SOC 2 Certification in Chicago
Executive Summary: SOC 2 Certification in Chicago is an attestation engagement conducted exclusively by a Licensed CPA Firm under AICPA Trust Services Criteria. CertPro, a Licensed CPA Firm, performs SOC 2 examinations for Chicago-based organizations across financial services, SaaS, logistics technology, and healthcare IT — issuing formal attestation reports that confirm controls are suitably designed and operating effectively.
OUR CLIENTS










What Is SOC 2 Certification in Chicago?
SOC 2 Certification in Chicago is not a government-issued license or a vendor-granted badge — it is a formal attestation engagement conducted by a Licensed CPA Firm under standards established by the American Institute of Certified Public Accountants (AICPA). The result of a completed SOC 2 engagement is an attestation report, not a certificate in the traditional sense. This distinction matters: an organization becomes “SOC 2 certified” when a Licensed CPA Firm has independently examined its controls and issued a formal opinion confirming that those controls meet the applicable Trust Services Criteria.
The AICPA developed the SOC 2 framework specifically to address data security, availability, processing integrity, confidentiality, and privacy controls at service organizations. Unlike ISO 27001, which produces a certificate from an accreditation body, SOC 2 produces a detailed attestation report that describes the auditor’s examination procedures and findings. This report-based format provides far greater transparency into the specific controls tested, the period covered, and the auditor’s conclusions — making SOC 2 attestation reports highly valued by enterprise procurement teams, regulators, and sophisticated buyers in Chicago’s B2B marketplace.
Chicago’s position as a major U.S. hub for financial services, SaaS development, logistics technology, and global corporate headquarters means that SOC 2 Certification carries significant commercial weight in this market. Large enterprises headquartered along the Chicago metropolitan corridor — from the Loop’s financial district to the broader technology corridor — regularly require SOC 2 reports from their vendors and cloud service providers before executing contracts. For Chicago-based organizations serving these clients, SOC 2 Certification in Chicago is frequently a prerequisite for revenue-generating business relationships.
The AICPA Framework and Trust Services Criteria
The AICPA framework governing SOC 2 examinations is codified in AT-C Section 205 (Examination Engagements) and the Trust Services Criteria (TSC) published in TSP Section 100. These standards define the criteria against which a service organization’s controls are evaluated. The Security criterion — also called the Common Criteria — is mandatory in every SOC 2 examination. The remaining four criteria (Availability, Processing Integrity, Confidentiality, and Privacy) are included based on the organization’s service commitments and the nature of the data it processes. A Licensed CPA Firm determines which criteria apply during scope definition at the outset of the engagement.
The Trust Services Criteria are organized into categories covering logical and physical access controls, system operations, change management, risk mitigation, and monitoring activities. Each criterion contains specific points of focus that the auditor evaluates through documentation review, inquiry, observation, and re-performance procedures. For Chicago organizations, aligning internal controls with these criteria before the examination period begins is essential to producing a clean attestation report. Controls that have been implemented but not consistently operated will generate findings — and findings in a SOC 2 report are visible to every recipient of that report.
SOC 2 Attestation vs. Other Compliance Frameworks
SOC 2 attestation differs from compliance frameworks such as HIPAA, PCI DSS, and NIST in a fundamental way: it produces a formal auditor’s opinion issued under professional attestation standards, not merely a self-assessment or a checklist. When a Chicago organization receives a SOC 2 Type II attestation report, recipients can trust that an independent Licensed CPA Firm examined evidence, tested controls across a defined period, and formed a professional opinion. This level of independent assurance is what distinguishes a SOC 2 examination from internal compliance programs or questionnaire-based vendor assessments.
| Framework | Issuing Body | Output Type | Geographic Relevance | Annual Renewal |
|---|---|---|---|---|
| SOC 2 | AICPA (Licensed CPA Firm) | Attestation Report | U.S.-centric, global acceptance | Yes — annual examination cycles |
| ISO 27001 | Accreditation Body / CB | Certificate | Global | Surveillance audits + 3-year recertification |
| PCI DSS | PCI SSC / QSA | Report on Compliance | Global (payment card industry) | Annual assessment |
| HIPAA | HHS / Internal | Self-assessment / OCR audit | U.S. healthcare sector | Ongoing compliance |
SOC 2 Type I vs. SOC 2 Type II: Explicit Comparison for Chicago Organizations
SOC 2 Certification in Chicago is available in two distinct report types — Type I and Type II — each serving a different purpose and carrying a different level of assurance. Understanding the distinction between these two report types is essential for Chicago organizations determining which engagement best fits their current operational maturity, client requirements, and timeline constraints. The choice between Type I and Type II directly affects the scope of the examination, the duration of the engagement, and the commercial value of the resulting attestation report.
