ISO 27001 is like a digital fortress that safeguards your information. It’s the gold standard for managing and protecting sensitive data. With ISO 27001, you can build a robust system to identify, assess, and mitigate risks to your information assets. It’s like a superhero cape for your organization, ensuring your data is secure from cyber threats, unauthorized access, and breaches. ISO 27001 provides a roadmap to establish strong controls, policies, and procedures to keep your information safe. So, if you want to fortify your digital kingdom and gain the trust of your customers, ISO 27001 is the ultimate armor you need.
This article presents an in-depth exploration of the ISO 27001 checklist, providing a valuable resource for organizations seeking to strengthen their information security framework. It covers the key domains and controls, including scope and objectives, leadership commitment, risk assessment and management, asset management, access control, incident management, and much more.
ISO 27001:2022: THE ENHANCED STANDARD FOR INFORMATION SECURITY
SO standards typically undergo regular reviews and revisions to ensure they remain current and aligned with the evolving needs of organizations and the technology landscape. The British Standards Institution (BSI) published British Standard (BS) 7799:1992 as a guideline for information security management.
In 2005, in place of ISO/IEC 17799:2000 and BS 7799-2:2002, the ISO/IEC 27001:2005 standard was issued. It established a more formal framework for ISMS, with an emphasis on risk management and ongoing development. It was then updated in 2013, incorporating feedback and lessons learned from organizations worldwide. This version emphasized a process-based approach to information security management and provided a clearer alignment with other ISO 27001 standards.
After 13 long years, ISO 27001:2022 got into the frame. With the long-awaited publication of the ISO 27001:2022 standard came a number of adjustments. 35 controls have not changed, but 57 have been combined, 23 have had their names modified, and 11 have been added. This results in a decrease in controls overall, from 114 to 93, distributed over 4 categories. The ISO 27001 implementation checklist is mandatory for someone.
A COMPLETE ISO 27001:2022 CHECKLIST FOR ENHANCED PROTECTION
An organization can strengthen its information security posture by putting ISO 27001 into practice. Nevertheless, if you lack the right support, navigating the intricate world of ISO 27001 regulations may be difficult. The ISO 27001 certification checklist is essential in this situation.
The ISO 27001 certification checklist is a useful tool for streamlining the implementation procedure and ensuring adherence to the strict criteria of the standard. It includes a complete collection of rules and regulations that businesses may use to create an effective ISMS that is suited to their particular requirements.
Let’s check the ISO 27001 requirements checklist. This checklist provides a high-level overview of the important criteria and controls commonly included in an ISO 27001 implementation. Let’s dive into it:
Scope and objectives:
- Determine the goals and objectives for your ISMS (Information Security Management System).
- Establish a framework for managing information security and specify your goals.
Leadership and dedication:
- Obtain managerial commitment and assistance for implementing and maintaining the ISMS.
- Assign roles, duties, and powers to ensure information security.
Risk evaluation and management:
- Identify and evaluate the dangers to information security.
- Create a risk management strategy to handle the identified hazards.
- Establish criteria and practices for risk acceptance.
Organizational context:
- Determine any internal or external problems that could affect the privacy and security of information.
- Find out who is interested and what they need in terms of information security.
- Create a procedure for keeping an eye on and reviewing the internal and external context.
Information security policy:
- Create an information security policy that is in line with the goals of the company.
- Share the policy with all necessary parties.
- Be careful to constantly check the policy and make any required updates.
Information security management:
- Create a management structure to carry out your information security policy.
- Establish reporting structures, roles, and duties for information security management.
- Conduct ongoing training and awareness campaigns for the workforce.
Human resource security:
- Establish the security roles and responsibilities for personnel in human resources.
- Implement a structured hiring and firing procedure for employees.
- Background checks and security awareness instruction.
Asset administration:
- Recognize and catalog information assets.
- Define who owns something and how it is classified.
- Put safeguards in place to protect information assets during the course of their existence.
Access control:
- Logical and physical access restrictions should be put in place to secure information.
- Based on organizational needs and roles, assign user access privileges.
- Review and keep an eye on user access rights on a regular basis.
Cryptography:
- Establish guidelines and protocols for employing cryptography to safeguard data.
- Use encryption techniques to safeguard sensitive data.
Physical and environmental security:
- Implement physical security measures to safeguard facilities, machinery, and assets. Environmental security.
- Protect against environmental risks and restrict access to sensitive regions.
Operations security:
- Establish protocols for the secure usage and operation of information processing facilities.
