CMMC 2.0 LEVELS EXPLAINED: CHOOSING THE RIGHT PATH FOR YOUR BUSINESS
The CMMC 2.0 is now a cybersecurity mandate that the Defense contractors can’t overlook. According to Defensescoop, the latest rule amending the Defense Federal Acquisition Regulation Supplement (DFARS), the updated CCMC 2.0 rules, officially takes effect on Nov 10, 2025.
Therefore, if you’re doing business with the U.S. Department of Defense (DoD), your inbox has been filled with vendor updates or prime contractors asking where you stand on CMMC 2.0 compliance. If your business handles defense data, you’ll need to demonstrate your cybersecurity maturity soon.
So what is CMMC 2.0 all about? In simple terms, it’s the DoD’s way of making sure every company that touches its sensitive information is implementing the right security measures to safeguard it. Consider the CMMC 2.0 framework as a layered security filter. Each level represents a different degree of defense, depending on the sensitivity of the data you handle.
This blog will break down the three CMMC 2.0 levels, explain which one applies to your business, and show you how to align your cybersecurity controls to match. Additionally, we will clarify what each level means, how assessments work, what they cost, and why choosing the right one early can save your business.
By the end, you’ll know exactly where your organization stands, how to plan your budget, and how to avoid the most common compliance mistakes that cost businesses time and contracts.
Tl; DR:
Concern: Starting November 10, 2025, all Defense contractors must meet the CMMC 2.0 compliance requirements under the updated DFARS rule. Many businesses are still unsure which level applies to them or how to prepare, risking contract eligibility and revenue loss.
Overview: CMMC 2.0 (Cybersecurity Maturity Model Certification) is the U.S. Department of Defense’s cybersecurity framework designed to protect sensitive data across its supply chain. It simplifies the previous five – level model into three levels based on the type of information handled. Each level has clear requirements, from basic self – assessments to government – led audits, ensuring that every contractor maintains proper cybersecurity maturity.
Solution: Firms should identify their data type (FCI or CUI), determine their required CMMC level, and start preparing early. Partnering with a compliance expert like CertPro helps streamline assessments, close security gaps, and achieve certification faster. This not only ensures DoD contract eligibility but also strengthens overall cybersecurity and business credibility.
WHAT IS CMMC 2.0? A BASIC OVERVIEW
CMMC 2.0 is also known as the Cybersecurity Maturity Model Certification. It is the U.S. Department of Defense’s updated framework to protect sensitive information across its supply chain. In plain terms, it’s the government’s way of making sure contractors and suppliers handling defense data have the right level of cybersecurity in place.
The earlier version, CMMC 1.0, had five levels that many businesses found confusing and expensive. With the latest update, the DoD simplified it to three levels under CMMC 2.0. Furthermore, this change was meant to make compliance more practical and cost – effective. This upgrade particularly focuses on smaller defense suppliers who were struggling to meet the previous version’s demands.
Now, let’s understand how it works. Each level is tied to the sensitivity of the data you handle. For instance, consider that your company deals only with Federal Contract Information (FCI). FCI consists of data that is not meant for public release and is not considered highly sensitive. Therefore, you will likely need Level 1, which focuses on basic cyber hygiene. Conversely, if you handle Controlled Unclassified Information (CUI), which is data that needs stronger protection, then you’ll fall under Level 2 or Level 3. Furthermore, it also depends on the role and the nature of your contracts.
Moreover, CMMC 2.0 also adjusts how assessments are done. Some businesses can now perform self – assessments every year, while those handling more critical data must undergo third – party or government – led audits every three years.
Specifically, the framework is based on well-known standards like NIST SP 800 – 171 and NIST SP 800 – 172, which define the actual security controls you need to meet.
Thus, CMMC 2.0 gives the defense industry a simpler, more flexible way to prove it can protect national security data.
THE THREE CMMC 2.0 LEVELS EXPLAINED
Level 1 (Foundational)
Who it applies to:
Businesses handling only Federal Contract Information (FCI).
Purpose:
Establishes basic cybersecurity hygiene and protects everyday contract information from unauthorized access.
Key requirements:
This level requires about 15 essential security practices, including:
- Using strong and unique passwords.
- In addition, controlling access to systems.
- Furthermore, keeping software and devices updated.
- Limiting data sharing to authorized users.
Assessment method:
Annual self – assessment is necessary. Plus, executive affirmation required to confirm compliance.
Pain point:
Many small businesses overlook these simple steps and risk being disqualified from future contracts.
Level 2 (Advanced)
Who it applies to:
Organizations handling Controlled Unclassified Information (CUI).
Purpose:
Strengthens cybersecurity posture for data that, if leaked, could harm national security or defense operations.
Key requirements:
Implements 110 security controls from NIST SP 800 – 171 Rev 2. To elaborate, the focus areas include:
- Access control and identity management.
- Additionally, it requires data encryption and monitoring practices.
- Likewise, it demands improved incident detection and response.
