NON-COMPLIANCE FINES & SANCTIONS 2026: WHAT BUSINESSES MUST KNOW NOW
Non – compliance fines are rising fast, and the business leaders are already feeling the pressure. As industry – leading auditors, we often encounter such scenarios during calls with businesses. They inform us that they’ve “done the basics” but still worry something might slip through.
That feeling is genuine because the global cybersecurity rules and privacy standards are more complex now. Furthermore, the global regulators are working together more closely, and they expect businesses to prove that their systems, policies, and controls actually function as intended.
Cybersecurity regulations in several regions include tight reporting deadlines, strict breach procedures, and new technical controls. Additionally, privacy regulators are enforcing stricter measures against inadequate data handling.
In this context, following security frameworks such as ISO 27001, ISO 42001, and regulations like HIPAA and GDPR can feel like a heavy burden. But ignoring relevant standards is far more expensive. It increases your exposure to fines, investigations, insurance challenges, and cross – border regulatory inquiries. Accordingly, you will face fines, investigations, and cross – border inquiries. A breach in one country can spark attention from regulators in three or four markets at once.
The exposure grows even more in 2026 because new rules are rolling out across the EU, US, UK, APAC, and India. Many of these rules push businesses to adopt mandatory security measures. Others tighten the way companies collect and share personal data.
Consider 2026 as the year when your compliance program will be reviewed thoroughly. This blog explains the trends shaping these penalties, the regions driving the biggest changes, and the risks that catch unprepared companies. It also gives you a simple plan to stay ahead of these fines and complex regulatory changes.
Tl; DR:
Concern: Non – compliance fines and sanctions are rising fast across the EU, US, UK, APAC, and India. Regulators are coordinating more closely and expect proof that your controls work in both practice and policy.
Overview: New laws and regulations such as the EU AI Act, the Digital Services Act (DSA), and India’s DPDP Act are making rules stricter about reporting breaches, getting consent, managing AI, and transferring data across Global turnover and the scale of impact increasingly influence the non – compliance fines.
Solution: Map all applicable laws and standards, run a readiness assessment, fix security and documentation gaps, test your breach response, and stay audit – ready all year. Partnering with experienced auditors like CertPro can help you reduce fine exposure and maintain certifications.
WHAT IS NON – COMPLIANCE?
Non – compliance refers to a state where a company fails to meet the laws, regulations, standards, or internal rules (internal risk management framework) that protect data and maintain system security. It often occurs when teams skip required controls, mishandle personal information, or fail to meet deadlines for mandatory reports.
These gaps eventually lead to real consequences like fines, lawsuits, and damaged trust. Businesses often don’t fail to follow these regulations on purpose. They simply move fast, ship products, and assume that security or privacy is “covered somewhere.” That’s usually when problems start.
Non – compliance can take many forms. For example:
- They fail to maintain accurate records of processing activities (RoPA) or skip required Data Protection Impact Assessments (DPIAs) when deploying new systems.
- Some may run critical systems without strong access controls, encryption, or patching.
- Some firms discover a breach but report it too late, demonstrating a weak incident reporting policy.
- Others depend on vendors without checking whether those partners follow strict data protection practices.
- Even simple misses, like poor documentation or skipped internal audits, count as non – compliance.
- Furthermore, in some cases, employees or leaders knowingly bypass rules because they feel pressure to move faster.
Recent enforcement shows how common these issues are. LinkedIn was fined hundreds of millions of euros for unlawful profiling and targeted advertising under GDPR. Regulators in France fined Google and Shein in 2025 for placing cookies and showing targeted ads without valid consent or clear opt – out choices. These cases remind businesses that regulators actively watch the way you collect data, use tracking tools, and safeguard customer information.
The following are some of the major factors that make non – compliance more likely.
- No clear ownership where compliance is “everyone’s job,” so no one is truly accountable.
- Outdated or missing policies with procedures existing in drafts but never reaching the teams that use them.
- Fast product changes, where new features ship without security or privacy audits.
- Unvetted vendor presence where SaaS tools and cloud providers slip into your stack without proper security review.
- Weak training for employees, where they never learn what the rules are or why they matter.
When these issues add up, non – compliance becomes a real business risk rather than a technical problem.
HOW REGULATORS WILL PENALIZE YOU IN 2026
Regulators worldwide are planning to intensify their enforcement measures. They’re moving fast because too many incidents still happen due to weak controls, poor data handling, or late reporting. This shift reflects broader trends in compliance that show regulators want stronger oversight.
