SOC 2 Certification in Jakarta
CertPro is a Licensed CPA Firm authorized to conduct SOC 2 attestation engagements for organizations headquartered or operating in Jakarta, Indonesia. Engagements are structured against the AICPA Trust Services Criteria, covering Security, Availability, Processing Integrity, Confidentiality, and Privacy. SOC 2 audit scope is determined based on system boundaries, organizational risk profile, and applicable data processing obligations under Indonesian regulatory frameworks.
OUR CLIENTS




What Is SOC 2 Certification?
SOC 2 Certification is a formal attestation standard developed by the American Institute of Certified Public Accountants (AICPA). It evaluates whether an organization’s information systems and internal controls meet the Trust Services Criteria (TSC) for data security, availability, processing integrity, confidentiality, and privacy. Unlike a compliance checklist, SOC 2 is an independent audit engagement conducted by a Licensed CPA Firm. The result is a detailed attestation report that describes control design and operational effectiveness over a defined review period.
SOC 2 Certification in Jakarta is increasingly recognized as a baseline requirement for technology companies, cloud service providers, SaaS platforms, financial technology firms, and data processors operating within Indonesia’s growing digital economy. As Jakarta serves as the commercial and technological center of Southeast Asia’s largest economy, organizations based in the city regularly encounter contractual requirements from international enterprise clients and institutional partners. These partners demand verified evidence of robust data security and privacy controls — making SOC 2 Certification in Jakarta an essential business credential.
The AICPA Trust Services Criteria Framework
The Trust Services Criteria (TSC) form the evaluative foundation of every SOC 2 audit. The Security criterion — also referred to as the Common Criteria — is mandatory for all SOC 2 engagements. It addresses logical and physical access controls, system monitoring, risk assessment, and incident response procedures. Additional criteria are selected based on the nature of the services an organization provides and the data it processes on behalf of clients.
The Availability criterion evaluates whether systems are operational and accessible as committed in service level agreements. Processing Integrity addresses whether system processing is complete, valid, accurate, timely, and authorized. The Confidentiality criterion covers protections applied to information designated as confidential — including encryption, access restrictions, and data disposal procedures. The Privacy criterion evaluates the organization’s handling of personal information throughout its lifecycle: collection, use, retention, disclosure, and disposal. This aligns closely with obligations under Indonesia’s Personal Data Protection (PDP) Law that Jakarta-based organizations must satisfy.
| Trust Services Criterion | Scope of Evaluation | Applicability |
|---|---|---|
| Security (Common Criteria) | Access controls, monitoring, risk management, incident response | Mandatory for all SOC 2 engagements |
| Availability | System uptime, performance, disaster recovery, business continuity | Service providers with SLA commitments |
| Processing Integrity | Completeness, accuracy, and authorization of system processing | Transaction processors, payroll, financial platforms |
| Confidentiality | Encryption, data classification, access controls for confidential data | Organizations handling sensitive client information |
| Privacy | Personal data collection, use, retention, and disposal practices | Companies subject to PDP Law and GDPR-equivalent obligations |
SOC 2 Attestation vs. Compliance: A Critical Distinction
SOC 2 attestation differs fundamentally from internal compliance declarations. SOC 2 compliance refers to an organization’s internal adherence to the Trust Services Criteria through self-assessed controls and policies — it carries no independent verification and cannot be presented as auditor-validated assurance. SOC 2 attestation, by contrast, is an external engagement performed by a Licensed CPA Firm under AICPA attestation standards. It produces a formal SOC 2 report that carries professional accountability and can be presented to enterprise clients, regulators, and business partners as verified evidence of control effectiveness.
For Jakarta-based organizations pursuing contracts with multinational enterprises, U.S.-headquartered technology companies, or regulated financial institutions, the distinction between compliance and attestation is critical. Enterprise procurement and vendor risk teams routinely require SOC 2 attestation reports — not self-declarations — before onboarding service providers that process sensitive data. Organizations that present only internal compliance documentation without an independently issued SOC 2 report frequently fail vendor qualification requirements, regardless of the quality of their actual security controls.
SOC 2 Type 1 vs. SOC 2 Type 2: Key Differences for Jakarta Organizations
SOC 2 engagements are structured as either Type 1 or Type 2 assessments, each serving a distinct purpose and suited to different organizational circumstances. Understanding which type applies to your situation is a critical early decision in the SOC 2 audit process. As a Licensed CPA Firm conducting SOC 2 audit services in Jakarta, Indonesia, CertPro evaluates organizational context, client requirements, and control maturity to determine the appropriate engagement structure for each organization.
