AUSTRALIA
SOC 2 CERTIFICATION IN AUSTRALIA
SOC 2 reporting provides independent assurance over an organization’s systems related to security, availability, processing integrity, confidentiality, and privacy. While SOC 2 is voluntary, many Australian organizations obtain SOC 2 reports to support customer reviews, vendor assessments, and contractual requirements.
SOC 2 examinations are performed against the Trust Services Criteria developed by the AICPA and focus on how systems and controls are described, designed, and operated during a defined period.
AUSTRALIA CLIENTS










SOC 2 EXAMINATIONS BY CERTPRO IN AUSTRALIA
CertPro performs SOC 2 examinations as a licensed CPA firm. Furthermore, our engagements are conducted in accordance with AICPA attestation standards and subject to peer review requirements.
During audits, our auditors evaluate management’s system description and test controls based on audit evidence. Thereby resulting in a SOC 2 Type 1 or Type 2 report issued for use by customers, partners, and stakeholders.
WHY ORGANIZATIONS ENGAGE CERTPRO FOR SOC 2 AUDITS
Organizations engage CertPro for SOC 2 examinations due to OUR role as a licensed CPA firm registered under the AICPA peer review program.
CertPro performs SOC 2 engagements with a defined scope, consistent audit procedures, robust control testing measures, and objective reporting. All examinations are conducted independently, with management retaining responsibility for system design and control operation.
SOC 2 ENGAGEMENT FEES IN AUSTRALIA
SOC 2 engagement fees in Australia vary based on the report type (Type I or Type II), system complexity, scope, and examination period. Fees are determined by the audit effort required and the engagement scope agreed upon at the start.
As an independent CPA firm, CertPro sets fees before the examination begins. The scope and testing approach are defined upfront and remain unchanged throughout the engagement. This preserves audit objectivity and report reliability.
WHAT IS SOC 2?
SOC 2 is a set of rules to help protect data and keep it safe. It is an attestation framework developed by the AICPA to report on controls relevant to security, availability, processing integrity, confidentiality, and privacy.
There are two types of SOC 2 reports:
Type 1 SOC 2 Report: This report checks if your security controls are in place at a specific time.
Type 2 SOC 2 Report: This report looks at how well the security controls are working over time and whether your organization is following the rules.
Therefore, SOC 2 compliance in Australia shows that your company has strong security measures in place to protect data. These measures include both technical and physical protections to keep the data safe. If you want to improve your company’s data security, it’s important to understand how SOC 2 works.
WHY SOC 2 REPORTS ARE REQUESTED IN AUSTRALIA
SOC 2 reports are frequently requested during vendor due diligence, procurement reviews, and third-party risk assessments. Organizations use these reports to assess how service providers design and operate controls over systems and data.
Although SOC 2 is not a statutory requirement, it is widely relied upon across technology, SaaS, healthcare, and financial services sectors as a standard assurance mechanism for transparency and trust.
ENQUIRE NOW
Related Links
SOC 2 in Australia
ISO 27701 in Australia
GDPR in Australia
ISO 27018 in Australia
HIPAA in Australia
CCPA in Australia
PIPEDA in Australia
ISO 17025 in Australia
ISO 13485 in Australia
CE Mark in Australia
GDP in Australia
GLP in Australia
ISO 9001 in Australia
ISO 14001 in Australia
ISO 45001 in Australia
ISO 22000 in Australia
HACCP in Australia
ISO 22301 in Australia
ISO 21001 in Australia
ISO 41001 in Australia
ISO 20000-1 in Australia

HOW TO GET SOC 2 CERTIFICATION IN AUSTRALIA?
SOC 2 certification in Australia follows a structured audit process. It begins by selecting the relevant Trust Services Criteria. Most organizations start with Security. This step defines what systems and controls the audit will review. A SOC 2 checklist can help confirm the audit scope early.
Next, the organization documents controls and processes that support the selected criteria. These controls must address how systems protect data during daily operations. Management remains responsible for control design and implementation.
An independent CPA firm then performs the SOC 2 audit. The auditor reviews control design and tests how controls operate. Testing may take place remotely or on-site, depending on the engagement scope.
