Businesses in today’s digital environment are depending more and more on storing enormous volumes of client data, especially in the fields of technology and cloud computing. With growing concerns about privacy and data security, regulatory frameworks such as Service Organization Control 2 (SOC 2) have become essential standards for companies that are responsible for protecting sensitive data. Software as a Service (SaaS) providers, data centers, and other similar enterprises are among the groups for which SOC 2 was especially designed. It provides a strong standard for managing and safeguarding client data that is held in the cloud.
Even though SOC 2 compliance is not legally required, its importance cannot be overemphasized, particularly for companies that operate in sectors like finance, healthcare, and e-commerce where protecting sensitive data is crucial. Using this framework, companies can reassure clients and customers about the security of their data by proving to them that they have put in place efficient security procedures. Given this, it becomes imperative that any firm handling consumer data understands who SOC 2 is for, as it offers a proactive way to resolve the constantly growing concerns surrounding data protection and compliance.
WHAT IS SOC 2?
The American Institute of CPAs (AICPA) created SOC 2, a crucial auditing process that guarantees organizations or applications handle client data securely, protecting the company and the privacy of their users. SOC 2 compliance is widely used in North America, especially in the SaaS sector, and it requires a careful examination of security procedures in comparison to predetermined standards. In order to satisfy these requirements, companies proactively conduct SOC 2 audits. Upon completion, an external auditor issues a SOC 2 certificate, attesting to the organization’s compliance with all standards. By demonstrating to stakeholders that strong safeguards are in place to secure their data, this certification not only verifies information security procedures but also builds credibility with those involved.
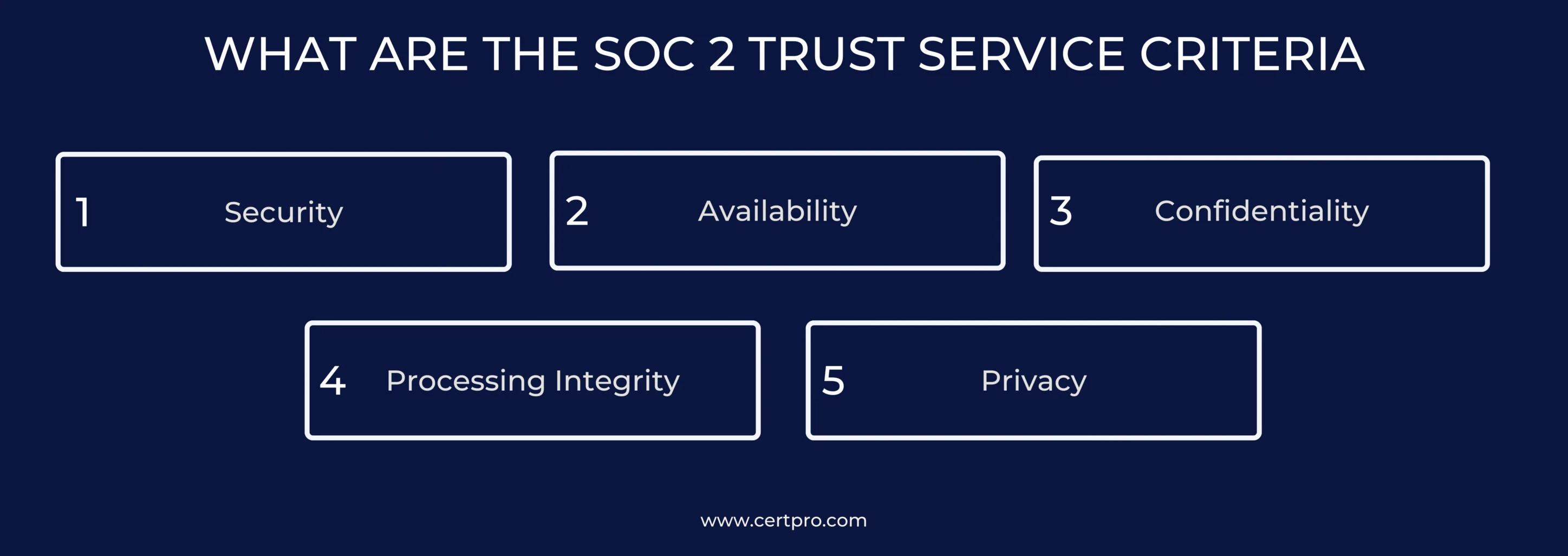
WHAT ARE THE SOC 2 TRUST SERVICE CRITERIA
During a SOC 2 audit, businesses are assessed based on five Trust Principles, also known as Trust Services Criteria (TSC). These criteria encompass Security, Availability, Confidentiality, Processing Integrity, and Privacy. Each of these principles targets a distinct aspect, outlining specific compliance objectives that form the basis for evaluating the organization’s information security program. Essentially, these criteria guide businesses to implement and adhere to controls that ensure compliance in areas crucial for maintaining the integrity, availability, and security of their information systems.
