In the current corporate world, the top priority for organizations is to protect sensitive data from the rising cyberattacks. In such a situation, ISO 27001:2022 domains and controls, an internationally recognized standard, provide a structured framework for building and maintaining an Information Security Management System (ISMS). To clarify, it assists businesses in managing risks and securing sensitive information. Furthermore, this standard offers businesses clear steps to follow to manage security risks and protect sensitive data. The revised version of ISO 27001 security controls promotes a more streamlined and flexible approach to information security. ISO controls and domains are specific security measures outlined in standards like ISO 27001:2022 to help organizations manage risks and protect the confidentiality, integrity, and availability of information
Therefore, this blog explains the key components of ISO 27001 domains and controls. Also, we’ll look at the different domains and controls that companies could use to strengthen their information security. Each ISO domain focuses on a specific area, such as access control or asset management, helping organizations address different security challenges. Plus, by following these guidelines, businesses can reduce the risk of a data breach, safeguard their digital assets, and build trust with customers and partners. Whether you’re new to information security or you’re an expert looking to sharpen your knowledge, this blog will give you clear insights into the ISO 27001 domains and controls and how they could help businesses stay secure.
WHAT IS ISO 27001:2022?
ISO 27001:2022 is a widely recognized international standard that helps companies protect their sensitive information. Also, to follow this standard, businesses must build, implement, and continually improve an Information Security Management System (ISMS). Accordingly, this system helps businesses manage security risks and keep sensitive data safe.
Moreover, this standard provides a clear structure of regulations, processes, and ISO controls. These ISO 27001:2022 domains and controls are designed to make sure that information remains confidential, integrous, and available when needed. In particular, each ISO domain focuses on a specific area of security, helping businesses organize their efforts effectively. The ISO 27001 domains and controls encourage businesses to first identify the risks they face and then put the right measures in place to manage them.
The ISO 27001 domains and controls have two main sections.
- Clauses 4-10: These sections outline the mandatory ISO 27001 requirements that an organization must follow to build and maintain an Information Security Management System (ISMS).
- Annex A controls: It is a flexible list of controls that helps businesses to manage specific security risks.
Notably, ISO 27001 domains and controls can be used by any industry that aims to protect their sensitive data and information. It’s a globally relevant standard that helps businesses implement the best practices in information security, ensuring they protect their data and stay ahead of potential threats and cyberattacks.
How does ISO 27001:2022 help companies?
ISO 27001 domains and controls offer businesses a clear and organized way to manage information security risks and build a strong system to protect information. Here’s how it helps:
- Risk Management: ISO 27001 domains and controls help businesses assess and identify potential risks. One key control, ISO 27001 Annex A 8.20 network security implementation, focuses on securing network infrastructure to protect data in transit. Accordingly, this standard assists businesses in analyzing potential threats and weaknesses. It therefore helps companies to take the right actions to control and lower these risks. This ensures the growth of the business without any risks.
- Legal and Regulatory Compliance: It’s crucial for businesses to follow laws and regulations. Hence, ISO 27001 domains and controls help businesses to ensure that companies meet all the necessary regulatory compliance for information security. Such compliance is key to avoiding penalties and staying compliant with industry standards.
- Customer Confidence: When a company has a robust information security system, it shows customers that their data is safe. Since ISO 27001 domains and controls is well-known and widely trusted, it builds customer confidence. As a result, people are more likely to do business with companies that protect their sensitive information.
- Internal Process Improvement: Following ISO 27001 domains and controls helps businesses manage data access, respond to incidents, reduce risks, and improve operations. Thereby, saving money by avoiding costly security and process mistakes.
5. Competitive Advantage: Implementing ISO 27001 security controls and achieving its certification can make a business stand out from competitors. Moreover, it indicates that the company follows best practices for information security, which can be a deciding factor for customers and partners choosing who to work with.
Now let’s understand some of the important ISO security controls in the following section.
