SOC for Cyber Security: Using SOC Audits to Prove Cyber Security Maturity
Customers do not trust security promises anymore. They want real-time evidence to prove it. Would security questionnaires or policy documents suffice? No. Buyers now demand independent verification from structured and independent audit processes they can trust. That’s where SOC audits come in. Licensed CPA firms conduct these examinations to assess the design and operating effectiveness of security controls over a defined examination period. Unlike internal audits and assessments that you run yourself, independent SOC 2 audits are valued and trusted more, as they are conducted by audit experts based on AICPA standards.
Still, many companies do not really get what SOC audits measure. Often, they wonder if they truly show cyber security maturity. This guide clears things up. You will learn how these audits work and why customers care so much about them.
A SOC 2 audit is an independent examination performed by a licensed CPA firm in accordance with AICPA SSAE standards. It evaluates whether a service organization has designed and operated controls that meet the Trust Services Criteria for security, availability, processing integrity, confidentiality, and privacy.
Tl; DR:
Concerns: Organizations struggle to prove cyber security maturity to customers and stakeholders. Internal assessments lack credibility, while customers demand independent verification of security controls. Without recognized assurance methods, sales cycles extend and enterprise opportunities disappear.
Overview: This guide explains how SOC audits demonstrate cybersecurity maturity through independent verification. Learn about SOC 2 requirements, Trust Services Criteria, audit processes, and how organizations use SOC reports to build customer trust and accelerate vendor evaluations.
Solution: Pursue SOC 2 Type 2 audits conducted by licensed CPA firms. Implement documented controls, collect evidence throughout examination periods, and address exceptions promptly. Use resulting reports to prove sustained security discipline to customers and stakeholders.
SOC IN CYBER SECURITY
Definition of SOC in the Context of Cyber Security
In cybersecurity, SOC audits evaluate whether service organizations have designed and operated controls that meet the AICPA Trust Services Criteria.
The American Institute of Certified Public Accountants (AICPA) created these audit frameworks. They help companies show customers their controls actually work. So when vendors mention “SOC” during sales talks, they mean these independent examinations.
SOC Audits vs Internal Security Assessments
Internal security checks help you find weak spots and fix them. It is useful but really not credible for outsiders. Companies naturally show themselves in the best light possible when checking their own work.
SOC audits work differently. Licensed CPA firms stay independent from the companies they examine. These auditors follow strict rules and lose their licenses for bad work. That is why customers believe the results of third-party SOC audits way more than internal reports.
Also, SOC audits check if your stated controls actually worked throughout a set period. This distinction is critical when demonstrating sustained control discipline.
Why SOC Audits Matter for Cyber Security Assurance
Good intentions don’t prove security. Customers need evidence that controls work consistently under normal conditions. But they can’t visit every vendor’s office or check every security log themselves. Therefore, many organizations rely on independent auditors to evaluate controls through SOC for cyber security, which provides structured and standardized assurance over security practices.
SOC audits test whether security controls ran as promised over several months. Results show what controls exist plus whether they actually worked when tested. Good SOC results prove you maintain security discipline over time, not just during quick assessment windows.
SOC AUDITS
Overview of SOC Audits and Their Purpose
A SOC audit is an independent check by a licensed CPA firm. The firm verifies whether your controls meet specific standards and worked properly during an examination period. These checks typically focus on controls affecting customer data, financial information, or service reliability.
The audit creates a formal report you share with customers. This report provides an explanation of the systems inspected, the controls in place, and the auditor’s findings. Customers can then judge whether your security practices meet their needs without running lengthy checks themselves.
TYPES OF SOC AUDITS
The AICPA defines three core SOC audits. They are detailed below
| Type | Focus | Who Uses It |
|---|---|---|
| SOC 1 | Financial reporting controls | Companies affecting customer financials |
| SOC 2 | Security and related controls | SaaS, cloud services, and tech vendors |
| SOC 3 | Summary of SOC 2 | Public marketing and light reviews |
For cybersecurity assurance, the SOC 2 audit is the most relevant SOC examination. Security is required for all SOC 2 engagements, and it checks security controls against the AICPA Trust Services Criteria.
