SOC 2 Certification in Cebu
SOC 2 Certification in Cebu represents a formal attestation issued by a Licensed CPA Firm confirming that a service organization’s information security controls meet the requirements established by the American Institute of Certified Public Accountants (AICPA) Trust Services Criteria. This certification is not a product or software standard — it is an audit-based attestation that evaluates how an organization manages, protects, and governs customer data across five defined criteria categories: Security, Availability, Processing Integrity, Confidentiality, and Privacy.
OUR CLIENTS










Introduction to SOC 2 Certification
SOC 2 Certification in Cebu represents a formal attestation issued by a Licensed CPA Firm confirming that a service organization’s information security controls meet the requirements established by the American Institute of Certified Public Accountants (AICPA) Trust Services Criteria. This certification is not a product or software standard — it is an audit-based attestation that evaluates how an organization manages, protects, and governs customer data across five defined criteria categories: Security, Availability, Processing Integrity, Confidentiality, and Privacy.
The SOC 2 framework was developed by the AICPA in response to growing demand for independent verification of data security practices among service organizations — particularly those providing cloud-based, SaaS, IT-managed, and data processing services to enterprise clients. Unlike prescriptive compliance standards, SOC 2 evaluates controls against a principles-based Trust Services Criteria (TSC) framework. This means organizations must demonstrate that their actual operational controls achieve specific control objectives rather than simply following a checklist. This flexibility makes SOC 2 compliance relevant across a wide range of industries and organizational sizes.
What SOC 2 Certification Means for Service Organizations
SOC 2 Certification in Cebu signifies that an independent Licensed CPA Firm has examined and attested to the design and operating effectiveness of a service organization’s internal controls as they relate to data security and the Trust Services Criteria. For Cebu-based organizations, achieving SOC 2 attestation communicates to clients, partners, and regulators that their data handling practices have been independently verified against internationally recognized standards. This is particularly relevant for organizations that store, process, or transmit sensitive client data on behalf of enterprise customers in the United States, United Kingdom, European Union, or other regulated markets.
SOC 2 differs fundamentally from internal self-assessments or vendor questionnaires. A SOC 2 audit is conducted by an external CPA firm with the authority to issue a formal attestation report — a document that carries legal and professional weight in vendor due diligence, contract negotiations, and regulatory compliance contexts. Organizations in Cebu that undergo a SOC 2 audit receive a report that details the scope of controls tested, the criteria applied, the testing procedures performed, and the auditor’s conclusions regarding control effectiveness. This report becomes a critical asset for business development, client retention, and regulatory alignment.
SOC 2 vs. SOC 1 and SOC 3: Key Distinctions
The AICPA issues three types of System and Organization Controls (SOC) reports, each serving distinct purposes. SOC 1 reports evaluate internal controls over financial reporting (ICFR) and are relevant for service organizations whose services directly affect a client’s financial statements — such as payroll processors or financial data management firms. SOC 2 compliance, by contrast, evaluates controls related to data security, availability, and privacy under the Trust Services Criteria, making it appropriate for technology, cloud, and data processing service providers. SOC 3 is a publicly available summary version of the SOC 2 report, designed for general distribution without the detailed control descriptions and testing procedures contained in a full SOC 2 attestation report.
| Report Type | Focus Area | Primary Audience | Availability |
|---|---|---|---|
| SOC 1 | Internal Controls over Financial Reporting (ICFR) | Clients’ auditors and financial stakeholders | Restricted — shared under NDA |
| SOC 2 | Trust Services Criteria (Security, Availability, etc.) | Enterprise clients, regulators, procurement teams | Restricted — shared under NDA |
| SOC 3 | Summary of SOC 2 findings | General public, marketing use | Publicly available |
Origin and Authority of the SOC 2 Framework
The SOC 2 framework was formally established by the AICPA under the AT-C Section 205 attestation standard, which governs examination engagements performed by CPAs. The Trust Services Criteria used to evaluate controls were developed collaboratively by the AICPA and the Canadian Institute of Chartered Accountants (CICA) and have been periodically updated to reflect evolving information security risks and technologies. The most current version of the TSC — updated in 2017 and amended subsequently — incorporates a Common Criteria (CC) framework aligned with the Committee of Sponsoring Organizations of the Treadway Commission (COSO) internal control framework. This alignment ensures that SOC 2 evaluations remain grounded in established governance and risk management principles.
Because SOC 2 is an AICPA-governed attestation standard, only Licensed CPA Firms — specifically those with attestation authority — are qualified to issue SOC 2 reports. This distinguishes SOC 2 from other cybersecurity frameworks such as ISO 27001 or NIST CSF, which can be certified by accredited third-party certification bodies without CPA licensure requirements. CertPro’s status as a Licensed CPA Firm is therefore a prerequisite for issuing valid, authoritative SOC 2 attestation reports for organizations seeking SOC 2 Certification in Cebu.
SOC 2 Compliance for Cebu IT and BPO Organizations
Cebu has emerged as one of the Philippines’ most dynamic technology and business process outsourcing (BPO) hubs, hosting a dense concentration of IT-BPM companies, SaaS providers, fintech startups, and multinational shared services centers. This commercial landscape creates a direct operational need for SOC 2 compliance that Cebu organizations must satisfy when competing for enterprise contracts with clients headquartered in the United States, Europe, and other data-sensitive markets. Enterprise procurement teams in these regions increasingly mandate SOC 2 attestation as a baseline vendor qualification requirement before entering into data processing agreements.