After audit completion, the CPA firm issues the SOC 2 report. Organizations then share the report with customers and stakeholders as part of vendor reviews.
SOC 2 certification requires ongoing oversight. Controls must continue to operate consistently. Most organizations complete the audit each year to keep reports current and usable.
STEPS FOR OBTAINING SOC 2 CERTIFICATION IN AUSTRALIA
SOC 2 certification in Australia follows a defined audit process that verifies an organization’s data protection measures. A SOC 2 engagement generally includes the following stages:
Step 1: Identify Trust Service Criteria: The engagement begins with identifying the applicable Trust Service Criteria. These criteria define which system components, data flows, and controls fall within the audit scope.
Step 2: Identify Relevant Controls: After scope definition, existing administrative and technical controls are identified for review. These controls typically include documented policies, access controls, system configurations, and network safeguards.
Step 3: Evaluate Control Design and Operation: The auditor evaluates whether the identified controls are designed appropriately and operate as documented. Testing results are assessed against the applicable Trust Service Criteria.
Step 4: Perform an Independent CPA Examination: An independent CPA firm performs the examination in accordance with AICPA standards. The auditor reviews documentation, observes processes, and collects audit evidence.
Step 5: Audit Fieldwork and Evidence Review: During fieldwork, management provides evidence and responds to audit inquiries. The auditor reviews control activity, system logs, and supporting records over the defined testing period.
Step 6: Issue of SOC 2 Report: After completing control testing, the auditor issues a SOC 2 report. The report documents any identified control gaps or exceptions with detailed supporting documentation.
Step 7: Ongoing Assessment in Future Periods: Management remains responsible for remediation of any identified control gaps. Subsequent SOC 2 examinations assess whether controls continue to operate consistently over time.
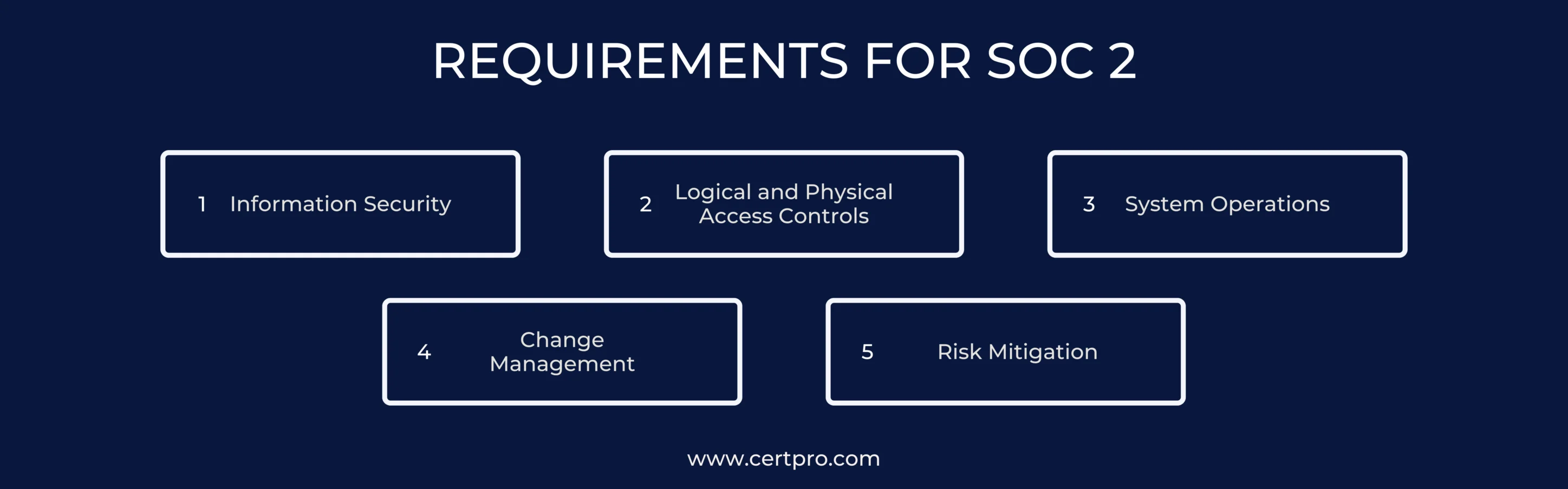
REQUIREMENTS FOR SOC 2 CERTIFICATION
During a SOC 2 examination, the auditor assesses whether the following requirement areas are in line with the applicable Trust Service Criteria.