They expect CISOs and compliance teams to monitor continuously, act early, and report breaches within the established time frame. This new approach implies that non – compliance will no longer be considered a minor oversight. Instead, it’ll be treated as a signal that the business didn’t take safety seriously.
How Enforcement Works: Penalty Types and Who Issues Them
Penalties for non – compliance now come in many forms. Such as, administrative fines, civil suits, criminal referrals for serious cases, and even contract bans. Some firms face de – platforming, higher processing fees, or costly remediation orders.
Enforcement bodies vary by region. Data protection authorities lead privacy cases. Meanwhile, the national cybersecurity agencies handle security failures. Healthcare, cloud, and SaaS regulators review sector-specific risks. Similarly, the payment bodies like PCI watch card data. Even clients push penalties when your firm fails audits. Moreover, the certification bodies also step in by suspending or withdrawing their certifications if you fail to prove secure business practices.
Why Certification Gaps Now Trigger Serious Action
Missing or lapsed certifications used to be treated as minor delays in the compliance process. Today, they are early warning signs for buyers, insurers, and sometimes regulators that your controls may not be reliable or consistently applied. As a result, when ISO 27001 or SOC 2 lapses, your buyers assume weak controls. Regulators also consider them signs of deeper process issues. This issue is another example of how trends in compliance influence modern risk decisions. It’s another area where non – compliance quietly turns into a business liability.
How Non – Compliance Fine Calculations Work in 2026
Penalty models depend on the specific law. Some systems, such as GDPR and UK GDPR, use turnover – based fines up to 4% of annual global revenue or a fixed cap, whichever is higher. Meanwhile, others set fines per exposed record or per day of non – compliance. In almost every system or jurisdiction, the final number depends on factors like intent, cooperation, past history, the number of affected individuals, and the speed of your response.
KEY AREAS THAT TRIGGER NON – COMPLIANCE FINES FOR BUSINESSES
Most enforcement actions fall into four areas, such as data protection, cybersecurity, certification and audit failures, and poor breach management.
Data Protection Laws: Regulations like GDPR, CCPA, and CPRA have changed the way companies handle personal data. Although the rules appear clear on paper, they require strict adherence. Fines often hit businesses that collect data without proper consent, store sensitive information longer than needed, or mismanage a breach by delayed reporting. To add on, even a simple error, like an outdated privacy notice, is enough to trigger investigations.
Cybersecurity Requirements: Frameworks such as ISO 27001, SOC 2, and HIPAA expect companies to maintain strong controls. When those controls fail, fines and penalties follow. To elaborate, weak access controls, poor logging, missing encryption, or a slow incident response process can expose an organization’s security posture. A single overlooked alert or an unpatched server could cause a breach that escalates quickly.
Certification and Audit Failures: Many businesses struggle here because audits require clean documentation and consistent evidence. Missing risk assessments, incomplete asset lists, or gaps in vendor reviews could lead to failed ISO or SOC audits. Furthermore, auditors review your risk management framework to check if your security controls work as expected.
Breach – Related Penalties: When a company can’t detect or contain a breach quickly, the financial impact grows fast. Delayed reporting, unclear incident response procedures, or poor security hygiene can lead to lawsuits, claims, and reputational damage.
These risks are common, but they’re manageable with the right structure and discipline.
