In the age of an interdependent and globalized business world, vendor and third-party risks are crucial boardroom priorities. Business leaders must understand that every new partner, supplier, or SaaS tool you bring in carries some level of security risk. Furthermore, with data breaches making headlines almost daily, companies are more cautious than ever in safeguarding their security posture. That’s where security questionnaires step in as an essential tool in risk management.
A security questionnaire is a standardized set of questions used to evaluate a vendor’s security controls. Your partners and auditors will send you these questions to confirm that your data handling, policies, and systems are safe. Consider it like a pre-flight checklist before a partnership takes off. These questionnaires are showing up in contracts, procurement processes, vendor onboarding, and even during compliance audits. Furthermore, your teams might struggle to answer them if they didn’t prepare ahead of time.
In this guide, we provide a clear overview of a security questionnaire. We will clarify what a security questionnaire really is, why it’s so important, and how it actually helps you stay compliant with frameworks like SOC 2, ISO 27001, or GDPR. If you’re a vendor trying to win deals, a compliance lead managing multiple frameworks, a security team protecting sensitive data, or a procurement officer vetting suppliers, this guide is for you. By the end, you’ll know exactly when you need a questionnaire, what to expect in one, and how to respond with confidence. The ultimate goal is to make security questionnaires something you can master and even use to your advantage.
Tl; DR:
Concern: Every new vendor, SaaS tool, or partner brings hidden security risks that could lead to data breaches, regulatory fines, and delayed deals. Many businesses miss out on opportunities due to rushed, incomplete, or outdated security questionnaire answers.
Overview: A security questionnaire is a structured set of questions used by clients, auditors, and procurement teams to evaluate your security posture. It covers data encryption, access controls, compliance readiness, and incident response. When handled well, it builds trust, proves compliance with ISO 27001, SOC 2, and GDPR, and speeds up vendor onboarding. Businesses now use AI security questionnaire tools to automate responses, flag gaps, and reduce manual effort.
Solution: Prepare early with accurate policies, strong controls, and clear audit evidence. Partner with CertPro to stay audit-ready, map your processes to global standards, and respond confidently. Our expertise and use of modern compliance automation tools turn security questionnaires into a growth enabler, reducing risks and closing deals faster.
WHAT IS A SECURITY QUESTIONNAIRE?
A security questionnaire is a structured document that asks detailed questions about how your organization protects data and manages risk. It’s not an audit or a full risk assessment. An audit verifies compliance against a standard like ISO 27001 or SOC 2. A risk assessment identifies vulnerabilities in your systems. On the other hand, a security questionnaire is a way for your clients or partners to evaluate your security posture before trusting you with their data.
These questionnaires usually appear during vendor onboarding, contract negotiations, or renewal cycles. If you sell software or manage sensitive data, it’s obvious that you should expect a cybersecurity questionnaire. They’re also common before compliance reviews, especially in regulated industries. To elaborate, in a security questionnaire, you will witness questions about data encryption, access controls, backup processes, and incident response plans. Additionally, some of the most critical security questions that businesses face revolve around vulnerability management, Secure Software Development Lifecycle (SDLC), logging activity, endpoint device security, business continuity, and disaster recovery. Many include compliance questions, asking if you meet regulations like GDPR or HIPAA. Some are also related to employee security training or even physical security measures.
Typically, they’re issued by procurement teams, security teams, or external auditors on the buyer’s side. Respondents are usually security leads, compliance officers, or vendor managers within the supplier organization. If you’re a startup without a dedicated security team, it might even land on the founder’s desk. Many businesses struggle not just to respond to these questionnaires but also to do so quickly and accurately. As a result, missing details or vague answers could delay contracts or even cost you deals. That’s why understanding these questionnaires early and preparing responses in advance can make vendor relationships smoother and speed up sales cycles.