SOC 2 Type 1 Audit: Point-in-Time Design Assessment
A SOC 2 Type 1 audit evaluates the design and implementation of an organization’s controls as of a specific date. The auditor assesses whether the controls described in the system description are suitably designed to meet the applicable Trust Services Criteria at that point in time. A SOC 2 Type 1 audit in Jakarta does not involve testing the operational effectiveness of controls over time — it confirms that the right controls exist and are logically configured to achieve their stated objectives.
The SOC 2 Type 1 audit is typically the appropriate starting point for organizations that have recently formalized their security programs, are entering the SOC 2 process for the first time, or face immediate client demands requiring documented assurance within a condensed timeframe. For Jakarta-based startups and early-stage technology firms building enterprise sales pipelines, a Type 1 report provides an initial credentialing milestone that demonstrates control design maturity — without requiring the extended observation period associated with a Type 2 engagement. Type 1 reports are generally issued within 6 to 10 weeks from the commencement of audit fieldwork.
SOC 2 Type 2 Audit: Operational Effectiveness Over Time
A SOC 2 Type 2 certification involves both the assessment of control design and the testing of operational effectiveness over a defined observation period. This period typically spans a minimum of six months and commonly extends to twelve months. During this time, the Licensed CPA Firm examines evidence that controls operated continuously and effectively — reviewing logs, exception reports, approval records, access reviews, and operational outputs to confirm that each control functioned as described throughout the audit window.
SOC 2 Type 2 certification in Jakarta represents the highest standard of SOC 2 assurance and is the format most widely demanded by enterprise clients, financial institutions, and regulated industry partners. A SOC 2 Type 2 report demonstrates not merely that controls were designed correctly at one moment, but that they operated reliably throughout an extended period — providing substantially greater assurance than a Type 1 report. Jakarta organizations in financial services, healthcare technology, cloud infrastructure, and data processing sectors typically require Type 2 attestation to satisfy the contractual and regulatory expectations of their client base.
| Characteristic | SOC 2 Type 1 | SOC 2 Type 2 |
|---|---|---|
| Assessment Focus | Control design and implementation | Control design and operational effectiveness |
| Time Period | Single point in time | Minimum 6 months (typically 12 months) |
| Audit Duration | 6–10 weeks from fieldwork commencement | 6–14 months including observation period |
| Assurance Level | Design-level assurance | Full operational assurance |
| Primary Use Case | Initial certification, new programs | Enterprise contracts, regulated industries |
Who Needs SOC 2 Certification in Jakarta?
SOC 2 Certification in Jakarta is relevant to a broad range of organizations that store, process, or transmit client data using information systems. The requirement typically originates from one of three sources: contractual demand from enterprise customers, vendor qualification requirements imposed by multinational partners, or proactive security positioning in competitive markets. Jakarta’s role as Indonesia’s primary commercial and technology hub means that organizations in the city are disproportionately exposed to international business requirements that mandate SOC 2 attestation.
Financial Technology and Banking Sector
Jakarta is home to Indonesia’s largest concentration of financial technology companies — including payment processors, digital lending platforms, wealth management applications, and cryptocurrency exchanges. SOC 2 compliance requirements for Jakarta fintech firms arise from multiple directions simultaneously: international banking partners imposing third-party risk management requirements, enterprise clients demanding security attestation before integrating payment APIs, and cross-border data transfer obligations that require demonstrated security controls. Digital payment providers, open banking platforms, and insurance technology firms operating in Jakarta frequently encounter SOC 2 Certification in Jakarta as a prerequisite for partnerships with regulated financial institutions.
SOC 2 certification engagements for Jakarta financial services organizations typically address the Security and Availability criteria as minimum scope. Many financial technology organizations also incorporate Processing Integrity to address concerns around transaction accuracy and completeness. The Confidentiality and Privacy criteria become particularly relevant for organizations handling consumer financial data subject to Bank Indonesia regulations and the Personal Data Protection Law — creating a natural alignment between SOC 2 compliance requirements and Indonesian regulatory obligations.
SaaS Platforms and Cloud Service Providers
Jakarta’s technology ecosystem includes a significant and growing cluster of Software-as-a-Service (SaaS) providers, cloud infrastructure operators, and managed service companies. These organizations frequently serve enterprise clients across multiple countries and are directly subject to vendor security questionnaire requirements that reference SOC 2 attestation. For SaaS providers, the SOC 2 report serves as a scalable mechanism for communicating security posture to hundreds or thousands of clients simultaneously — replacing individual security assessments with a single, independently verified document that satisfies enterprise vendor qualification standards.