ISO 27001 DOMAINS AND CONTROLS: SAFEGUARDING INFORMATION SECURITY
ISO 27001 is a global standard that helps organizations establish, implement, maintain, and continually improve their Information Security Management Systems (ISMS). Specifically, it provides clear standards that companies could follow to protect their sensitive information. One important part of this framework is understanding what is Annex A, which outlines 93 control measures that support risk management and information security. But it doesn’t require them to use all 93 control measures listed. Instead, businesses have the freedom to select the ISO 27001 domains and controls that best suit their unique risks and requirements in a Statement of Applicability (SoA). Hence, by using the ISO 27001 security controls as a foundation, companies can create a more resilient information security management system (ISMS). Now let’s clearly understand what has changed from the 2013 to the latest version of ISO 27001:2022 domains and controls.
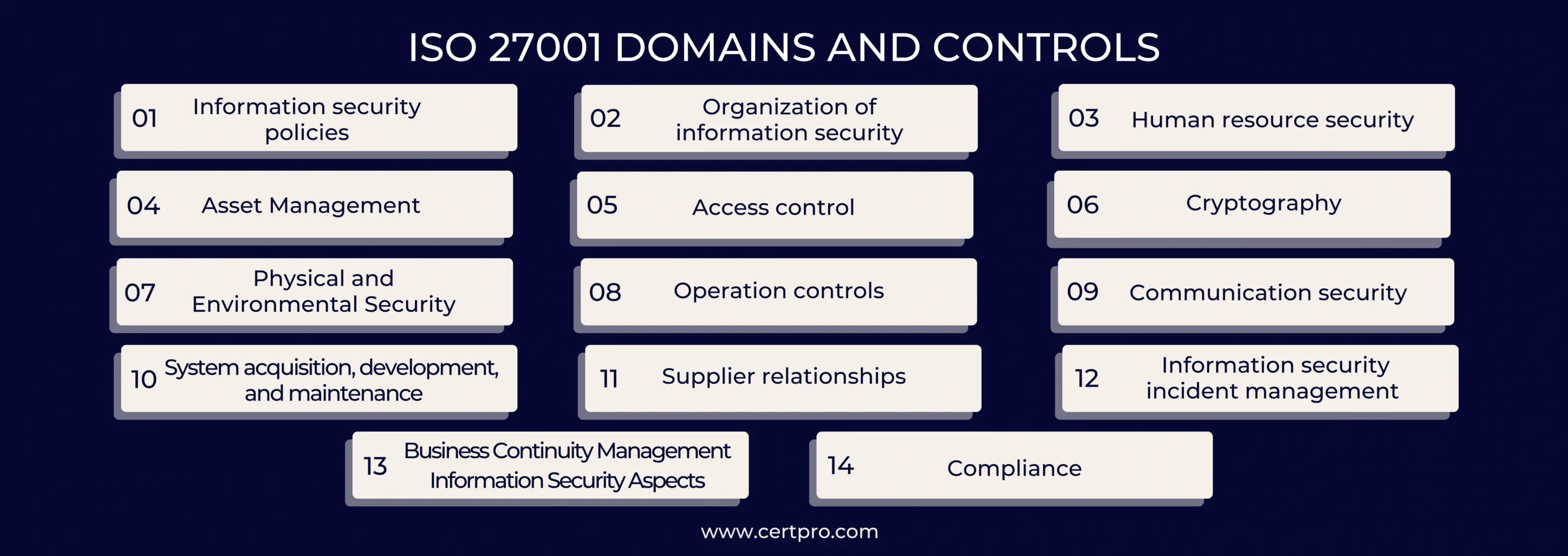
ISO 27001 Domains and Controls
The ISO 27001:2022 version has 93 controls classified into four main categories or domains. These domains are
- Organizational Controls (37 controls)
- People Controls (8 controls)
- Physical Controls (14 controls)
- Technological Controls (34 controls)
Getting clear idea of what is Annex A controls could help you define the specific measures and controls that an organization can implement to protect their sensitive information. With regard to the above-mentioned information, let’s understand some of the important ISO controls in detail.