The information technology and business process management (IT-BPM) sector in Cebu processes substantial volumes of sensitive client data daily — including personally identifiable information (PII), financial records, healthcare data, and proprietary business intelligence. Organizations in this sector that lack documented, independently verified security controls face increasing barriers to contract renewal and new business acquisition. SOC 2 audit engagements in Cebu conducted by CertPro directly address this risk by producing attestation reports that satisfy client due diligence requirements and support the organization’s data governance posture.
Cebu’s Technology Sector and Data Security Obligations
Cebu City and the broader Cebu metropolitan area host numerous economic zones — including the Cebu IT Park and Cebu Business Park — which collectively accommodate hundreds of technology companies, shared services centers, and BPO operators. Many of these organizations hold contracts with FTSE-listed companies, Fortune 500 corporations, and regulated financial institutions that require their service providers to maintain independently audited security controls. SOC 2 Certification in Cebu provides the formal attestation documentation required to satisfy client security questionnaires and vendor risk management programs for companies operating within these economic zones.
Cebu’s data center and cloud infrastructure landscape has expanded significantly in recent years. Colocation facilities and managed cloud service providers have established operations in the region to serve both domestic and international clients. Organizations operating cloud infrastructure, managed security services, or data hosting facilities in Cebu are among the most common candidates for SOC 2 audit services, as their clients require independent verification that physical and logical security controls are in place and operating effectively. The SOC 2 attestation report directly addresses the control domains most relevant to infrastructure providers: security, availability, and confidentiality.
Regulatory Intersections: NPC, GDPR, and ICO Relevance
Cebu-based organizations that process personal data are subject to the Philippine Data Privacy Act of 2012 (Republic Act 10173), enforced by the National Privacy Commission (NPC). The NPC’s data protection requirements — including the obligation to implement appropriate organizational, physical, and technical security measures — align substantively with the Security and Privacy Trust Services Criteria evaluated during a SOC 2 audit. Organizations that have undergone SOC 2 attestation are better positioned to demonstrate NPC compliance, as the SOC 2 report provides documented evidence of control design and operating effectiveness that regulators can review.
Cebu companies providing services to clients in the European Union must also address General Data Protection Regulation (GDPR) obligations — particularly those relating to data processor accountability, technical and organizational measures (Article 32), and the ability to demonstrate compliance upon request. While SOC 2 attestation is not a GDPR certification per se, the SOC 2 report — particularly when the Privacy Trust Services Criterion is included in scope — provides substantial evidentiary support for GDPR Article 32 compliance. Similarly, organizations handling data of UK residents may need to satisfy Information Commissioner’s Office (ICO) expectations, for which SOC 2 attestation serves as a recognized indicator of robust data security governance.
SOC 2 Certification for Cebu Fintech and SaaS Companies
SOC 2 compliance for Cebu fintech organizations is driven by the nature of financial data they process and the regulatory expectations of their enterprise clients. Fintech companies in Cebu that provide payment processing, lending technology, or financial analytics services to banks, credit unions, and investment firms in regulated markets must demonstrate that their security controls meet independently verified standards. A SOC 2 Type 2 report provides the time-tested control evidence that financial institution clients and their regulators require before entering into third-party service agreements. SOC 2 Certification in Cebu similarly gives IT services providers a differentiating credential in competitive RFP processes, directly supporting business growth and client retention.
SOC 2 vs. Other Certifications: Key Distinctions
SOC 2 attestation occupies a distinct position among data security and information management frameworks. Understanding how SOC 2 differs from other commonly referenced standards — including ISO 27001, PCI DSS, HIPAA, and FedRAMP — is essential for Cebu-based organizations determining which certification or attestation best fits their business model and client requirements. Each framework addresses overlapping but distinct compliance domains, and in many cases organizations pursue multiple certifications to satisfy the full range of client and regulatory expectations. SOC2 Certification remains the preferred standard for US-facing service organizations.
SOC 2 vs. ISO 27001
SOC 2 and ISO 27001 are both information security frameworks that evaluate an organization’s controls, but they differ in their governing bodies, assessment methodology, and the nature of the resulting credential. ISO 27001 is an international standard published by the International Organization for Standardization (ISO) and certified by accredited certification bodies under the ISO/IEC 17021 accreditation standard. SOC 2, by contrast, is governed by the AICPA and can only be attested by Licensed CPA Firms. ISO 27001 certification confirms that an organization’s Information Security Management System (ISMS) conforms to the standard, while SOC 2 attestation provides a detailed auditor’s report on the operating effectiveness of specific controls against the Trust Services Criteria.
From a market acceptance perspective, SOC 2 is the dominant data security attestation standard required by US-headquartered enterprise clients — particularly in the technology, financial services, and healthcare sectors. ISO 27001, while broadly accepted internationally, is more commonly required by European and Asia-Pacific clients. Cebu-based organizations serving US enterprise clients — particularly those in SaaS, IT-BPM, and cloud services — typically prioritize SOC 2 Certification in Cebu as their primary credential. Organizations with significant European client bases may pursue both ISO 27001 and SOC 2 attestation to address the full spectrum of client requirements.
SOC 2 vs. PCI DSS and HIPAA
PCI DSS (Payment Card Industry Data Security Standard) and HIPAA (Health Insurance Portability and Accountability Act) are prescriptive, sector-specific compliance frameworks that mandate specific security controls for organizations handling payment card data and protected health information (PHI), respectively. SOC 2 audit engagements in Cebu, by contrast, are not sector-specific and apply principles-based criteria that allow organizations to define the scope of controls evaluated. Organizations subject to PCI DSS or HIPAA may also pursue SOC 2 attestation to provide clients with a broader, independently verified view of their overall security posture. In many cases, SOC 2 audit evidence overlaps substantially with PCI DSS and HIPAA compliance documentation, making combined compliance programs operationally efficient.