Assessment method:
Self – assessment for non-critical CUI contracts (annual). Whereas, third – party assessment every three years for “prioritized acquisitions.”
Pain point:
Mid – sized contractors often struggle with documentation and cost but find this level necessary for long-term DoD eligibility.
Level 3 (Expert)
Who it applies to:
Companies managing high – sensitivity CUI or facing advanced persistent threat (APT) risks.
Purpose:
Ensures the highest degree of protection for critical defense data.
Key requirements:
Builds on Level 2. It adds advanced controls from NIST SP 800 – 172, including:
- Continuous monitoring.
- Advanced threat detection and containment.
- Enhanced system and network defense.
Assessment method:
Government – led or top – tier third-party audits every three years.
Pain point:
High investment and effort required, but necessary for organizations directly supporting top defense programs.
HOW TO CHOOSE THE RIGHT CMMC 2.0 LEVEL FOR YOUR BUSINESS
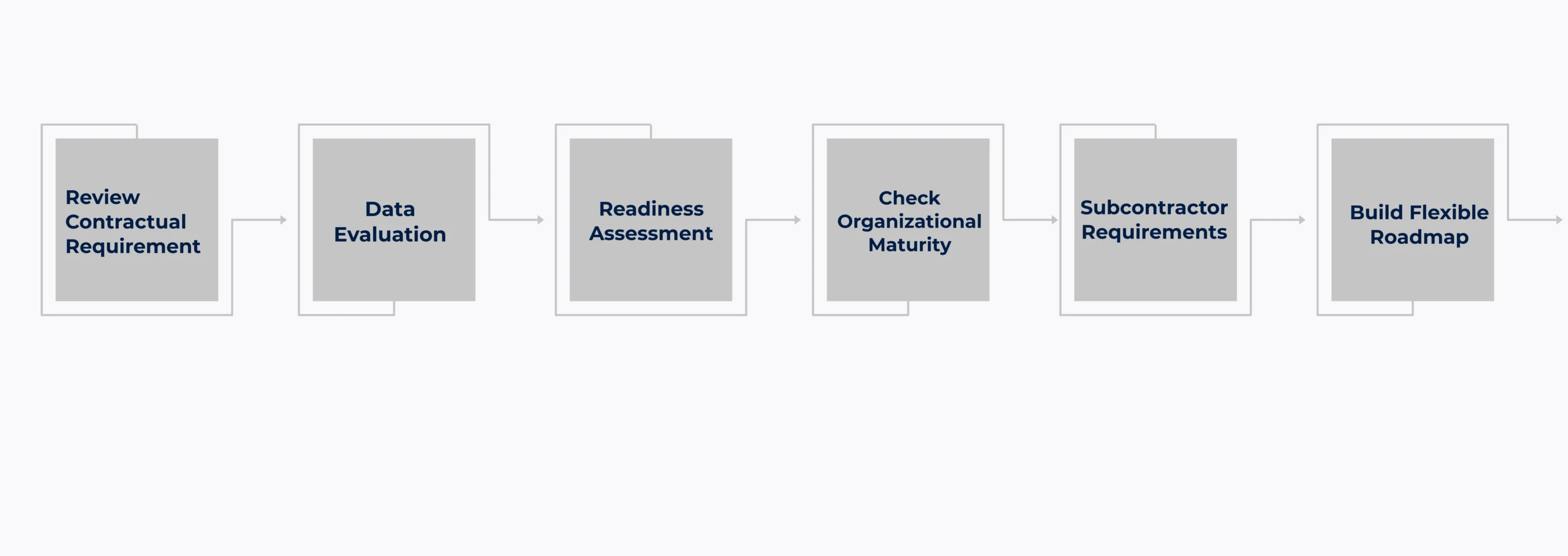
Choosing the right CMMC 2.0 level is about understanding your contracts, your data, and your current cybersecurity posture. This will ensure your compliance without wasting time or resources on unnecessary requirements. The following steps will guide your firm in choosing the right CMMC 2.0 level.
Review Contractual Requirement: Every DoD solicitation or flow-down clause will specify which CMMC level applies. That’s your baseline. Furthermore, don’t just follow your client’s needs; rather, focus on clearly identifying your scope.
Data Evaluation: If it’s only Federal Contract Information (FCI), Level 1 will usually cover you. On the other hand, if you handle Controlled Unclassified Information (CUI), then you need Level 2. Likewise, if that CUI supports critical defense programs, Level 3 must be on your horizon.
Readiness Assessment: Higher CMMC 2.0 levels demand detailed documentation, technical safeguards, and third-party assessments. Most companies take 6 to 18 months to prepare for Level 2, depending on their existing security posture.
Check Organizational Maturity: If your policies already align with NIST SP 800-171, Level 2 is realistic. If not, then begin with Level 1, stabilize your practices, and plan for growth.
Subcontractor Requirements: Don’t overlook subcontractor flow-downs. Because, even if you handle only FCI, your prime contractor might require you to meet their higher level.