1. Organizational Controls (37 Controls) (5.1-5.37)
The ISO 27001 security controls in this domain mainly focus on policies, governance, and risk management. To clarify, this section explains how to establish rules, processes, and governance to secure information.
A.5 Information Security Policies (2 controls)
A.5.1 Policies for Information Security
Organizations must establish clear security policies that align with their business objectives. Thus, the organizations must have a clear and well-documented policy that defines how they would protect their sensitive information. Moreover, this policy should be approved by the management and communicated to everyone.
A.5.2 Roles and Responsibilities
Organizations must define who is responsible for the security-related tasks. For example, a healthcare institution assigns a Data Protection Officer (DPO) to oversee patient data protection. This process is in accordance with ISO 27001 requirements, which emphasize assigning clear roles and responsibilities for managing information security.
A.5.3 Segregation of Duties
Organizations must provide separate responsibilities to workers to avoid the conflict of interest.
A.5.5 Contact with Authorities
Organizations must establish clear communication with regulators and law enforcement bodies. Therefore, the company must have a clear plan to approach the regulators and police during security incidents.
A.5.7 Threat Intelligence (Added in 2022)
Organizations must collect and analyze information about new threats and hacking trends to stay ahead of the attackers.
A.5.9 Inventory of Information and Other Associated Assets
Organizations must maintain an inventory and keep a list of everything they need to protect and who is responsible for it. For instance, this includes safeguarding software, computers, data, and other crucial digital assets. Following ISO 27001 requirements, businesses must ensure all assets are clearly identified, tracked, and managed to reduce security risks.
A.5.10 Acceptable Use of Information and Other Associated Assets
Companies must establish rules for how people can use their assets and sensitive information. For instance, a company is asking their employees to use the office laptops only for official purposes.
2. People Controls (8 Controls) (6.1-6.8)
People could be your biggest assets or weaknesses in an organization. Accordingly, these ISO 27001 security controls focus on managing human risks, like mistakes, ignorance, or malice, through training, rules, and oversight.
A.6.1 Screening
The entity must check the people’s background during hiring and intake of new employees. This helps them to identify the trustworthy employees. In simple words, one bad hire could potentially steal your data or sabotage your systems.
A.6.2 Terms and Conditions Employment
Companies should include security duties in job contracts to ensure employees understand their responsibilities. Thereby, establishing clear boundaries for them. For example, a software developer must sign a contract that assures they will not leak any code or client information.
A.6.3 Information Security Awareness, Education and Training
The entity must train their employees regularly to identify the security risk early. This is important because untrained staff become easy targets for attackers.
A.6.4 Disciplinary Process
The organization must follow an uncompromised system to take action against people who break the security rules. This helps in building accountability among the employees.
A.6.5 Responsibilities after Termination or Change of Employees
Organizations must make sure that ex-employees are restricted from accessing the digital assets of the firm after they leave the company.
A.6.7 Remote Working
A company must ensure the security of its employees who work remotely. Hence, they must be provided with VPNs (Virtual Private Network) and secured, encrypted laptops to protect the data.
3. Physical Controls (14 Controls) (7.1-7.14)
These ISO 27001 controls guide you in protecting the physical assets of your entity, such as the building, office, and equipment.
A.7.1 Physical Security Perimeters
The entity must use locks, fences, and barriers to protect the physical areas holding sensitive data.
A.7.2 Physical Entry
The entity is responsible for controlling and regulating the provision of access to secure areas that contain critical assets. To clarify, before entering secured areas, the entire IT department must scan their access cards and badges.
A.7.4 Physical Security Monitoring
The entity must keep the premises under full surveillance to detect any suspicious activity.
A.7.8 Equipment Siting and Protection
The company must lock and shield its important assets, like servers and laptops, to avoid theft or damage.