SOC 2 Type 1 vs. SOC 2 Type 2: Critical Differences
The distinction between SOC 2 Type 1 and SOC 2 Type 2 is one of the most important concepts for Cebu organizations evaluating their certification pathway. SOC 2 Type 1 engagements in Cebu evaluate the design and implementation of controls at a specific point in time. The Type 1 report attests that the organization’s controls are suitably designed to meet the applicable Trust Services Criteria as of a defined date — but does not evaluate whether those controls operated effectively over an extended period. A Type 1 report is typically pursued by organizations new to SOC 2 that wish to establish a documented baseline of control design before undertaking a more comprehensive Type 2 engagement.
SOC 2 Type 2 engagements in Cebu evaluate both the design of controls and their operating effectiveness over a defined audit period — typically six to twelve months. The Type 2 report provides the most comprehensive level of SOC 2 assurance and is the report most commonly required by enterprise clients in the United States and other regulated markets. Because Type 2 reports demonstrate that controls functioned consistently over time rather than merely existing on paper, they carry significantly greater evidentiary weight in vendor due diligence contexts. Most Cebu-based organizations ultimately pursue SOC 2 Type 2 certification as their target credential, with a Type 1 engagement serving as an interim milestone.
| Dimension | SOC 2 Type 1 | SOC 2 Type 2 |
|---|---|---|
| Evaluation Scope | Control design at a point in time | Control design and operating effectiveness over a period |
| Audit Period | Single date | Typically 6–12 months |
| Report Weight | Moderate — establishes baseline | High — demonstrates sustained control operation |
| Common Use Case | First SOC 2 report, early-stage organizations | Ongoing enterprise client requirements |
| Renewal Frequency | As needed for updates | Annual or biennial re-audit |
Industries That Require SOC 2 Certification in Cebu
SOC 2 Certification in Cebu is relevant across multiple industries and business models. The common thread is the processing, storage, or transmission of sensitive client data on behalf of enterprise customers. The following sectors represent the primary industries in Cebu’s business landscape that require or commonly pursue SOC 2 attestation to meet client expectations, regulatory obligations, or contractual requirements.
Business Process Outsourcing and IT-BPM
SOC 2 certification that Cebu BPO companies pursue is driven by the volume and sensitivity of data processed on behalf of their offshore clients. BPO organizations in Cebu routinely handle customer records, financial transactions, healthcare information, and proprietary business data for clients in the United States, United Kingdom, Australia, and other regulated markets. These clients — particularly those in regulated industries such as financial services and healthcare — are increasingly required by their own regulators and auditors to verify that third-party service providers maintain independently attested security controls. A SOC 2 Type 2 report produced by CertPro satisfies this client obligation and reduces the administrative burden of responding to security questionnaires on a client-by-client basis.
The IT-BPM sector in Cebu encompasses a broad range of service models — including customer support, back-office processing, software development outsourcing, and knowledge process outsourcing (KPO) — all of which involve access to client systems, data repositories, and internal business processes. As enterprise clients apply greater scrutiny to their supply chains and third-party risk exposure, demonstrating SOC 2 compliance becomes a competitive differentiator and a prerequisite for contract qualification in many procurement processes for Cebu IT-BPM organizations.
SaaS, Cloud, and Technology Service Providers
Software-as-a-Service (SaaS) providers and cloud infrastructure companies based in Cebu are among the most frequent participants in SOC 2 audit engagements. These organizations host client applications, databases, and data processing workflows in environments where the security, availability, and confidentiality of client data are central service commitments. Enterprise SaaS clients — particularly those in financial services, legal, healthcare, and government contracting — routinely request SOC 2 Type 2 reports as part of vendor onboarding and annual vendor review processes. Cebu-based SaaS companies that have obtained SOC 2 attestation are better positioned to close enterprise contracts and reduce the risk of client attrition due to perceived security deficiencies.
Financial Services and Fintech Organizations
The fintech sector in Cebu — encompassing payment processors, lending platforms, digital banking service providers, and financial data analytics firms — operates under elevated data security scrutiny due to the financial sensitivity of the data processed. SOC 2 compliance demonstrated by Cebu fintech organizations is typically evaluated against the Security and Confidentiality Trust Services Criteria, with Availability included for organizations providing mission-critical financial processing services. Banks, investment firms, and regulated financial institutions that contract with Cebu-based fintech providers require SOC 2 attestation as a standard due diligence requirement — and in some cases as a contractual obligation under their own regulatory frameworks.
Healthcare, Legal, and Other Data-Sensitive Sectors
Healthcare technology companies, medical billing organizations, legal process outsourcing (LPO) firms, and human resources technology providers in Cebu also represent significant candidates for SOC 2 Certification in Cebu. Healthcare-related organizations processing protected health information on behalf of US-based healthcare providers may be subject to HIPAA Business Associate Agreement obligations, and SOC 2 attestation serves as evidence of the technical and organizational safeguards required under HIPAA. Legal process outsourcing firms handling privileged client communications and case records face similar data sensitivity obligations from their law firm and corporate legal department clients.