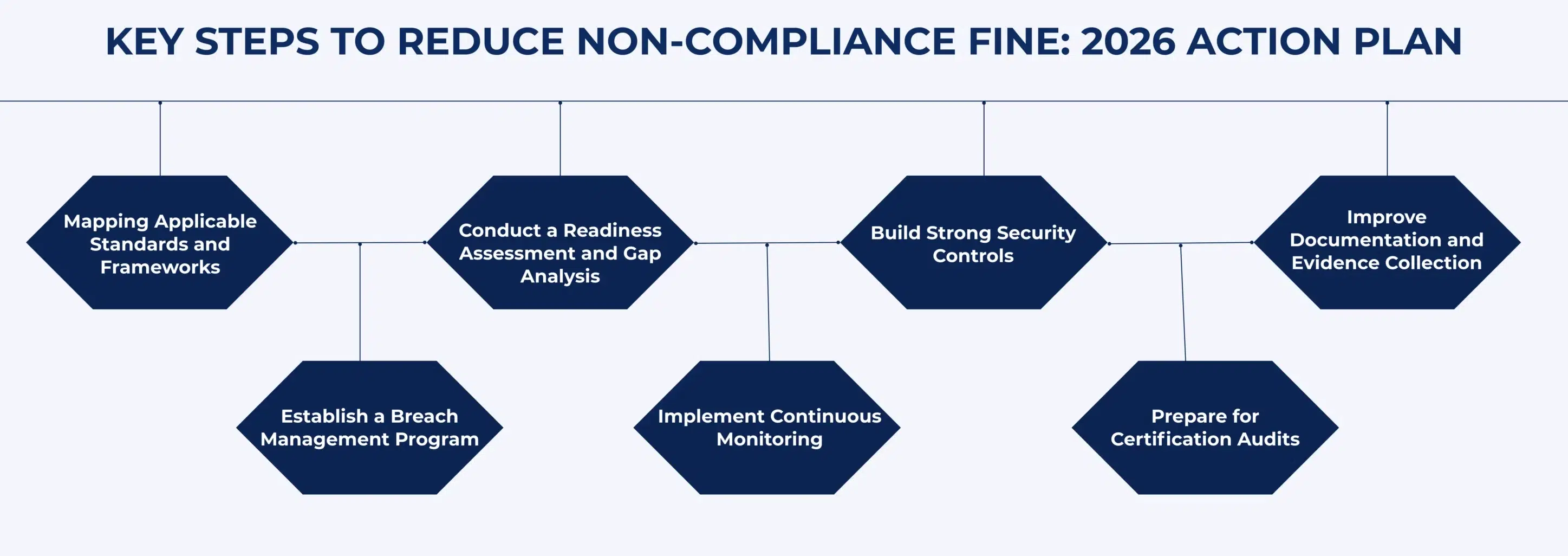
KEY STEPS TO REDUCE NON – COMPLIANCE FINE: 2026 ACTION PLAN
In this section, let’s learn about the key steps involved in building a solid plan that is necessary to avoid non – compliance fines and sanctions.
Mapping Applicable Standards and Frameworks
Begin the process by identifying every regulation that applies to your business. Consider it like checking all the road signs before a long drive. Many teams skip this step and later discover they missed a key requirement. Therefore, map GDPR, CCPA, HIPAA, ISO 27001, SOC 2, and any local laws in your target markets.
Conduct a Readiness Assessment and Gap Analysis
Now, it’s time to assess your current security posture. A simple readiness assessment will show you the strong controls and vulnerabilities. Hence, a clear gap list helps you focus on real risks and avoid non – compliance.
Build Strong Security Controls
Now, it’s time to boost your security posture. Accordingly, secure access controls, implement data encryption, and monitor security incidents.
Reinforce the basics that regulators and auditors expect:
- Strong identity and access management (MFA, least privilege, joiner – mover – leaver processes).
- Encryption in transit and at rest for sensitive data.
- Patch and vulnerability management with defined SLAs.
- Central logging, monitoring, and alerting for critical systems.
- Vendor due diligence and security clauses in contracts.
These controls prevent most avoidable incidents and directly reduce non – compliance risk.
Improve Documentation and Evidence Collection
Proper documentation mechanisms could protect you from noncompliance. Therefore, keep your policies current, your procedures practical, and your evidence centralized. At a minimum, maintain:
- Information security and privacy policies.
- Records of processing activities (RoPA).
- DPIAs for high – risk processing and AI use cases.
- Risk registers, asset inventories, and vendor registers.
- Training logs and incident records.
A mature risk management framework helps reduce fines by proving that your company manages risks in a structured way. Clean documentation is often the difference between a warning and a fine.
Establish a Breach Management Program
Despite all the planned defenses, companies do face some unforeseen security incidents. The way to avoid non – compliance depends on your incident – response policy. So, build:
- A 24/7 incident reporting channel.
- Policies that match with regulatory deadlines (For example, GDPR’s 72 – hour breach notification and Singapore PDPA’s 3 – day limit for notifiable breaches).
- A communications plan for regulators, customers, and partners.
Implement Continuous Monitoring
Establish and implement continuous monitoring policies with simple dashboards, alerts, and vendor scorecards. This approach helps you identify problems early, rather than reacting to them after a disaster occurs.
Prepare for Certification Audits
Conduct internal audits, address findings, and maintain an audit folder where all the audit – related documents are stored. This keeps your team ready for external audits.
To sum up, reducing non – compliance fines comes down to strong controls, solid documents, and steady audit readiness.
