In today’s fast-paced digital landscape, ensuring robust cybersecurity measures is imperative for organizations aiming to protect sensitive data and maintain stakeholder trust. The American Institute of CPAs (AICPA) crafted the SOC for cybersecurity reporting framework, offering organizations a valuable avenue to showcase the efficacy of their cybersecurity management program and associated controls. Offering flexibility and devoid of mandatory constraints, this framework serves as a conduit for organizations across diverse industries to articulate pertinent details regarding their risk management endeavors using a straightforward and universally understood language.
Service organizations were the only organizations eligible to take SOC exams in the past. This inclusion, however, now encompasses a wider range of organizational sectors because of the framework’s recent scope increase. This important change makes it possible for enterprises to systematically assess how well their internal controls match cybersecurity threats, which improves their capacity to reassure stakeholders about their dedication to protecting important assets.
SOC for cybersecurity enables comparison analysis with related frameworks such as ISO 27001, allowing firms to compare their cybersecurity activities against established industry standards and discover areas for improvement. In this article, we will look at the importance of SOC for cybersecurity, including its numerous benefits and how organizations can use it to strengthen their cybersecurity posture and promote trust in an increasingly digital environment. Join us as we explore the complexities of the Security Operations Center for data security and demonstrate its ability to protect against the ever-changing spectrum of cyber attacks.
WHAT IS SOC IN CYBERSECURITY?
The phrase “what is SOC in cybersecurity” refers to a centralized unit within an organization that monitors, detects, assesses, and responds to security incidents and issues. The Security Operations Center serves as the main point for defending the organization’s digital assets, including networks, systems, and data, against various cyber threats. A SOC, composed of skilled cybersecurity professionals, continuously scans the company’s IT infrastructure for any signs of criminal behavior or potential security breaches using state-of-the-art tools, technologies, and procedures. When a security incident is discovered, SOC analysts look into it right away, evaluate its implications, and take the necessary action to limit and lessen the threat. Ultimately, by proactively identifying and mitigating cybersecurity threats, guaranteeing regulatory compliance, and reducing the impact of security incidents on business operations, a SOC is essential to an organization’s ability to maintain its security posture.
SOC FOR CYBERSECURITY REQUIREMENTS
The AICPA SOC for cybersecurity testing is based on two major sets of criteria: descriptive criteria and control criteria.
Descriptive criteria serve as the foundation for creating and evaluating the description of your risk management program. Both the entity crafting the description and the practitioner evaluating it utilize these criteria. They include the following sections:
1. Nature of Business and Operations: This part describes the essential features of your organization’s activities and functions, giving context for assessing its cybersecurity posture.
2. Nature of Information at Risk: In this section, you describe the categories of information that your organization handles and how they are vulnerable to cybersecurity risks.
3. Cybersecurity Risk Management Program Goals: This section outlines the particular goals and objectives of your cybersecurity risk management program, which will guide the overall direction and focus of your operations.
4. Risks Associated with Inherent Cybersecurity: Significant Influencers Your business largely influences the inherent cybersecurity risks it faces by recognizing and investigating various aspects of its operating environment.
5. Cybersecurity Risk Governance Structure: This covers the reporting lines, roles, and responsibilities as well as the organizational framework and structure in charge of monitoring and controlling cybersecurity risks.
6. Cybersecurity Risk Assessment Process: It defines the methodology and processes used to detect, analyze, and evaluate cybersecurity threats within your company, providing the foundation for informed decision-making.
7. Cybersecurity Communications and the Quality of Cybersecurity Information: The efficacy and caliber of channels for cybersecurity-related communication and information distribution within your company are the main topics of this section.
8. Monitoring of the Cybersecurity Risk Management Program: In this section, you’ll outline the processes and systems set up to keep an eye on your cybersecurity risk management program and evaluate its efficacy on a regular basis. This will allow you to make necessary adjustments and enhancements on time.
9. Cybersecurity Control Processes: These comprise the particular safeguards and actions put in place to reduce cybersecurity risks and shield important data and assets from possible attacks.