Healthcare Technology, E-Commerce, and Data Processors
Healthcare technology companies in Jakarta that process electronic medical records, telemedicine data, or patient management information require SOC 2 attestation to satisfy both international health data standards and the privacy obligations arising from Indonesia’s PDP Law. E-commerce platforms managing large volumes of consumer personal data, transaction records, and third-party seller information similarly benefit from SOC 2 attestation as a mechanism for demonstrating data governance maturity. Data processing organizations, analytics platforms, and business process outsourcing firms that handle client data on behalf of international companies represent another major category requiring SOC 2 Certification in Jakarta.
- ✓Financial technology companies and digital payment processors
- ✓SaaS providers and cloud infrastructure operators
- ✓Healthcare technology platforms processing patient data
- ✓E-commerce organizations managing consumer personal data
- ✓Business process outsourcing and data processing firms
- ✓Managed security service providers and IT service companies
- ✓Multinational corporations with Jakarta-based data processing operations
- ✓Startups building enterprise sales pipelines requiring vendor qualification
- ✓Logistics technology platforms handling supply chain data
- ✓Insurance technology and wealth management application providers
SOC 2 Certification Requirements
SOC 2 certification requirements encompass a structured set of organizational, technical, and procedural elements that must be established and demonstrable before and during audit fieldwork. Requirements are organized around the applicable Trust Services Criteria selected for the engagement scope. CertPro’s audit program for SOC 2 Certification in Jakarta evaluates each requirement category through document review, system inspection, personnel interviews, and control testing procedures appropriate to the engagement type.
Documentation requirements for SOC 2 certification encompass formal written policies, procedures, and system descriptions that accurately reflect the organization’s security and operational environment. The system description — a narrative document prepared by management — defines the system boundaries, components, infrastructure, and data flows subject to audit evaluation. This document is critical because auditors evaluate its completeness and accuracy as a primary element of the SOC 2 report. Required documentation includes an information security policy, acceptable use policy, access control policy, incident response plan, change management procedures, vendor management policy, and business continuity and disaster recovery documentation.
Risk assessment documentation is a mandatory component of the Common Criteria. It must demonstrate that the organization has systematically identified threats and vulnerabilities relevant to its systems, assessed their likelihood and potential impact, and implemented controls to reduce risk to an acceptable level. For Jakarta-based organizations, risk assessments should account for the threat landscape relevant to Indonesian operations — including considerations specific to the regulatory environment, local infrastructure dependencies, and the geographic and jurisdictional context of data processing activities.
Technical control requirements for SOC 2 certification address the implemented mechanisms that protect systems and data against unauthorized access, modification, and disruption. Logical access controls — including multi-factor authentication, role-based access assignment, privileged access management, and regular access reviews — are among the most consistently evaluated technical requirements across all SOC 2 engagements. Encryption requirements apply to data in transit and at rest, with auditors examining the cryptographic standards implemented and the key management procedures in place to protect encryption materials.
Network security controls — including firewall configurations, intrusion detection and prevention systems, network segmentation, and vulnerability management programs — are evaluated against the Security criterion’s requirements for protecting system boundaries. Logging and monitoring capabilities must demonstrate that security-relevant events are captured, retained, and reviewed with sufficient regularity to detect and respond to anomalies. For SOC 2 audit services in Jakarta, Indonesia, auditors examine evidence of monitoring activity — including SIEM system outputs, alert review logs, and documented escalation procedures — to confirm that monitoring controls operated throughout the audit period.
Operational requirements for SOC 2 certification address the people-centered controls that form a critical layer of any effective security program. Background verification procedures for personnel with access to sensitive systems and data, security awareness training programs with documented completion records, and formal onboarding and offboarding procedures that govern access provisioning and deprovisioning are standard elements evaluated during SOC 2 audit fieldwork. Change management procedures — governing the testing, approval, and deployment of system changes — are examined to ensure that modifications to production environments are controlled and do not introduce unauthorized or untested changes.
