SOC 2 Type 2 Audit Guide: Scope, Controls, Timeline, and Audit Expectations
If you run a SaaS business today, SOC 2 compliance enters the conversation early. Security sits at the board level, and buyers expect evidence that critical data and systems stay protected under real conditions. Enterprise customers now review security posture before product demos or pricing discussions. They ask for evidence, not assurances. SOC 2 Type 2 audit provides that evidence.
It shows how controls operate over time and how teams manage access, changes, incidents, and risk in daily operations. Leaders who understand these requirements move faster during sales cycles. They answer security questionnaires with confidence and avoid last – minute audits that stall deals.
A clear understanding of SOC 2 Type 2 principles helps teams design controls that stand up to buyer scrutiny. It also supports smoother audits and stronger trust with customers.
Modern buyers look for signals of operational maturity. To clarify, they want to know how data moves through systems, who can access it, and how teams respond to unforeseen security incidents. Policies alone won’t be sufficient to rectify the concerns. Buyers want evidence that controls work in real conditions, over time, under pressure.
Many teams feel prepared because they passed internal checks. However, that feeling changes during sales conversations. Audit – ready teams have controls documented. However, only the sales – ready teams could prove that those controls operated consistently during the audit period. Ultimately, this gap causes delays, surprise requests, and lost momentum.
This guide explains how a SOC 2 Type 2 audit works in practice. Further, it explains the audit scope, control testing, timelines, and what auditors actually examine. You will learn what buyers expect to see and how audit outcomes affect your growth. Moreover, you will get clarity on SOC 2 type 2 controls.
Tl; DR:
Concern: SaaS buyers now demand proof of security before sales conversations move forward. Delays, unclear evidence, or weak evidence slow deals and create friction. Many teams feel prepared internally but struggle to prove that controls worked consistently over time. This gap leads to follow – up questions, extended reviews, and lost momentum during enterprise sales.
Overview: This guide explains how a SOC 2 Type 2 audit works in real conditions. It breaks down audit scope, Trust Services Criteria, and the key controls auditors test, including access control, change management, incident response, vendor oversight, risk assessment, and data protection. It also walks through the full SOC 2 Type 2 audit timeline, from readiness and gap assessment to the observation period, audit fieldwork, and final issuance of SOC 2 Type 2 report. You will learn what evidence auditors expect, how findings affect reports, and what buyers focus on when reviewing results.
Solution: A well – scoped SOC 2 Type 2 audit backed by consistent control execution builds buyer trust and shortens sales cycles. Additionally, working with an independent CPA – led audit firm adds credibility that procurement, legal, and security teams recognize. Thus, a clear SOC 2 Type 2 report answers buyer questions upfront, reduces repeat reviews, and supports faster vendor approval. This approach helps SaaS businesses move from reactive security discussions to confident, evidence – backed growth.
WHAT IS A SOC 2 TYPE 2 AUDIT?
A SOC 2 Type 2 audit shows the effectiveness of your security and operational controls over time. Here, auditors look at access logs, change management records, incident response plans, and approvals across a defined period, often six to twelve months. The report answers a simple question buyers care about: can this company run its systems safely on an ongoing basis?
For instance, consider that you are a SaaS founder who feels confident after passing a SOC 2 type 1 audit. Then a large customer asked a follow – up question. “How do we know these controls actually worked last quarter?” This question led to a stall in the deal. A SOC 2 Type 2 report would have answered it in one step. SOC 2 Type 1 audit shows a control design at a point in time. Meanwhile, the SOC 2 Type 2 principles show control behavior over time. That difference matters during real buying decisions.
When Is the Right Time to Start a SOC 2 Type 2 Audit After Type 1? Most SaaS companies begin a SOC 2 Type 2 audit after completing a SOC 2 Type 1 audit and operating those controls consistently for several months. The key signal here is to prove control stability.
Buyers, partners, and regulators depend on SOC 2 Type 2 audit reports because they reduce assumptions and provide documented evidence of control performance over the audit period.
- Procurement teams use them to speed vendor approval.
- Security teams use them to assess risk without long meetings.
- Legal teams use them to document due diligence.
- Everyone saves time when the report tells a clear story.
To sum up, a SOC 2 Type 2 report becomes your growth catalyst that buyers expect to see. It shows the operational effectiveness of your security controls. This ensures that they are partnering with a security – focused company.