SOC 2 Type I: Design Evaluation at a Point in Time
A SOC 2 Type I audit in Chicago evaluates whether a service organization’s controls are suitably designed to meet the applicable Trust Services Criteria as of a specific date. The auditor examines the design of controls — their structure, the policies governing them, and the procedures in place — but does not test whether those controls operated effectively over a period of time. A Type I report is particularly useful for organizations that have recently implemented their control environment and need to demonstrate to clients or prospects that their controls are properly structured before accumulating sufficient operational history for a Type II examination.
For Chicago startups, early-stage SaaS companies, and organizations entering enterprise procurement processes for the first time, a SOC 2 Type I audit report provides an initial baseline of assurance. It signals to prospective clients that controls have been formally examined by a Licensed CPA Firm — even if the operating effectiveness testing of a Type II has not yet been completed. Many Chicago-based fintech companies and cloud service providers use a Type I report as a bridge while they accumulate the monitoring period required for a Type II engagement.
SOC 2 Type II: Operating Effectiveness Over a Defined Period
A SOC 2 Type II certification engagement in Chicago evaluates both the design and the operating effectiveness of controls over a defined review period — typically six to twelve months. The auditor tests whether controls not only existed and were suitably designed, but also whether they functioned as intended throughout the entire monitoring period. This requires evidence collection across the full review window: logs, exception reports, access reviews, change management records, and other operational documentation that demonstrates continuous control operation.
SOC 2 Type II reports carry substantially greater assurance value than Type I reports and represent the standard requirement for enterprise procurement in Chicago’s financial services and large corporate sectors. A twelve-month Type II attestation report demonstrates that controls operated consistently across an entire year — through personnel changes, system updates, and operational events. For Chicago organizations competing for contracts with major financial institutions, healthcare systems, or multinational corporations headquartered in the city, a Type II report is typically the minimum acceptable standard.
| Attribute | SOC 2 Type I | SOC 2 Type II |
|---|---|---|
| Evaluation Focus | Design of controls at a point in time | Design + operating effectiveness over a period |
| Review Period | Single date (point in time) | Minimum 6 months, typically 12 months |
| Evidence Testing | Design review and documentation inspection | Sampling, re-performance, observation over full period |
| Commercial Acceptance | Early-stage / bridge assurance | Enterprise-grade; required by most large buyers |
| Typical Timeline | 6–10 weeks from scope definition | 3–6 months depending on review period length |
Choosing Between Type I and Type II for Your Chicago Organization
The decision between a SOC 2 Type I and Type II engagement in Chicago depends primarily on client requirements and the organization’s stage of control maturity. Organizations with well-established controls and a clear client mandate for Type II should proceed directly to a Type II examination — skipping the intermediate Type I step. Organizations that are early in their control implementation and facing an immediate procurement deadline may benefit from completing a Type I report first, then progressing to Type II once the monitoring period has elapsed. CertPro, as a Licensed CPA Firm, determines the appropriate engagement structure during the initial scope definition phase based on the organization’s documented control environment and client-facing requirements.
The Five AICPA Trust Services Criteria Explained
The AICPA Trust Services Criteria define the five categories of controls evaluated in every SOC 2 examination. Each criterion maps to a specific set of control objectives and points of focus that the Licensed CPA Firm tests during the engagement. Chicago organizations must understand which criteria apply to their service commitments before scoping the examination — selecting criteria that do not align with actual service delivery creates examination scope mismatches, while omitting applicable criteria may undermine the report’s usefulness to clients.
The Security criterion is mandatory in every SOC 2 engagement and serves as the foundation of the entire examination. It addresses the protection of system resources against unauthorized access — covering logical access controls, network security, encryption, vulnerability management, incident response, and monitoring. The Security criterion is organized into nine categories of Common Criteria (CC1 through CC9), each containing multiple points of focus. For Chicago-based SaaS companies and cloud service providers, the Security criterion typically generates the largest volume of control testing because it encompasses the broadest range of technical and organizational controls.
Key control areas examined under the Security criterion include user access provisioning and deprovisioning, multi-factor authentication, encryption of data in transit and at rest, firewall and network segmentation configurations, patch management procedures, security incident detection and response protocols, and vendor management controls. Chicago organizations operating in cloud environments — using AWS, Azure, or Google Cloud infrastructure — must demonstrate that their shared responsibility model controls are properly designed and, for Type II engagements, that they operated continuously throughout the review period.