- ✓Formal information security policy and supporting procedure documentation
- ✓System description document defining audit boundaries and data flows
- ✓Documented risk assessment process with identified threats and mitigating controls
- ✓Multi-factor authentication and role-based logical access controls
- ✓Encryption of data in transit and at rest with documented key management
- ✓Vulnerability management program with evidence of regular scanning and remediation
- ✓Security incident response plan with documented testing and activation records
- ✓Business continuity and disaster recovery documentation with tested recovery procedures
- ✓Vendor and third-party risk management procedures for critical service providers
- ✓Security awareness training program with completion records for all personnel

- ✓Documentation and Policy Requirements
- ✓Technical Control Requirements
- ✓Operational and Human Resources Requirements
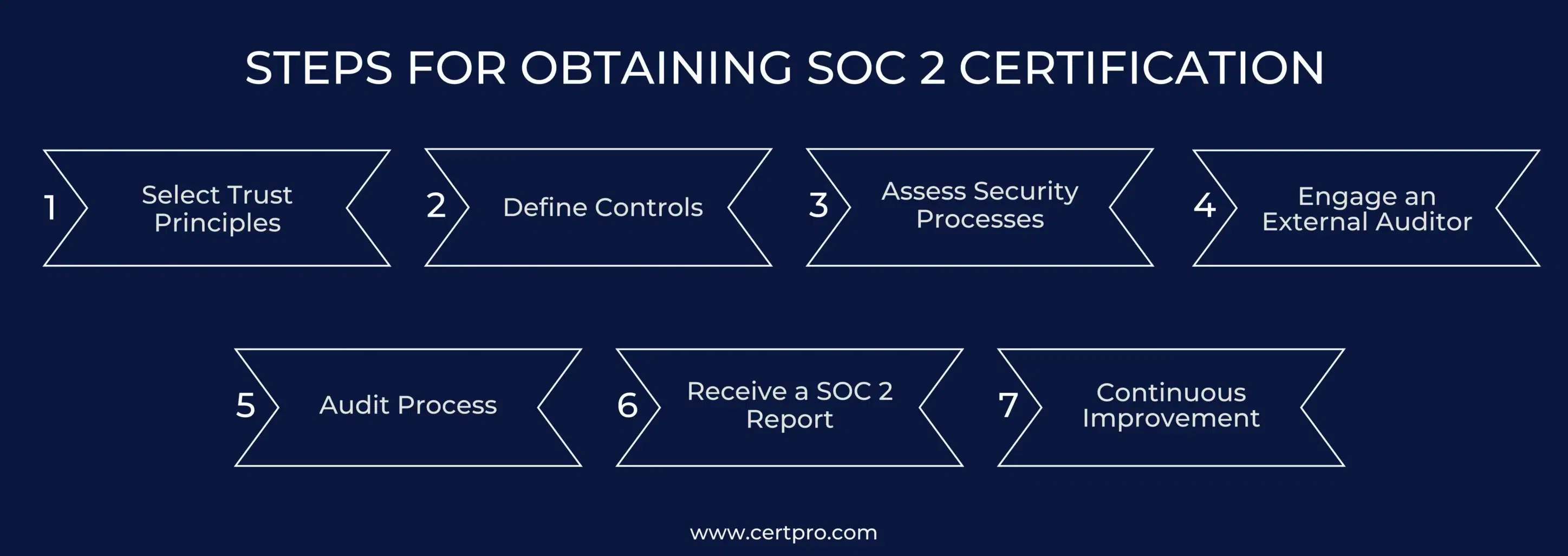
The SOC 2 Audit Process: Step-by-Step
The SOC 2 audit process follows a structured sequence of stages, each with defined objectives, activities, and deliverables. CertPro conducts SOC 2 audit engagements in Jakarta according to AICPA attestation standards (AT-C Section 105 and AT-C Section 205), ensuring that each engagement stage is performed with the rigor and professional judgment required to issue a credible, defensible SOC 2 attestation report. The following stages describe the complete engagement sequence for SOC 2 Certification in Jakarta.
Scope definition is the foundational stage of every SOC 2 engagement. During this stage, the audit team and organizational management jointly establish the system boundaries subject to audit examination — defining which applications, infrastructure components, data centers, cloud environments, personnel, and processes fall within scope. System boundaries must be defined with sufficient precision to identify all relevant controls and evidence sources, while remaining focused enough to make the audit program executable within the planned timeframe and resources.
Trust Services Criteria selection occurs during scope definition, based on the nature of the organization’s services and the contractual or regulatory requirements driving the engagement. For most Jakarta-based organizations, the Security criterion is mandatory; additional criteria are selected based on service commitments, data types processed, and client expectations. Engagement planning also establishes the audit type (Type 1 or Type 2), the observation period dates for Type 2 engagements, the overall audit timeline, and the evidence collection procedures that will govern fieldwork activities.
Following scope definition, the audit team develops a tailored audit program that maps the organization’s described controls to the applicable Trust Services Criteria. Each identified control is assigned specific testing procedures appropriate to its nature — automated controls may be tested through system configuration review and log analysis, while manual controls require documented evidence of execution such as approval records, meeting minutes, or workflow outputs. The audit program ensures comprehensive coverage of all in-scope criteria and establishes the sampling methodology for testing control operation across the audit period in Type 2 engagements.