These descriptive criteria can be modified and improved over time as your organization’s awareness of and response to cyber threats change, given the dynamic nature of cybersecurity.
Control criteria, on the other hand, serve as a standard against which the effectiveness of your controls is evaluated. These standards correspond with certain trust service standards and are applied to assess how well your company meets its intended cybersecurity goals.
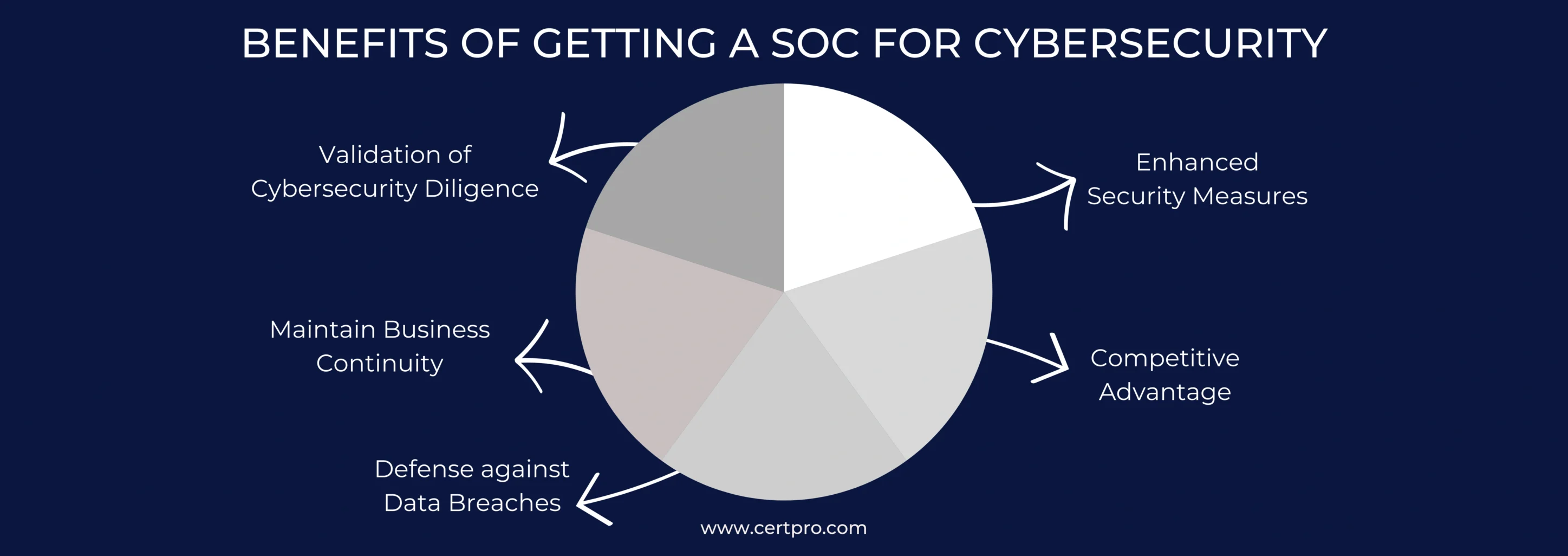
BENEFITS OF GETTING A SOC FOR CYBERSECURITY
1. Validation of Cybersecurity Diligence: Organizations can demonstrate to clients, partners, investors, and internal teams their commitment to cybersecurity by putting themselves through a Security Operations Center for data security test. Through this external validation process, confidence in the organization’s ability to properly protect sensitive data and systems is fostered. Organizations show transparency and accountability by putting themselves through this rigorous evaluation, which strengthens their resolve to keep strong cybersecurity safeguards in place. In the end, this validation improves the company’s standing and fortifies its bonds with stakeholders, establishing it as a dependable and trustworthy player in the digital sphere.
2. Enhanced Security Measures: Implementing the necessary SOC for data security controls strengthens the organization’s overall security posture while also ensuring compliance with legislation. These steps go beyond basic security procedures, strengthening the organization’s defenses against cyberattacks and improving its ability to spot and stop possible breaches. The company exhibits a proactive approach to cybersecurity by strengthening its defenses and more effectively managing risks by going above and beyond simple compliance. In addition to protecting sensitive information and systems, this proactive approach promotes a culture of ongoing cybersecurity practice development.
