
HITRUST COMPLIANCE: ENTERPRISE ROADMAP TO CERTIFICATION
HITRUST compliance is the process of aligning your security program with the HITRUST CSF (Common Security Framework) and obtaining a certifiable, third – party – validated report. Originally developed for healthcare, HITRUST is now used across industries to manage cyber risk and regulatory compliance in a single, unified framework. A 2025 HITRUST trust report states that organizations with HITRUST certification report an incident rate of just 0.59%, which means 99.41% of them remained breach – free in 2024. This is a remarkable improvement over the previous years.
Data security and compliance are crucial elements of any business organization handling sensitive data. In this context, the healthcare industry demands extra security and protection. Most of these businesses collect, store, process, and transfer sensitive patient data as part of their daily operations. They do have some legal mandates, like HIPAA, but what they lack is a comprehensive cybersecurity framework that helps them build a solid security posture.
This void led to the emergence of HITRUST CSF (Common Security Framework). HITRUST stands for Health Information Trust Alliance, which was founded in 2007. This organization established the HITRUST CSF as a certifiable framework for healthcare organizations. To elaborate, they guide businesses in handling information security risks and prove compliance with regulations and standards like HIPAA, ISO, NIST, and GDPR.
In this blog, we help you understand what is HITRUST, why it is important, and who needs to adhere to its security standards. Furthermore, we will learn the differences between HIPAA vs. HITRUST and the key steps involved in the HITRUST certification process.
Tl; DR:
Concern: Healthcare and other data – driven businesses handle multiple regulations (HIPAA, ISO, NIST, and GDPR) without a single, reliable process to prove security maturity. This leads to higher breach risk, slow vendor approvals, audit fatigue, and uncertainty when customers or regulators ask for proof.
Overview: HITRUST CSF (Common Security Framework) is a certifiable, unified security framework that is based on major global standards and privacy laws. Furthermore, it offers three assessment types (e1, i1, r2) and a detailed, testable control set that turns scattered compliance efforts into one structured program and recognized certification. But most organizations struggle to achieve HITRUST compliance due to a lack of guidance and a clear roadmap.
Solution: Therefore, this blog provides you with a clear and step – by – step roadmap to obtain HITRUST certification. Based on it, the businesses must start treating HITRUST compliance as a continuous program instead of a one – time project. To begin with, define your scope early. Then run a readiness assessment to assess your current security posture. Thereafter, address the identified gaps and conduct a complete validated assessment with an Authorized External Assessor. Finally, ensure continuous monitoring of your controls over time. This steady approach lowers risks of security incidents, boosts procurement, improves cyber insurance results, and helps your organization build a security posture.
WHAT IS HITRUST COMPLIANCE?
HITRUST was established to provide companies with a single, trustworthy framework for addressing cybersecurity risk management across a matrix of third – party assurance assessments. Their primary aim is to reduce, consolidate, or eliminate the need to follow multiple regulations, which leads to multiple reports demonstrating compliance with each standard. In this context, businesses must understand that HITRUST does not replace any laws, but it simplifies your compliance work.
Instead of requiring businesses to manage multiple regulations from ISO, NIST, HIPAA, PCI, GDPR, and other new mandates, HITRUST simplifies the process. The HITRUST CSF combines them, maps the overlapping requirements, addresses the gaps, and turns them into one certifiable system.
Within HITRUST CSF, you’ll find broad control categories, often called domains. Inside each domain, HITRUST sets out specific goals and provides control references that show how each control matches up with important standards. Additionally, it outlines the requirement statements, which describe what you actually need to implement.
The CSF also knows that each organization is unique and doesn’t require the same level of rigor while aiming for HITRUST compliance. Therefore, it has outlined three levels of assessments suitable for all business sizes and security readiness.
- HITRUST Essentials (e1 assessment): This is the lightest option, covering essential controls for small teams or low – risk use cases.
