The Certified Information Systems Auditor (CISA) plays an important role in cybersecurity by ensuring that organizations have secure, compliant, and well-managed IT systems. ISACA has established this well-known global certification program. The auditors with CISA cybersecurity certifications help businesses assess cyber risks, detect vulnerabilities, and implement security control measures to safeguard sensitive data. They conduct a comprehensive cybersecurity audit to review the security policies, access controls, and adherence to regulations such as ISO 27001, GDPR, and SOC 2. Moreover, they help businesses in establishing risk management policies and incident response plans. This process helps organizations to detect, respond to, and recover from cyber threats. The CISA cybersecurity approach also emphasizes continuous monitoring of key business processes to detect suspicious activities.
Not only that, regular cybersecurity audits safeguard businesses from data breaches and financial risks. Additionally, many global firms invest in CISA cybersecurity training to improve their internal security teams’ skills. This process provides operational efficiency and safeguards the reputation of the firms among customers and stakeholders. To add on, the business organizations are relying on CISA-certified auditors to safeguard their IT systems and ensure regulatory conformance. Without them, the businesses will face financial losses, legal fines, and operational disruptions. Plus, CISA audits assess whether organizations properly implement cybersecurity guidelines to reduce security risks. Therefore, a strong cybersecurity audit is a business mandate for growth, prosperity, and long-term success in a vulnerable market.
This blog provides you with a thorough understanding of the core guidelines for a cybersecurity audit and how businesses should integrate them into their audit plans to mitigate risks.
TL;DR:
Concern: As the current business environment is facing more cyberattacks, organizations are looking forward to conducting an effective cybersecurity audit. But they lack the proper guidance and support to perform the audits.
Overview: To help businesses conduct an effective cybersecurity audit, the International Professional Association called ISACA has outlined best cybersecurity assessment practices in its CISA certification guidelines.
Solution: So, the organizations must partner with global audit firms that follow the standard CISA procedures to conduct a cybersecurity audit. This step helps them in securing their information security posture, sensitive data, and digital systems. Furthermore, it helps them in demonstrating their compliance with key regulations like ISO 27001, GDPR, HIPAA, and SOC 2.
PRIORITIZE A RISK-BASED CYBERSECURITY AUDIT
According to the CISA’s governance framework, risk assessment is the foundation of a strong cybersecurity audit. This is because organizations cannot effectively protect their data and systems without a thorough understanding of the risks. So, the main focus of the cybersecurity assessment must be identifying, analyzing, and mitigating the risks to safeguard the businesses from security breaches. CISA cybersecurity best practices also include regular risk assessments as a crucial component for identifying and addressing vulnerabilities. In simple words, a risk-based cybersecurity audit for your organization means that your primary focus must be on the areas that could cause the most trouble due to a vulnerability or attack. Instead of equally focusing on all systems and controls, businesses must identify the most likely attack point.
Such an approach helps organizations to optimize their resources and refrain from wasting them on smaller and manageable risks. Furthermore, this approach assists businesses to identify the bigger risks first and mitigate them quickly. This approach safeguards the organization from major damages such as operational shutdowns. The CISA auditors focus on identifying the vulnerabilities in an organization’s IT systems. Some common weaknesses that they evaluate include:
- Outdated software and programs with security flaws
- Simple and weak passwords
- Systems with a lack of Multi-Factor Authentication (MFA)
- Outdated systems with an absence of required updates
- Excess access and permission for employees
Hackers and cyberattackers can easily exploit these weak spots. So, to overcome this challenge, the CISA cybersecurity assessments classify the risks based on their impact assessment and likelihood assessment. To clarify, once the vulnerabilities are identified, the auditors evaluate the damage they can cause and check how common they could be. For example, an unpatched server, hacked cloud storage, and malware-infected endpoint devices are some examples of high-risk areas.