- ✓Business Process Outsourcing (BPO) and IT-BPM organizations processing client data
- ✓SaaS and cloud service providers hosting enterprise applications and data
- ✓Fintech companies providing payment processing, lending, and financial analytics services
- ✓Data center and managed hosting providers in Cebu’s infrastructure sector
- ✓Healthcare technology and medical billing organizations handling PHI
- ✓Legal process outsourcing firms managing privileged client communications
- ✓Human resources and payroll technology providers processing employee data
- ✓Managed security service providers (MSSPs) offering security monitoring and response
- ✓E-commerce platforms and digital marketplace operators handling transaction data
- ✓Government technology contractors subject to public sector data security requirements
Trust Services Criteria: A Detailed Breakdown
The Trust Services Criteria (TSC) form the evaluative framework against which SOC 2 controls are assessed during a SOC 2 audit. Developed by the AICPA, the TSC consists of five categories — Security, Availability, Processing Integrity, Confidentiality, and Privacy — each containing specific points of focus that define the expected outcomes of an organization’s internal control environment. Security is the only criterion that is mandatory in every SOC 2 engagement. The remaining four criteria are included based on the nature of the service organization’s commitments to its clients and the relevance of each criterion to its service model. Selecting the right criteria is a critical step in structuring an effective SOC 2 compliance program.
The Security criterion — also known as the Common Criteria (CC) — is the foundational element of every SOC 2 audit and must be included in all SOC 2 engagements regardless of scope. The Common Criteria evaluate controls related to logical and physical access, change management, risk assessment, monitoring of controls, and incident response. These criteria are organized into nine CC categories: CC1 (Control Environment), CC2 (Communication and Information), CC3 (Risk Assessment), CC4 (Monitoring Activities), CC5 (Control Activities), CC6 (Logical and Physical Access Controls), CC7 (System Operations), CC8 (Change Management), and CC9 (Risk Mitigation). Each category contains multiple points of focus specifying the expected behaviors and outcomes an organization’s controls must achieve.
During a SOC 2 audit engagement in Cebu, the Licensed CPA Firm evaluates whether the organization’s controls across all applicable Common Criteria categories are suitably designed (for Type 1) and operating effectively (for Type 2). Control testing under the Security criterion typically involves examination of access control configurations, review of change management records, testing of logical access provisioning and de-provisioning processes, evaluation of security monitoring systems, and assessment of incident response procedures. The depth and rigor of this testing is one of the primary factors that distinguishes a credible SOC 2 attestation report from a superficial one.
The Availability criterion evaluates controls that ensure system resources are available for operation and use as committed or agreed upon in service level agreements. For Cebu-based cloud providers, data centers, and SaaS organizations, Availability is a particularly relevant criterion because service uptime and resilience directly affect client operations. Controls evaluated under this criterion include infrastructure redundancy, disaster recovery planning, backup procedures, capacity management, and environmental protections. Organizations that include Availability in their SOC 2 scope must demonstrate that uptime commitments are supported by documented and tested operational controls.
Processing Integrity evaluates whether system processing is complete, valid, accurate, timely, and authorized — criteria directly relevant to organizations providing transaction processing, data transformation, or financial calculation services. Confidentiality evaluates controls that protect information designated as confidential under service agreements, such as trade secrets, proprietary business data, and non-public financial information. Organizations that commit to keeping client data confidential — as most BPO and managed services providers do — typically include the Confidentiality criterion in their SOC 2 scope. Privacy, the fifth and most complex criterion, evaluates the collection, use, retention, disclosure, and disposal of personal information in accordance with defined privacy commitments and applicable legal requirements, including those under GDPR and the Philippine Data Privacy Act.
The scope of Trust Services Criteria included in a SOC 2 audit is determined by the nature of the service organization’s commitments to its user entities, as documented in system descriptions and service contracts. CertPro evaluates the organization’s System Description — a formal document describing the boundaries of the system under audit, the nature of services provided, and the controls in place — to determine which criteria are applicable and relevant. Selecting an inappropriate scope — either too narrow to satisfy client requirements or too broad to be supported by existing controls — can compromise the utility of the resulting SOC 2 attestation report and undermine the organization’s SOC 2 compliance posture.

- ✓Security: The Common Criteria Framework
- ✓Availability, Processing Integrity, and Confidentiality Criteria
- ✓Defining Scope: Selecting the Right Trust Services Criteria
Evidence Collection and Audit Preparation
SOC 2 audit preparation involves the systematic assembly of evidence demonstrating that the organization’s controls are designed and — for Type 2 engagements — operating effectively across the audit period. Evidence collection is one of the most operationally intensive phases of any SOC 2 engagement, requiring coordination across IT, security, HR, legal, and operations teams to produce documented artifacts corresponding to each control point under examination. Thorough preparation directly influences both audit efficiency and the quality of the resulting SOC 2 attestation report.
Documentation and Policy Requirements
The documentation reviewed during a SOC 2 audit in Cebu includes information security policies, access control procedures, change management records, vendor management policies, business continuity and disaster recovery plans, employee training records, incident response playbooks, and system configuration documentation. Each policy and procedure must be formally approved, version-controlled, and demonstrably implemented — not merely drafted. The Licensed CPA Firm auditing the organization examines documentation to verify that policies address all applicable control objectives and that documented procedures correspond to actual operational practices observed during the audit.
For SOC 2 Type 2 engagements, documentation must also include operational records — such as access review logs, change management tickets, vulnerability scan reports, penetration test results, and incident response records — that demonstrate the consistent execution of controls throughout the audit period. The completeness and quality of these operational records is a critical determinant of audit outcomes. Gaps in documentation may result in exceptions noted in the SOC 2 report, which can affect the report’s utility in client due diligence contexts.