SOC 2 TYPE 2 AUDIT SCOPE: AN OVERVIEW
Defining scope shapes the entire SOC 2 Type 2 audit. It sets clear boundaries around what the auditor will review and what evidence teams must provide. To add on, the scope answers practical questions such as which systems matter, which services touch customer data, and which teams operate those systems. Without this clarity, audits might lose focus, and timelines could expand.
In simple terms, scope covers the systems, processes, and infrastructure that support your service. For most SaaS companies, this includes production applications, cloud hosting platforms, databases, access management tools, and monitoring systems. It also covers supporting services like ticketing tools, CI pipelines, and backup environments when they affect system reliability or data protection. Moreover, auditors follow the data flow of your organization. Therefore, if customer data passes through a system, that system belongs in scope.
AICPA’s Trust Services Criteria guide these decisions. In this context,
- The security criterion always applies. Auditors expect controls around access, logging, and incident response.
- Availability comes into play when uptime service commitments exist.
- Confidentiality applies when your contracts promise data protection.
- Processing integrity matters for platforms that handle transactions or calculations.
- Privacy applies when personal data processing falls under stated policies.
Each criterion enhances the audit’s depth and increases the expectations for evidence.
Scoping choices affect cost, effort, and risk. To clarify, a narrow scope reduces testing but raises buyer questions later. In contrast, a broad scope increases audit work and evidence volume. Balanced scoping supports clean reports and smoother sales reviews. Teams that scope carefully avoid audit rework and last – minute clarifications.
Delays often start with unclear boundaries. This happens when teams forget shared tools, exclude third – party services, or mismatch scope with public descriptions. Hence a clear scope is necessary to keep your audits focused, timelines predictable, and trust intact during vendor reviews
KEY CONTROLS EVALUATED IN A SOC 2 TYPE 2 AUDIT
Security controls show who can access systems, how changes move into production, and how teams react when something goes wrong. Precisely, they reflect habits, not intentions. Here, even your well – structured policies could fail an audit if approvals lived only in private chats. Now, let’s learn about the key controls and policies verified during a SOC 2 Type 2 audit.
Access control sits at the center of every audit. Thereby, auditors check how users get access, how roles change, and how accounts close when people leave. Identity Access Management tools, change approval logs, and periodic reviews matter here. Any weak access trails could raise immediate concern here.
Change management policies show how the code moves forward safely. Auditors look at pull requests, testing records, and deployment approvals. Therefore, a clean trail of change management records reads like a well – kept journal. But random commitments without context slow down reviews and spark security questions.
Incident response plans prove your readiness under pressurized situations. Here, auditors review alerts, tickets, and post – incident notes. They want to see clear ownership and timely action. A fast response with calm documentation builds trust.
Risk assessment ties everything together. Teams document known risks, review them regularly, and track decisions. As a result, their work helps auditors understand your firm’s priorities and tradeoffs.
Vendor management policies focus on third parties that touch systems or data. Contracts, reviews, and risk notes show control over shared responsibility.
Data protection covers encryption, backups, and retention. Furthermore, logs, configurations, and access reports support this area.
Based on real SOC 2 Type 2 audits, the most common issues arise from inconsistent access reviews, undocumented change approvals, and informal incident handling. Teams that centralize evidence early experience fewer exceptions and faster report issuance.
KEY MILESTONES OF SOC 2 TYPE 2 AUDIT
A SOC 2 Type 2 audit runs on a planned structure to avoid confusion, delays, and rushed fixes. Furthermore, understanding the SOC 2 Type 2 audit timeline and requirements helps teams avoid delays and rework.
Typical Timeline Overview: The process starts with preparation, moves into an observation period, and then ends with testing and reporting. Each phase builds on the previous process. Therefore, skipping any step could cause audit rework later.
Readiness and Gap Assessment Phase: In this phase, auditors check whether access reviews exist, whether change approvals show timestamps and owners, and whether incident records include resolution notes. Furthermore, tools get mapped to controls, evidence sources get confirmed, and gaps are identified. Common issues include skipped access reviews, missing deployment approvals, and shared ownership across teams. Businesses must ensure that the fixes are implemented before the beginning of the observation period.
Observation Period: The observation period usually lasts six or twelve months. Controls must operate consistently during this window. To elaborate, access approvals, deployments, incidents, and reviews all leave a trail. Auditors expect clean records of consistent control performance when testing begins. This phase rewards discipline and steady habits.
Audit Execution and Evidence Review: Fieldwork starts once the observation period ends. Auditors request specific evidence samples from across the review window. These include access approvals, change tickets, incident records, and monitoring logs. Moreover, they also schedule interviews with control owners to walk through real workflows. Each sample gets tested against stated controls. In response, teams answer questions, share context, and clarify edge cases.
