Security reviews used to happen at the tail end of a deal. Today, they happen in the first conversation. Enterprise buyers come prepared. They ask about access controls before they ask about pricing. They want incident documentation before they agree to a demo.
The SOC 2 framework sits at the center of those conversations. For SaaS and technology companies, the SOC 2 framework has become a measurable trust signal. Vendors who can walk buyers through clear, documented controls close deals faster. Those who can't hit friction that's hard to explain and harder to reverse.
What's less obvious is that the SOC 2 framework itself has changed. Heading into 2026, the way auditors assess controls, the depth of evidence they expect, and the specific risk areas they focus on have all shifted. Teams that last went through an audit in 2022 or 2023 may be operating on assumptions that no longer hold.
This guide explains exactly what's changed, why it matters, and where technology firms should focus their compliance effort in 2026.

Concern
Enterprise buyers now evaluate security at the very start of the sales cycle, so SOC 2 readiness directly impacts deal velocity. However, many SaaS teams still rely on outdated assumptions from earlier audit cycles. As a result, gaps appear in critical areas such as vendor risk, AI usage, and access controls. At the same time, auditors expect deeper and continuous evidence across the full audit period. Therefore, weak or inconsistent documentation leads to audit findings, slows down procurement reviews, and creates friction in enterprise deals.
Overview
The SOC 2 framework in 2026 reflects a clear shift toward real-time operational visibility. Third-party risk management now requires continuous monitoring, formal risk scoring, and periodic reassessment. AI systems fall under existing criteria, which means teams must document validation processes, accuracy checks, and access controls. Access reviews must be structured, timestamped, and consistently recorded. Continuous monitoring has replaced periodic evidence collection, so auditors now evaluate controls based on how they perform over time.
Solution
To align with these changes, teams should begin with a clear gap assessment based on current audit expectations. Then, they should integrate evidence collection into daily workflows, including access reviews, system logging, and ticketing processes. At the same time, assigning clear ownership for each control helps maintain accountability across functions. Furthermore, organizations must implement ongoing vendor risk management with defined review cycles and triggers for reassessment. Finally, teams should map and document AI system usage, especially where customer data is involved.
What Is SOC 2 And Why SOC 2 Framework Keeps Evolving?
What is SOC 2? It's an auditing standard developed by the AICPA that defines how technology and cloud-based companies should protect the data they store, process, and transmit. The SOC 2 framework structures those expectations into five Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy.
Security is mandatory in every SOC 2 audit. The other four criteria are optional, though most SaaS firms include Availability and Confidentiality because enterprise buyers request them directly.
Understanding what is SOC 2 also means understanding why the SOC framework isn't static. The entire SOC framework operates on the principle that security controls must reflect current risk, not the risk landscape from two years ago. The AICPA updates guidance as threats evolve, as cloud infrastructure grows more complex, and as the operational risk profile of technology companies changes.
That's by design. A framework that adapts stays relevant. But it also means businesses need to keep pace. Teams relying on stale control documentation or audit assumptions from earlier cycles often find gaps at the worst possible moment — mid-audit or mid-deal. Knowing what is SOC 2 today means knowing how it's being applied right now, not how it was applied when you last looked.
What Has Changed In SOC 2 Framework In 2026?