- HITRUST Implemented (i1 assessment): This assessment goes a step further, focusing on implemented practices that hold up year after year. It is suitable for businesses that demand a stronger assurance for customers and regulators.
- HITRUST Risk – based (r2 assessment): It is regarded as the gold standard for information security management due to its comprehensive control requirements. To add on, it’s tailored, risk – based, and built for companies with complex operations or strict customer demands.
This layered design makes the CSF practical, achievable, and trusted across industries, which is why so many growing businesses see it as a long – term investment rather than another compliance chore.
HIPAA VS. HITRUST: WHAT ARE THE KEY DIFFERENCES?
HITRUST vs. HIPAA are often used for similar purposes during business conversations. Yet they are not the same and serve very different purposes. To clarify, HIPAA is a US federal law. It creates legal duties for covered entities and business associates. On the other hand, HITRUST is a private certifiable framework. It provides organizations with a structured process to prove their security and privacy practices. Both matter, but for different reasons.
HIPAA outlines broad obligations for privacy, security, and breach reporting. However, it lacks an explanation for the process of meeting these rules. This flexibility can benefit small teams, but it often leads to uncertainty, particularly when customers request evidence of your controls.
In contrast, HITRUST offers detailed controls, clear testing steps, and a rigorous validation process. Because the HITRUST CSF maps directly to HIPAA, it helps organizations show alignment, which helps you to prove auditor and client expectations.
When considering HIPAA vs. HITRUST, the nature of enforcement acts as a key differentiating factor. To clarify, for HIPAA, the enforcement happens when the Office for Civil Rights investigates a breach or complaint.
Conversely, the HITRUST compliance requires an Authorized External Assessor, a formal QA review, and a certification timeline. Furthermore, while considering the frequency of assessments between HIPAA vs. HITRUST, the former is more flexible. But HITRUST compliance follows a structured assessment cycle and procedure.
If your business sells into health care, works with enterprise clients, or serves customers across multiple states or countries, HITRUST can be a suitable option. It builds trust with buyers and creates a single structure for meeting many regulatory needs. So while HIPAA is mandatory, HITRUST gives you an advantage when strong proof of your security posture is required.
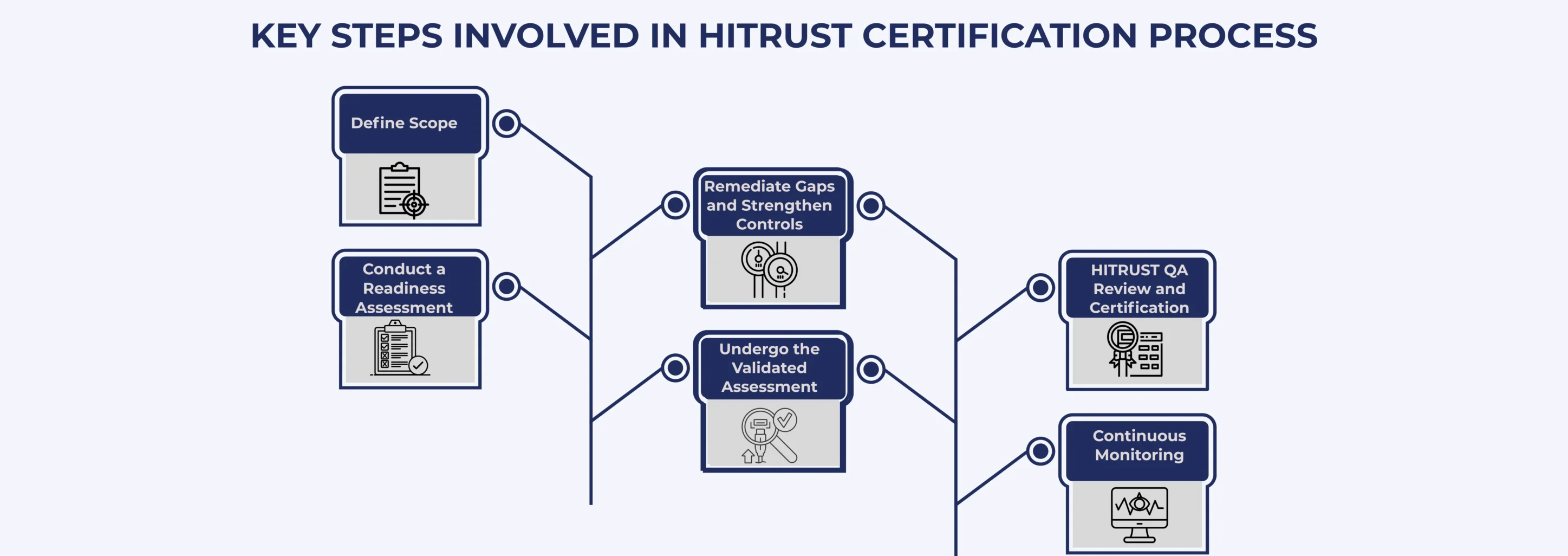
KEY STEPS INVOLVED IN HITRUST CERTIFICATION PROCESS
HITRUST certification works best when enterprises treat it as a steady process rather than rushing to finish it soon. Because each stage builds context, confidence, and clarity on your organization’s data protection process. The following steps outline the path enterprises follow during their HITRUST compliance process.
