The rise of cloud-based business models is an obvious trend in the current corporate world. The vast majority of startups and enterprises are moving toward cloud infrastructure. Additionally, with the rise of remote work, cloud network security has become a top priority for IT leaders. Nowadays, cloud services manage all data, business operations, and applications. Despite their widespread usage, we can’t deny the fact that they come with some challenges. This is why implementing strong cloud security measures is important for modern businesses in 2025. Because, irrespective of how you store or access your data as an organization, it is your sole responsibility to safeguard your customer information. This approach helps you to demonstrate your commitment to data security and privacy. Plus, it also enables you to stay compliant with all the top industry standards like ISO 27001, SOC 2, HIPAA, and GDPR.
Businesses must realize that one misconfigured setting is enough to damage your cloud setup. The worst case is that it could also lead to the loss of sensitive data. However, we can easily prevent all these incidents. The real problem here is relying on traditional cloud security measures to safeguard modern cloud computing systems. Hence, ensuring modern cloud information security practices with 6 key pillars is essential for the survival of your businesses.
So, what is cloud security? In simple words, cloud security is the process of protecting your data, systems, and applications on the internet instead of on your servers. Moreover, cloud infrastructure security is not just about firewalls or antivirus tools. They are the complete protection protocol for your business assets. In this blog, you will learn about all six key pillars of cloud security. To add on, we also explore the benefits, challenges, and best practices associated with cloud security measures.
Tl; DR:
Concern: Modern businesses rely heavily on cloud systems to store and manage data. But with this convenience come serious risks like misconfigurations, data breaches, and compliance violations. Traditional security methods are no longer enough.
Overview: Cloud security is about protecting your data, applications, and infrastructure in the cloud. It involves modern tools and strategies like encryption, access control, and continuous monitoring. The foundation of effective cloud information security lies in six key pillars: Identity Management, Data Protection, Monitoring, Configuration Management, Compliance, and Business Continuity.
Solution: To stay secure and compliant in 2025, businesses must adopt modern cloud security practices. This includes zero trust models, encryption, AI-powered monitoring, and employee training. CertPro helps companies implement strong, compliant, and scalable cloud information security strategies tailored to their needs.
WHAT IS CLOUD SECURITY AND WHY IT MATTERS IN 2025
In 2025, cloud security measures are no longer an option. They are the guardians of modern digital operations. To elaborate, it is the set of tools, policies, and procedures that protects your data and systems in the cloud. This process has several layers, such as security controls, policies, and technologies that work together to keep your cloud infrastructure safe from cyberattacks.
By moving to a cloud-based setup, your company could experience more speed, scalability, and flexibility. But if the system is not secured, you will probably face security issues like data breaches. Also, there are other factors to look for like misconfigurations and unsafe APIs. To clarify, a misconfiguration is when your cloud setting is not set up correctly. For example, leaving a storage bucket open to the public by mistake is a misconfiguration. Likewise, your APIs must be secured to keep the hackers away from them. What businesses need here is strong cloud network security to secure the APIs and log-on pages.
Now, let’s understand the different kinds of cloud services, as each one needs its own kind of protection. They are infrastructure as a service (IaaS), platform as a service (PaaS), and software as a service (SaaS).
- In IaaS, you manage the apps, and the service provider manages the hardware. So your duty is to protect your own operating systems and network.
- In PaaS, you control the app, and the provider manages the platform. So, your focus must be on code and data security.
- With SaaS, you use the software and the provider handles most of the things. Yet, you must ensure secure access and data privacy.
In the following section, let’s explore the six key pillars of cloud security in detail.