IMPLEMENTATION OF STRONG ACCESS CONTROLS
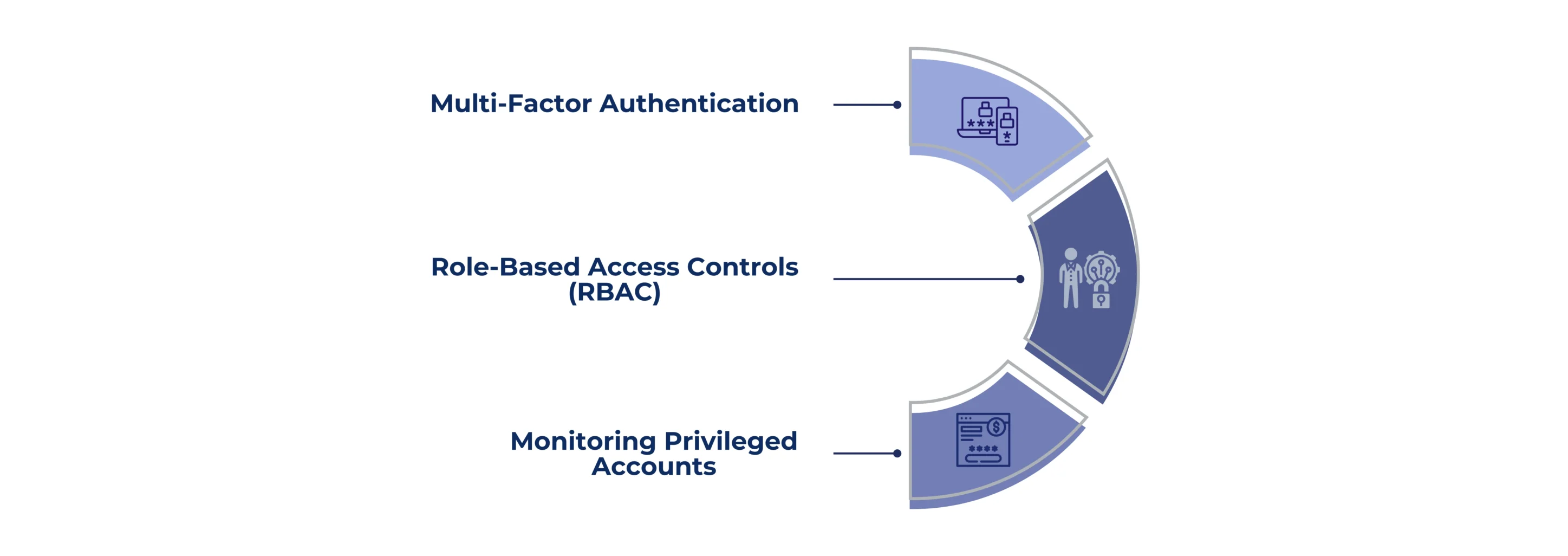
The CISA’s cybersecurity framework focuses on strong access controls to prevent unauthorized users from accessing the sensitive data and systems. If the access is not properly managed, the hackers or even the employees might steal or leak the sensitive information. In simple words, assume these access controls are locks and keys for an organization’s digital assets, such as data, systems, and apps. These controls decide who gets in and what they can do. Some of the key access controls used in a cybersecurity audit are as follows:
Multi-Factor Authentication: This control requires users to verify their identity using two or more methods before gaining access. For example, logging into your email needs a password and a code texted to your mobile number. This step is important because, even if a hacker can steal a password, he will still need a code to access the sensitive information. Strong passwords and multi-factor authentication are the key cybersecurity guidelines for securing the user accounts.
Role-Based Access Controls (RBAC): This control ensures that employees get access only to data and tools needed to do their jobs. For example, a finance manager can access the financial records, but a customer service agent can only access the customer account details.
Monitoring Privileged Accounts: Regular monitoring and review of the activities of higher-level executives, such as department admins and managers, is necessary due to their wide and powerful access. Such oversight is necessary because the misuse of privileged accounts can result in significant harm. Therefore, businesses must maintain a log for all the actions performed by privileged accounts. This information helps them to identify any suspicious activity, such as the downloading of unauthorized data.