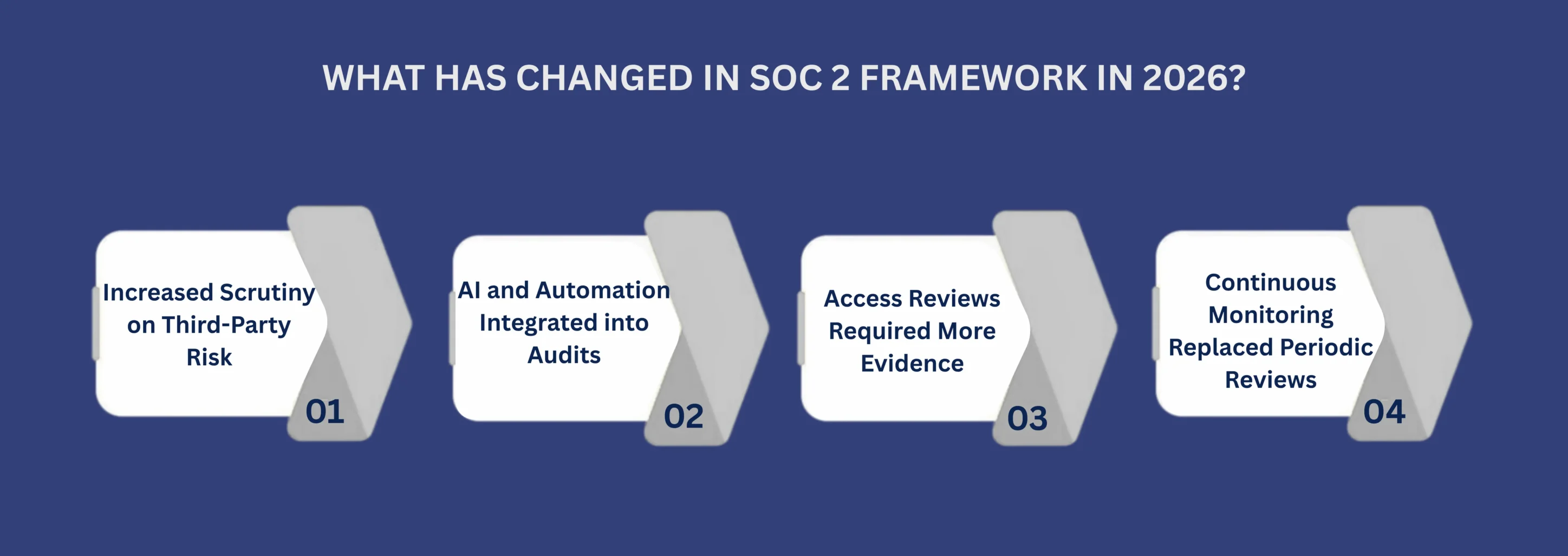
Increased Scrutiny on Third-Party Risk
The SOC 2 framework has always required vendor oversight. In 2026, auditors give it serious depth. A vendor list and a signed agreement aren't sufficient anymore. Auditors now expect documented risk ratings, defined review frequencies, and clear evidence that your team reassesses vendors when their services change or when incidents originate on their end.
AI and Automation Integrated into Audits
AI tools have embedded themselves in most SaaS workflows. In 2026, auditors started asking where AI sits in your data environment and whether it touches customer data directly. The SOC 2 framework doesn't have a dedicated AI criterion yet, but the existing Security and Processing Integrity criteria now apply more directly to automated decision-making systems and AI-assisted data workflows.
Access Reviews Required More Evidence
Access control has always been central to the SOC 2 framework. What's changed is the standard of proof. Auditors now expect documented access reviews that are timestamped, structured, and tied to a defined schedule. A quarterly access review that's completed, recorded, and retrievable is now a baseline expectation.
Continuous Monitoring Replaced Periodic Reviews
The old approach of collecting evidence before the audit, organizing it quickly, and submitting it doesn't hold up the way it once did. The SOC 2 framework in 2026 favors teams that monitor consistently and log continuously across the full audit period. Auditors sample broadly, and gaps in alert review, incident documentation, or system logging are visible.
SOC 2 Requirements That Tech Firms Misunderstand
SOC 2 requirements span a wide range of daily behaviors. Most technology firms have the right tools. Fewer have the right habits. These are the control areas where gaps appear most often and where audits slow down.
Scope Definition: A scope that's too narrow misses what buyers actually care about. Too broad and the audit becomes expensive and unwieldy. Getting scope right before fieldwork begins saves significant time and cost.