- To manage changes to information systems, establish change management procedures.
- Put in place safeguards for virus defense, data backup, and logging.
Communications security:
- Information should be protected during transmission through networks as part of communications security.
- Use secure network protocols and architectures.
- Configure network hardware securely and take precautions against network threats.
Supplier relationships:
- Evaluate and control the risks connected to these connections.
- Establish supplier security criteria and include them in contracts.
- Keep an eye on and evaluate the vendors’ information security performance.
Incident management:
- Establish a procedure for managing and responding to incidents.
- Establish roles, responsibilities, and processes for incident reporting and response.
- Test and evaluate incident response strategies’ efficiency on a regular basis.
Management of business continuity:
- Develop and implement a business continuity plan.
- Check and assess the plan’s efficacy on a regular basis.
- Create procedures to deal with interruptions and restore crucial company operations.
Compliance:
- Determine the relevant laws, rules, and contractual obligations.
- Create procedures to guarantee adherence to legal and regulatory standards.
- Review and keep an eye on compliance often.
Internal audit:
- Consistently perform ISMS internal audits.
- Review and evaluate the performance of the controls and procedures.
- Report conclusions and suggest enhancements.
Management review:
- Conduct recurring ISMS management reviews.
- Analyze the ISMS’s suitability and efficacy.
- Establish goals for the upcoming term and identify areas that need development.
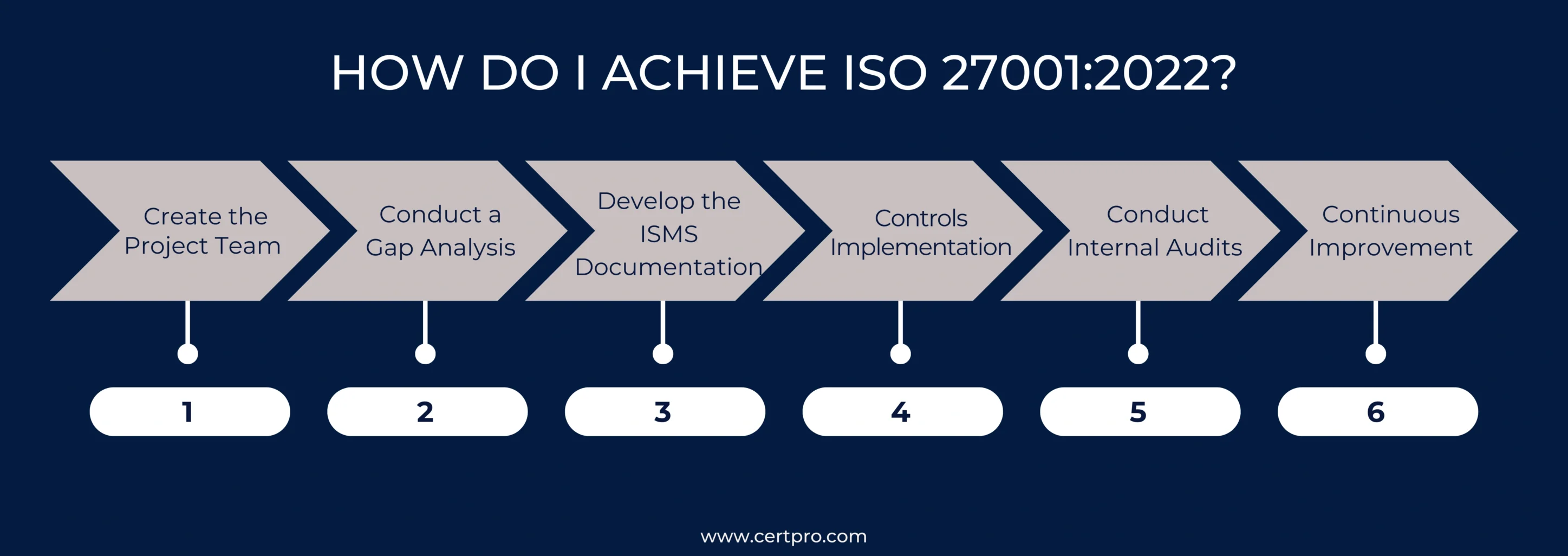
HOW DO I ACHIEVE ISO 27001:2022?
Achieving ISO 27001:2022 is not at all an easy process, but by following a few important steps, we can be ISO 27001:2022 compliant.
1. Create the Project Team: After opting for top management to implement and maintain ISO 27001:2022, Assemble a focused team or choose trustworthy people to take charge of the implementation project. This team will be in charge of planning and carrying out all essential tasks during the certification process.