Audit fieldwork constitutes the primary evidence-gathering phase of the SOC 2 engagement. Auditors conduct document reviews, system configuration inspections, personnel interviews, and control testing procedures in accordance with the audit program developed in Stage 2. Evidence collection encompasses policy documents, system-generated logs, access review records, change tickets, training completion records, vulnerability scan reports, penetration testing results, and operational outputs that demonstrate control execution. For SOC 2 Type 2 engagements, auditors sample evidence across the full observation period to confirm that controls operated consistently and effectively throughout.
During fieldwork, auditors identify exceptions — instances where evidence indicates that a control did not operate as described or failed to meet the applicable Trust Services Criterion requirement. Each exception is documented with sufficient detail to enable management to understand the nature, timing, and potential impact of the control deviation. Identified exceptions are communicated to management during fieldwork to allow for factual accuracy review before being included in the final SOC 2 report.
Following fieldwork completion, the audit team conducts a comprehensive review of all findings, exceptions, and control testing results. Management responses to identified exceptions are evaluated, and factual corrections are incorporated where supported by evidence. The SOC 2 report is then drafted, incorporating the management-prepared system description, the auditor’s opinion on control design (Type 1) or design and operational effectiveness (Type 2), and detailed descriptions of each tested control along with any noted exceptions. The report is reviewed by engagement management and quality control reviewers before finalization.
The final SOC 2 attestation report is issued upon completion of quality review and resolution of any outstanding matters. The report includes the auditor’s opinion, system description, description of tests performed, results of testing, and any exceptions noted. For organizations pursuing SOC 2 Certification in Jakarta, the issued report represents the authoritative evidence of control evaluation that can be presented to clients, partners, and regulators. Annual surveillance and recertification cycles maintain the currency of the SOC 2 report, as Type 2 reports are typically refreshed annually to reflect the most recent observation period.
- Stage 1 — Scope Definition: Establish system boundaries, select Trust Services Criteria, and determine engagement type (Type 1 or Type 2)
- Stage 2 — Audit Program Determination: Develop control-to-criteria mappings and tailored testing procedures for each identified control
- Stage 3 — Fieldwork Initiation: Collect documentation, review system configurations, and conduct personnel interviews
- Stage 4 — Control Testing: Execute audit procedures and sample evidence across the observation period for Type 2 engagements
- Stage 5 — Exception Identification: Document control deviations and communicate findings to management for factual accuracy review
- Stage 6 — Nonconformity Review: Evaluate management responses and finalize exception documentation with impact assessment
- Stage 7 — Report Drafting: Prepare SOC 2 attestation report incorporating system description, test procedures, results, and auditor opinion
- Stage 8 — Quality Review: Subject draft report to engagement-level and firm-level quality control review
- Stage 9 — Attestation Issuance: Issue final signed SOC 2 report and deliver to the organization
- Stage 10 — Surveillance and Recertification: Initiate subsequent audit cycle to maintain current attestation status
- ✓Stage 1: Scope Definition and Engagement Planning
- ✓Stage 2: Audit Program Determination and Control Identification
- ✓Stage 3: Fieldwork — Evidence Collection and Control Testing
- ✓Stage 4: Nonconformity Review and Report Issuance
Benefits of SOC 2 Certification for Jakarta-Based Organizations
SOC 2 attestation delivers measurable commercial, operational, and regulatory benefits for Jakarta-based organizations operating in competitive and compliance-intensive markets. The benefits extend beyond the audit report itself. The process of achieving SOC 2 Certification in Jakarta systematically strengthens an organization’s security posture, operational discipline, and risk management practices — producing lasting organizational value that is independent of the attestation document.
SOC 2 attestation directly enables market access in enterprise and regulated-industry customer segments that impose vendor security requirements as a condition of engagement. For Jakarta-based technology companies pursuing contracts with U.S.-headquartered enterprises, European financial institutions, or multinational corporations with formal third-party risk management programs, a SOC 2 Type 2 report is frequently the specific document required to pass vendor qualification and procurement processes. Organizations without SOC 2 attestation are routinely excluded from enterprise RFP processes — or required to complete individual security assessments for each prospective client — a process that is both time-consuming and commercially limiting.
The commercial value of SOC 2 Certification in Jakarta extends to customer retention as well as acquisition. Enterprise clients that onboard a vendor on the basis of SOC 2 attestation require annual report renewals as part of ongoing vendor management — creating a structured incentive to maintain current attestation status. Organizations with current SOC 2 reports experience significantly lower customer churn in enterprise segments, as the audit evidence reduces friction during annual vendor security reviews and contract renewals.