Technical Evidence and System Configuration Review
Technical evidence collected during a SOC 2 audit includes configuration exports from identity and access management (IAM) systems, firewall and network security configurations, encryption key management records, multi-factor authentication (MFA) enrollment reports, endpoint detection and response (EDR) system logs, cloud security configuration baselines, and data backup verification records. The Licensed CPA Firm examines this technical evidence to assess whether the organization’s system configurations align with the controls described in its System Description and whether those configurations meet the applicable Trust Services Criteria requirements.
Cloud-native organizations operating in Cebu’s technology sector commonly use platforms such as AWS, Microsoft Azure, or Google Cloud Platform as the foundation of their production environments. During the SOC 2 audit, CertPro examines cloud security configurations — including IAM policies, S3 bucket access controls, VPC network segmentation, logging and monitoring configurations, and encryption settings — to evaluate compliance with the applicable Common Criteria. The organization’s use of infrastructure-as-code (IaC) tools and automated configuration management systems is also evaluated to determine whether security configurations are consistently applied and protected against unauthorized modification.
People Controls and Organizational Evidence
SOC 2 compliance is not limited to technical controls — the organizational and people dimensions of security are equally important in the audit evaluation. Evidence related to people controls includes background check records for employees with access to sensitive systems, security awareness training completion records, job descriptions that define security responsibilities, performance management records reflecting security accountability, and separation of duties documentation. For SOC 2 certification for Cebu BPO companies with large workforces, the consistency and completeness of HR-related security controls across the employee population is a frequently examined area during audit fieldwork.
Certification and Auditing Services for SOC 2 in Cebu
CertPro conducts SOC 2 audits in Cebu as a Licensed CPA Firm operating under AICPA attestation standards. The firm’s audit engagement process is structured to evaluate the design and operating effectiveness of service organization controls against the applicable Trust Services Criteria, culminating in the issuance of a formal SOC 2 attestation report. The following sections describe each stage of the SOC 2 audit process as conducted by CertPro for Cebu-based service organizations.
Stage 1: Scope Definition and System Description Review
The first stage of the SOC 2 audit process involves defining the scope of the engagement — specifically, the systems, services, infrastructure, and organizational boundaries that will be evaluated. CertPro reviews the organization’s System Description, which formally defines the nature of the services provided, the system components in scope, and the controls in place. The System Description must be accurate, complete, and consistent with the organization’s actual operational environment. The Licensed CPA Firm evaluates the System Description for completeness and identifies any discrepancies between the described system and the observed operational environment before proceeding to control testing.
Stage 2: Audit Program Determination and Planning
Following scope definition, CertPro determines the audit program — the specific procedures and tests that will be applied to evaluate each control against the applicable Trust Services Criteria. The audit program is tailored to the organization’s specific control environment, system architecture, and the criteria in scope. For SOC 2 Type 2 engagements, the audit program also specifies the sampling methodology applied to operational records across the audit period, ensuring that evidence of control operation is evaluated consistently and in sufficient volume to support the auditor’s conclusions.
Stage 3: Control Testing and Evidence Examination
Control testing is the core fieldwork phase of the SOC 2 audit, during which CertPro’s auditors examine evidence collected by the service organization and perform independent testing procedures to assess control design and operating effectiveness. Testing methods include inquiry (interviews with personnel responsible for control execution), observation (direct examination of system configurations and processes), inspection (review of documentation and records), and re-performance (independent execution of a control procedure to verify the outcome). Combining multiple testing methods for each control point strengthens the evidentiary basis for the auditor’s conclusions and reduces the risk of relying on a single evidence source.
Stage 4: Nonconformity Review and Management Response
When control testing identifies deviations from the applicable Trust Services Criteria — referred to as exceptions in the SOC 2 framework — CertPro’s auditors document the nature, extent, and potential impact of each exception. The organization’s management is then provided an opportunity to review identified exceptions and provide a formal management response, which is included in the SOC 2 report alongside the auditor’s findings. The presence of exceptions does not automatically invalidate a SOC 2 report. Rather, the nature and severity of exceptions — combined with management’s response and any remediation actions — are factors that report users evaluate when assessing the organization’s overall control environment.
Stage 5: Attestation Report Issuance and Distribution
Upon completion of control testing, nonconformity review, and management response, CertPro issues the formal SOC 2 attestation report. The report includes the Licensed CPA Firm’s opinion on whether the service organization’s controls are suitably designed (Type 1) or suitably designed and operating effectively (Type 2) over the audit period. The report also contains the organization’s System Description, management’s assertion regarding the effectiveness of controls, and the detailed results of CertPro’s testing procedures. SOC 2 attestation reports are confidential documents shared by the service organization with its clients and other authorized report users under appropriate non-disclosure arrangements.