The Availability criterion evaluates whether systems are available for operation and use as committed in service level agreements. This criterion is particularly relevant for Chicago-based managed service providers, cloud platforms, and financial technology companies whose clients depend on continuous system uptime. Controls tested under Availability include disaster recovery planning, business continuity procedures, system redundancy configurations, capacity monitoring, and performance benchmarking against contractual SLAs.
The Processing Integrity criterion evaluates whether system processing is complete, valid, accurate, timely, and authorized — applying primarily to organizations that process transactions or execute data transformations on behalf of clients. Chicago’s fintech sector, payment processing companies, and financial data analytics platforms frequently include this criterion. Confidentiality addresses whether information designated as confidential is protected in accordance with the organization’s commitments — critical for Chicago law firms, financial services firms, and healthcare IT organizations handling sensitive client data. Privacy governs the collection, use, retention, disclosure, and disposal of personal information in alignment with the organization’s privacy notice and applicable regulatory requirements, including intersections with GLBA for financial institutions and HIPAA for healthcare-adjacent organizations operating in Chicago.
- ✓Security (CC1–CC9): Mandatory criterion covering logical access, network controls, encryption, incident response, and monitoring
- ✓Availability (A1): System uptime, disaster recovery, business continuity, and SLA performance controls
- ✓Processing Integrity (PI1): Completeness, accuracy, validity, timeliness, and authorization of system processing
- ✓Confidentiality (C1): Protection of information designated as confidential under service commitments and contracts
- ✓Privacy (P1–P8): Collection, use, retention, disclosure, and disposal of personal information per privacy notice and applicable law

- ✓Security: The Common Criteria (Mandatory)
- ✓Availability, Processing Integrity, Confidentiality, and Privacy
SOC 2 Certification Process: Sequential Steps for Chicago Organizations
The SOC 2 examination process follows a defined sequence of professional audit procedures governed by AICPA attestation standards. Each stage of the SOC 2 engagement produces specific deliverables, involves distinct activities by both the Licensed CPA Firm and the client organization, and must be completed before the subsequent stage begins. Chicago organizations undergoing SOC 2 Certification for the first time should understand the full process structure to allocate internal resources appropriately and maintain examination timelines.
The examination begins with scope definition — the formal process of identifying which systems, services, infrastructure components, and Trust Services Criteria will be included in the SOC 2 engagement. CertPro’s Licensed CPA Firm auditors conduct a structured review of the organization’s service description, system boundaries, subservice organizations, and applicable service commitments. The scope definition phase produces the System Description that becomes Section III of the final attestation report. Errors in scope definition — such as excluding infrastructure components that process client data — can compromise the report’s accuracy and usefulness to its recipients.
During scope definition, CertPro’s auditors also determine the examination type (Type I or Type II), the review period for Type II engagements, the applicable Trust Services Criteria, and the evidence collection approach. For Chicago organizations with complex multi-cloud environments, third-party hosting arrangements, or shared infrastructure with parent or affiliate companies, this phase requires careful delineation of organizational boundaries and subservice organization carve-out versus inclusive decisions. The audit program — the formal document specifying the procedures the auditor will execute — is finalized before evidence collection begins.
Following scope definition, CertPro auditors execute the audit program by requesting and reviewing the organization’s control documentation. This stage includes examination of information security policies, access control procedures, change management processes, vendor agreements, risk assessment documentation, business continuity plans, and system configuration standards. Auditors verify that documented controls align with the control descriptions in the System Description and that the controls, as documented, are capable of meeting the applicable Trust Services Criteria points of focus.
For Type II engagements, control testing is the most substantive phase of the SOC 2 examination. CertPro auditors collect evidence across the full review period — typically twelve months for Chicago organizations with established control environments — using sampling methodologies aligned with AICPA auditing standards. Evidence types include access provisioning and deprovisioning records, change management tickets, vulnerability scan reports, penetration testing results, backup completion logs, security awareness training records, and incident response documentation. The SOC 2 attestation engagement in Chicago requires that evidence be sufficient, appropriate, and traceable to specific control descriptions in the System Description.
Control testing procedures include inquiry (interviews with control owners), observation (direct observation of control execution), inspection (review of documentation and records), and re-performance (independent re-execution of a control to verify it produces the expected outcome). For automated controls — such as system-enforced access restrictions, automated log monitoring alerts, or configuration enforcement policies — auditors examine the configuration settings and verify that the automated control operated throughout the review period without interruption. CertPro’s audit fieldwork for Chicago clients is conducted both on-site and remotely, depending on the nature of the controls being tested and the organization’s operational structure.
Following control testing, CertPro auditors document any identified control exceptions — instances where a control did not operate as described, was not consistently applied, or produced an unintended outcome. Exceptions are categorized and evaluated for their materiality relative to the overall opinion. The organization has an opportunity to review identified exceptions, provide management responses, and present additional evidence before the report is finalized. This nonconformity review phase is a formal component of the SOC 2 examination process and ensures that the final report accurately reflects both the auditor’s findings and the organization’s perspective.
