In today’s IT world, the cloud-based companies and SaaS firms are occupying the major part of the sector. In addition to that, the number of cyberattacks and security threats is also increasing at an alarming rate. This trend has made the IT and service-based organizations realize the importance of cybersecurity and maintaining a strong security controls framework. As a result, businesses are now focusing on achieving compliance with top standards like ISO 27001 and SOC 2. In particular, most service-based organizations handling sensitive data are aiming to achieve SOC 2 compliance to demonstrate a strong cybersecurity posture. Accordingly, businesses undergo comprehensive SOC 2 audits based on AICPA standards and Trust Services Criteria (TSCs) to ensure compliance.
Furthermore, the AICPA standards outline several critical guidelines and professional standards to auditors to guide them during the auditing process. This complexity can result in audit failures if not addressed early. This leads to unexpected audit failures during SOC 2 compliance audits. Therefore, this blog provides you with a holistic understanding of SOC 2 and how to meet the AICPA standards for a SOC 2 compliance audit.
TI; DR:
Concern: Service organizations dealing with sensitive customer data are required to achieve SOC 2 compliance. This helps them in demonstrating their commitment to data security and privacy. But businesses often face difficulties due to a lack of understanding of the AICPA standards.
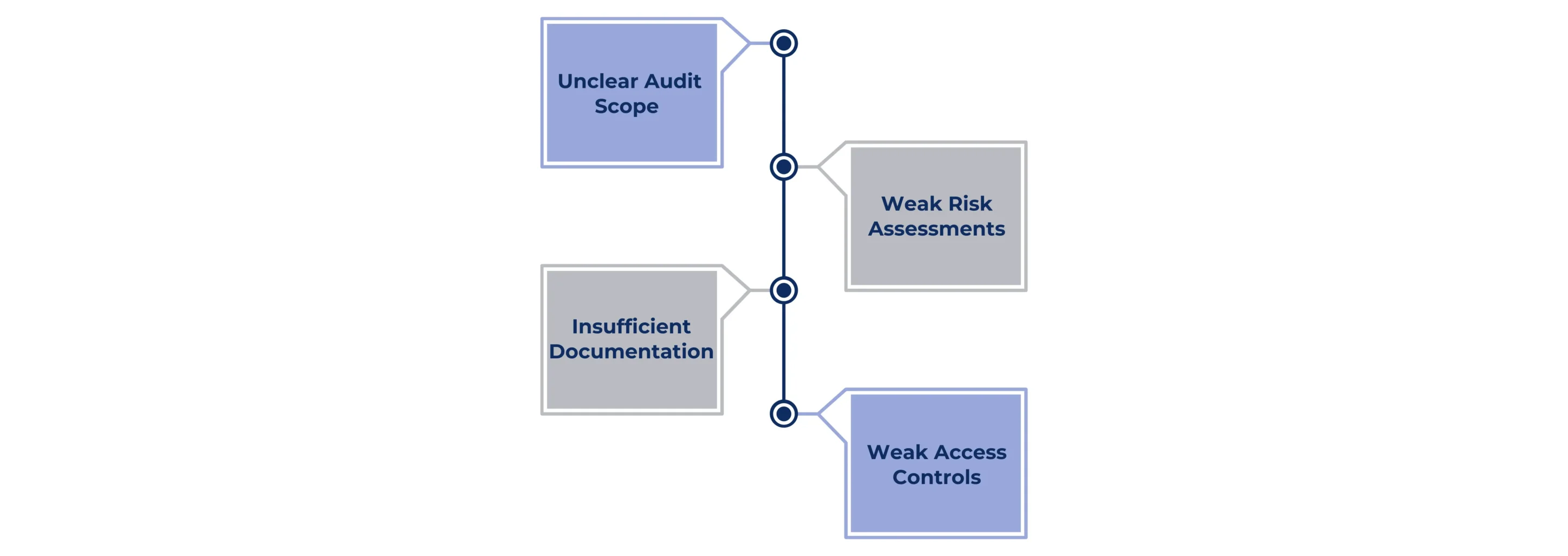
Overview: Some of the common difficulties faced by the organizations are unclear scope, lack of evidence, weak security controls, and skipping risk assessments.
Solution: Organizations must collaborate with expert audit firms to ensure a smooth compliance process. These audit firms provide them with enough guidance regarding the AICPA Trust Services Criteria and critical auditing standards. Moreover, they follow a well-organized audit plan to ensure a smooth compliance journey.