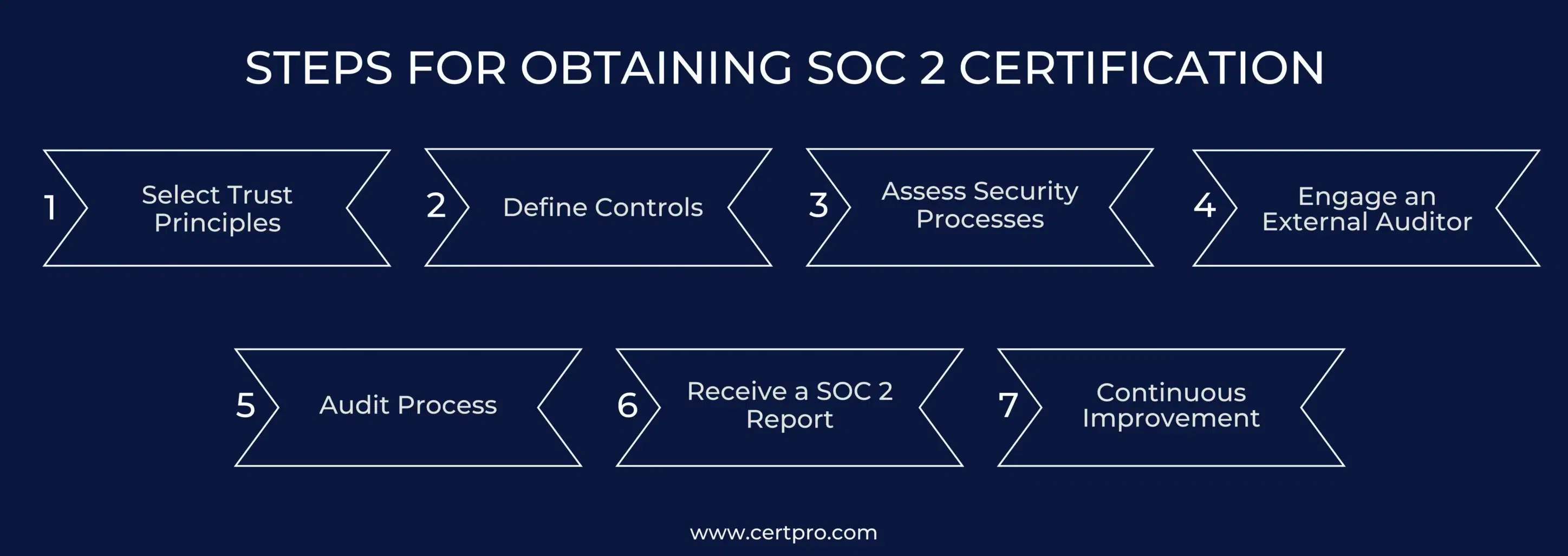
- Scope Definition: Identify systems, services, and organizational boundaries in scope for the SOC 2 engagement
- Audit Program Determination: Develop a tailored audit program based on the applicable Trust Services Criteria and organizational control environment
- Stage 1 Assessment: Review System Description and verify alignment with actual operational environment
- Type 1 or Type 2 Assessment: Conduct control design evaluation (Type 1) or design and operating effectiveness evaluation (Type 2)
- Control Testing: Execute inquiry, observation, inspection, and re-performance procedures across all in-scope controls
- Nonconformity Review: Document exceptions, assess severity, and obtain management response
- Certification Decision: CertPro’s Licensed CPA Firm renders its attestation opinion based on audit findings
- Issuance of Attestation Report: Deliver the formal SOC 2 attestation report including System Description, management assertion, and auditor opinion
- Surveillance and Recertification: For ongoing SOC 2 compliance, plan subsequent Type 2 audit engagements to maintain current attestation status
Benefits of SOC 2 Certification for Cebu Organizations
SOC 2 Certification in Cebu delivers measurable business and operational benefits to service organizations across the technology, BPO, fintech, and cloud services sectors. These benefits extend beyond the immediate credential itself to encompass improved internal governance, enhanced client relationships, competitive market positioning, and regulatory alignment. The following subsections detail the primary categories of benefit associated with SOC 2 attestation for Cebu-based organizations.
SOC 2 attestation provides Cebu-based organizations with a documented, independently verified security credential that differentiates them from competitors lacking formal attestation. In enterprise sales processes — particularly for contracts with US, UK, and European clients — security questionnaires and vendor risk management (VRM) reviews have become standard components of procurement. Organizations holding a current SOC 2 Type 2 report can respond to security questionnaires by referencing their attestation report, reducing the time and resources required to complete due diligence and accelerating contract closure timelines. For Cebu IT services providers competing for large-scale outsourcing contracts, this competitive positioning translates directly into increased win rates and contract values.
The market access benefits of SOC 2 attestation are particularly significant for Cebu organizations targeting clients in the United States financial services sector. Third-party risk management frameworks — including those derived from OCC Bulletin 2013-29, FFIEC guidance, and SOC requirements under SSAE 18 — create explicit expectations for independent attestation. Organizations without current SOC 2 attestation may be disqualified from regulated financial sector procurement processes regardless of their technical capabilities or pricing competitiveness.
Enterprise clients are increasingly subject to their own regulatory obligations requiring them to manage and monitor the security practices of their third-party service providers. SOC 2 attestation directly addresses this client-side obligation by providing an independent, professionally issued report that client procurement teams, internal audit functions, and compliance officers can review as part of their third-party risk management programs. For Cebu-based organizations, holding a current SOC 2 attestation reduces the audit burden placed on them by individual clients — replacing multiple ad-hoc security assessments with a single, comprehensive attestation report that can be shared across the client portfolio.
The process of undergoing a SOC 2 audit produces internal governance benefits beyond the attestation report itself. Organizations that implement the controls necessary to meet Trust Services Criteria standards develop more mature and disciplined information security management practices — including formalized access control processes, systematic change management, structured incident response capabilities, and documented risk assessment programs. These improvements reduce exposure to data breaches, system outages, and operational failures. For Cebu-based BPO and IT-BPM organizations handling client data under contractual confidentiality obligations, the internal control improvements associated with SOC 2 compliance directly reduce the probability of contractual breaches and associated liability.