CertPro then drafts the SOC 2 attestation report, which includes the Independent Service Auditor’s Report (the auditor’s formal opinion), the Management Assertion, the System Description, and the detailed description of tests performed and results obtained. The completed report is issued under CertPro’s Licensed CPA Firm authority and delivered to the client organization. The report is then distributed to specified users — typically the organization’s clients, prospects, and regulators — under a use restriction that limits distribution to parties who have knowledge of the service organization and its controls.
- Scope Definition: Identify system boundaries, applicable Trust Services Criteria, and examination type (Type I or Type II)
- Audit Program Determination: Finalize examination procedures, evidence requirements, and review period
- Control Documentation Review: Examine policies, procedures, system configurations, and control design
- Evidence Collection (Type II): Gather operational evidence across the full review period using sampling methodologies
- Control Testing: Execute inquiry, observation, inspection, and re-performance procedures against sampled controls
- Nonconformity Review: Document exceptions, evaluate materiality, and obtain management responses
- Report Drafting: Prepare the SOC 2 attestation report including auditor’s opinion and detailed test results
- Attestation Issuance: Issue the final report under Licensed CPA Firm authority and deliver to the client organization
- Surveillance and Recertification: Initiate subsequent annual examination to maintain current attestation status
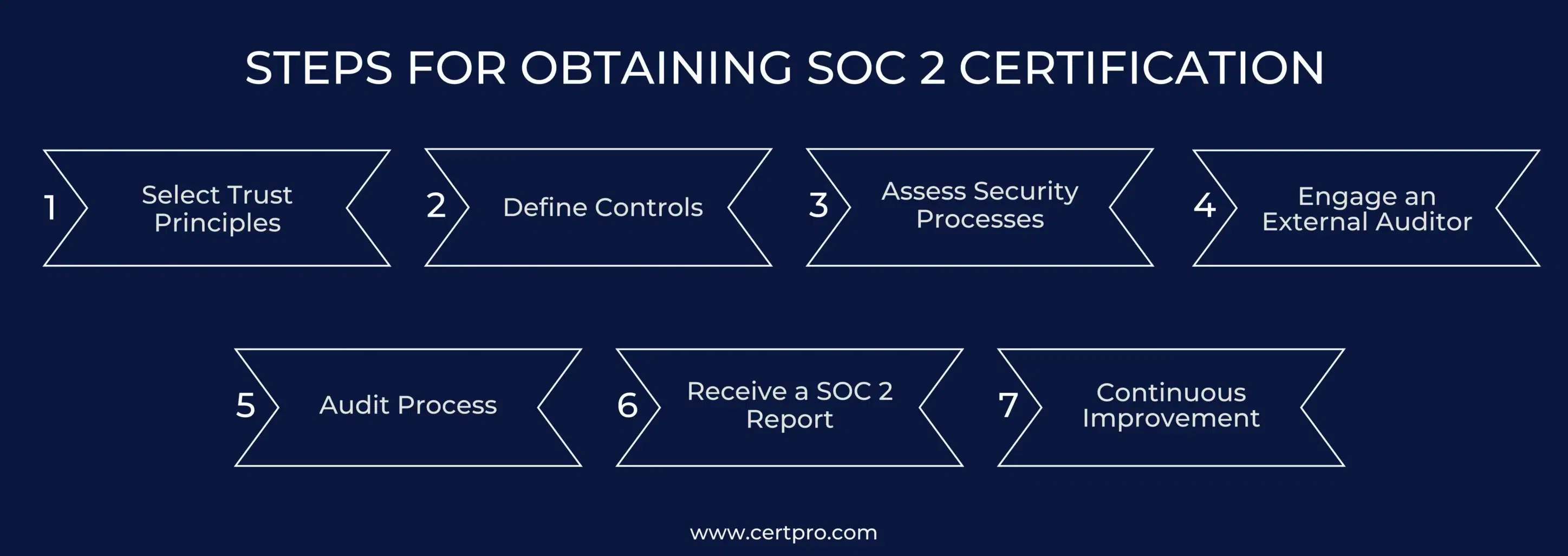
- ✓Stage 1: Scope Definition and Examination Planning
- ✓Stage 2: Control Documentation Review and Audit Program Execution
- ✓Stage 3: Evidence Collection and Control Testing (Type II)
- ✓Stages 4–7: Nonconformity Review, Report Drafting, and Attestation Issuance
SOC 2 Compliance Requirements for Chicago Businesses
SOC 2 compliance for Chicago businesses requires a documented, operational, and consistently applied control environment that covers each of the Trust Services Criteria included in the examination scope. Unlike prescriptive compliance frameworks that specify exact technical controls, SOC 2 is criteria-based — the organization must implement controls that are appropriate and sufficient to meet each criterion’s points of focus, given its specific system, services, and client commitments. This flexibility means that SOC 2 requirements differ between a Chicago fintech company processing payment transactions and a Chicago SaaS company delivering HR management software, even if both are examined under the same Security criterion.