- Define Scope: Identify the systems, applications, business processes, and data types that fall under the HITRUST CSF framework. Additionally, focus on environments handling PHI or other regulated data and note where other frameworks (HIPAA, GDPR, PCI DSS, and SOC 2) apply. This process of defining a clear scope helps you select the right HITRUST assessment level.
- Conduct a Readiness Assessment: Once scoping is done, compare your current controls against HITRUST CSF requirements. This readiness assessment highlights gaps in policies, access control, monitoring, training, vendor management, and incident response.
- Remediate Gaps and Strengthen Controls: This is the stage where your firm has to take action on the identified gaps. Implement or improve controls to close identified gaps. Accordingly, update policies, refine access rules, enhance logging and monitoring, and improve incident handling. During this phase, build your evidence library, including system configurations, logs, training records, risk assessments, and meeting minutes, to demonstrate the effectiveness of your controls.
- Undergo the Validated Assessment: Once your environment is stable, an Authorized External Assessor checks your implementation. They review evidence, interview your teams, and score controls across maturity levels. Moving forward, if they find any issues, you must respond with Corrective Action Plans (CAPs).
- HITRUST QA Review and Certification: HITRUST performs a final quality review, validates the assessor’s scoring, and issues your certification or validated report if you meet the thresholds. Plus, the timelines here ultimately depend on the assessment type (e1, i1, r2) and the complexity of your environment.
- Continuous Monitoring: Never consider certification as the end; it’s the beginning of your security program. Therefore, continuously monitor key controls, perform interim reviews (especially for r2), and complete annual or biannual updates. This culture of continuous monitoring could help you stay audit – ready and adapt to new threats, technologies, and regulatory changes.
BENEFITS OF HITRUST COMPLIANCE
Enterprise firms choose HITRUST compliance because it gives them an independent, certifiable framework to prove the effectiveness of their security controls. Thereby, the HITRUST CSF removes the need for the daunting task of adhering to multiple standards and regulations.
A Single, Harmonized Control Framework
HITRUST maps requirements from HIPAA, NIST, ISO, PCI, and several other standards into one unified framework. Hence, instead of repeating the same control work under ten different names, your team could implement HITRUST CSF once and apply it everywhere.
Faster Procurement and Fewer Roadblocks
Large buyers expect clear evidence of your security posture and risk management. They don’t want vague statements or security summaries. A HITRUST certificate gives procurement teams the proof. This validated assessment will move your stalled deals to get approved in days.
Better Insurance Outcomes
Cyber insurers value third – party validated frameworks like HITRUST. This often leads to more stable insurance premiums and straightforward renewals because underwriters can rely on consistent control testing.