KEY BENEFITS OF USING A SECURITY QUESTIONNAIRE
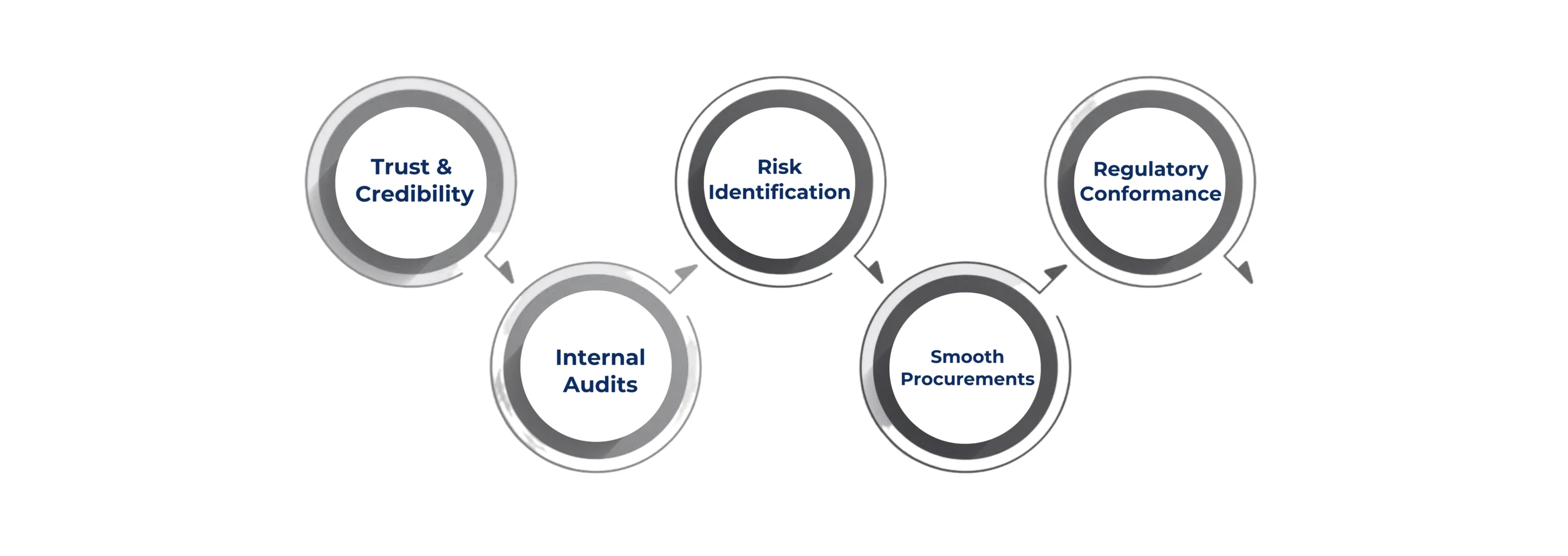
Security questionnaires might feel like extra paperwork, but when performed correctly, they offer real value. Let’s learn about the potential benefits of using a security questionnaire in this section.
Trust & Credibility: Their first and biggest benefit is building trust with clients and partners. The act of proving your data protection measures reassures them you’re safe to work with. Trust is hard to earn in the B2B market. Yet, these questionnaires make it visible and verifiable through documented answers.
Risk Identification: They also shine a light on risks that could be overlooked. One of the biggest sources of breaches today is third-party relationships. A good cybersecurity questionnaire helps you uncover weak points, like an outdated backup process or missing access controls, before they escalate into bigger incidents.
Regulatory Conformance: For compliance teams, they’re a lifesaver. Whether it’s GDPR, ISO 27001, SOC 2, or HIPAA, a security compliance questionnaire helps prove that you have your controls in place and they are working as intended. Thereby, they turn a vague “yes, we’re compliant” into specific, documented evidence auditors can actually trust.
Internal Audits: A security questionnaire is also a great tool for internal health checks. To clarify, your security teams could use them quarterly to spot gaps and keep improving. Cybersecurity management is a continuous process, and questionnaires ensure that no details are overlooked.
Smooth Procurements: On the business side, these questionnaires facilitate a more efficient procurement process. Procurement teams rely on a cybersecurity questionnaire to evaluate whether a new supplier meets minimum security standards. For instance, when onboarding a new vendor or closing a deal, having a clear security questionnaire can help prevent vendor security issues.
HOW SECURITY QUESTIONNAIRES SUPPORT YOUR COMPLIANCE NEEDS
Security questionnaires are one of the most practical tools for staying on the right side of compliance. Most regulations today, like HIPAA for healthcare, GLBA (Gramm-Leach-Bliley Act) for financial data, and GDPR for EU personal data, require third-party risk management. Security questionnaires are a practical way to evidence due diligence. Imagine yourself as a small SaaS firm that must respond to a cybersecurity form in order to seal a deal with a large enterprise. Initially, you may experience a sense of overwhelm. But eventually, you would realize that it helped you to check gaps such as missing data retention policies and weak access reviews.
These questionnaires often align with standard security frameworks, which is why they’re so valuable. Businesses are also starting to use AI security questionnaire solutions to speed up responses and reduce human error while keeping evidence accurate. If you’ve ever seen ISO 27001, SOC 2, or NIST CSF requirements, you’ll notice many questions map directly to them. Things like “Do you encrypt data at rest?” or “How do you manage third-party risk?” aren’t random. They’re core compliance requirements in disguise. If your answers are solid, you’re halfway toward passing an audit or getting certified.
Some teams now rely on AI security questionnaire tools to organize responses and flag gaps before auditors find them. Moreover, the answers don’t just sit in a file somewhere. They show up in audits, board risk reports, and even in contracts where you agree to protect customer data. They can become evidence if there’s ever a breach or dispute, so honesty and accuracy matter. Thus, a security questionnaire is a mirror that shows how secure your business really is. So, treat them as a chance to tighten your risk management program. Now, let’s explore the best practices for handling security questionnaires in the upcoming section.