A SOC 2 examination requires comprehensive written documentation of all in-scope controls. At minimum, Chicago organizations must maintain a current Information Security Policy, an Access Control Policy, a Change Management Policy, an Incident Response Plan, a Business Continuity and Disaster Recovery Plan, a Vendor Management Policy, a Risk Assessment process, and a Data Classification Policy. Each policy must be reviewed, approved, and dated — and evidence of annual policy review cycles is a standard auditor request during Type II engagements. Policy documents that are outdated, undated, or inconsistent with actual operational practices will generate exceptions during the examination.
Beyond formal policies, the examination requires operational documentation — the records produced by executing controls day-to-day. This includes access provisioning and deprovisioning tickets, quarterly user access review records, change request and approval documentation, vulnerability scanning reports and remediation tracking, security awareness training completion records, system backup logs, and incident response records. For Chicago organizations using automated ticketing systems such as ServiceNow or Jira, this documentation is typically available in audit-ready format. For organizations relying on manual or email-based processes, producing consistent operational records across a twelve-month period is frequently the most demanding aspect of SOC 2 examination preparation.
Technical controls form the operational foundation of the SOC 2 control environment. Chicago organizations under examination must demonstrate that multi-factor authentication is enforced for all privileged access and remote connections, that encryption is applied to data in transit (TLS 1.2 or higher) and data at rest, that production systems are separated from development and test environments, and that vulnerability scanning is conducted at defined intervals with findings tracked to remediation. Firewall rule sets, intrusion detection or prevention system configurations, and endpoint protection tool deployment records are standard evidence requests in every SOC 2 engagement conducted in Chicago.
Chicago organizations that rely on third-party subservice organizations — cloud hosting providers, co-location data centers, payment processors, or managed security service providers — must address these relationships in their SOC 2 examination. The examination scope must either include the subservice organization (inclusive method) or carve it out and document the complementary user entity controls the Chicago organization employs to manage the associated risks (carve-out method). Auditors require evidence of vendor due diligence, including review of subservice organization SOC reports, contractual security requirements, and ongoing vendor monitoring activities. For Chicago-based companies using AWS, Microsoft Azure, or Google Cloud, these hyperscale providers’ SOC reports are typically available and used as part of the evidence package.
- ✓Documentation Requirements
- ✓Technical Control Requirements
- ✓Subservice Organization and Vendor Requirements
Industry-Specific SOC 2 Demand in Chicago
Chicago’s economic composition drives high demand for SOC 2 Certification across multiple industry verticals. The city’s concentration of financial services firms, insurance companies, logistics technology providers, SaaS platforms, and healthcare technology organizations creates a dense market where SOC 2 reports are routinely required as a condition of doing business. Understanding which sectors drive SOC 2 demand in Chicago helps organizations benchmark their certification timeline against client expectations and competitive dynamics in their specific vertical.
Financial Services and Fintech
Chicago is home to major financial institutions, trading firms, investment managers, and a rapidly expanding fintech ecosystem — including companies in payments, lending technology, wealth management software, and regulatory technology. SOC 2 compliance for Chicago fintech companies is driven by two forces: the requirement that financial institution clients impose on their technology vendors, and the intersection of SOC 2 controls with GLBA (Gramm-Leach-Bliley Act) safeguards requirements. A SOC 2 Type II attestation report addressing the Security and Confidentiality criteria provides significant overlap with GLBA-required safeguards documentation, reducing duplicative compliance effort for Chicago fintech organizations serving bank and broker-dealer clients.
SaaS, Cloud Providers, and Technology Companies
Chicago’s technology sector includes hundreds of SaaS companies across HR technology, marketing technology, supply chain software, legal technology, and enterprise software categories. For these organizations, SOC 2 Certification is a standard sales enablement requirement — enterprise buyers in Chicago and nationally use SOC 2 reports as a primary vendor security evaluation tool, often replacing or supplementing lengthy security questionnaire processes. Chicago-based technology firms that are SOC 2 certified find that their enterprise clients expect current Type II reports, typically no older than twelve months, as a condition of contract execution.