Evidence Ownership: SOC 2 requirements work best when specific people own specific controls — people who understand what they're accountable for and collect evidence as part of their regular workflow. When ownership is vague, evidence collection becomes reactive and inconsistent.
Change Management Records: Engineering teams usually have strong release processes. What they often lack is documentation that auditors can trace clearly. Deployment logs, approval records, and test results need to exist in a structured, retrievable format — not scattered across channels and tickets.
Incident Response Documentation: Auditors don't expect zero incidents. They expect structured, documented responses with clear timelines and resolution records. Sparse incident logs create findings that slow the audit and raise questions during enterprise security reviews.
Vendor Reassessment: SOC 2 requirements now treat vendor risk as an ongoing responsibility, not a one-time task. Initial vendor reviews are expected. Re-evaluations when vendor circumstances change are equally expected, and auditors ask for both.
Key Steps For Aligning With SOC 2 Compliance Framework In 2026
-
Start With a Gap Assessment
Many teams reach for compliance software before they've mapped their actual control gaps. The SOC 2 compliance framework rewards clear thinking before automation. Run an honest comparison of your current operations against what auditors test in 2026. That assessment tells you where to invest effort and where your existing practices already hold up.
-
Build Evidence Into Normal Operations
Evidence collection works best when it's a natural byproduct of daily work rather than a separate task that runs on urgency. Ticketing systems, access review schedules, deployment pipelines, and monitoring logs should generate audit-ready evidence as operations run. Teams that treat evidence as a continuous output move through audits faster and with far less friction.
-
Distribute Ownership Across Functions
The SOC 2 framework is a cross-functional responsibility. Engineering, IT, security, and leadership each carry a share of it. Assigning one compliance lead without distributing accountability creates bottlenecks. Each control domain needs a clear owner who understands the specific SOC 2 framework requirement and the evidence it demands.
-
Revisit Your Vendor and AI Exposure
Given the 2026 updates to the SOC 2 compliance framework, vendor oversight and AI-related controls deserve a dedicated review. Map your full vendor ecosystem. Identify where AI systems interact with customer data. Document your review cycle and the conditions that trigger re-evaluation. These are areas where auditors spend real time in current examinations.
How Enterprise Buyers View Your SOC 2 Reports
A SOC 2 report does more than satisfy procurement checklists. It tells a story about how your company actually runs. Buyers read that story carefully, and in 2026, they're more fluent in what it means than they were two or three years ago.
Procurement teams at enterprise companies now include vendor risk analysts who understand the SOC 2 framework well enough to spot control gaps, question audit periods, and push back on Type 1 reports when their security policy requires Type 2.
Gaps Signal Culture, Not Just Process: When an auditor flags a finding, experienced buyers don't just note the finding. They read it as evidence of how your team prioritizes security in daily operations. A gap in access reviews or a missing vendor reassessment tells them something about internal discipline, not just documentation.
Report Timing Carries Its Own Signal: Buyers also look at when your last audit was completed. A SOC 2 report that's fourteen months old raises questions even before anyone reads the findings. Staying current with your audit cycle is itself a trust signal. It shows that compliance is a continuous commitment, not a credential you earned once and left on the shelf.
Conclusion
The SOC 2 framework has always been grounded in operational reality. In 2026, that reality is tested with more precision. Auditors examine controls with greater depth. Buyers interpret audit reports with sharper questions. And the distance between firms that run a disciplined SOC 2 compliance framework and those that treat compliance as a formality is becoming visible in sales cycles, procurement reviews, and customer retention conversations.
CertPro CPA LLC is a licensed CPA firm that conducts SOC 2 examinations for technology organizations with professional independence and precision. We assess what exists, test how it performs under real operating conditions, and issue reports that enterprise buyers, procurement teams, and regulators trust. CertPro also performs examinations across ISO 27001, HIPAA, GDPR, and related frameworks, giving technology companies one licensed examiner who understands how compliance obligations interact in modern SaaS environments.