Data Breach Costs and Impact in 2025: Global Insights for Business
A data breach can be defined as an incident where sensitive information is leaked or compromised by unauthorized users. In simple words, it happens when someone gets access to data they should not have. The data include customer records, employee files, payment details, medical records, and internal systems. One question that defines 2025 is that even firms that have passed audits in the past have experienced incidents of cyberattacks.
Therefore, monitoring these data breaches becomes more important now. Breaches are not new in the business scenario. But as business leaders, you must have realized that the impact of a data breach 2025 keeps evolving with time. One breach today could halt your operations, attract regulatory fines across regions, and deteriorate your reputation in the market.
Breaches are happening on a larger and faster scale in 2025. Moreover, AI plays a key role here. Attackers use it to write smarter phishing emails, scan systems at scale, and move quickly once inside.
Such security incidents are a major blow to the compliance teams. Regulations like GDPR, HIPAA, and industry-specific rules change fast after a data breach. To elaborate, the incident reporting deadlines become short, the penalties add up, and audits become more complex in nature. During such instances, risks become a management issue rather than a technical issue.
In this blog, we deliver a report that summarizes what actually happened in 2025. It discusses real breach cases, their impact, and lessons to be learned. It also breaks down the risks behind those incidents and how AI changed the threat picture.
If you are an executive, a CISO, or a compliance lead, this book is for you. We provide you with actionable insights and best practices to prevent such data breaches in the future.
Tl; DR:
Concern: Data breaches in 2025 are no longer rare security events. They are evolving business risks. Breaches now cost millions, take months to detect, and cause legal, audit, and trust issues across regions. Having said that, AI has made these cyberattacks smarter, faster, and harder to spot, while third – party risks continue to grow.
Overview: The global average data breach cost is about $4.44 million, while U.S. breaches average over $10 million. It still takes roughly 241 days to detect and contain an incident. Credential theft, phishing, vendor compromise, and scattered data environments remain the top causes. AI has amplified both attack speed and scale, increasing pressure on compliance and security teams.
Solution: To prevent a data breach in 2025, businesses need strong security controls, zero – trust security protocols, a continuous monitoring culture, and a solid vendor risk management program. Incident response must align with compliance regulations like GDPR, HIPAA, SOC 2, and ISO standards. Working with an experienced audit and compliance partner like CertPro helps reduce risk early, prove trust, and avoid costly last-minute remediation driven by regulators or breaches.
KEY DATA BREACH STATISTICS IN 2025
Let’s begin the report with some hard data, because this information is what business leaders care about the most.
In 2025, the global average cost of a data breach sits around $4.44 million. That’s slightly lower than in past years. But don’t let that number relax you. Costs didn’t drop because breaches became easier to handle. They dropped because many firms now contain incidents faster. Those who contain incidents slowly still pay far more than the average.
In the United States, the average data breach cost is about $10.22 million. U.S. firms face stringent enforcement, higher legal fees, and an increased likelihood of lawsuits.
Time is also another key factor here. In 2025, it takes about 241 days to spot and contain a breach. That’s nearly eight months. For months, attackers might sit inside systems, copying data, testing access, and waiting to surface the next attack. Most companies succeed in defense but fail in detection.
The scale is also growing. Thousands of breaches were reported globally, exposing billions of records that include customer data, employee files, health records, and login details. One trend stands out clearly. Credential theft surged, with stolen usernames and passwords remaining as the top entry point.
Additionally, AI made things harder. A significant share of data breaches involved AI, either used by attackers or missing on the defense side. AI helped in expanding the phishing surface and speeding up attacks. Meanwhile, firms with weak detection and monitoring tools struggled to keep up.
These numbers clarify that breaches aren’t rare events anymore. They’re business risks that demand attention, resources, and accountability at the top.
MAJOR DATA BREACHES OF 2025 AND ITS IMPACT ON INDUSTRY
Below are five incidents from 2025 that shaped leaders’ perspectives on data breaches. Each one highlights a different vulnerability that businesses still struggle with.
Aflac Cyberattack
The Aflac data breach affected about 22.65 million people. The breach exposed social security numbers, health data, and claims information. The event deeply affected many executives. Although the insurance firms operate under heavy regulation, they have vulnerabilities that allowed the attackers to get in.