Furthermore, standards like ISO 27001 and SOC 2 highlight the importance of access controls.
CONTINUOUS TESTING AND MONITORING OF SYSTEMS
The CISA certification guidelines highlight that the process of cybersecurity is not a one-time task but a consistent monitoring activity. This approach helps businesses to detect and prevent data breaches before they cause damage. Some of the continuous monitoring practices recommended by CISA are
Penetration Testing: This process involves using ethical hackers to put on a cyberattack to check the organization’s defenses. It helps businesses to identify the weak area used by the ethical hacker and fix it before actual hackers exploit it. For example, a financial institution can hire security experts to hack their website. If they succeed, they will fix the vulnerabilities.
Vulnerability Scans: These are automated tools that scan the digital assets to identify the weaknesses, such as outdated software and misconfigured settings. It quickly identifies the vulnerable areas and fixes them before they get exploited. For example, an organization can run a weekly scan covering all the endpoint devices, apps, and networks to detect problems. Consequently, inform the IT department to fix it before hackers take advantage of it.
Monitoring and Analysis of Logs: Security teams must regularly check the system log to find unusual activities like unauthorized access or data transfers. This system records all details like who logged in, at what time, and what task they performed. For example, a security team detects multiple failed login attempts from an unauthorized user and blocks the access before the exploit can affect the system.
The organizations must include these continuous auditing methods in their cybersecurity audit. As a result, the key audit findings guide them in creating strong security policies and risk mitigation plans.
STRONG INCIDENT RESPONSE AND RECOVERY PLANS
Incident response plans are an inevitable part of cybersecurity assessment because attacks and system failures are unavoidable. Therefore, the goal is to detect, respond to, and recover from the incidents swiftly to reduce the damage. In CISA’s cybersecurity audit, an organization is assessed for clear, structured, and tested incident response and recovery plans. To put it simply, an incident response plan functions similarly to a cyberattack fire drill. You already knew where the fire extinguisher was and how to use it to prevent your place from damage.
Similarly, once the attack happens, you can effectively mitigate it using a structured incident response plan. The key steps involved in this process are:
Detection of Incidents: Watch the systems all the time using real-time monitoring tools to detect any weird or suspicious activity. Plus, use Security Information and Event Management Systems to check the logs and alert systems. You should also teach your staff to report strange things like malware infections, phishing emails, and illegal access. To put it in simple words, this process is for spotting trouble and problems.
Incident Response: Follow a predefined incident response plan. Assign roles and responsibilities by forming a specific team to contain the incident. Quickly remove the affected systems to prevent the attack from spreading. For instance, if a virus hits a computer, shut it down and remove it as soon as possible. Furthermore, if needed, inform the details of the incident to all the key parties, like IT teams, legal experts, and regulators.
Post-Incident Review: Conduct a post-mortem analysis to prevent future incidents. It’s like looking back and analyzing the incident. It involves analyzing the incident to determine what went wrong, how you handled it, and what we can fix to prevent it from happening again.
REGULAR TRAINING AND AWARENESS FOR EMPLOYEES
Another major factor to be ensured by organizations in a cybersecurity audit is training the employees to transform them into a strong first line of defense. In particular, employees can accidentally make a mistake by clicking on a malicious link or sharing a password. So, thorough training and awareness programs are necessary to reduce these human errors. CISA recommends not just training with lectures but also stresses providing hands-on practice to employees. Some of the notable training processes are:
Phishing Simulations: This method involves sending fake scam emails to employees to check how they respond to them. They receive training to recognize suspicious emails that attempt to steal login details or spread malware. For example, a fake email with the subject “Reset your password” is sent to all employees. Provide proper training to those who click and respond to it, enabling them to recognize the fake emails going forward.
Security Policies: Businesses must make sure that their employees clearly understand their security policies. These policies provide guidelines on how to handle sensitive data and use company devices safely. For example, a financial institution trains it’s staff to lock the screen when they are away from the desks to prevent unauthorized access.