HOW NON – COMPLIANCE FINES APPLY ACROSS EU, US, UK, AND APAC
As global auditors, we understand that the regulations and standards are different everywhere, yet their pressure feels the same. If your business indulges in cross – border data transfers, you’ll see how each region treats non – compliance.
European Union (EU)
- GDPR sets the toughest fines. Regulators expect quick breach reports and strong security controls.
- New laws like the DSA (Digital Services Act) and the EU AI Act expand oversight for platforms and AI – heavy products.
- ISO 27001 and ISO 27701 help companies prove discipline. Businesses that keep these certificates current and updated have accelerated deal closures in the EU.
- They expect strict action when consent flows, profiling, or monitoring tools don’t meet requirements.
United States (US)
- The US runs on a patchwork of state privacy laws like CCPA, CPRA, Colorado, and Virginia.
- HIPAA enforcement stays active, especially after healthcare breaches.
- SOC 2 is a key factor in procurement and sales cycles. As enterprise vendors, you will lose contracts if you can’t exhibit a clean report.
United Kingdom (UK)
- The ICO has taken a steady enforcement path since 2023. As a result, you will find non – compliance penalties for poor security basics and unstructured data practices.
- UK GDPR mirrors the EU in many areas, but enforcement feels more risk – based.
- Under UK GDPR and the Data Protection Act 2018, the ICO can impose fines up to £17.5 million or 4% of global annual turnover for serious violations.
Asia – Pacific (APAC)
- Countries like Singapore (PDPA), Thailand (PDPA), and India (DPDP Act 2023 + DPDP Rules 2025) now run strong privacy laws with penalties.
- ISO 27001 adoption continues to rise. Many APAC buyers treat it as a trust signal.
- Local regulators focus on data misuse, weak access controls, and unmanaged vendors.
To conclude, non – compliance fines vary by region, but privacy, cybersecurity, and audit failures remain common risk drivers worldwide.
CONCLUSION
Business leaders are already feeling the pressure in 2026. Regulators, with strict deadlines and sharp breach notification mechanisms, are no longer lenient when a security incident happens. Non – compliance fines are rising because too many companies still treat security and privacy as “later tasks,” and that delay turns into unavoidable consequences.
This is why a strong audit partner matters, and CertPro is a strategic choice for it. We’re a global compliance audit firm with immense experience across regulated industries. As a registered CPA firm under AICPA, CertPro can deliver end – to – end SOC 2 audits and attestation services.
We also support ISO 27001, ISO 27701, ISO 42001, GDPR readiness, HIPAA, PCI, and several national standards across key regions, as we have a strong global network of regional associates. Moreover, we excel in virtual audits, as established by the standards and procedures.
Delaying compliance now costs far more than doing it right the first time. To clarify, one missed renewal, one weak control, or one late breach notification could lead to unexpected security issues.
You don’t have to take that path. If you want clear guidance, faster certification, and a partner who actually understands your business, connect with CertPro today. Together, let’s protect your business growth and resilience.
FAQ
What is meant by non - compliance in business?
Non – compliance in business occurs when a company fails to meet legal, regulatory, contractual, or internal policy requirements related to operations, security, or privacy. It often stems from weak controls, inadequate documentation, insufficient training, or outdated policies.
What are the consequences of non - compliance?
Non – compliance can lead to fines, legal action, and forced corrective steps. It also hurts customer trust and slows deals. Many companies lose contracts or face tougher audits because they can’t show proper controls or proof of their security measures.
What is non - compliance in healthcare?
Non – compliance in healthcare refers to violations of medical privacy rules, patient safety standards, and data protection laws. It often involves HIPAA gaps, weak access controls, or late breach notifications. These failures increase patient risk and trigger strong enforcement.
What is cybersecurity compliance?
Cybersecurity compliance means following security standards that protect systems and data. It includes risk assessments, access controls, monitoring, and incident reporting. Businesses use frameworks like ISO 27001, SOC 2, and NIST to build programs that pass audits and reduce exposure.
What is non - compliance with regulatory guidelines?
Non – compliance with regulatory guidelines occurs when a business fails to meet requirements set by privacy, security, financial, or industry regulators. Examples include missed filing or reporting deadlines, inadequate or inaccurate documentation, weak security and privacy controls, or late incident and breach notifications. All these will ultimately lead to penalties, remediation orders, and regulatory scrutiny during future audits.