- ✓Accelerated vendor qualification in enterprise procurement processes through independently attested security credentials
- ✓Reduced administrative burden from client security questionnaires via referenceable SOC 2 attestation reports
- ✓Enhanced market access to US, UK, and EU enterprise clients with mandatory third-party attestation requirements
- ✓Demonstrated regulatory alignment with Philippine Data Privacy Act, GDPR, and HIPAA requirements
- ✓Strengthened internal information security governance across access, change, and incident management processes
- ✓Reduced risk of data breaches and associated financial, legal, and reputational consequences
- ✓Improved employee security awareness and accountability through control implementation and monitoring
- ✓Competitive differentiation in RFP processes for regulated industry contracts in financial services and healthcare
- ✓Foundation for additional compliance certifications such as ISO 27001 through overlapping control evidence
- ✓Ongoing assurance to existing clients supporting contract renewal and relationship continuity

- ✓Competitive Advantage in Enterprise Sales Processes
- ✓Client Trust and Third-Party Risk Management
- ✓Internal Control Improvement and Risk Reduction
SOC 2 Report Structure and Components
Understanding the structure and components of a SOC 2 attestation report is important for Cebu-based organizations that will be distributing their report to clients and other authorized users. A SOC 2 report is a multi-section document that provides a comprehensive account of the audit engagement — including the scope, methodology, findings, and the Licensed CPA Firm’s attestation opinion. The content and format of SOC 2 reports are governed by AICPA guidance and are consistent across all engagements, enabling report users to efficiently locate and interpret key information.
Key Sections of a SOC 2 Attestation Report
A SOC 2 report issued by CertPro following a SOC 2 audit engagement in Cebu contains several standard sections: (1) the Independent Service Auditor’s Report, which presents the Licensed CPA Firm’s attestation opinion; (2) Management’s Assertion, in which service organization management asserts that the System Description is accurate and that controls are suitably designed and — for Type 2 — operating effectively; (3) the System Description, which describes the service organization’s system, services, infrastructure, software, personnel, and controls; (4) the Description of Tests of Controls and Results, which details the testing procedures performed and results for each control (Type 2 only); and (5) Other Information provided by management that is not covered by the auditor’s opinion.
The Independent Service Auditor’s Report is the most critical component of the SOC 2 attestation for report users. This section contains the auditor’s opinion — which may be unqualified (clean), qualified, adverse, or disclaimed — regarding the fairness of the System Description and the suitability of control design and operating effectiveness. An unqualified opinion indicates that, in the auditor’s professional judgment, the System Description is fairly presented and that controls are suitably designed and operating effectively without material deviations. The presence of exceptions in the Description of Tests does not necessarily result in a qualified opinion; materiality and pervasiveness of exceptions are key factors in the auditor’s determination.
How Clients Use SOC 2 Reports
Client organizations — referred to as user entities in AICPA terminology — use SOC 2 reports as an input to their own internal control assessments and third-party risk management programs. User entities review the System Description to understand the scope of controls in place at the service organization, examine the Description of Tests to identify any exceptions, and read the auditor’s opinion to form a view on the overall control environment. In regulated industries, user entities may be required to document their review of service provider SOC 2 reports as part of their own compliance obligations — for example, under FFIEC guidance for financial institutions or SOX requirements for public companies. Annual renewal of SOC 2 attestation is therefore important for maintaining client confidence and satisfying ongoing due diligence requirements.
Ongoing SOC 2 Compliance and Surveillance Considerations
SOC 2 attestation is not a one-time certification — it requires ongoing operational commitment and periodic re-audit to maintain currency. Unlike some certification standards that issue credentials valid for a fixed multi-year period, SOC 2 Type 2 reports cover a specific audit period (typically six to twelve months) and must be renewed through subsequent audit engagements to remain current. Organizations that allow their SOC 2 attestation to lapse — or that fail to obtain a new report covering the most recent audit period — may face client requests for explanations, delays in contract renewal, or disqualification from new business opportunities. Sustaining SOC 2 compliance is therefore as important as achieving it initially.
Annual Re-Audit and Report Renewal
Most Cebu-based organizations that maintain SOC 2 attestation operate on an annual audit cycle, with each Type 2 report covering a twelve-month period. CertPro conducts annual re-audit engagements that re-evaluate the organization’s controls against the applicable Trust Services Criteria for the current audit period. These annual engagements provide an opportunity to update the System Description to reflect changes in the organization’s system architecture, service offerings, or control environment — and to address any exceptions identified in prior periods. Consistent annual SOC 2 compliance builds a track record of control maturity that enhances the credibility of the attestation in client due diligence contexts.
Managing Control Changes Between Audits
Organizations undergoing SOC 2 Type 2 audits must maintain consistent control operation throughout the audit period — not only during audit fieldwork. Significant changes to the system environment, access control configurations, key personnel, or organizational structure during the audit period must be documented, assessed for control impact, and disclosed in the System Description and management’s assertion. CertPro evaluates the completeness and accuracy of disclosures related to significant control changes when issuing the SOC 2 attestation report. Undisclosed material changes to the control environment could constitute a misrepresentation in management’s assertion, with potential professional and legal consequences.
Subservice Organizations and Complementary User Entity Controls
Many Cebu-based service organizations rely on third-party subservice providers — such as cloud infrastructure providers (AWS, Azure, GCP), colocation data centers, or managed security service providers — as part of their overall system architecture. The SOC 2 attestation report must address the role of subservice organizations and specify whether their controls are included within scope (the inclusive method) or excluded with complementary subservice organization controls (CSCs) identified (the carve-out method). Similarly, the report must identify any Complementary User Entity Controls (CUECs) — controls that user entities are expected to implement for the overall control environment to function effectively. CertPro’s audit process addresses both subservice organization and CUEC considerations as part of the System Description review and control testing procedures.