Organizations whose services impact customers’ financial statements primarily use SOC 1 examinations, which concentrate on controls relevant to financial reporting. While SOC 1 may include IT controls, its objective is financial reporting assurance rather than general cybersecurity validation.
SOC 3 reports are summary versions of SOC 2 reports intended for public distribution. They confirm that a SOC 2 examination was performed but do not include the detailed description of tests of controls and results. Vendor due diligence requires transparency into control testing and operating effectiveness, most enterprise buyers request a full SOC 2 Type 2 report instead.
When Organizations Are Expected to Undergo SOC Audits
Companies pursue SOC audits because customers ask for them during vendor reviews. SaaS companies, cloud providers, and tech firms handling customer data face these requests regularly. Companies serving enterprise customers or regulated industries see even more pressure.
No regulation generally requires organizations to obtain a SOC audit. Instead, demand is driven primarily by market expectations and vendor due diligence requirements. When enterprise customers require a SOC 2 report as part of their procurement process, service organizations pursue the examination to remain competitive and maintain sales momentum.
Timing is strategic. Organizations should ideally complete their first SOC audit before entering major enterprise sales cycles or contract negotiations. Once established, maintaining an annual SOC 2 examination cycle ensures customers receive current reports and demonstrates ongoing commitment to control discipline and independent assurance.
SOC AUDITS AND CYBER SECURITY MATURITY
Understanding Cyber Security Maturity Models
Cybersecurity maturity models help companies check how developed their SOC for cyber security programs are. These models usually show stages from basic awareness up to optimized, always-improving programs. Companies use them to spot gaps and plan fixes systematically.
Common maturity signs include written policies, defined processes, consistent use, ongoing monitoring, and continuous improvement. As companies move up maturity levels, their security practices get more formal, measurable, and reliable.
How SOC Audits Align With a SOC Maturity Model
SOC for cyber security audits don’t assign maturity scores. But they check maturity signs through examining control design and how well controls work. Companies with mature security usually do better in SOC audits because their controls are well-documented, consistently used, and properly watched.
A mature company keeps clear policies, trains staff regularly, watches control performance, and fixes issues quickly. These habits create the documented proof auditors need to verify controls work. Companies with spotty security practices struggle to show consistent control operation over long periods.
So while SOC audits don’t explicitly score maturity, they effectively measure whether you’ve achieved the discipline that marks mature security programs.
Using SOC Audits to Demonstrate Control Maturity Over Time
One SOC audit shows a snapshot during a specific period. Multiple back-to-back SOC audits show sustained maturity over years. Companies that regularly pass SOC audits without big exceptions show customers they keep security discipline despite business changes or staff turnover.
You can also show maturity growth by comparing results across years. Fewer exceptions, a bigger examination scope, or added Trust Services Criteria show customers your security keeps getting stronger.
Enterprise buyers rely on SOC 2 reports to evaluate third-party risk. The detailed testing of security controls provides structured evidence that supports vendor risk assessments, compliance programs, and board-level oversight.
SOC 2 AUDITS IN CYBER SECURITY
Why SOC 2 Is Most Relevant for Cyber Security
Among SOC types, SOC 2 tackles cybersecurity head-on. Unlike SOC 1 (which focuses on financial controls), SOC 2 checks how you protect data and keep systems secure. This SOC 2 is a perfect choice for tech vendors proving cybersecurity skills to customers.
SOC 2’s flexibility lets you pick criteria matching your specific services and customer promises. This focused approach gives more relevant proof than generic security certifications that might miss actual customer concerns.
SOC 2 Trust Services Criteria and Security Controls
SOC 2 audits check controls against Trust Services Criteria:
- Security: Stops unauthorized access (required for all SOC 2 audits).
- Availability: Keeps systems accessible as promised.
- Processing Integrity: Ensures accurate, complete, timely processing.
- Confidentiality: Protects confidential information.
- Privacy: Handles personal information properly.
Security shows up in every SOC 2 audit as the foundation. Then you add other criteria based on customer promises. Backup services add Availability. Payment processors add Processing Integrity.
SOC 2 Type 1 vs SOC 2 Type 2 Audits
SOC 2 has two versions with big differences:
SOC 2 Type 1 checks if controls were designed right on one specific date. The auditor confirms controls look good on paper. But Type 1 doesn’t test if controls actually worked over time. It proves planning, not execution.