Security Drills: Practice periodic test runs for cyber emergencies. Pretend there is a ransomware attack, and make your employees follow the step-by-step process as outlined in the incident response plan. Accordingly, the employees must report the incident, lock the affected systems, and call the security team.
CHOOSE CERTPRO FOR AN EFFECTIVE CYBERSECURITY AUDIT
To conclude, by following all the above-mentioned guidelines, businesses can conduct an effective cybersecurity audit. Consequently, they can protect their businesses from potential risks and enhance their security posture. In addition to these five guidelines, businesses must also focus on ensuring regulatory conformance with top standards like ISO 27001, SOC 2, GDPR, HIPAA, and PCI DSS. Also, organizations must integrate a proactive security approach based on CISA cybersecurity best practices to prevent unforeseen downtime and operational shutdowns.
Moreover, the audit process must be equipped with detailed and flawless documentation and reporting. All the audit findings must be effectively communicated to all the relevant stakeholders. Consequently, you must follow up and evaluate the remediation measures recommended during the process. Implementing a robust cybersecurity framework will therefore lower the likelihood of cyber threats and data breaches. Is everything sounding too technical and complex? No worries. Partnering with an expert audit firm will help you ease through the process.
CertPro is here to assist you in conducting a standard cybersecurity audit as recommended by the CISA cybersecurity best practices. We are an international audit firm with a client base across diverse locations. Our team of expert auditors provides you with holistic guidance on the process of a cybersecurity audit. Furthermore, our unique approach is based on the foundation of conducting audits as per the target rulebook. We deliver thorough, high-quality audits. We also equip your cybersecurity audit procedure with cutting-edge tools for compliance automation to deliver audits more quickly. Connect with us today to ensure your cybersecurity compliance and enhance your security posture by adhering to global standards.
FAQ
What are the types of cybersecurity?
The different types of cybersecurity are network security, application security, information security, IoT security, and identity and access management. Ensuring these securities can help organizations protect from cyber attacks.
What are the essential aspects of a cybersecurity audit?
The essential aspects of any cybersecurity assessment include the review of cybersecurity policies, the development of an integrated approach, the analysis of the cyber competence of the personnel and the facilitation of risk-based auditing initiatives in the organization.
Who is the ISACA?
The Information Systems Audit and Control Association (ISACA) is a professional organization focused on IT governance. They are a team of IT professionals working together to advance digital trust. They are dedicated to creating a digital world that’s safe, secure and accessible to all.
What are the areas covered in the five main domains of the CISA program?
The process of information system auditing, governance & management of IT, information systems acquisition, development & implementation, information systems operations and business resilience are the key topics covered in the domains of the CISA certification program.
What are the common cybersecurity threats faced by an organization?
Cybersecurity threats are false attempts to damage, steal, or disrupt the data and digital assets of an individual or organization. Some of the common cybersecurity threats are malware, ransomware, phishing e-mails, social engineering, denial of service attacks, man-in-the-middle attacks, and advanced persistent threats.

About the Author
RAGHURAM S
Raghuram S, Regional Manager in the United Kingdom, is a technical consulting expert with a focus on compliance and auditing. His profound understanding of technical landscapes contributes to innovative solutions that meet international standards.
How CertPro Conducts an Effective SOC 2 Type II Audit: A CPA-Led Playbook for SaaS
A SOC 2 Type 2 examination results in an independent CPA - issued attestation report on whether your controls are suitably designed and operated effectively over a period of time. It’s based on the AICPA Trust Services Criteria. This requirement is essential, as in...
AUDIT REPORTING BEST PRACTICES FOR ACCURACY & COMPLIANCE
Audit reporting is important for every business organization. For business leaders, clear audit reporting is essential to understand risks, controls, and issues that need remediation. A simple and direct reporting process turns audit work into plain insights that...
AUDITING REPORT FORMAT: BEST PRACTICES FOR CYBERSECURITY COMPLIANCE
If you are a business leader thriving in this era of strict regulations and sophisticated cyberattacks, then you must have realized the importance of compliance and security audits. According to Deloitte, 93% of audit committees rank cybersecurity in their top three...