WHAT IS SOC 2? A BRIEF INTRODUCTION
The Service and Organization Controls (SOC 2) is an auditing framework established by the American Institute of Certified Public Accountants (AICPA). To clarify, it provides guidelines for AICPA-certified auditors on the key steps and standards to be followed while conducting third-party compliance audits. These auditors check how the service-based organizations manage their customer data based on five trust services criteria. These criteria are security, availability, processing integrity, confidentiality, and privacy. Moreover, SOC 2 is a voluntary compliance guideline that does not have any legal mandate on organizations. It is prepared with a primary focus on assisting the technology and cloud-based businesses to make sure that they handle the customer data in a safe and secure manner.
The key features of the SOC 2 framework include its trust services criteria and its flexible nature in choosing one. Simply put, this framework enables businesses to select only those criteria that align with their business operations and service commitments. For instance, consider a company providing a cloud-based project management platform for small businesses. They must select the security criterion when performing SOC 2 compliance audits, as it is required for all SOC 2 audits. Additionally, choosing availability criteria is more suitable for their service commitment. This is because they are committed to ensuring the consistent availability of their platform for their customers.
The following five SOC 2 Trust Services Criteria outlined by the AICPA form the foundation of SOC 2 standards.
- Security: Protecting the data and systems from unauthorized access
- Availability: Ensuring the availability of the systems and platforms as per the business objective
- Processing Integrity: Checking whether the systems process data correctly and consistently according to the business goals
- Confidentiality: Keeping the sensitive information safe from unauthorized access
- Privacy: Ensuring data privacy while managing the sensitive personal information
IMPORTANCE OF A SOC 2 AUDIT IN 2025: KEY BENEFITS
In 2025, the SOC 2 audits guided by the AICPA standards are essential for service-based organizations handling sensitive customer data. Furthermore, with the rise of cyber threats, the stakeholders are demanding proof of protection from the organizations handling their data. It is a tool for your business to enhance your credibility and reputation in this data-driven digital world. Now let’s understand some of the key benefits demonstrating the importance of SOC 2 audits.
Client Trust: The SOC 2 report, achieved based on AICPA standards, proves that your security controls are strong and solid. This, in turn, enhances the trust and credibility of your firms. For instance, consider a cloud service provider showing SOC 2 report to its healthcare clients. This means that their sensitive patient data are safe and secure.
Competitive Advantage: Achieving SOC 2 compliance puts your business ahead of your non-compliant competitors. In the contemporary market, most business deals and contracts are won by organizations demonstrating a strong security posture.
Reduced Risk: Compliance helps identify and mitigate potential vulnerabilities through robust controls, as required by AICPA standards. This is because the AICPA professional standards demand a thorough risk assessment process during SOC 2 audits.
Furthermore, SOC 2 audits based on AICPA standards also enhance the operational efficiency of key business processes. For example, a firm with SOC 2 compliance could tighten their monitoring abilities. Thereby, avoiding operational shutdowns and increasing the reliability of the core services.
UNDERSTANDING AICPA AUDITING STANDARDS FOR SOC 2
The organizations need to obey the rules set by AICPA to ease through SOC compliance audits. Plus, these AICPA standards are mentioned in the Statements on Standards for Attestation Engagements (SSAE). These standards are further classified into specific sections called AT-C sections. In particular, the AT-C 101, AT-C 105, and AT-C 205 are very essential for SOC 2 audits. To clarify, these sections provide the rules and methods that auditors must follow during SOC 2 audits. Now, let’s have a profound understanding of these sections.
AT-C 101: This section is considered the foundation of SOC 2 audits. It’s like a rulebook for auditors examining an organization for its security controls. This section encourages and enables the auditors to examine non-financial security controls. In other words, this section asks the auditor to check deeply for the presence and performance of the security controls in the organizations.
AT-C 105: This section provides auditors with the basic principles to follow. This ensures that the audit remains safe, fair, and reliable. It encompasses crucial aspects like planning the audit, gathering the evidence, and maintaining the ethical nature of it. Moreover, this section makes sure that the auditors are not biased, they collect solid evidence, and they perform a complete risk assessment during the compliance audits.
AT-C 205: This section is a framework for auditors to assess management’s assertions during the SOC 2 audits. Furthermore, it guides the auditors on how to test a control, arrive at an opinion, and write a report. The key process focused on in this section is the assertion-based examinations. In simple words, this process occurs when a company claims that they have solid access control measures. Accordingly, this section demands that auditors check if their claim is right and ensure that it is free from unauthorized access.
COMMON PITFALLS FACED BY BUSINESSES IN MEETING THE AICPA STANDARDS
The AICPA standards provide a complete rulebook to perform SOC 2 audits. Yet, the organization faces several difficulties while undergoing compliance audits. Let’s study the common pitfalls faced by businesses in this section.