3. Competitive Advantage: Obtaining a SOC for a cybersecurity report gives businesses a significant advantage over competitors. In today’s digitally driven world, where cybersecurity is critical, having a comprehensive cybersecurity report helps set a firm apart in the eyes of investors, partners, and consumers. This uniqueness and importance have the potential to improve the company’s reputation and credibility in the marketplace. Organizations get a competitive edge in an increasingly competitive market by projecting a trustworthy and credible image through such reports, which showcase a proactive commitment to cybersecurity.
4. Defense against Data Breaches: Security Operations Center for data security reports is an essential tool for internal awareness and preparedness in addition to providing external validation. These reports give staff the ability to identify and fix any security risks by providing an overview of cybersecurity rules and practices. This internal understanding and readiness are essential components of a strong defensive plan against cyberattacks and data breaches. Giving employees this knowledge improves the organization’s overall security posture and encourages proactive risk reduction and awareness in the workplace.
5. Maintain Business Continuity: Even small security lapses can have serious consequences, interfering with operations and possibly having a domino effect on other systems. When it comes to security, prevention is always more important than correction. SOC in cybersecurity gives you a way to evaluate your risk management strategy and find any holes or weaknesses. By taking proactive steps to address these concerns, this review guarantees continuous business operations and protects against future disruptions. Organizations can reduce the effects of catastrophes and ensure business continuity by proactively addressing security risks.
SOC VS CYBERSECURITY
It’s often assumed that “SOC” and “cybersecurity” are synonymous terms, but in reality, they serve distinct purposes within the realm of digital security.
SOC specifically refers to the controls and processes implemented by organizations to manage security risks effectively. This entails proactive monitoring, analysis, and response mechanisms tailored to address cyber threats promptly and efficiently.
Cybersecurity encompasses a broader approach to security, extending beyond the confines of a SOC. It involves a comprehensive strategy encompassing various practices, technologies, and processes aimed at protecting digital assets from a wide range of threats. This includes securing endpoints, networks, data storage, and other critical components against unauthorized access and malicious activities.
FAQ
Who can benefit from SOC for Cybersecurity?
Any organization that wants to enhance its cybersecurity posture and build trust with stakeholders can benefit from SOC for Cybersecurity. This includes businesses of all sizes, from small startups to large enterprises, as well as service providers that handle sensitive information on behalf of their clients.
How often should my organization obtain a SOC for cybersecurity report?
The frequency of obtaining a SOC for a cybersecurity report depends on factors such as organizational size, industry regulations, and the evolving threat landscape. However, it’s typically recommended to undergo assessments at least annually.
Who typically performs SOC for cybersecurity assessments?
Security Operations Center for data security assessments are often performed by certified cybersecurity professionals or third-party audit firms with expertise in security assessment and compliance standards.
Is SOC for cybersecurity mandatory for all businesses?
The Security Operations Center for data security is not mandatory for all businesses, but it is highly recommended, especially for those handling sensitive data or operating in regulated industries.
Can Security Operations Center for data security reports be shared with external stakeholders?
The Security Operations Center’s data security reports can be shared with external stakeholders such as regulators, auditors, business partners, and customers to demonstrate the organization’s commitment to cybersecurity and compliance.

About the Author
RAGHURAM S
Raghuram S, Regional Manager in the United Kingdom, is a technical consulting expert with a focus on compliance and auditing. His profound understanding of technical landscapes contributes to innovative solutions that meet international standards.
Multi-Framework Compliance Guide: Best Practices and Strategies
SOC 2 FRAMEWORK REQUIREMENTS IN 2026. WHAT HAS CHANGED?
HOW SOC 2 COMPLIANCE SOFTWARE CHANGES AUDIT READINESS
There's a version of SOC 2 preparation that most security teams know too well. The audit date is approaching. Someone sends a spreadsheet asking for access logs, vendor assessments, and approval records. People scramble. Documentation gaps appear. What should take...