Measurable Risk Management
HITRUST’s prescriptive controls and recurring assessments monitor risks without confusion. You improve consistency because the framework forces regular audits, updates, and revalidation. Eventually, this process leads to building a well – established and measurable security posture.
Regulatory Compliance with Global Value
While HITRUST is well known in health care, its value goes far beyond HIPAA. The CSF maps to international standards and privacy laws, which helps global companies prove compliance across regions.
CHALLENGES AND BEST PRACTICES OF HITRUST COMPLIANCE
Businesses begin their HITRUST compliance journey with the right intentions but still face avoidable problems. These issues rarely come from technology alone. Most often, they arise from rushed planning, unclear roles, or pressure to finish quickly.
- One of the most common mistakes is starting with a vague scope. When teams do not know which systems, data, or processes fall under HITRUST, they lose time and fix unexpected gaps later.
- Another challenge is underestimating the effort needed to update controls and policies. Remediation does take time, and businesses must realize that shortcuts usually slow down the process rather than speeding it up.
- Documentation also becomes a hurdle here. HITRUST compliance depends heavily on real, traceable evidence. Therefore, weak or scattered records make it challenging to prove how the environment works.
- Additionally, many organizations also move into the assessment phase before checking the effectiveness of the controls. This leads to repeated work and missed deadlines.
- Plus, a lack of clear control owners and weak continuous monitoring adds more friction as the program grows.
However, the path becomes smoother when teams follow a few steady best practices.
- A readiness assessment sets the right baseline.
- Careful scoping helps everyone work with clarity. Assigning owners for each control builds accountability.
- Keeping a well – organized evidence library saves hours during audits.
- Stable control operation over time builds confidence for the validated assessment.
- Tools and compliance platforms can help, especially for larger teams. They reduce manual effort and give leaders transparency over the process.
Finally, leadership support matters more than most people expect. When executives treat HITRUST as a strategic need, teams receive the time, resources, and direction to succeed.
CONCLUSION
HITRUST compliance is a time – intensive process that demands steady focus and effort. But its benefits are relevant to every modern business. Data risks grow each year, and customers now expect clear evidence that companies can protect their sensitive data. Because of this shift, HITRUST compliance has become a symbol of security and reliability.
Delaying this work often creates hidden costs, which include delayed deals, longer vendor reviews, and the piling up of security questions during sales cycles. When organizations define their scope early, check their readiness with honesty, fix gaps with discipline, complete the assessment with confidence, and keep improving over time, they build a stronger foundation for their future growth. This approach gives leaders clarity over their operations, builds trust with partners, and supports long – term growth. To sum up, HITRUST compliance is a practical investment in trust, stability, and market credibility. It acts as a strategic catalyst that boosts faster and safer growth.
FAQ
What does HITRUST stand for?
HITRUST stands for Health Information Trust Alliance. It creates a unified security and privacy framework. This framework helps organizations protect sensitive data. It also supports compliance with many standards. Therefore, many businesses use it to guide strong security practices.
Is HITRUST certification mandatory?
HITRUST certification is not mandatory. However, many healthcare organizations ask for it because it shows strong security controls. It also helps businesses build trust. As a result, many companies choose it to meet client and partner expectations.
What is the difference between HITRUST and SOC 2?
HITRUST focuses on healthcare data protection. It combines many security and privacy standards in one framework. SOC 2 reviews security controls for service organizations. It applies to many industries. Therefore, businesses choose between them based on their compliance needs.
How long is the HITRUST certification valid for?
The validity of HITRUST certification is based on their portfolio level. To elaborate, the e1 and i1 assessment certifications are valid for one year. But the r2 assessment process is valid for 2 years. Yet, the interim review and ongoing control maintenance are necessary for all the levels.
What are the challenges in the HITRUST certification process?
The HITRUST certification process requires strong documentation and control testing. Many organizations struggle with time, resources, and evidence collection. They also face strict assessment criteria. Therefore, planning early and using expert support can reduce these challenges.