Qantas Airways Breach
Qantas confirmed that 5 million customers’ records involving contact details and travel data were exposed. Regulators moved fast, and public scrutiny followed even faster. For airlines and travel firms, this incident showed how customer trust can drop overnight and how one data breach can destroy years of brand reputation.
Allianz Life Insurance Breach
Allianz Life lost data for around 1.1 million U.S. customers. The breach came through a third – party cloud provider. Such incidents worry CISOs the most. It proves that a vendor can still harm you even if you secure your systems. Therefore, managing vendor risk is a cardinal rule for risk-free business.
Coupang Data Incident
Coupang disclosed a data breach impacting about 34 million records. The company later announced a large compensation plan that reduced backlash but increased costs. Retail and platform businesses learned a hard truth here. The way you treat affected customers carries equal importance to the speed of your incident response procedures.
Nissan and Red Hat Third-Party Breach
This data breach impacted roughly 21,000 customers through a shared vendor environment. The numbers might look small, but the impact is huge. Even limited exposure creates legal and audit pressure when third parties are involved.
Together, these cases show one thing. In 2025, breaches don’t happen due to one weak point. Instead, they come from chains of small ones.
CAUSES AND PATTERNS IDENTIFIED IN 2025 DATA BREACHES
When we look at the 2025 breach reports, one pattern seems common. That is, most attacks didn’t start with fancy exploits; they began with people. To elaborate, a rushed click, a fake login page, or a message that looked legit might have compromised their security. In this section, let’s understand the patterns and root causes of those data breaches.
Here, phishing and social engineering stayed on top for a reason. Attackers got better at tone, timing, and context. This is to say, the emails referenced real vendors, and messages arrived during payroll week. Even smart teams slip when the pressure is on.
Then there’s the supply chain problem. Businesses often go through an unfair situation here. Because you lock down your systems and pass audits diligently. Then a vendor gets hit, and suddenly your data is exposed. In 2025, third parties both added to and multiplied the businesses’ risk exposure.
Credential theft poured more fuel on this fire. Automation played a big role in such attacks. Once attackers got one valid login, scripts did the rest. They tested access across tools in minutes using automation to expand their attack surface. Consider it like a copied key that opens more doors than expected.
Finally, the scattered nature of data in the current business world caught up with everyone. Information now lives everywhere, from cloud apps to on – premises systems to shared folders to vendor platforms. Each different location adds another window to monitor and track closely.
What 2025 showed us is that breaches come from many small gaps lining up at the wrong time. Learning how to prevent data breaches and fixing them takes more than tools and resources. That’s the real question leaders face now. It takes awareness, ownership, and constant follow – up post – remediation.
AI – DRIVEN PATTERNS AND OPERATIONAL RISKS OF DATA BREACHES IN 2025
AI has emerged as an unparalleled force in the modern business world. But how is this force affecting data breaches and the risk surface? Let’s understand that in this section.
1. AI-Powered Phishing and Deepfakes: In 2025, phishing underwent an upgrade. To clarify, the attackers used AI to write clean emails, copy real writing styles, and time messages perfectly. Some even used voice deepfakes. Hence, AI removed the rough edges, which made human judgment harder. For security teams, this means that traditional awareness training is ineffective, as traps feel more personal now.
2. Shadow AI Inside the Business: Another quiet risk emerged from within the organization. Employees started using AI tools on their own, where they uploaded contracts, logs, and customer data just to “get faster answers.” There is zero review and approval. When a breach happened, no one knew where sensitive data had gone. These factors drove up investigation time and legal costs. Thus, shadow AI didn’t cause every breach, but it made recovery slower and more inconsistent.
3. AI-Scaled Exploitation: After gaining access, attackers used AI to move more quickly across the systems during a data breach. Here, the AI tools scanned environments, mapped systems, and flagged weak spots in minutes. What once took days now took hours.
4. AI for Detection and Containment: Still, AI wasn’t only a threat. Many firms used it to spot odd behavior sooner. In this context, automated alerts flagged strange logins and unusual data movement across your digital assets. The lesson from 2025 is balanced, where AI has raised the stakes on both sides. The risk is not AI in itself; instead, it lies in using it without control, visibility, and clear ownership.
MAJOR IMPLICATIONS: REGULATORY, COMPLIANCE, AND LEGAL
Data breaches in 2025 quickly turned into legal and compliance problems. Here’s how that played out for regulated businesses.