SOC 2 Type 2 tests if controls worked properly throughout an examination period (usually six to twelve months). Auditors collect evidence across this whole period, testing controls repeatedly to verify consistent operation. Type 2 gives much stronger proof because it shows sustained performance, not just excellent design.
For cyber security proof, customers heavily prefer Type 2 reports. Customers seek evidence of consistent control work, not merely confirmation of well-planned procedures.
HOW SOC AUDITS WORK
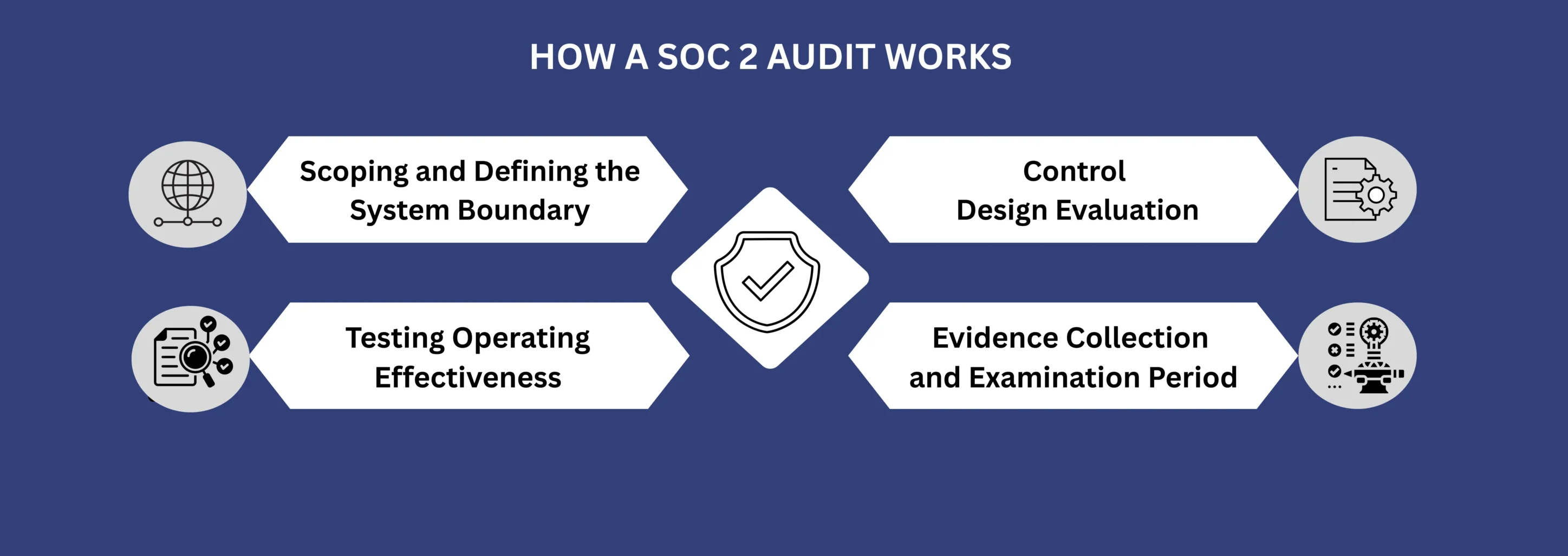
Scoping and Defining the System Boundary
First, you define exactly what the SOC audit will examine. This means identifying which services, systems, infrastructure, and processes fall within scope. Clear boundaries stop confusion about what the audit actually covers.
Scoping choices hugely impact how useful the audit is for customers. If key systems fall outside scope, the audit won’t give assurance for those areas. Think carefully about customer expectations when setting boundaries.
Control Design Evaluation
Auditors check if controls are designed properly to meet Trust Services Criteria. This means reviewing control descriptions, checking policies and procedures, and judging if controls logically tackle stated goals.
Good controls have clear goals, defined steps, assigned owners, and proper timing. If controls lack these pieces, auditors might spot design problems before even testing how well they work.
Testing Operating Effectiveness
After confirming good design, auditors test if controls actually ran as described throughout the examination period. Testing involves reviewing evidence, watching processes, interviewing staff, and checking samples.
If a control needs quarterly access reviews, auditors verify all four reviews happened during the examination period, were done properly, and led to the right actions when problems showed up.
