enterprise buyers changed how they evaluate vendors. They no longer trust self-reported security claims. Instead, vendor risk management became a top priority. Consequently, procurement teams demand independent proof. They need verification that vendors protect their...
SOC 1 VS SOC 2: WHICH REPORT YOUR CUSTOMERS ACTUALLY ASK FOR
If you sell SaaS or provide outsourced services, you have likely been asked for a SOC report. However, the follow-up question is rarely easy to answer: do they mean SOC 1 or SOC 2? Both reports fall under the AICPA’s System and Organization Controls (SOC) reporting...