Information Security: The organization must maintain controls designed to protect information from unauthorized access, disclosure, or misuse. These controls are evaluated for both design and operation during the examination period.
Logical and Physical Access Controls: SOC 2 examinations assess how access to systems, applications, and facilities is restricted and monitored. This includes user access management, authentication mechanisms, and physical safeguards protecting infrastructure.
System Operations: The organization’s system operations are reviewed to determine whether systems are monitored for availability, performance, and security events. This includes incident detection, response activities, and the presence of backup and recovery mechanisms.
Change Management: SOC 2 requires documented processes for managing system changes. Auditors evaluate whether changes to applications, infrastructure, and configurations are authorized, tested, and recorded in accordance with established procedures.
Risk Management Controls: The examination reviews how risks related to data security and system reliability are identified and addressed through control activities. This includes ongoing monitoring and documentation supporting risk-related decisions.
SOC 2 CERTIFICATION COST IN AUSTRALIA
The cost of SOC 2 certification in Australia varies based on the scope and complexity of the organization being examined. Factors such as system size, number of in-scope services, and length of the examination period directly influence engagement fees.
SOC 2 Type 1 reports generally involve lower costs, as they assess the design of controls at a specific point in time. In contrast, SOC 2 Type 2 reports require testing control operation over an extended period, which increases examination effort and overall cost.
Engagement fees also reflect the extent of audit procedures required to obtain sufficient evidence. Organizations with multiple systems, locations, or integrated third-party services typically require broader testing.
SOC 2 certification involves recurring examinations, particularly for Type 2 reports. As a result, costs are not one-time and may recur annually to maintain report relevance for customers, regulators, and stakeholders.
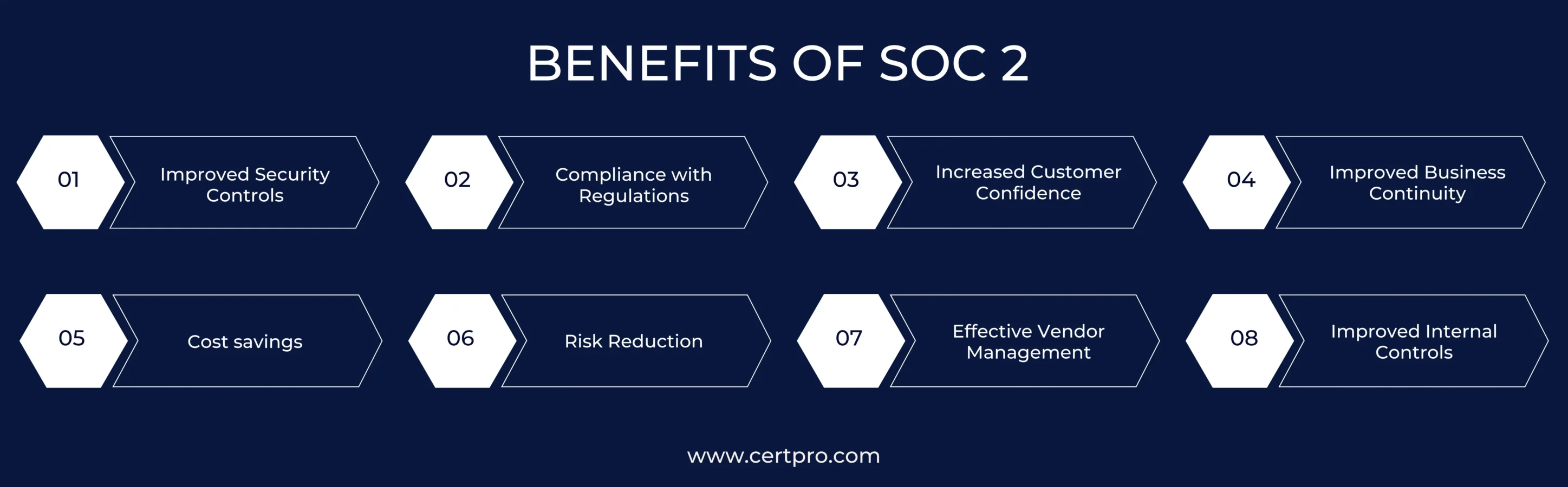
BENEFITS OF SOC 2 CERTIFICATION
SOC 2 certification in Australia provides documented assurance over how an organization designs and operates controls related to data security and system reliability. The benefits stem from independent examination results rather than advisory activity.