GDPR and Global Privacy Laws
- Breach notification timelines stayed tight. In many regions, firms had 72 hours to report. If you miss that window, then fines will follow, sometimes exceeding millions.
- Regulators focused on provable evidence. They asked simple questions. When did you know about the data breach? What did you do next to prevent it?
US State Breach Notification Rules
- The US stayed fragmented, with each state having its own rules.
- Some required notice to customers, while others required notice to regulators or attorneys general.
Healthcare and Finance Pressure
- Healthcare firms will face HIPAA investigations after patient data breaches.
- Here, regulators will review your access controls and training records.
- Financial firms also had to deal with Gramm – Leach – Bliley Act (GLBA) reviews following the exposure of customer data.
Third-Party and Supply Chain Exposure
- Most data breaches started with vendors. Therefore, under SOC 2, firms had to show effective controls focusing on vendor management and monitoring.
- Plus, the ISO frameworks pushed for accountability in risk management, risk ownership, and evidence.
Today, the consequences of a data breach are intricate and multi – layered. Legal, regulatory, and audit impacts build quickly. Moreover, the documentation, time taken for response, and accountability matter as much as technical fixes.
BEST PRACTICES TO PREVENT SUCH DATA BREACHES
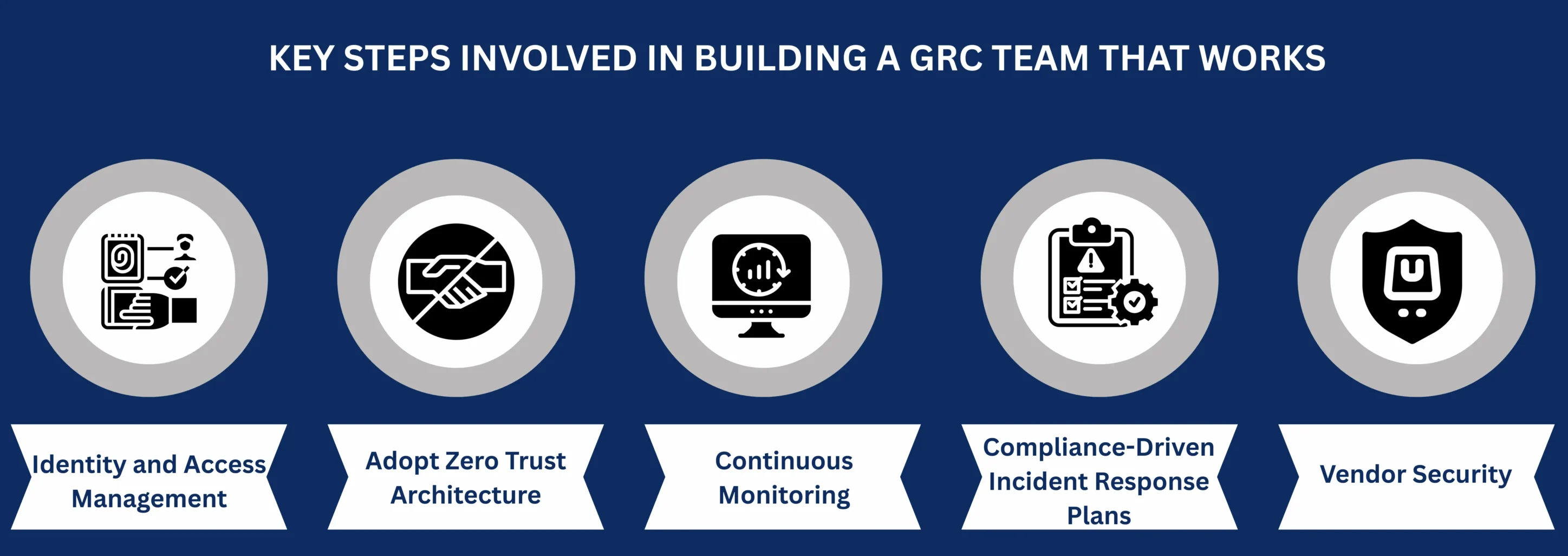
By 2025, one thing is clear. Most breaches don’t happen due to weak technology. Instead, they start with broken basic security controls. Let’s learn about some of the best practices for preventing data breaches in this section.
Identity and Access Management: Attackers still try to exploit the people first. That’s why identity governance matters. Review who has access and remove what’s no longer needed. Use multi – factor authentication (MFA) everywhere, not just on email.