Healthcare IT, Logistics Technology, and Other Sectors
Healthcare technology companies operating in Chicago — including electronic health record vendors, health information exchanges, clinical decision support platforms, and health insurance technology providers — frequently pursue both SOC 2 and HIPAA compliance. SOC 2 examination engagements for Chicago healthcare IT organizations typically include the Security, Availability, Confidentiality, and Privacy criteria, providing a framework that complements HIPAA Security Rule requirements without duplicating them entirely. Chicago’s position as a major logistics hub has also generated significant SOC 2 demand from logistics technology, supply chain visibility, and transportation management software companies — sectors where operational continuity and data confidentiality are primary client concerns.
- ✓Financial Services and Banking: GLBA alignment, vendor risk management requirements from financial institution clients
- ✓Fintech and Payments: SOC 2 compliance for Chicago fintech companies serving bank and broker-dealer clients
- ✓SaaS and Cloud Providers: Enterprise procurement requirement across all vertical markets
- ✓Healthcare IT: SOC 2 and HIPAA intersection for organizations handling protected health information
- ✓Logistics Technology: Availability and Confidentiality criteria emphasized for supply chain software providers
- ✓Insurance Technology: Data confidentiality and processing integrity requirements from insurance carrier clients
- ✓Legal Technology: Confidentiality criterion emphasis for document management and e-discovery platforms
- ✓Managed Service Providers: Security and Availability criteria for IT service delivery organizations
Benefits of SOC 2 Certification for Chicago Organizations
SOC 2 Certification in Chicago delivers measurable, concrete benefits that extend well beyond regulatory compliance. For Chicago organizations competing in B2B markets where enterprise clients, financial institutions, and global corporations dominate the buyer landscape, SOC 2 attestation provides independently verified evidence of security control effectiveness — evidence that internal security questionnaire responses and self-assessments cannot provide. The commercial, operational, and reputational benefits of SOC 2 Certification are well-documented across the Chicago market.
SOC 2 certified organizations that Chicago-based enterprises contract with enjoy a measurable advantage in procurement processes. Enterprise buyers — particularly financial institutions, insurance companies, and large healthcare systems headquartered in Chicago — use SOC 2 reports as a primary screening criterion for technology vendors. Organizations without a current SOC 2 report are frequently disqualified from consideration before the evaluation process begins. Conversely, organizations that present a clean SOC 2 Type II attestation report can accelerate procurement cycles by eliminating the extended security review period that non-certified vendors must navigate.
The revenue impact of SOC 2 Certification in Chicago extends beyond individual deal acceleration. Maintaining current SOC 2 Certification creates ongoing commercial value by enabling the certified organization to respond to security questionnaires with a standardized report rather than custom responses — reducing the sales operations burden associated with enterprise security reviews. Organizations with current SOC 2 Type II reports also report higher close rates on enterprise deals, shorter procurement timelines, and improved negotiating positions on contract security terms, as the attestation report pre-addresses many of the security warranties that buyers otherwise negotiate individually.
Beyond external commercial benefits, the SOC 2 examination process produces internal operational improvements that strengthen the organization’s security and reliability posture. The examination requires organizations to formalize, document, and consistently execute controls that may have previously been informal or inconsistently applied. This formalization reduces operational risk, improves incident response capability, and creates institutional knowledge about control ownership and accountability that survives personnel changes. Chicago organizations that have completed multiple annual SOC 2 examination cycles consistently report improvements in security incident metrics, access control hygiene, and change management discipline as direct outcomes of the sustained control discipline required to produce a clean SOC 2 report year over year.
- ✓Enterprise sales enablement: SOC 2 reports replace lengthy security questionnaire processes with recognized independent assurance
- ✓Procurement acceleration: Certified organizations move through vendor security review stages significantly faster than non-certified competitors
- ✓Revenue protection: Current SOC 2 report status prevents disqualification from enterprise procurement processes
- ✓Risk reduction: The examination process formalizes controls that reduce the likelihood and impact of security incidents
- ✓Regulatory alignment: SOC 2 controls overlap with GLBA, HIPAA, and CCPA requirements, reducing duplicative compliance effort
- ✓Client retention: Existing enterprise clients require current SOC 2 reports at contract renewal — absence creates churn risk
- ✓Insurance premium optimization: Many cyber insurance underwriters offer improved terms for SOC 2 certified organizations
- ✓Internal accountability: The examination process establishes clear control ownership and testing cadences that persist operationally
- ✓Investor confidence: SOC 2 Certification is increasingly cited in due diligence processes for Chicago-based technology companies raising growth capital
- ✓Partnership qualification: Large platform providers and ecosystem partners require SOC 2 Certification from integration and data-sharing partners

- ✓Competitive and Commercial Benefits
- ✓Operational and Internal Benefits
SOC 2 Certification Cost and Timeline in Chicago
SOC 2 Certification cost in Chicago is determined by examination scope — the number of Trust Services Criteria included, the complexity of the system environment, the number of in-scope subservice organizations, and whether the engagement is Type I or Type II. CertPro operates on a fixed-pricing model for SOC 2 engagements, providing Chicago organizations with transparent, predetermined examination fees rather than open-ended hourly billing arrangements. Fixed pricing enables accurate budgeting and eliminates the cost uncertainty that characterizes hourly-fee engagement structures.