A.7.14 Secure Disposal or Re-Use of Equipment
The entity must ensure that the data from the old devices are wiped off before reusing them.
4. Technological Controls (34 Controls) (8.1–8.34)
The focus of these ISO 27001 controls is on tech-based defenses for hardware, software, and systems to safeguard data against cyberthreats.
A.8.1 User Endpoint Devices
The entity must secure devices like laptops, phones, or tablets that employees use. Endpoint devices are a prime target for attackers.
A.8.7 Protection Against Malware
The entity must use tools and awareness to stop viruses and ransomware from damaging the digital assets of the firm. Because malware has the potential to cripple systems or steal data.
A.8.12 Data Leakage Prevention
An organization must stop sensitive info from escaping. In simple words, a company must block employees from emailing customer lists outside the company. This is because leakage of sensitive information can ruin trust and break laws.
A.8.15 Logging
The entity must record system activity to spot issues or investigate breaches.
To address the modern needs, 11 new controls are added to ISO 27001 domains and controls:
- 5.7 Threat Intelligence: Monitor emerging threats.
- 5.23 Information Security for Cloud Services: Secure cloud usage.
- 6.7 Remote Working: Protect remote workers.
- 8.9 Configuration Management: Secure system setups.
- 8.11 Data Masking: Hide sensitive data.
- 8.12 Data Leakage Prevention: Stop data leaks.
- 8.16 Monitoring Activities: Watch for anomalies.
- 8.23 Web Filtering: Block risky websites.
- 8.28 Secure Coding: Write safer software.
IDENTIFY THE CONTROLS YOU NEED TO IMPLEMENT
Organizations don’t have to use all the 93 controls and measures listed in ISO 27001:2022. While the standard provides a detailed list of ISO 27001 Domains and Controls as a guide, companies should select and apply ISO controls based on their risks and business needs. To clarify, ISO 27001 encourages organizations to look at their information security risks and choose the best controls to manage them. The Statement of Applicability, a crucial document that bolsters this choice, explains the chosen controls and the reason behind them. Accordingly, conducting a gap analysis against ISO 27001 domains and controls can identify weaknesses in an organization’s security posture. Consequently, organizations must map their existing security measures to ISO 27001 domains and controls to identify gaps. Plus, they must consider implementing training for their staff. Because training employees on the ISO 27001:2022 domains enhances security awareness across the organization.
By doing this, companies can identify the biggest weaknesses, threats, and potential impacts on their security posture. From there, they can focus on the most relevant and essential ISO 27001 controls based on their specific situation. This process becomes much clearer when guided by a well-prepared Statement of Applicability, which ensures alignment with actual risks.
The main goal of the ISO 27001 domains and controls is to create a tailored Information Security Management System (ISMS) that fits the business’s needs. This means companies can apply ISO 27001 controls that match their risk level, size, complexity, and industry. Thus, compliance with ISO 27001 domains and controls strengthens an organization’s overall cybersecurity posture. Creating a strong Statement of Applicability is a key step in demonstrating that security choices are thoughtful, relevant, and based on real threats.
WHAT IS A STATEMENT OF APPLICABILITY, AND WHY IS IT IMPORTANT?
The Statement of Applicability (SoA) is an important document in ISO 27001 domains and controls. It provides all the Annex A controls and shows which ones the organization has selected or excluded and the reason for such a decision. In simple words, the SoA explains what security measures the company uses and why.
In the ISO 27001 framework, the SoA connects the risk treatment plan to Annex A controls. Also, it shows how the company chooses controls based on its risks and business needs.
The SoA includes a full list of Annex A controls. To clarify, it delivers notes on which controls are included or excluded. Furthermore, it explains the rationale behind the inclusion or exclusion of each control. It also presents the current status of each control, regardless of its implementation, planning, or lack thereof.
Role of SoA in Information Security:
- It aligns controls with real business risks.
- It shows transparency and decision-making.