The SOC 2 Trust Services Criteria are listed as follows:
- Security: Security, the main criterion in SOC 2, is required for all completed SOC 2 reports. This category serves as the foundation, defining the controls that are essential to protecting data from breaches and unauthorized access. Essential components include establishing an environment that prioritizes integrity and security, documenting policies to communicate data handling expectations, monitoring and assessing potential risks, ensuring the effectiveness of security controls, reducing risk through implementing appropriate controls, implementing both logical and physical access controls, establishing system monitoring capabilities, creating a recovery plan for system operations, testing and approving system changes before deployment, and monitoring third-party risks through vendor risk management. To be in compliance with SOC 2, an organization needs to implement all of these measures, highlighting how security is a non-negotiable component of this framework.
2. Availability: The availability category, which ensures that data is still available for its intended use, is crucial to the SOC 2 architecture. This entails keeping up strong systems to guarantee clients’ and staff’s continuous access, supported by extensive recovery strategies to handle any data loss situations. Organizations must put certain controls in place to meet the requirements. These controls include the frequent testing of recovery operations, the installation of environmental protections, and the strategic management of capacity needs. SOC 2 compliance with availability is especially important for companies that offer data-centric services. This is especially important in situations where clients or staff rely on company data, such as with cloud storage or CRM software. In these kinds of situations, consistent and dependable data access is essential to task completion and product utilization.
3. Confidentiality: The confidentiality factor in SOC 2 is essential to improving data security protocols. It becomes pertinent when companies work with datasets that must be kept highly secret and accessible to authorized individuals only. Identification and preservation of designated information’s secrecy as well as the appropriate disposal of sensitive data, are important confidentiality measures. Businesses handling sensitive or confidential data, such as trade secrets, client intellectual property, or private financial reports, must integrate confidentiality into SOC 2 compliance. This guarantees that only authorized individuals have access, highlighting the significance of strong procedures to secure and preserve the confidentiality of such information within the framework of SOC 2.
4. Processing Integrity: The processing integrity category in SOC 2 guarantees that systems operate correctly by guarding against mistakes or data manipulation during data processing. It focuses on how dependable systems are at processing data accurately, preventing customers or staff from receiving erroneous outcomes. Maintaining high-quality data, putting policies and procedures for system inputs and processing into place, guaranteeing timely and correct data outputs, and creating protocols for storing inputs, items in processing, and outputs are all important controls. For companies processing data on behalf of clients, including processing integrity in SOC 2 is essential since it reassures them of the reliability of studies and findings. This highlights a dedication to SOC 2 framework-based, precise, and dependable data processing.
5. Privacy: SOC 2’s privacy category protects consumer rights and data integrity by making sure companies adhere to strict guidelines for gathering data, preventing unwanted access, and disposing of it in a way that respects customer preferences. Providing notice on privacy practices, giving customers choices and options for consent, gathering only the information required with their express consent, protecting privacy throughout the data lifecycle, giving customers access and editing capabilities, revealing collected data, preserving data quality, and setting up procedures for monitoring and enforcing privacy laws are all examples of essential controls. By including these measures in SOC 2’s privacy criteria, organizations may create a thorough framework that places an emphasis on responsible data management and aligns them with values that uphold and safeguard customer privacy throughout the data lifecycle.
WHO NEEDS SOC 2 COMPLIANCE
SOC 2 is essential for companies handling consumer data since it helps them both build their security posture and make a strong impression on prospective customers. SOC 2 compliance is now a requirement for potential clients, especially when choosing vendors for possible joint ventures. However, what is SOC 2 exactly, and who has to follow its rules.