Factors Affecting SOC 2 Examination Scope and Cost
The primary cost driver in a SOC 2 examination is scope complexity. An organization with a single-cloud environment, a well-documented control framework, and scope limited to the Security criterion will require significantly less examination effort than an organization with multi-cloud infrastructure, multiple data centers, numerous subservice organizations, and scope across all five Trust Services Criteria. Additional factors include the volume of in-scope systems and applications, the number of control owners who must be interviewed during fieldwork, the maturity and completeness of the organization’s existing documentation, and the length of the review period for Type II engagements.
Chicago organizations should plan for both the direct examination fee paid to the Licensed CPA Firm and the internal cost of preparing and producing examination evidence. Internal cost estimates vary widely based on the organization’s current documentation maturity, staff availability for auditor inquiries, and whether any control gaps must be addressed before the examination period begins. Organizations with immature documentation environments typically incur higher internal costs in their first examination cycle — costs that decrease substantially in subsequent annual cycles as the evidence collection process becomes systematized.
SOC 2 Timeline Expectations for Chicago Organizations
A SOC 2 Type I examination typically requires six to ten weeks from scope definition to report issuance, assuming the organization has complete documentation and responsive control owners available for auditor inquiries. A SOC 2 Type II examination requires a minimum of six months of review period plus four to eight weeks of fieldwork and reporting — meaning the total elapsed time from engagement start to report issuance is typically seven to nine months for a six-month review period and thirteen to fifteen months for a twelve-month review period. Chicago organizations facing near-term client deadlines should communicate their timeline requirements at the outset of the engagement to determine whether a Type I bridge report is warranted while the Type II monitoring period accumulates.
| Engagement Type | Review Period | Typical Timeline to Report | Best For |
|---|---|---|---|
| SOC 2 Type I | Point in time | 6–10 weeks | Early-stage organizations, immediate client requirements |
| SOC 2 Type II (6-month) | 6 months | 7–9 months total | Organizations with established controls seeking faster initial Type II |
| SOC 2 Type II (12-month) | 12 months | 13–15 months total | Enterprise-grade assurance; standard for mature organizations |
Why CertPro — A Licensed CPA Firm — Conducts SOC 2 Audits in Chicago
CertPro is a Licensed CPA Firm authorized under AICPA professional standards to conduct SOC 2 examination engagements and issue formal attestation reports. This authorization is not a credential that technology consulting firms, cybersecurity vendors, or compliance software platforms can hold — only Licensed CPA Firms are legally authorized to perform SOC 2 attestation engagements and issue opinions under AT-C Section 205. Chicago organizations that engage non-CPA entities for “SOC 2 preparation” or “SOC 2 certification” are receiving services that do not constitute a valid SOC 2 examination and cannot produce a recognized SOC 2 attestation report.
Licensed CPA Firm Authority and AICPA Standards
CertPro’s SOC 2 engagements are conducted under AICPA attestation standards — specifically AT-C Section 105 (Concepts Common to All Attestation Engagements) and AT-C Section 205 (Examination Engagements). All examination work is performed and reviewed by licensed CPA professionals with experience in information technology auditing and Trust Services Criteria evaluation. CertPro’s audit methodology is documented, quality-controlled, and subject to peer review requirements applicable to all AICPA-member CPA firms. This institutional accountability structure is what distinguishes a CertPro SOC 2 engagement from non-CPA vendor assessments or software-generated compliance reports.
Fixed Pricing and Examination-Based Engagement Model
CertPro delivers SOC 2 examination engagements for Chicago organizations under a fixed-pricing model. Fees are determined at the outset of the engagement based on scope, examination type, and system complexity — and do not change based on hours expended during fieldwork. This model eliminates the budget uncertainty inherent in hourly-fee structures and allows Chicago organizations to accurately forecast their SOC 2 examination costs for annual compliance budgeting. Fixed pricing applies to both Type I and Type II engagements, covering scope definition, audit program execution, evidence review, testing, report drafting, and final attestation issuance.