Why CertPro for SOC 2 Certification in Cebu
CertPro is a Licensed CPA Firm with audit authority under AICPA attestation standards, qualified to issue SOC 2 Type 1 and Type 2 attestation reports for service organizations operating in Cebu, Philippines. The firm’s institutional positioning as a Licensed CPA Firm — rather than a technology vendor, compliance platform, or advisory firm — reflects the legal and professional requirements governing the issuance of SOC 2 attestation reports. Only Licensed CPA Firms with the appropriate professional qualifications and independence requirements can issue valid SOC 2 reports under AICPA standards. For organizations pursuing SOC 2 Certification in Cebu, engaging a qualified CPA firm is not optional — it is a prerequisite for a valid attestation.
Licensed CPA Firm Authority and Professional Standards
CertPro’s Licensed CPA Firm status ensures that SOC 2 attestation reports issued to Cebu-based organizations carry the professional authority and institutional credibility required by enterprise clients, regulated industries, and governmental bodies. The firm operates under the AICPA’s Code of Professional Conduct and the standards established in AT-C Section 205, ensuring that audit engagements are conducted with the independence, objectivity, and professional skepticism that distinguish CPA-firm attestations from other forms of third-party security assessments. This professional framework is recognized and accepted by procurement teams, internal audit functions, and regulatory bodies in the United States and internationally as the governing standard for SOC 2 report issuance.
Local Presence and Regional Expertise in the Philippines
CertPro’s presence in the Philippines positions the firm to conduct SOC 2 audit services for Cebu-based organizations with a thorough understanding of the local business environment, regulatory landscape, and the specific control challenges faced by Cebu’s technology and BPO sectors. The firm’s auditors are familiar with the operational realities of Cebu’s IT-BPM sector — including the use of shared economic zone infrastructure, the prevalence of distributed workforce models, and the integration of cloud-based service delivery platforms — enabling more precise and contextually relevant audit evaluations than auditors lacking regional expertise.
Scope of Audit Services Across Industries and Organization Sizes
CertPro conducts SOC 2 audit engagements for Cebu-based organizations across all relevant industries and organizational sizes — from early-stage SaaS startups to established multinational BPO operations. The firm’s audit methodology is calibrated to the specific system scope, Trust Services Criteria in scope, and organizational risk profile of each engagement, ensuring that audit procedures are proportionate to the complexity of the control environment under evaluation. SOC 2 attestation reports issued by CertPro are accepted by enterprise clients and their internal audit teams in the United States, United Kingdom, European Union, Australia, and other markets where SOC 2 compliance is a recognized standard for third-party risk management.
Organizations seeking SOC 2 Certification in Cebu through CertPro engage with a Licensed CPA Firm that combines professional audit authority, regional expertise, and institutional credibility to deliver SOC 2 attestation reports that satisfy the expectations of the most demanding enterprise clients and regulatory frameworks. CertPro’s audit process is structured to provide clear, defensible, and accurate attestation of control effectiveness — the foundation upon which Cebu’s leading technology and business services organizations build their security credibility and market access strategies.
CertPro’s SOC 2 Audit Engagement Deliverables
- ✓Formal SOC 2 Type 1 or Type 2 attestation report issued under AICPA AT-C Section 205
- ✓Independent Service Auditor’s Report containing the Licensed CPA Firm’s attestation opinion
- ✓Detailed System Description reviewed and attested for accuracy and completeness
- ✓Management’s Assertion reviewed for consistency with audit findings and control environment
- ✓Description of Tests of Controls and Results (Type 2 engagements) documenting all testing procedures and outcomes
- ✓Identification of Complementary User Entity Controls (CUECs) and subservice organization considerations
- ✓Documentation of exceptions identified during control testing with management response included in report
- ✓SOC 3 report summary available for public distribution upon request
- ✓Audit engagement records maintained in accordance with AICPA professional standards for documentation retention
FAQ
▶
What is What is SOC 2 certification and why is it relevant?
▶
Question: What is SOC 2 Certification and who requires it in Cebu?
▶
Question: How long does a SOC 2 audit take for a Cebu-based organization?
▶
Question: What is the difference between SOC 2 Type 1 and Type 2 for Cebu organizations?
▶
Question: Which Trust Services Criteria should a Cebu BPO or IT company include in scope?
▶
Question: Does SOC 2 attestation satisfy GDPR and Philippine Data Privacy Act requirements?
▶
Question: How often must a Cebu organization renew its SOC 2 attestation?
▶
Question: Can a Cebu startup or small technology company obtain SOC 2 attestation?

SOC 2 CERTIFICATION IN INDIA: STRATEGIES FOR TECH SECTOR COMPLIANCE IN 2026
The AICPA developed SOC 2 certification in India as a collection of guidelines to assist IT businesses in protecting client data. With the rapid growt…

THE IMPACT OF SOC 2 CERTIFICATION ON CUSTOMER RETENTION AND ACQUISITION
The world and businesses are changing together. Now, companies have transformed into online operations and transmitted data electronically. Therefore,…
HOW SOC 2 COMPLIANCE SOFTWARE CHANGES AUDIT READINESS
There’s a version of SOC 2 preparation that most security teams know too well. The audit date is approaching. Someone sends a spreadsheet asking for a…
Get In Touch
have a question? let us get back to you.