Indonesia’s Personal Data Protection (PDP) Law, enacted in 2022, established comprehensive data protection obligations for organizations processing personal data of Indonesian residents. While the PDP Law and SOC 2 operate under different frameworks, significant areas of alignment exist — particularly around security controls, data processing accountability, breach notification procedures, and privacy management practices. Jakarta-based organizations that implement and audit the SOC 2 Privacy and Confidentiality criteria simultaneously advance their positioning under the PDP Law’s data controller and processor obligations.
Ministry of Communication and Informatics (Kominfo) oversight of digital service providers in Indonesia increasingly references international security standards as benchmarks for regulatory expectations. SOC 2 compliance engagements in Jakarta produce audit evidence and control documentation that can be presented to regulatory bodies as independently verified proof of structured data security practices. For organizations subject to Bank Indonesia’s fintech licensing requirements or Financial Services Authority (OJK) oversight, SOC 2 attestation provides an additional layer of credible third-party verification that supports regulatory examinations and supervisory inquiries.
The process of undergoing a SOC 2 audit produces operational improvements that extend well beyond the attestation report. Organizations that engage in SOC 2 audit preparation typically identify and remediate control gaps, inconsistencies in policy implementation, and procedural weaknesses that had not been systematically identified through internal processes. The discipline required to maintain SOC 2 compliance across an observation period — including consistent execution of access reviews, change management approvals, vulnerability remediation, and incident response procedures — raises the operational maturity of the security program substantially.
- ✓Enables access to enterprise and regulated-industry customer segments requiring vendor security attestation
- ✓Provides independently verified evidence of security control effectiveness to client risk management teams
- ✓Advances alignment with Indonesia’s Personal Data Protection Law obligations for Jakarta-based data processors
- ✓Reduces time and cost of responding to individual client security questionnaires through a single audited report
- ✓Demonstrates data governance maturity to investors, board members, and institutional stakeholders
- ✓Strengthens incident detection and response capabilities through auditor-identified operational improvements
- ✓Supports cross-border data transfer compliance for organizations serving international markets
- ✓Provides a competitive differentiator in markets where SOC 2 attestation is not yet universally adopted
- ✓Creates a documented audit trail of control operation that supports internal governance and accountability

- ✓Enterprise Market Access and Contract Enablement
- ✓Regulatory Alignment and Data Governance Positioning
- ✓Operational Security Strengthening and Risk Reduction
SOC 2 Certification Cost in Jakarta
SOC 2 certification cost in Jakarta is determined by several interconnected factors that reflect the complexity, scope, and duration of the audit engagement. CertPro structures SOC 2 audit engagements with transparent, fixed pricing frameworks calibrated to organizational size, the number of Trust Services Criteria in scope, the selected audit type, and the complexity of the technology environment under evaluation. Fixed pricing provides Jakarta-based organizations with cost certainty from engagement commencement — eliminating the budget uncertainty associated with variable hourly billing models.
Factors Influencing SOC 2 Audit Cost
The primary cost determinants for SOC 2 certification in Jakarta include the scope of Trust Services Criteria selected, the scale and complexity of the technology infrastructure within audit boundaries, the number of control domains requiring testing, and the audit type. SOC 2 Type 1 audits are generally less costly than Type 2 engagements because they do not require extended observation period testing or the associated evidence sampling across multiple months. Organizations with complex hybrid cloud environments, multiple data centers, or large numbers of in-scope personnel and systems will typically incur higher audit costs than those with simpler, more contained system boundaries.
For Jakarta-based organizations, the number of Trust Services Criteria included in scope is a significant cost driver. Engagements limited to the Security criterion (the minimum required scope) involve fewer control domains and less extensive testing than engagements incorporating all five criteria. Organizations in the financial technology sector frequently include Processing Integrity and Privacy criteria in addition to Security and Availability — expanding the audit program and correspondingly increasing engagement cost. CertPro provides fixed SOC 2 certification cost estimates for Jakarta engagements following a preliminary scope discussion, enabling organizations to plan accurately for the investment required.
| Cost Factor | Lower Cost Scenario | Higher Cost Scenario |
|---|---|---|
| Audit Type | SOC 2 Type 1 | SOC 2 Type 2 (12-month period) |
| Criteria Scope | Security (Common Criteria) only | All five Trust Services Criteria |
| Organization Size | Small startup, limited infrastructure | Enterprise with complex hybrid cloud |
| System Complexity | Single cloud environment, standardized stack | Multi-cloud, on-premise, third-party integrations |
| Observation Period | N/A (Type 1) | 12 months with full evidence sampling |
Return on Investment Framing for Jakarta Organizations
The investment in SOC 2 certification for Jakarta companies should be evaluated in the context of the commercial opportunities it enables and the operational costs it reduces. Enterprise contracts won on the basis of SOC 2 attestation frequently represent contract values that far exceed the total cost of the audit engagement. The elimination of individual client security assessment processes — which can consume significant internal resources across legal, security, and executive functions — represents a tangible operational saving for organizations serving multiple enterprise clients simultaneously. Organizations that have achieved SOC 2 Certification in Jakarta consistently report reduced time-to-close in enterprise sales cycles and improved vendor qualification outcomes.