Documented Control Assurance: SOC 2 report confirms that security and operational controls are designed and, where applicable, operating as described. This reduces uncertainty for customers, partners, and regulators who rely on the report.
Regulatory and Contractual Alignment: SOC 2 reports support due diligence requirements across industries that handle sensitive data. Many organizations use SOC 2 as a baseline expectation during procurement, vendor reviews, and compliance assessments.
Stakeholder Confidence: SOC 2 report issued by a licensed CPA firm provides third parties with objective evidence of control effectiveness. This supports trust during enterprise sales, audits, and contractual reviews.
Operational Continuity Evidence: SOC 2 examinations include controls related to system availability and incident response. This demonstrates that processes exist to support service continuity and system stability during critical moments.
Risk Visibility: The examination process identifies control gaps and exceptions within the reporting period. Management can use these findings to understand areas of operational risk.
Third-Party Oversight: SOC 2 reports help organizations show how vendor-related risks are managed within defined system boundaries, where control responsibilities are shared between the service provider and its customers.
Stronger Internal Accountability: SOC 2 examinations reinforce consistent control operation and documentation. This exhibits clearer ownership of processes and reduces control breakdowns over time.
SOC 2 CERTIFICATION IN AUSTRALIA BY CERTPRO
SOC 2 certification in Australia provides independent assurance over an organization’s internal control design and, where applicable, control operating effectiveness. CertPro conducts SOC 2 examinations as a licensed CPA firm in accordance with AICPA standards.
Our role is limited to performing control testing, evaluating audit evidence within the defined system scope, and issuing SOC 2 Type I or Type II reports based on examination results.
SOC 2 reports issued by CertPro support third-party reliance during vendor due diligence, procurement reviews, regulatory assessments, and contractual evaluations. All engagements follow applicable professional auditing standards, documentation requirements, and AICPA quality control expectations.
FAQ
Is SOC 2 applicable in Australia?
Yes, SOC 2 is widely used in Australia to enhance data security and build trust with clients, especially in sectors requiring strong privacy controls.
What are the steps to obtain SOC 2 certification?
SOC 2 certification involves selecting trust principles, setting up data controls, conducting internal assessments, and having an external audit.
How much does SOC 2 Type 2 certification cost?
SOC 2 Type 2 costs vary depending on an organization’s size and complexity, with Type 2 typically more expensive due to detailed audits.
Who needs SOC 2 compliance?
SOC 2 compliance is required by organizations handling sensitive data, particularly in sectors like finance, healthcare, and SaaS.
How long is SOC 2 compliance valid?
SOC 2 compliance is generally valid for 12 months, after which organizations need to undergo periodic audits for continued compliance.
HOW SOC 2 COMPLIANCE SOFTWARE CHANGES AUDIT READINESS
There's a version of SOC 2 preparation that most security teams know too well. The audit date is approaching. Someone sends a spreadsheet asking for access logs, vendor assessments, and approval records. People scramble. Documentation gaps appear. What should take...
HOW SOC 2 TYPE II CERTIFICATION IMPACTS CUSTOMER CONFIDENCE AND DATA SECURITY
Enterprise buyers changed how they evaluate vendors. They no longer trust self-reported security claims. Instead, vendor risk management became a top priority. Consequently, procurement teams demand independent proof. They need verification that vendors protect their...
SOC 1 VS SOC 2: WHICH REPORT YOUR CUSTOMERS ACTUALLY ASK FOR
If you sell SaaS or provide outsourced services, you have likely been asked for a SOC report. However, the follow-up question is rarely easy to answer: do they mean SOC 1 or SOC 2? Both reports fall under the AICPA’s System and Organization Controls (SOC) reporting...