Report Issuance and Management Responses: After testing, auditors prepare a draft SOC 2 Type 2 report. Management reviews each finding for accuracy and context. When exceptions appear, management adds a written response that explains what happened, why it happened, and how the issue was addressed.
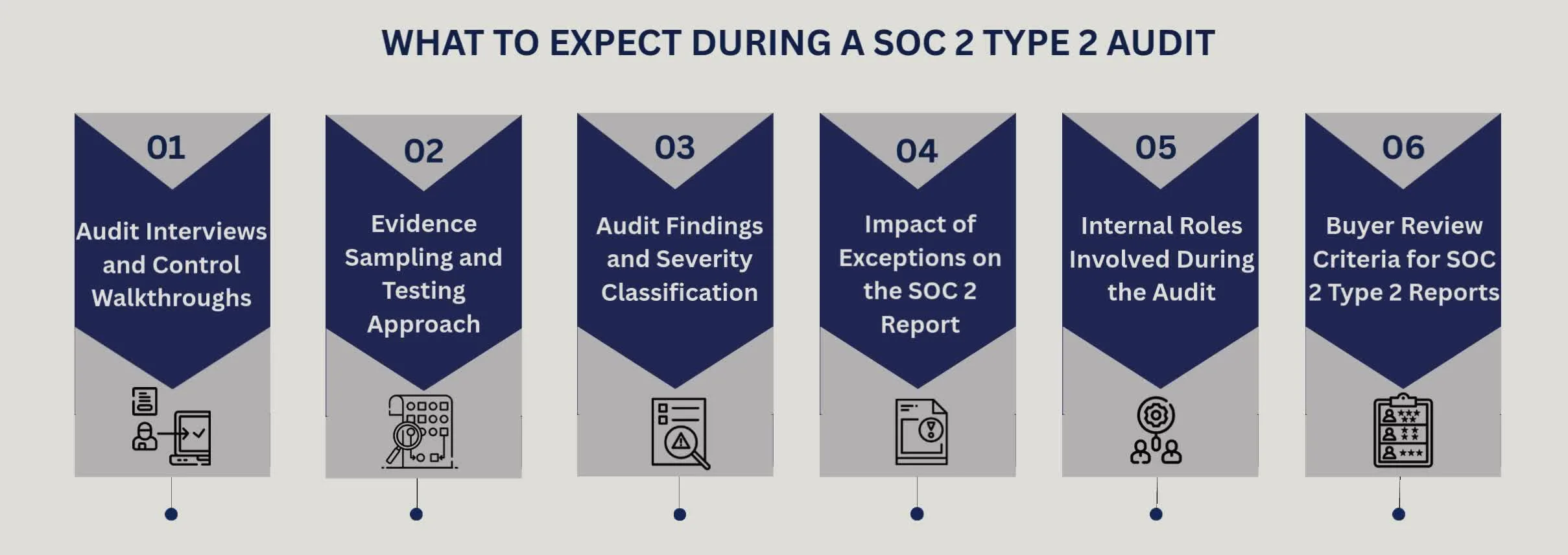
WHAT TO EXPECT DURING A SOC 2 TYPE 2 AUDIT
Most businesses hesitate to begin their SOC – 2 audit because they are unclear about the key processes involved in it. Therefore, in this section, let’s learn about some of the standard processes that an organization could expect during a SOC 2 type 2 audit.
Audit Interviews and Control Walkthroughs
Auditors begin by speaking with the individuals responsible for daily operations. These conversations focus on how work actually happens. Here, you can expect questions about access approvals, incident handling, change reviews, and vendor oversight. Furthermore, walkthroughs follow real tasks. An auditor may ask someone to demonstrate how a user account is created or how alerts are handled. These sessions reveal consistency between written policies and real actions.
Evidence Sampling and Testing Approach
Auditors test evidence through sampling. In simple terms, they select records from across the audit period that include access logs from random months, ticket samples, or change approvals from different teams. Auditors test a small set of records from different points in the audit period. Accordingly, they may review access approvals from several months, change tickets from random releases, and incident logs from both routine and high – activity periods. This sampling shows whether controls worked consistently over time. Thus, clean samples signal steady operations. Meanwhile, missing or inconsistent records point to control gaps. Teams with clear, centralized tracking respond faster and face fewer follow – up requests.