SOC 2 is essentially an audit designed specifically for businesses that keep consumer data. Organizations need to demonstrate that their internal controls effectively ensure the security, availability, processing integrity, confidentiality, and privacy of customer data. This assurance, collectively known as the Trust Services Criteria in the context of SOC 2, is a requirement to obtain a SOC 2 attestation. This comprehensive report plays a crucial role in attracting new customers.
This inclusive category encompasses various types of organizations, including:
- Software as a Service (SaaS) companies
- Businesses specializing in business intelligence or analytics
- Financial service institutions, including banking, investment, and insurance
- Security firms
- Any organization storing customer data in the cloud
All entities falling under this description should prioritize SOC 2 compliance, recognizing its pivotal importance for their overall security and credibility.
WHY DO COMPANIES NEED SOC 2 COMPLIANCE?
The primary focus of SOC 2 security principles is to prevent unauthorized use of the organization’s assets and data. In order to limit misuse, stop harmful assaults, prevent illegal data deletion, and stop unauthorized manipulation or publication of firm information, this principle requires organizations to set up access controls.
1. Customer Trust: The statement indicates a strong commitment to protecting, granting access to, and maintaining the privacy of client data. Building partnerships through a dedication to data security and confidentiality cultivates confidence with clients and partners looking for assurance in the handling of sensitive information.
2. Market Differentiation: Obtaining SOC 2 certification sets a business apart from its competitors and establishes it as a standard for security procedures. This accreditation proves to be a useful tool for marketing and sales initiatives, as it demonstrates the company’s dedication to strict security guidelines that differentiate it from rivals.
3. Data Protection: SOC 2 prioritizes the security of client data. By helping businesses establish and maintain strong data protection procedures, compliance lowers the risk of data breaches and illegal access.
4. Regulatory Requirements: Some industries demand compliance with regulatory requirements, making SOC 2 compliance a must. A company that has earned certification has proven that it is committed to the highest levels of data protection and confidentiality, exceeding industry-specific security and privacy criteria.
5. Internal Process Improvement: Companies often modify internal procedures as part of the path to SOC 2 compliance, which leads to improvements in security policies and overall risk management methods. Through this path, organizational procedures are refined pro-actively for increased security and reduced risk.
6. Third-Party Assurance: SOC 2 compliance includes independent third-party audits, offering external validation of an organization’s security controls. This process provides reassurance to stakeholders, including customers, investors, and business partners, as it ensures an unbiased assessment of the company’s commitment to robust security measures.
WHAT IS SOC 2 SCOPE?
SOC 2 scope is essentially a set of guidelines for assessing internal controls in the course of a SOC 2 audit. By outlining the methods and controls that service providers put under inspection to guarantee the security of client data, this procedure improves transparency. Organizations can reassure clients of strict data protection by methodically evaluating and strengthening their security procedures by clearly defining their scope. This thorough approach creates a foundation for ongoing development in data security procedures, in addition to making clear the areas of focus for investigation. SOC 2 scope is like a roadmap, ensuring a thorough evaluation of important controls that contribute to the overall assurance of data integrity and confidentiality.
HOW TO PREPARE SOC 2 SCOPE?
Here’s how to get your organization ready for SOC 2 scope:
1. Select the right Trust Service Criteria.
Selecting one of the five Trust Service Criteria is the first step towards defining the SOC 2 scope. The audit’s assessment is based on the criteria. Here’s how you make a choice:
- Security (Common Criteria): This is mandatory and forms the baseline for SOC 2.
- Availability: If your services must be accessible at all times, particularly for crucial tasks like financial transactions, then make sure to highlight this requirement. Take customer requests and availability-affecting risks into account.
- Process Integrity: If your company handles a lot of data, particularly sensitive data, or depends on precise data processing for important choices, then include this.
- Confidentiality: Include confidentiality if your company deals with sensitive data that needs to be protected from unwanted access, such as financial records or health information. Take cyber hazards and legal regulations into consideration.
- Privacy: Make sure that any firm handling personal data complies with data protection legislation. For sectors like healthcare and e-commerce, this is essential.
2. List the services that are included in the scope.
It’s critical to identify and include service offerings that are in line with the organization’s activities when defining the scope of a SOC 2 audit. Services like cloud computing or managed IT services that include gathering, storing, processing, or transmitting sensitive data must be included in the scope according to the applicable Trust Service Criteria (TSC).