BEST PRACTICES FOR RESPONDING TO OR ISSUING SECURITY QUESTIONNAIRES
Responding to or issuing security questionnaires doesn’t have to feel like a painful chore. You could actually build trust by doing it right.
For Vendor Assessment:
If you’re a vendor, then accuracy is everything. Therefore, don’t rush your answers just to hit a deadline. You may face difficulties later when a client requests proof. Always take enough time to gather real evidence, such as screenshots, policy excerpts, and SOC 2 reports that back your claims. Also, update your security policies to avoid having to explain outdated practices. Many SaaS vendors use an AI security questionnaire to speed up due diligence during vendor onboarding. This software-driven process uses artificial intelligence to automate the assessment process, which helps verify a vendor’s security posture. Furthermore, it is advisable to create a solid security questionnaire playbook that clearly defines roles for each domain using a RACI model. This method avoids confusion regarding ownership. Plus, it is essential to maintain a central repository with mapped evidence and to set a regular review cadence to keep responses updated.
Tips for Organizations that Issue Security Questionnaires:
A cybersecurity questionnaire is a practical tool to identify security gaps and improve internal processes. If you’re responsible for sending questionnaires, always consider simplifying the process for everyone involved. Keep the design clear and avoid asking the same question twice in ten different ways. Furthermore, tier your vendors so that a small marketing agency isn’t answering the same 300-question survey as a critical SaaS provider.
Use Recognized Standards to Save Time:
It is always preferable to use standardized frameworks when creating a security questionnaire. Moreover, using standardized frameworks like the Standardized Information Gathering (SIG) Questionnaire or the Consensus Assessments Initiative Questionnaire (CAIQ) saves everyone time and ensures you’re covering the right ground.
- SIG by Shared Assessments offers both a complete version and a lite version for due diligence.
- CAIQ by Cloud Security Alliance focuses on cloud-specific controls and maps directly to the CSA Cloud Controls Matrix.
Common Pitfalls:
Vague answers like “we follow best practices” are not sufficient for security teams. Missing evidence or sharing outdated policies could sink trust fast. Therefore, always pretend that the person reading your answers knows nothing about your company and will double-check everything. This mindset will help keep your responses clear, fresh, and defensible. Automating your security compliance questionnaire saves time and ensures consistent, accurate responses.
CONCLUSION
In the current business world, every deal, partnership, or vendor relationship carries hidden risk. A solid cybersecurity posture is your ticket to trust, faster deal closures, and fewer compliance headaches. Moreover, having a strong cybersecurity posture will also help your organization face a security questionnaire with ease. However, many businesses miss out on valuable opportunities due to hasty, incomplete, or outdated answers and evidence. Hence, this results in delayed contracts, missed revenue, and reputational damage.
This is where CertPro steps in to help you build the right security controls, policies, and evidence libraries so you can face any security questionnaire with confidence. Our team works closely with you to map requirements to frameworks like ISO 27001, ISO 42001, SOC 2, and GDPR. To add on, we use compliance automation tools to simplify security questionnaires by auto-filling responses, centralizing evidence, flagging gaps, and tracking progress. Thereby, we save time, ensure accurate answers, and keep your business audit-ready all year round.
So, don’t wait for a security compliance questionnaire to land in your inbox and disrupt a deal. Preparing now means faster approvals, fewer risks, and stronger customer trust. Connect with CertPro today and turn security questionnaires from stressful roadblocks into a growth advantage.
FAQ
What is a compliance questionnaire?
A compliance questionnaire is a structured list of questions that checks whether a business follows required regulations, policies, and security controls. It helps identify gaps, prove adherence to standards like ISO 27001 or GDPR, and prepare for audits efficiently.
What is the standard security questionnaire?
A standard security questionnaire is a pre-built, widely accepted set of security questions, like SIG or CAIQ, used by companies to evaluate vendors. It ensures consistency, saves time, and helps assess risk across data protection, access control, and compliance areas.
What are some examples of security questions?
Common security questions include “Do you encrypt data at rest?”, “How is access controlled?”, “Do you have incident response plans?”, and “Are employees trained in security awareness?” These questions verify security readiness and compliance with frameworks like SOC 2.
What is a security risk assessment checklist?
A security risk assessment checklist is a step-by-step guide to identify threats, vulnerabilities, and controls in an organization. It includes tasks like reviewing access permissions, testing backup plans, and documenting mitigation measures for compliance and audit readiness.
How does automation help in managing security questionnaires?
Automation speeds up questionnaire responses by centralizing data, reusing past answers, and auto-filling repetitive fields. It reduces manual errors, ensures consistency, and helps compliance teams respond faster during vendor assessments, procurement processes, or regulatory audits.

About the Author
RAGHURAM S
Raghuram S, Regional Manager in the United Kingdom, is a technical consulting expert with a focus on compliance and auditing. His profound understanding of technical landscapes contributes to innovative solutions that meet international standards.