Jakarta’s Technology and Regulatory Landscape for SOC 2
Jakarta occupies a unique position as the center of Indonesia’s digital economy — home to some of Southeast Asia’s largest technology companies, a vibrant startup ecosystem, expanding data center infrastructure, and a regulatory environment actively evolving to address the governance demands of the digital age. This context makes SOC 2 Certification in Jakarta particularly relevant and increasingly urgent for organizations seeking to operate credibly in both domestic and international markets.
Jakarta’s Digital Economy and SOC 2 Demand Drivers
Indonesia’s digital economy — the largest in Southeast Asia by gross merchandise value — is anchored in Jakarta, where unicorn companies including Gojek, Tokopedia, and Traveloka have built technology platforms serving hundreds of millions of users. The scaling of these platforms and the development of their enterprise supplier ecosystems creates substantial demand for SOC 2 attestation among the technology vendors, SaaS providers, and infrastructure companies that serve them. As Jakarta’s technology ecosystem matures, security attestation requirements are migrating from the largest players into mid-market and growth-stage organizations now expected by their own enterprise clients to maintain formal security certifications.
Jakarta’s expanding data center ecosystem — including facilities operated by regional and global providers — positions the city as a major cloud infrastructure hub for the broader Southeast Asian region. Data center operators and colocation providers serving international clients face SOC 2 attestation requirements from their customer base, particularly from financial services and technology companies that impose supply chain security requirements on critical infrastructure providers. SOC 2 audit engagements in Jakarta for data center operators typically focus on the Security and Availability criteria, with particular attention to physical security controls, environmental monitoring, and redundancy architecture.
Indonesia’s PDP Law and SOC 2 Criteria Alignment
Indonesia’s Personal Data Protection Law (UU PDP), which entered into force in October 2022, establishes comprehensive obligations for personal data controllers and processors operating in Indonesia. Key obligations under the PDP Law — including the requirement to implement appropriate technical and organizational security measures, the obligation to notify affected individuals and regulators following data breaches, and the requirement to document data processing activities — align directly with control requirements evaluated under the SOC 2 Security, Privacy, and Confidentiality criteria. Jakarta organizations that achieve SOC 2 attestation with these criteria in scope build documented, auditor-verified evidence of PDP Law compliance practices.
The Ministry of Communication and Informatics (Kominfo) serves as the primary regulatory body overseeing data protection compliance under the PDP Law and has authority to impose penalties on organizations that fail to implement adequate data security measures. While SOC 2 attestation is not a formal regulatory certification under Indonesian law, the independently verified control evidence it produces gives Jakarta-based organizations a defensible record of security program maturity that is directly relevant to regulatory examinations. Organizations subject to Kominfo oversight increasingly reference SOC 2 compliance as part of their regulatory engagement strategy to demonstrate a proactive and structured approach to data protection.
CertPro: Licensed CPA Firm for SOC 2 Attestation in Jakarta
CertPro is a Licensed CPA Firm authorized to conduct SOC 2 attestation engagements under AICPA attestation standards. CertPro’s authority to issue SOC 2 reports derives from its status as a licensed public accounting firm — a qualification that distinguishes it from technology consultancies, security advisory firms, and compliance service providers that do not hold the professional licensing required to issue legally recognized SOC 2 attestation reports. Organizations that engage non-CPA entities for SOC 2 services receive documents that cannot constitute valid SOC 2 reports under AICPA standards and will not be accepted by enterprise clients or regulatory bodies.
Audit Authority and Professional Standards
CertPro conducts SOC 2 audit engagements in accordance with AICPA Statement on Standards for Attestation Engagements (SSAE) No. 18 — specifically AT-C Section 105 (Concepts Common to All Attestation Engagements) and AT-C Section 205 (Examination Engagements). These standards govern the professional conduct of attestation engagements, including independence requirements, evidence sufficiency standards, reporting obligations, and quality control procedures. Adherence to these standards ensures that CertPro’s SOC 2 reports meet the professional quality and independence requirements that enterprise clients, financial institutions, and regulatory bodies expect from a credible SOC 2 attestation.