The SOC 2 scope should also include a detailed description of sub-service organizations, which are outside suppliers or vendors that support the company. Since these organizations might have access to their data or resources, the audit process entails evaluating the risks associated with those access points and making sure that sufficient controls are in place while the entity is participating in the audit.
3. Determine policies, procedures, systems, and people:
- Policies: Organizational policies establish the standards for security procedures and practices. Important rules, such as data protection and vendor management, must be identified and included for the SOC 2 audit.
- Procedures: Standard Operating Procedures (SOPs) provide detailed instructions for particular tasks, such as managing security incidents. The SOC 2 scope must include procedures for incident identification, communication, staff duties, remediation, and post-incident actions. Auditors will assess these procedures to determine the degree of conformity.
- Systems: A key component of the SOC 2 scope is the technical and physical information systems, which include hardware, software, and network components pertinent to the selected criteria. Examples of risk management for information security that have been evaluated include intrusion detection systems, firewalls, and access controls.
- Personnel: Staff members in charge of creating and executing controls actively play a direct role. Defining clear roles and responsibilities for personnel controlling access restrictions, incident detection, and security training comes under the SOC 2 scope, assuring conformity with Trust Service Criteria (TSC).
4. Select between SOC 2 types 1 and 2
Type 1 and Type 2 SOC 2 reports have different scopes, but both seek to improve organizational security. Type 1 is ideal for new businesses looking to discover opportunities for development, as it offers a snapshot of the security control design at a particular point in time. Conversely, companies opting for Type 2 evaluations, aiming to showcase continuous security measures, assess both control design and operational effectiveness over a minimum of six months. Organizations usually perform an annual Type 2 audit to ensure SOC 2 compliance. The organization’s maturity in SOC 2 audits and its intention to demonstrate either a snapshot or sustained effectiveness will determine which Type 1 and Type 2 audits to choose.
FAQ
Why is SOC 2 compliance important for businesses handling consumer data?
SOC 2 compliance is crucial for organizations dealing with consumer data, especially in sectors like technology and cloud computing. It assures clients that stringent security measures are in place, building trust and credibility. Compliance also addresses growing concerns about data protection and privacy.
Who needs SOC 2 compliance, and what types of organizations fall under this requirement?
SOC 2 compliance is necessary for businesses handling consumer data, such as SaaS providers, data centers, and financial institutions. It is especially relevant for those in sectors like finance, healthcare, and e-commerce, where safeguarding sensitive data is paramount.
How does SOC 2 compliance contribute to market differentiation and building customer trust?
SOC 2 certification sets businesses apart from competitors by demonstrating a commitment to robust security procedures. It becomes a valuable tool for marketing and sales initiatives, showcasing the company’s dedication to strict security guidelines and building trust with customers and partners.
Is SOC 2 compliance legally required, and what are the industries that demand compliance with regulatory requirements?
SOC 2 compliance is not legally required, but it is essential for industries such as finance, healthcare, and e-commerce that demand adherence to strict regulatory requirements. Compliance ensures that organizations surpass industry-specific security and privacy criteria, demonstrating a commitment to the highest levels of data protection.
How often should organizations undergo SOC 2 audits, and what is the difference between Type 1 and Type 2 audits?
Organizations typically perform annual SOC 2 audits. The choice between Type 1 and Type 2 audits depends on the organization’s maturity and intention. Type 1 offers a snapshot of security control design, while Type 2 assesses both design and operational effectiveness over a minimum of six months, showcasing sustained security measures.

About the Author
RAGHURAM S
Raghuram S, Regional Manager in the United Kingdom, is a technical consulting expert with a focus on compliance and auditing. His profound understanding of technical landscapes contributes to innovative solutions that meet international standards.
Multi-Framework Compliance Guide: Best Practices and Strategies
SOC 2 FRAMEWORK REQUIREMENTS IN 2026. WHAT HAS CHANGED?
HOW SOC 2 COMPLIANCE SOFTWARE CHANGES AUDIT READINESS
There's a version of SOC 2 preparation that most security teams know too well. The audit date is approaching. Someone sends a spreadsheet asking for access logs, vendor assessments, and approval records. People scramble. Documentation gaps appear. What should take...