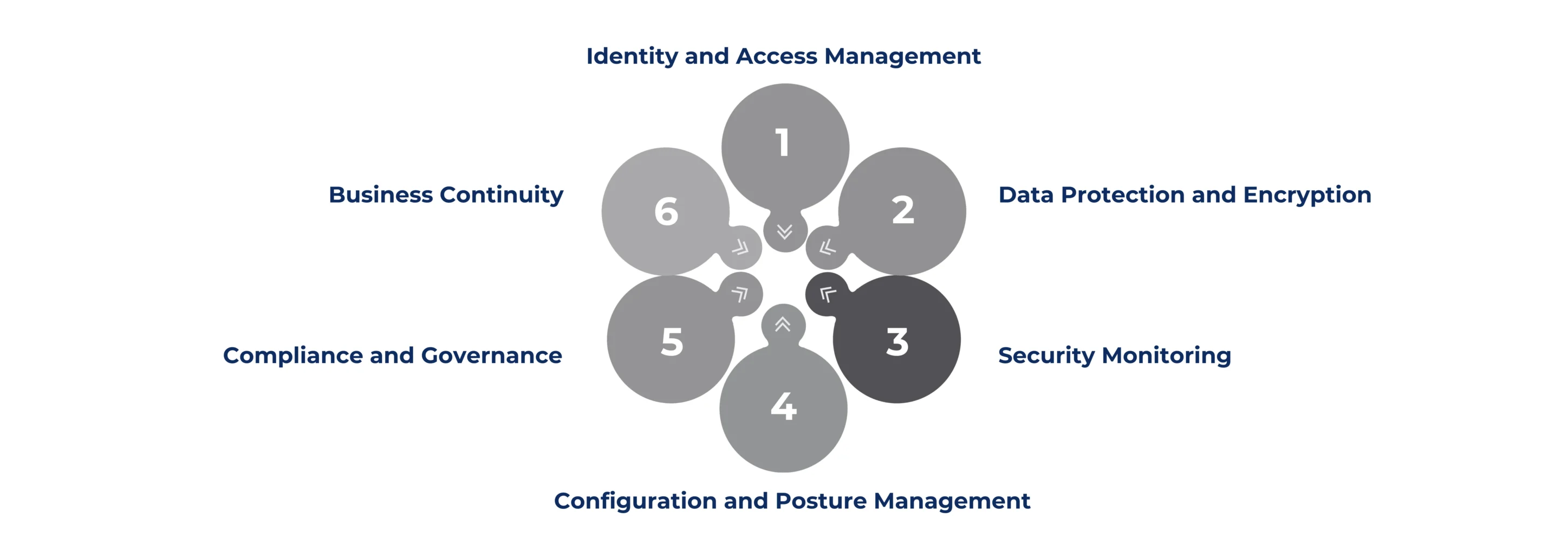
UNDERSTANDING THE SIX PILLARS OF CLOUD SECURITY
The following six key pillars of cloud security form the foundation for a strong cloud infrastructure. Now, let’s learn about the six key pillars in detail.
1. Identity and Access Management: This tool is all about strong access control. It decides who can access what information in the cloud. For instance, consider this tool as a digital ID card or key for accessing your cloud. It works on the principle of least privilege. Additionally, important methods used for this purpose include multi-factor authentication (MFA) and role-based access control (RBAC), which require an extra password or a biometric verification to confirm the identity of the person attempting to access the cloud.
2. Data Protection and Encryption: Your data is one of your crucial assets. Therefore, you must protect and encrypt your data. The process of encryption locks your data using codes like Advanced Encryption Standard (AES-256). This process makes sure the data is protected both during transit and at rest. Additionally, legal frameworks like GDPR and HIPAA demonstrate this protection.
3. Security Monitoring: Tools like Security Information and Event Management (SIEM), Extended Detection and Response (XDR), and AI log analysis help you track and alert you during unusual activities. They are like security cameras watching your cloud all the times.
4. Configuration and Posture Management: One small misconfiguration is enough to disrupt your system and leak sensitive data. Therefore, use a cloud security posture management (CSPM) tool to enforce rules, fix gaps, and secure your default settings.
5. Compliance and Governance: As users, you must follow the cloud compliance regulations by adhering to top standards like ISO 27001 and SOC 2. This helps you monitor access, store logs, and follow legal frameworks.
6. Business Continuity: Despite the safeguards, things could go down unexpectedly. So, you must need strong backups, disaster response plans, and systems to recover back soon.
BENEFITS OF CLOUD SECURITY MEASURES
With the rise of cloud computing technologies, security threats like ransomware, phishing, and data breaches are becoming so common now. Therefore, implementing the core pillars of cloud security is not just a protection, but it is necessary for long-term business growth and building customer trust. Here are some key benefits of cloud security.
1. Protection from Threats: Cloud information security measures protect your data and systems from modern threats like ransomware and phishing using firewalls, encryption, and threat detection systems.
2. Regulatory Conformance: Most of the compliance regulations and standards demand data protection and cloud infrastructure security. And advanced cloud platforms offer automated audits, access logs, and compliance reports. This process helps reduce manual tasks and speeds up the certification process.
3. Centralized Visibility and Control: Modern cloud security platforms offer dashboards for monitoring users, data, and applications, all from one place. This provides greater visibility and control. Moreover, these platforms also help in managing multiple cloud setups, ensuring multi-cloud security. Cloud network security helps organizations secure hybrid and multi-cloud environments with centralized control.
4. Scalability: A well-set-up cloud information security grows along with your business. To clarify, it adapts through automated policies and flexible controls. This is the reason why most startups scale their business without requiring a new cloud security setup each time.
BEST PRACTICES FOR CLOUD SECURITY
In 2025, cloud-related threats are becoming more advanced than ever. Therefore, businesses need to implement robust cloud security measures to maintain resilience and peace of mind.