Unclear Audit Scope: Businesses often fail to set a clear scope and boundary for their SOC 2 audits. To clarify, the organizations must clearly understand the specific systems, processes, and controls that need to be examined during the SOC 2 audit. Without a clear audit scope, companies risk overlooking key security areas or wasting resources on irrelevant systems.
Weak Risk Assessments: Comprehensive risk assessments are the foundation of SOC 2 audits. It helps the organizations to identify the areas with potential risks and fix them before they cause problems during the actual audit. In simple words, only a risk assessment could help your organization to identify the controls that might fail to meet the AICPA TSCs.
Insufficient Documentation: Documentation is an irreplaceable aspect of achieving compliance in SOC 2 audits. The AICPA professional standards demand clear and appropriate evidence from businesses to prove the effectiveness of their security measures. Additionally, clear documentation also helps businesses in building trust with the interested parties. Outdated policies and inconsistent logs are some examples of weak documentation and evidence.
Weak Access Controls: Weak access controls are a common reason organizations fail to meet SOC 2 standards, leading to audit failures. In particular, if an organization has a weak Identity and Access Management (IAM), it means they’ve failed to meet the security criteria. This, in turn, permits unauthorized access to sensitive data and systems. Therefore, businesses must ensure Role-Based Access Controls (RBAC), Multi-factor Authentication (MFA), and continuous monitoring of security controls.
COLLABORATE WITH CERTPRO: YOUR TRUSTED PARTNER IN CONDUCTING SOC 2 AUDITS
In 2025, SOC 2 has evolved from a voluntary step to a critical business need due to market demands. So businesses must conduct this process based on the structured AICPA principles to ensure security and privacy. But they often face difficulties in the form of the above-discussed pitfalls due to their poor planning and execution. The solution to this challenge is to collaborate with an expert auditing firm that strictly follows the key principles and AICPA standards in conducting SOC 2 audits. Moreover, to achieve SOC 2 reports, companies must show their continuous commitment to SOC 2 standards.
CertPro is a global auditing firm with years of experience in professional compliance and auditing services. We make sure that our client gets the best possible service by achieving their compliance goals. When it comes to SOC 2 audits, our testimonials are a testament to our excellence. We are a market leader in providing SOC 2 compliance audits. Additionally, we make sure that our clients receive a standard SOC 2 report that aligns with AICPA principles. Our expert audit team possesses profound knowledge of the AICPA professional standards and trust services criteria. This allows us to provide you with seamless guidance and consultation services throughout the monitoring period. We also assist companies in regularly updating their SOC 2 risk assessment to align with the evolving SOC 2 standards.
Furthermore, we provide faster audits with modern compliance automation tools. In particular, we excel at tailoring unique audit strategies catering to the needs of businesses of all sizes across sectors. Connect with us today to build the foundation for compliance-driven business growth and success with our quality audits.
FAQ
What are the three pillars of SOC?
The three pillars of SOC are people, process, and technology. These pillars provide an efficient SOC environment by combining skilled personnel, structured processes, and advanced technological tools.
What happens if a company fails to meet AICPA standards during SOC 2 audit?
Failing to meet the AICPA’s standards, like AT-C 105 AND 205, will have a huge impact on the auditor’s opinion. For instance, he might issue a qualified opinion stating some ineffective controls. Else, he might issue an adverse opinion indicating deficiencies in the security controls.
Who performs SOC 2 audits?
SOC 2 audits are performed by third-party auditors certified by the AICPA. These auditors follow certain principles and professional standards while conducting the audits.
What is the impact of third-party vendors on SOC 2 compliance?
The third-party vendors can bring security-related risks into compliance with SOC 2. So, it is necessary for businesses to conduct vendor-risk assessments and demand SOC 2 reports from critical vendors before joining hands for business deals.
What is SOC 2 readiness assessment?
Organizations must consider performing SOC 2 readiness assessments to identify compliance gaps before a formal audit, strengthen controls to address vulnerabilities, and ensure ongoing compliance with AICPA standards.

About the Author
BENEDICT ESSANDOH
Benedict Essandoh, CertPro’s Regional Director in Ghana, is a compliance and ISO standards expert. Specializing in health and safety, he conducts audits, implements ISO 9001 and ISO 45001, and excels in accident investigation and site inspections, ensuring international standards are met.
Multi-Framework Compliance Guide: Best Practices and Strategies
SOC 2 FRAMEWORK REQUIREMENTS IN 2026. WHAT HAS CHANGED?
HOW SOC 2 COMPLIANCE SOFTWARE CHANGES AUDIT READINESS
There's a version of SOC 2 preparation that most security teams know too well. The audit date is approaching. Someone sends a spreadsheet asking for access logs, vendor assessments, and approval records. People scramble. Documentation gaps appear. What should take...