2. Conduct a Gap Analysis: Carefully evaluate how your firm now handles information security in comparison to ISO 27001. This gap analysis will show you where your company needs to strengthen its compliance and improve.
3. Develop the ISMS Documentation: Create and record the relevant guidelines, protocols, and controls needed by ISO 27001. This comprises a Statement of Applicability, an Information Security Policy, a Risk Assessment and Treatment Methodology, and other pertinent papers.
4. Controls Implementation: Carry out the controls recommended in your ISMS manual. Applying technological, physical, and organizational safeguards is necessary to safeguard information assets and reduce risks found during the risk assessment procedure.
5. Conduct Internal Audits: Audit your ISMS internally to see how well it functions and if it complies with ISO 27001 standards. Before the certification audit, these audits can help find any non-conformities or areas that require improvement.
6. Continuous Improvement: Achieving ISO 27001 is a lifelong endeavor. You must regularly evaluate and enhance your ISMS if you want to keep your certification. Conduct routine management reviews and internal audits, and address any areas that may be improved.
It takes dedication to information security and continued development to get ISO 27001 accreditation, which is a continuous process. Engaging with experienced consultants or ISO 27001 specialists might offer helpful direction during the certification process.
CERTPRO: EMPOWERING CERTIFICATION EXCELLENCE
Businesses can leverage CertPro’s expertise and tap into their comprehensive understanding of ISO 27001 regulations through collaborative efforts. With CertPro’s proven methodology and adherence to best practices, organizations can confidently pursue ISO 27001 certification.
We at CertPro act as a reliable ally in the constantly changing world of information security, enabling businesses to improve their information security posture and achieve a competitive advantage. Organizations may improve their data protection methods, show that they are committed to protecting sensitive information, and gain confidence by working with CertPro.
FAQ
Can we obtain ISO 27001 certification without outside help?
While obtaining ISO 27001 certification without outside help is feasible. Working with a trustworthy certification company can assist firms in avoiding frequent errors, streamlining implementation, and increasing the likelihood of successful certification thanks to their knowledge and experience in ISO 27001 implementation and certification.
Is ISO 27001 certification a one-time achievement?
No, maintaining a commitment to information security is necessary for ISO 27001 accreditation. Organizations continuously review and enhance Information Security Management Systems (ISMS) post certification to maintain compliance. To guarantee that ISMS remains successful and is in line with shifting risks and management reviews, focused actions are crucial.
What is a checklist for ISO 27001?
The international de facto standard for protecting the security of data and the assets that enable it is called ISO 27001. A firm may demonstrate its security procedures to potential clients anywhere on the globe by obtaining ISO 27001 certification.
What modifications were made to ISO 27001 between 2013 and 2022?
ISO 27001:2022 hasn’t changed much, although it has the same number of clauses as ISO 27001:2013. The modifications support ISO 27001’s alignment with other ISO management standards. Planning, creating process requirements, and monitoring standards are the main topics of significant change.
What distinguishes ISO 27002 from ISO 270001?
The standards for creating, putting into practice, upholding, and continuously enhancing an Information Security Management System (ISMS) are laid forth in ISO 27001. A code of practice called ISO 27002 (known as ISO 17799) offers recommendations and best practices for implementing certain security measures within the framework of ISO 27001.

About the Author
ANUPAM SAHA
Anupam Saha, an accomplished Audit Team Leader, possesses expertise in implementing and managing standards across diverse domains. Serving as an ISO 27001 Lead Auditor, Anupam spearheads the establishment and optimization of robust information security frameworks.
IS SOC 2 THE SAME AS ISO 27001?
In today's digital landscape, ensuring the safeguarding of client data is paramount for businesses. Adhering to recognized compliance standards is vital to meeting this demand. ISO 27001 vs. SOC 2 represent two prominent benchmarks in the realm of data security with...
WHO NEEDS ISO 27001 CERTIFICATION AND WHY?
The esteemed ISO 27001 security framework is designed to evaluate the effectiveness of an organization's Information Security Management System (ISMS) in safeguarding its data. Obtaining ISO 27001 certification is a practical way for a corporation to demonstrate its...
IS ISO 27001 RISK ASSESSMENT VITAL FOR SECURITY MEASURES?
The ISO 27001 standard provides a framework for information security, highlighting the importance of a thorough risk assessment procedure. Organizations use the methodical and complex ISO 27001 risk assessment process to identify and assess information security...