1. Using a Shared Responsibility Model: It means segregating the task of protecting your assets between you and your provider. For example, a cloud platform must keep its servers safe. But it’s your responsibility to secure your data and access settings.
2. Implement Zero Trust Architecture: The principle behind zero trust is to never trust any user or device, even in your network. You must always verify using MFA and access control measures before allowing anyone to access your cloud. Implementing a zero-trust model is a modern approach to cloud network security.
3. Use AI and Automation: AI tools can identify unusual behavior much more effectively than humans. This approach assists you in identifying threats early and isolating the affected systems before escalation. So, businesses must embrace modern AI tools and automation systems in their cloud security measures.
4. Encrypt Everything: Encryption is a crucial aspect of cloud infrastructure security. Your company must use encryption to protect data at rest, in transit, and even during use. Such holistic cloud information security measures not only help protect data but also enhance compliance with regulations. But it also assists you to comply with regulations like GDPR and HIPAA.
5. Training: Companies must understand that security is not an IT team’s problem but an organization’s responsibility. Therefore, embed security practices into daily operations. Businesses must conduct regular training and awareness programs for their teams to help them detect phishing emails and cyberattacks. Moreover, they must clearly understand all the key pillars of cloud security.
CHOOSE CERTPRO FOR GUIDANCE IN SOLID CLOUD SECURITY MEASURES
Therefore, we can conclude that cloud security is only as effective as its six key pillars. Each pillar plays a crucial role in ensuring cloud security. But, when combined together, they form a strong and secure foundation that keeps your cloud environment safe, compliant, and resilient.
However, businesses must understand the fact that cloud information security is not a one-time task. You can’t just implement one, fix things up and forget. It won’t work that way. As modern threats and compliance regulations keep changing, your cloud data security strategy also needs constant review and updates. All these processes need expert guidance and regular support. This is where CertPro excels. We, as an audit firm, possess immense experience in guiding global businesses in setting up strong cloud security postures. As a result, these firms also show compliance with top standards like ISO 27001, ISO 27018, SOC 2, HIPAA, and GDPR.
Our specialty lies in providing expert guidance, continuous support, and standard audits. As a result, your firm could easily understand the technicalities of protecting modern multi-cloud environments and meeting cloud compliance obligations. Plus, our cloud auditing infrastructure helps you build a customized cloud security strategy suitable for your business needs. Connect with us today for establishing strong, secure, and compliant cloud infrastructure.
FAQ
What is a big challenge in cloud development?
Security issues are the biggest challenge in cloud infrastructure development. This includes lack of identity access management, data misuse, lack of control and visibility tools, misconfiguration, and insecure APIs.
How does identity and access management (IAM) strengthen cloud security?
IAM controls who can access cloud resources. It uses multi-factor authentication (MFA) and role-based access control (RBAC) to prevent unauthorized access and reduce insider threats, making it a foundation of secure cloud systems.
What tools are used for real-time cloud security monitoring?
Tools like SIEM (Security Information and Event Management), XDR (Extended Detection and Response), and AI-based log analysis detect suspicious activity. These tools provide real-time alerts to prevent and respond to cyberattacks.
What is cloud security posture management (CSPM) and how does it work?
CSPM tools continuously scan cloud environments to identify misconfigurations, enforce policies, and ensure compliance. They help maintain a strong security posture across multi-cloud environments.
How does cloud security support business continuity and disaster recovery?
Cloud security ensures regular data backups, failover systems, and recovery plans. These measures help businesses recover quickly from cyberattacks or service outages, ensuring minimal downtime.

About the Author
SUBBAIAH KU
Subbaiah Ku is the Regional Director for CertPro in Oman, bringing a wealth of expertise in process and system auditing. As a seasoned lead assessor, Subbaiah is dedicated to ensuring the highest standards in compliance and security. His unique blend of technical acumen, rooted in Mechanical Engineering, is complemented by a diverse range of certifications and extensive training.
GRC IN CYBERSECURITY: WHAT IT MEANS AND WHY IT MATTERS IN 2026
In 2026, the pressure on companies to manage cyber risk responsibly has never been greater. Regulators demand structured controls, boards want clear risk reporting, and threat actors are becoming more sophisticated. Against this backdrop, GRC in cybersecurity has...
HOW COMPLIANCE AUDIT SOFTWARE IMPROVES AUDIT READINESS
Today, most companies deal with a growing number of compliance regulations. From data privacy standards to security frameworks like SOC 2 and ISO 27001, the list of compliance obligations keeps expanding. At the same time, regulators and external auditors now expect...
Compliance Best Practices in 2026: How to stay ahead of regulatory changes
Why is the implementation of compliance best practices critical for 2026? Compliance in 2026 demands operational proof, not the documentation intent. Regulations change faster, audit scrutiny is higher, and reporting timelines are tighter across privacy,...