Evidence Collection and Examination Period
You must collect and keep evidence showing controls ran throughout the examination period. Evidence might include logs, tickets, reports, approvals, training records, or scan results. Without enough evidence, auditors can’t verify controls worked.
Examination periods typically run six to twelve months for Type 2 audits. Service organizations must collect evidence steadily during this period instead of hunting for papers when auditors show up.
CAN YOU FAIL A SOC AUDIT?
What “Failure” Means in a SOC Audit Context
SOC audits don’t give simple pass/fail grades. Auditors issue opinions about whether controls were suitably designed and operated effectively in accordance with the Trust Services Criteria. Opinions can be unqualified (clean), qualified (with concerns), or adverse (controls didn’t meet standards).
Even clean opinions might include exceptions for specific controls. “Passing” isn’t yes/no. It’s about whether the overall control setup proved effective despite individual issues.
Control Exceptions vs Audit Opinions
Single control exceptions don’t automatically create qualified or adverse opinions. Auditors weigh exception severity, frequency, and management response when forming overall opinions. Minor exceptions with strong fixes might not hurt the opinion much.
But many exceptions, bad control failures, or weak management responses can push auditors to qualify their opinion or say controls didn’t meet standards.
How Organizations Address Identified Gaps
When auditors identify control gaps or exceptions, it is important to address them promptly. This might mean better procedures, more monitoring, or extra training.
Document these fixes and show evidence to auditors. Strong responses to exceptions prove maturity and commitment to getting better, which partly offsets the negative hit from exceptions themselves.
SOC 2 AUDIT AT A GLANCE
- Performed by Licensed CPA firm.
- Follows the AICPA SSAE standards.
- Focuses on security and Trust Services Criteria.
- SOC 2 Type 1 checks the design of controls at a point.
- SOC 2 Type 2 checks the Operating effectiveness over a certain period of time.
- Purpose is to demonstrate Independent assurance for customers and stakeholders.
CONCLUSION
SOC audits evaluate whether an organization maintains the operational discipline required for sustained cybersecurity performance. They assess not only the existence of controls but also whether they operated effectively over a defined examination period under normal business conditions.
Organizations that consistently achieve clean SOC reports demonstrate that security is embedded within their operating model rather than treated as a temporary initiative. This level of documented control execution gives more confidence than just policies or one-time technical implementations.
As cyber threats evolve and third-party risk scrutiny increases, independent assurance becomes essential. SOC examinations performed by licensed CPA firms transform security representations into evidence-based attestations that stakeholders can rely on.
FAQ
What does SOC stand for in cyber security?
SOC stands for Service Organization Control. It refers to independent audit reports that evaluate whether an organization has properly designed and implemented effective internal controls.
How long does a SOC audit take?
For a SOC 2 Type 2, the reporting period typically spans 6 to 12 months. In addition, audit activities such as scoping, evidence collection, control testing, and report issuance typically require 3 to 6 months, depending on system complexity and readiness.
What is the difference between SOC 1 and SOC 2?
SOC 1 evaluates controls relevant to customer financial reporting. It is based on ICFR principles. Meanwhile, SOC 2 evaluates controls against the Trust Services Criteria and focuses on operational and data protection controls rather than financial reporting.
Can a company fail a SOC audit?
SOC examinations do not use pass or fail language. Instead, auditors issue opinions such as an unqualified opinion, a qualified opinion, an adverse opinion, or a disclaimer of opinion. These opinions depend on control design, operating effectiveness, and evidence quality.
How often should organizations get SOC audits?
Most organizations undergo SOC examinations annually. Enterprise customers generally expect a report that covers a recent 12-month period. After one year, procurement teams usually request an updated report for ongoing vendor risk assessment.
Multi-Framework Compliance Guide: Best Practices and Strategies
SOC 2 FRAMEWORK REQUIREMENTS IN 2026. WHAT HAS CHANGED?
HOW SOC 2 COMPLIANCE SOFTWARE CHANGES AUDIT READINESS
There's a version of SOC 2 preparation that most security teams know too well. The audit date is approaching. Someone sends a spreadsheet asking for access logs, vendor assessments, and approval records. People scramble. Documentation gaps appear. What should take...