Adopt Zero Trust Architecture: Zero trust is a habit where you verify every request, even inside your network. This practice is relevant now as teams work across cloud and on – premises systems.
Continuous Monitoring: A data breach won’t wait for your quarterly access reviews. Therefore, adopting a culture of continuous monitoring helps you spot trouble early. To add on, the AI – assisted tools can flag odd behavior faster than manual efforts. But remember that tools don’t replace judgment. You still need experts who know what “normal” looks like in your environment.
Compliance – Driven Incident Response Plans: When a security incident hits, problems follow. This means your teams rush to contain it, regulators question your security posture, and auditors ask for proof of your security controls. In contrast, if your data breach response plans match regulatory compliance requirements, then they become more effective.
Vendor Security: Many 2025 breaches began outside the company. Hence, a solid vendor risk program matters. Consider enquiring about SOC 2 reports from your vendors and checking whether they have complied with ISO frameworks and standards like HIPAA, GDPR, and CCPA.
To summarize, preventing data breaches is about discipline, visibility, and follow – through
CLOSING THOUGHTS
The data breaches of 2025 prove that every delay widens your risk exposure, attracts legal fines, and weakens your trust. What used to be a security issue is now a board – level business problem. In the current corporate world, startups realize it through stalled enterprise deals. Growing firms feel it through audit pressure, customer expectations, and rising insurance costs. Enterprises faced the need when a data breach caused by a vendor mistake turned into a global incident.
All these could be overwhelming for you. But CertPro is here to lead the journey. We work with businesses before a breach forces action. We help you identify risk early, build strong controls, and prove compliance through audits that actually reflect how your business runs. Our standardized and quality audit approach connects security, compliance, and operations to help you align with the security expectations of your regulators, customers, and partners.
We support independent audits and certifications for ISO frameworks like ISO 27001, ISO 27701, ISO 27018, and ISO 42001. Plus, we are a global leader in helping businesses achieve SOC 2 compliance in an affordable way that is uncompromised in quality.
In this context, the real cost is not about investing in compliance. But postponing it dictates a timeline for your firm that could be detrimental to your progress. If you want security, control, and order in 2025, connect with CertPro today. Let’s assess where you stand and fix the gaps before they turn into headlines.
FAQ
What is a data breach?
A data breach happens when an unauthorized individual gains access to private and sensitive information. It includes customer details, employee files, medical records, and payment information. A data breach puts sensitive information at risk and could cause legal and business consequences.
What are examples of data breach?
Examples of data breaches include a company server hacked and customer data exposed, employee credentials leaked through phishing, or a third – party vendor compromise that reveals internal records. Any event that exposes private data to unauthorized users is a breach.
Who is affected by a data breach?
Customers, employees, and partners are directly affected when their personal data is exposed. Businesses also suffer from financial loss, regulatory fines, damaged reputation, and operational disruption after a breach.
What are the steps involved in a data breach response plan?
A breach response plan includes detecting and confirming the incident, containing the impact, notifying stakeholders, investigating the root cause, restoring systems, and reviewing controls to prevent future breaches.
What is the most common cause of a data breach?
The most common cause of a data breach is credential theft through phishing or weak authentication. Attackers often exploit stolen usernames and passwords to enter systems and move laterally to access sensitive data
KEY DATA BREACH STATISTICS IN 2025
MAJOR DATA BREACHES OF 2025 AND ITS IMPACT ON INDUSTRY
CAUSES AND PATTERNS IDENTIFIED IN 2025 DATA BREACHES
AI-DRIVEN PATTERNS AND OPERATIONAL RISKS OF DATA BREACHES IN 2025
MAJOR IMPLICATIONS: REGULATORY, COMPLIANCE, AND LEGAL
CONTINUOUS INTEGRATION FOR DEVSECOPS: HOW AUDITORS EVALUATE SECURITY CONTROLS
Identity Verification in SOC 2 and ISO 27001: Audit Expectations for User Onboarding
ETHICAL HACKING FOR AUDIT ASSURANCE: STRENGTHENING SOC 2, ISO 27001, AND HIPAA COMPLIANCE
Ethical Hacking For Control Effectiveness. Uncover Gaps And Strengthen Audit Evidence For SOC 2, ISO 27001, And HIPAA Compliance Reviews.