CertPro’s engagement teams include credentialed professionals with deep expertise in information systems auditing, cloud security architecture, and the specific control environments common among Jakarta-based technology organizations. Engagement leads hold Certified Information Systems Auditor (CISA) and Certified Public Accountant (CPA) credentials — bringing both the technical depth required to evaluate complex security control environments and the professional certification required to issue authoritative attestation reports. This combination of technical expertise and professional licensing defines CertPro as a qualified SOC 2 audit services provider in Jakarta, Indonesia.
Engagement Transparency and Fixed Pricing Structure
CertPro structures SOC 2 audit engagements with fixed pricing that is established and agreed upon before fieldwork commences. Fixed pricing eliminates the budget uncertainty associated with hourly billing models and provides Jakarta-based organizations with a clear understanding of total engagement costs from the outset. Pricing is determined following a preliminary scope assessment that evaluates system boundaries, criteria selection, audit type, and infrastructure complexity — ensuring that pricing accurately reflects the scope of work required for each specific SOC 2 engagement in Jakarta.
CertPro has conducted SOC 2 certification engagements for organizations across Jakarta’s technology, financial services, healthcare technology, and infrastructure sectors. The depth of experience across these sectors enables CertPro’s audit teams to efficiently evaluate control environments common in Jakarta’s business landscape — reducing audit friction without compromising the rigor and independence that SOC 2 attestation requires. CertPro’s Jakarta client base includes organizations at various stages of the SOC 2 lifecycle: from initial Type 1 engagements through multi-year Type 2 recertification cycles.
SOC 2 Certification in Jakarta: Summary and Next Steps
SOC 2 Certification in Jakarta represents a strategically significant attestation for technology companies, financial services organizations, cloud service providers, and data processors operating in Indonesia’s primary commercial and technology center. As Jakarta’s digital economy continues to scale and its integration with international enterprise markets deepens, SOC 2 attestation is transitioning from a competitive differentiator to a baseline commercial requirement for organizations operating in data-intensive sectors and serving enterprise clients globally.
CertPro conducts SOC 2 attestation engagements for Jakarta-based organizations as a Licensed CPA Firm operating under AICPA attestation standards. Engagements are structured against the Trust Services Criteria applicable to each organization’s specific service commitments, data processing obligations, and client requirements — producing SOC 2 reports that meet the professional standards demanded by enterprise clients, regulated-industry partners, and institutional stakeholders worldwide. Organizations ready to initiate a SOC 2 audit engagement in Jakarta are invited to contact CertPro to discuss scope, timeline, and fixed pricing applicable to their specific operating environment.
The SOC 2 audit process for Jakarta organizations begins with a structured scope definition discussion that establishes system boundaries, applicable Trust Services Criteria, and engagement type — providing a clear framework for the audit program and a fixed cost estimate before any fieldwork commences. Organizations at any stage of security program maturity can engage CertPro for SOC 2 Certification in Jakarta: from organizations pursuing an initial Type 1 attestation to those entering annual Type 2 recertification cycles that maintain the currency of their attestation status across successive reporting periods.
FAQ
▶
What is SOC 2 Certification and how does it differ from ISO 27001?
▶
How long does SOC 2 certification take in Jakarta?
▶
What is the difference between SOC 2 Type 1 and Type 2 for Jakarta companies?
▶
Does SOC 2 certification help Jakarta organizations comply with Indonesia’s PDP Law?
▶
Can a hybrid cloud environment be included in SOC 2 audit scope in Jakarta?
▶
How frequently must SOC 2 reports be renewed?
▶
What industries in Jakarta most commonly require SOC 2 certification?
▶
Why must a Licensed CPA Firm conduct SOC 2 engagements?

SOC 2 CERTIFICATION IN INDIA: STRATEGIES FOR TECH SECTOR COMPLIANCE IN 2026
The AICPA developed SOC 2 certification in India as a collection of guidelines to assist IT businesses in protecting client data. With the rapid growt…

THE IMPACT OF SOC 2 CERTIFICATION ON CUSTOMER RETENTION AND ACQUISITION
The world and businesses are changing together. Now, companies have transformed into online operations and transmitted data electronically. Therefore,…

Multi-Framework Compliance Guide: Best Practices and Strategies
Most compliance teams aren’t managing one framework. They’re managing three, four, sometimes five — simultaneously. A SaaS company selling to enterpri…
Get In Touch
have a question? let us get back to you.
–>