Audit Findings and Severity Classification
Audit findings usually fall into two groups. Minor issues show small process gaps with limited risk. On the other hand, significant issues indicate instances of repeated control failures or the absence of evidence. Examples include delayed access reviews or incomplete incident records. Clear documentation and timely follow – up often prevent minor issues from growing.
Impact of Exceptions on the SOC 2 Report
Exceptions appear directly in the report. Enterprise buyers read them closely. A small exception may raise questions, and multiple exceptions raise concern. Clear explanations and corrective actions could help reduce buyer anxiety. Teams that resolve issues early protect report quality.
Internal Roles Involved During the Audit
SOC 2 Type 2 audits touch many teams. This is to say that security leads guide controls, IT teams provide system evidence, compliance managers coordinate timelines, engineering supports technical questions, and leadership stays involved when findings affect risk.
Buyer Review Criteria for SOC 2 Type 2 Reports
Buyers often focus on the scope, testing results, and exceptions. They look for consistency and maturity in your internal controls. As a result, a clean report shortens reviews and builds trust, and a confusing report slows deals and triggers follow – ups.
A SOC 2 Type 2 audit evaluates whether security and operational controls operate effectively over a defined period. It focuses on evidence, consistency, and operational maturity.
CONCLUSION
A SOC 2 Type 2 audit is the key to securing enterprise deals and ensuring long – term growth. Rephrased security answers, incomplete reports, and weak evidence could undermine their confidence. That’s where the right audit partner changes the outcome.
CertPro CPA LLC is a licensed CPA firm performing SOC 2 examinations under the AICPA peer review program. The firm is led by experienced auditors who focus on quality, standards, and credibility. SOC 2 examinations are performed in accordance with AICPA SSAE 18 attestation standards, ensuring independence and consistency when enterprise buyers, legal teams, and regulators review the report. Furthermore, your teams know exactly what we test, how we evaluate evidence, and how findings land in the final SOC 2 Type 2 audit report.
Beyond SOC 2 type 2 audit, CertPro conducts independent audits and certifications across ISO standards, along with privacy assessments tied to GDPR, CCPA, and HIPAA. This helps growing companies to achieve multi – standard compliance.
Hence, if your sales team faces repeated security reviews, stalled deals, or long questionnaires, the solution is simple. Start with a credible audit report issued by a CPA firm that gains buyers’ trust. Connect with CertPro CPA LLC to move forward with confidence and close deals without friction.
FAQ
Who issues SOC 2 type 2?
SOC 2 Type 2 reports are issued by licensed CPA firms authorized under the AICPA framework. These firms act as independent examiners and evaluate how a company’s controls operate over a defined period using the Trust Services Criteria.
How to prepare for SOC 2 type 2 audit?
Preparation starts with defining audit scope, mapping controls to systems, and documenting daily processes. Teams then fix gaps, assign control owners, and set up clear evidence tracking so controls operate consistently throughout the observation period.
What is the difference between SOC 2 type 1 and type 2 audit?
SOC 2 Type 1 assesses the control design at a single point. SOC 2 Type 2 evaluates operating effectiveness over a certain period of time using real – time evidence. Enterprise buyers often prefer Type 2 for assurance of sustained performance.
How many controls are there in SOC 2 type 2?
There is no fixed number of controls. The count depends on audit scope, systems in use, and selected Trust Services Criteria. Most SaaS companies test between 40 and 100 controls across security, availability, and data handling.
How long is a SOC 2 type 2 valid for?
A SOC 2 Type 2 report reflects control performance over a specific period, usually six or twelve months. Buyers typically expect a new report every year to confirm that controls continue to operate consistently.
HOW SOC 2 COMPLIANCE SOFTWARE CHANGES AUDIT READINESS
There's a version of SOC 2 preparation that most security teams know too well. The audit date is approaching. Someone sends a spreadsheet asking for access logs, vendor assessments, and approval records. People scramble. Documentation gaps appear. What should take...
HOW SOC 2 TYPE II CERTIFICATION IMPACTS CUSTOMER CONFIDENCE AND DATA SECURITY
Enterprise buyers changed how they evaluate vendors. They no longer trust self-reported security claims. Instead, vendor risk management became a top priority. Consequently, procurement teams demand independent proof. They need verification that vendors protect their...
SOC 1 VS SOC 2: WHICH REPORT YOUR CUSTOMERS ACTUALLY ASK FOR
If you sell SaaS or provide outsourced services, you have likely been asked for a SOC report. However, the follow-up question is rarely easy to answer: do they mean SOC 1 or SOC 2? Both reports fall under the AICPA’s System and Organization Controls (SOC) reporting...