Build Flexible Roadmap: Compliance is a dynamic and evolving process. To clarify, your business might only need Level 1 today, but if your business expands into new defense projects, moving to Level 2 could be your next step. So, the smartest approach is to plan ahead for compliance, credibility, and growth.
BENEFITS OF CMMC 2.0 COMPLIANCE
CMMC 2.0 is the key to doing business with the Department of Defense. Therefore, if your contracts rely on federal work, this certification will determine whether you remain competitive or face exclusion. Let’s learn about the potential benefits of CMMC 2.0 compliance in this section.
Winning DoD Contracts: Without CMMC 2.0 compliance, bids won’t even reach review. Obtaining certification ensures that your proposal remains unaffected by compliance gaps. Furthermore, it signals to contracting officers that you’re ready to protect sensitive information.
Improved Efficiency: When prime contractors shortlist vendors, they don’t take changes on firms that are still “working on compliance.” Thus, certification removes that hesitation by eliminating longer bid cycles and chances of disqualification. The CMMC 2.0 cybersecurity framework also helps your business achieve speed and trust.
Cyber Resilience: Implementing the NIST SP 800-171 and 172 controls helps you catch threats earlier, control data access, and strengthen your response to incidents.
Competitive Advantage: You’ll also gain a market advantage beyond defense contracts. Commercial clients perceive CMMC as evidence of your commitment to data security. In this context, the CMMC 2.0 compliance becomes your quiet but powerful selling point in the business market.
Business Clarity: With simplified levels and defined assessment routes, it’s easier to plan costs, training, and timelines.
As the primes push CMMC requirements downstream, being certified now avoids future bottlenecks. Of course this CMMC 2.0 certification process demands some investment upfront. But it pays back through lower cyber insurance premiums, stronger client trust, and better contract margins.
CLOSING THOUGHTS
Getting CMMC 2.0 compliance is not yet another regulatory process. Moreover, it protects sensitive data, keeps you eligible for DoD contracts, and positions your business for growth. All firms aspire to secure their cybersecurity posture. But they lack the guidance on how and where to start. This is where CertPro excels as the leading compliance auditor and CPA firm in the market.
We help companies get ISO 27001 and SOC 2 compliant. This builds a strong cybersecurity foundation that makes CMMC 2.0 much easier and faster to achieve. To clarify, it is like laying a solid groundwork: with these standards in place, your controls, policies, and documentation are already aligned with most of the expectations of DoD audits.
CertPro collaborates closely with startups, SMBs, and established contractors. Thereby, tailoring guidance to your current setup and helping you plan a clear roadmap for CMMC 2.0. From assessments to gap remediation and ongoing support, we make compliance practical, manageable, and actionable.
Take action and connect with CertPro today and discover how we can help your business secure sensitive data, win contracts, and stay ahead in 2025’s competitive defense landscape.
FAQ
What does CMMC stand for?
CMMC stands for Cybersecurity Maturity Model Certification. It is a U.S. Department of Defense (DoD) framework that sets cybersecurity standards for contractors and suppliers handling federal contract information or controlled unclassified information (CUI).
What is the difference between CMMC 2.0 and NIST 800 171?
CMMC 2.0 builds on NIST SP 800-171 by adding certification requirements. While NIST 800-171 outlines security controls, CMMC 2.0 verifies compliance through self-assessments or third-party audits before contractors can qualify for DoD contracts.
What are the five levels of CMMC?
The original CMMC model had five levels, ranging from basic cyber hygiene (Level 1) to advanced security (Level 5). Each level added more security controls and maturity processes for protecting sensitive defense data.
Who needs CMMC 2.0 compliance?
All Department of Defense contractors and subcontractors that handle Federal Contract Information (FCI) or Controlled Unclassified Information (CUI) must meet CMMC 2.0 requirements to bid on or maintain defense-related contracts.
What are the 3 levels of CMMC 2.0?
CMMC 2.0 includes three levels: Level 1 (Foundational), Level 2 (Advanced, based on NIST SP 800-171), and Level 3 (Expert, aligned with NIST SP 800-172). Each level reflects the sensitivity of data handled by contractors.
GRC IN CYBERSECURITY: WHAT IT MEANS AND WHY IT MATTERS IN 2026
In 2026, the pressure on companies to manage cyber risk responsibly has never been greater. Regulators demand structured controls, boards want clear risk reporting, and threat actors are becoming more sophisticated. Against this backdrop, GRC in cybersecurity has...
HOW COMPLIANCE AUDIT SOFTWARE IMPROVES AUDIT READINESS
Today, most companies deal with a growing number of compliance regulations. From data privacy standards to security frameworks like SOC 2 and ISO 27001, the list of compliance obligations keeps expanding. At the same time, regulators and external auditors now expect...
Compliance Best Practices in 2026: How to stay ahead of regulatory changes
Why is the implementation of compliance best practices critical for 2026? Compliance in 2026 demands operational proof, not the documentation intent. Regulations change faster, audit scrutiny is higher, and reporting timelines are tighter across privacy,...