CertPro’s engagement model is strictly examination-based — the firm conducts SOC 2 audits and issues attestation reports. CertPro does not provide consulting, advisory, implementation, or gap analysis services. This separation maintains the independence required under AICPA independence standards for attestation engagements and ensures that CertPro’s audit opinions are not compromised by pre-engagement advisory relationships. Chicago organizations that require control implementation support prior to their SOC 2 examination must engage a separate, non-audit firm for those activities to preserve the independence of CertPro’s examination engagement.
SOC 2 Attestation Chicago: Evidence Collection and Audit Fieldwork
SOC 2 attestation engagements in Chicago follow a structured fieldwork methodology that CertPro’s Licensed CPA Firm auditors execute consistently across all client organizations. Fieldwork encompasses the procedures by which auditors collect, evaluate, and document the evidence supporting their examination conclusions. For Chicago organizations, fieldwork is typically conducted through a combination of remote evidence review and on-site visits for procedures that require physical observation or direct inspection of infrastructure components.
Evidence Request Management and Documentation
CertPro manages evidence requests through a structured request list issued at the beginning of fieldwork. This list itemizes every control being tested, the evidence type required, the format in which evidence should be provided, and the deadline for each submission. Chicago organizations with dedicated IT governance or compliance teams typically manage evidence requests through project management tools or secure file-sharing platforms. CertPro’s auditors review submitted evidence for completeness and adequacy before proceeding to testing — incomplete or inadequate evidence submissions result in follow-up requests that can extend the fieldwork timeline.
The SOC 2 examination fieldwork process in Chicago for a twelve-month Type II engagement typically involves multiple evidence collection waves — an initial documentation submission at engagement start, followed by operational evidence submissions covering the full review period. For controls tested through sampling, auditors select samples from the population of control executions across the review period and request evidence for each sampled item individually. This granular evidence collection process is what distinguishes a SOC 2 Type II examination from a point-in-time review — auditors are evaluating whether controls operated consistently month over month, not just whether they were in place at a single moment in time.
SOC 2 Certification in Chicago: Requirements Summary
The following summary consolidates the key requirements for SOC 2 Certification in Chicago across documentation, technical controls, operational processes, and organizational governance. Chicago organizations preparing for their first SOC 2 examination should verify that each requirement category is addressed before the examination period begins. Requirements that are not met at the start of the review period cannot be retroactively applied to the beginning of that period for Type II purposes — control effectiveness can only be demonstrated from the date the control was implemented and consistently executed.
- ✓Documented Information Security Policy, reviewed and approved annually with evidence of review cycle
- ✓Access Control Policy with procedures for provisioning, periodic review, and deprovisioning of user access
- ✓Change Management Policy with documented approval and testing requirements for all production changes
- ✓Incident Response Plan with defined roles, escalation procedures, and post-incident review process
- ✓Business Continuity and Disaster Recovery Plan with documented recovery time and recovery point objectives
- ✓Vendor Management Policy with security review requirements for subservice organizations and critical third parties
- ✓Risk Assessment process with documented assessment methodology, risk register, and treatment decisions
- ✓Multi-factor authentication enforced for all privileged and remote access to in-scope systems
- ✓Encryption of data in transit (TLS 1.2+) and data at rest for all in-scope systems storing confidential data
- ✓Vulnerability scanning conducted at defined intervals with remediation tracking and exception management
- ✓Security awareness training program with completion tracking for all personnel with access to in-scope systems
- ✓Separation of production, development, and test environments with access controls enforcing boundary separation
FAQ
▶
What is SOC 2 certification?
▶
What is SOC 2 Certification and how does it differ from SOC 2 compliance?
▶
How long does a SOC 2 examination take in Chicago?
▶
Which Trust Services Criteria does my Chicago organization need to include?
▶
Can a small Chicago company pursue SOC 2 Certification?
▶
Does SOC 2 attestation satisfy HIPAA or GLBA requirements for Chicago organizations?
▶
How often does SOC 2 Certification need to be renewed in Chicago?
▶
What is the difference between a SOC 2 engagement and a SOC 2 examination?

SOC 2 CERTIFICATION IN INDIA: STRATEGIES FOR TECH SECTOR COMPLIANCE IN 2026
The AICPA developed SOC 2 certification in India as a collection of guidelines to assist IT businesses in protecting client data. With the rapid growt…

THE IMPACT OF SOC 2 CERTIFICATION ON CUSTOMER RETENTION AND ACQUISITION
The world and businesses are changing together. Now, companies have transformed into online operations and transmitted data electronically. Therefore,…

Multi-Framework Compliance Guide: Best Practices and Strategies
Most compliance teams aren’t managing one framework. They’re managing three, four, sometimes five — simultaneously. A SaaS company selling to enterpri…
Get In Touch
have a question? let us get back to you.