- Auditors and stakeholders can use it as proof of compliance.
- It supports internal planning and future audits.
SoA and ISO 27001 Domains and Controls Gap Analysis:
- Controls that are missing or not strong enough.
- Gaps between current practices and ISO 27001 requirements.
- Areas that need quick attention and fixes.
For example, a company finds control A.12.6.1 missing in its SoA, so it updates its risk plan to fix the technical vulnerability gap.
Best practices for maintaining your SOA include updating the SoA when your company changes systems or teams. And review it after any risk assessment or security event. More importantly, keep it ready and accessible for audits and internal reviews. Understanding how many controls in ISO 27001 are mandatory can guide you in creating a tailored Statement of Applicability.
CERTPRO: THE LEADING ISO 27001:2022 AUDITOR
ISO 27001 domains and controls help businesses build and maintain robust information security systems. Furthermore, the ISO 27001:2022 update reduced the number of controls from 114 in the 2013 version to 93 across 4 main domains. Consequently, companies aiming for a strong security posture should adopt the updated 2022 standard, with a transition deadline of October 31, 2025, as set by the certification bodies.
In simple words, getting certified to ISO 27001 shows a company’s dedication to protecting information and following the best practices. Additionally, to achieve certification, companies must demonstrate compliance with all the necessary ISO 27001 controls through proper ISO 27001 documentation and audits. By implementing the right ISO 27001 domains and controls that align with their risk profile, businesses can lower security risks, protect sensitive information, and stay compliant with regulations.
If your company needs help, CertPro, a trusted audit partner, can guide you through the process of becoming ISO 27001 certified. With our expertise in ISO 27001:2022 and information security systems, we can help businesses set up the right ISO 27001 controls, perform risk assessments, and achieve certification.
In addition, CertPro’s expert audit team assists you in understanding nuances and overcoming the complexities of this process. Our standardized audits are well-equipped with compliance automation tools to provide you with faster audits. What makes CertPro’s compliance services unique is that we never compromise on the standards. And our auditors possess profound knowledge of ISO 27001 domains and controls, leaving no place for errors or inconsistencies. Thus, we ensure that our audit services and compliance strategy bolster your reputation. Also helping you find out how many controls in ISO 27001 apply to your industry and business size. Connect with us today to begin your journey toward compliance and business growth.
FAQ
What are domains and controls in ISO 27001 2022?
How many control objectives are in ISO 27001 2022?
- ISO 27001:2022 no longer separates control objectives distinctly. Instead, it includes 93 controls organized into 4 themes: Organizational, People, Physical, and Technological. Each control supports the overall information security objective.
What are the differences between ISO 27001 2013 and 2022?
What is Annex A controls of ISO 27001:2022?
What are the pillars of ISO 27001?

About the Author
ANUPAM SAHA
Anupam Saha, an accomplished Audit Team Leader, possesses expertise in implementing and managing standards across diverse domains. Serving as an ISO 27001 Lead Auditor, Anupam spearheads the establishment and optimization of robust information security frameworks.
IS SOC 2 THE SAME AS ISO 27001?
In today's digital landscape, ensuring the safeguarding of client data is paramount for businesses. Adhering to recognized compliance standards is vital to meeting this demand. ISO 27001 vs. SOC 2 represent two prominent benchmarks in the realm of data security with...
WHO NEEDS ISO 27001 CERTIFICATION AND WHY?
The esteemed ISO 27001 security framework is designed to evaluate the effectiveness of an organization's Information Security Management System (ISMS) in safeguarding its data. Obtaining ISO 27001 certification is a practical way for a corporation to demonstrate its...
IS ISO 27001 RISK ASSESSMENT VITAL FOR SECURITY MEASURES?
The ISO 27001 standard provides a framework for information security, highlighting the importance of a thorough risk assessment procedure. Organizations use the methodical and complex ISO 27001 risk assessment process to identify and assess information security...





